Learning how to build a cybersecurity awareness training program is essential to reducing cyber risk among employees. This guide provides security leaders, IT managers, and compliance officers with a practical framework for every stage of the build:
- Assessing current risk posture
- Designing role-based curricula
- Running multi-channel phishing simulations across email, vishing, smishing, and deepfake scenarios
- Translating behavioral data into metrics suitable for board-level review
- Addressing business email compromise (BEC), executive impersonation, and AI-generated threats that require a fundamentally different training architecture than annual compliance modules
The result is a concrete, step-by-step program design that organizations can adapt to their size, industry, and compliance requirements.
Organizations seeking to develop a cybersecurity awareness training program are encouraged to explore the Adaptive Security demo to understand how the platform supports each stage of the process.
What Cybersecurity Awareness Training Is and Why It Matters in 2026
A cybersecurity awareness training program is a structured, ongoing project designed to change employee security behavior and reduce human-layer risk. That is achieved through a combination of security awareness, which builds threat recognition and a security-first mindset, with security training, which develops the specific skills employees need to act on that awareness.
Recognition without practiced response skills leaves employees aware that a threat exists but without the capacity to respond effectively. Both components must operate together for an organization to measurably reduce its exposure.
To maximize effectiveness, organizations should implement their cybersecurity awareness training using best practices, such as clearly defining the training scope and tailoring it to job type or level of experience.
This ensures that cybersecurity training addresses both general and targeted threats and that employees are prepared to respond to the various methods cyberattackers use.

How Cybersecurity Awareness Training Programs Have Evolved
Early security awareness programs were built around annual compliance requirements: a training module completed before a deadline, a certificate filed, a box checked. That model treated employee security behavior as an audit problem rather than a risk problem.
Modern human risk management programs are developed to continuously assess and improve employee security behavior, using phishing simulations, behavior-based scoring, and targeted microlearning triggered by real actions rather than calendar dates.
The shift from compliance obligations to behavioral change is the foundational decision any security leader must make before designing a program, and it shapes every step that follows in assessing an organization's actual exposure.
Ultimately, the financial case for a cybersecurity awareness training program is inseparable from the cost of ignoring it. According to the FBI 2025 IC3 Annual Report, cybercrime losses reached $20.9 billion, marking the first time they surpassed $20 billion.
How to Build a Cybersecurity Awareness Training Program Step 1: Assess the Organization's Security Posture and Risk Landscape
Building a cybersecurity awareness training program begins with:
- Auditing existing training completion logs
- Reviewing past phishing simulation results
- Mapping employee open-source intelligence (OSINT) exposure
- Identifying which compliance frameworks govern the organization.
Additionally, it is essential to evaluate the specific risks and vulnerabilities of IT systems, particularly in regulated or government environments, where such systems are common targets for cyber intrusions.
Every downstream decision, including curriculum scope, simulation targeting, and reporting structure, flows directly from what this assessment reveals. A pre-training knowledge assessment at this stage also establishes the performance baseline needed to demonstrate the program's effectiveness in subsequent months.
Audit Existing Training Records and Incident History
The first data source most organizations overlook is the one they already possess. Training completion logs should be reviewed to identify departmental gaps, roles that were never enrolled, and whether the content covered anything beyond email phishing.
Completion data should be cross-referenced with internal incident history to determine which teams submitted the most reported phishing attempts, which individuals clicked on previous simulation links, and where credential-compromise events originated.
This analysis reveals exactly where behavioral risk is concentrated before a single module is designed, and understanding and meeting reporting requirements is essential, particularly for organizations in regulated sectors.
Map OSINT Exposure and Credential Breach History
Attackers build targeting lists from publicly available employee data before initiating contact, using, among others:
- LinkedIn profiles
- Conference speaker bios
- GitHub profiles
- Corporate directory leaks
Such data provides adversaries with sufficient information to craft personalized spear phishing lures targeting specific roles. This reconnaissance enables attackers to identify high-value targets and craft personalized lures, increasing the risk to sensitive data and accounts.
An OSINT sweep across the employee population, cross-referenced against known credential-breach databases, surfaces accounts that are already circulating on the dark web.
Identify High-Risk Roles and Applicable Compliance Frameworks
Not every employee carries equal risk, with examples including:
- Finance staff can authorize wire transfers
- Executives' identities can be cloned for business email compromise (BEC)
- IT administrators with privileged access can represent disproportionate exposure relative to their headcount
Roles such as this should be identified through job function analysis, followed by mapping of the regulatory frameworks applicable to the organization, including GDPR, HIPAA, PCI-DSS, SOC 2, and ISO 27001, each of which creates specific, mandatory security awareness training obligations with documented audit requirements.
Government entities and defense industrial systems, in particular, face especially stringent training and compliance requirements, often mandated by statutory standards and focused on safeguarding sensitive data and IT systems.
This compliance mapping determines both minimum training frequency and the evidence required for auditors, making it a non-negotiable input before curriculum design begins.
How to Build a Cybersecurity Awareness Training Program Step 2: Define Clear Goals, Objectives, and Program Ownership
Building a cybersecurity awareness training program involves setting measurable KPIs, establishing program ownership, and securing executive buy-in through business risk language, then using that foundation to design the curriculum.
Set KPIs That Go Beyond Completion Rates
Training completion rates confirm that employees finished an exercise, not that their behavior has changed. The most important metrics include:
- Phishing simulation click rates
- Time to report suspicious emails
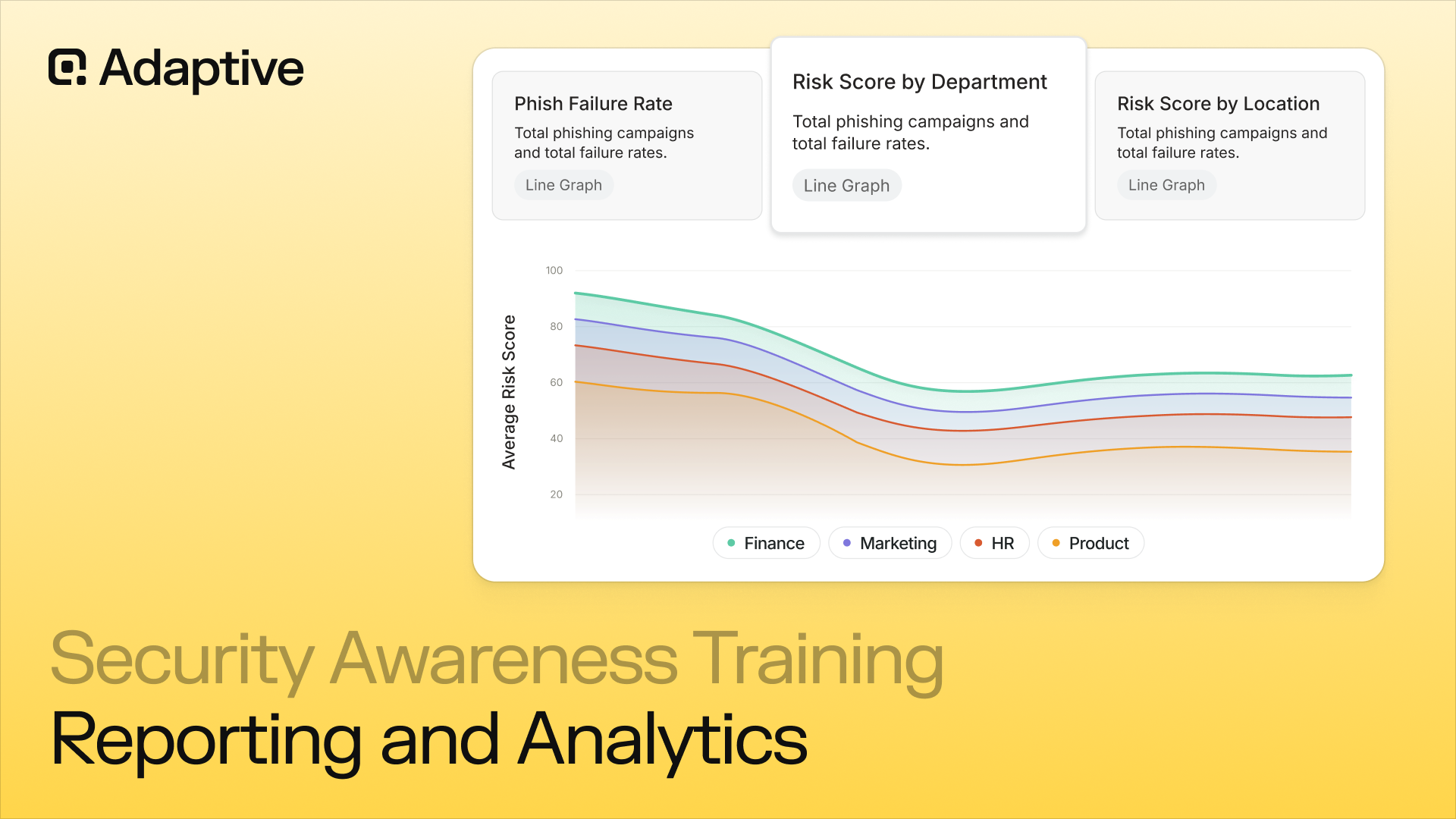
- Human risk score trends across departments and roles
To illustrate, a defensible program goal might read as follows: to reduce phishing click rates from 22% to under 8% within six months, or to achieve a measurable reduction in risk score across the finance team by Q3.
Compliance deadlines introduce a second layer of urgency. Organizations subject to HIPAA, PCI-DSS, or SOC 2 requirements should map each training module to the corresponding control and document completion against the audit calendar rather than the annual reset date.
Establish Clear Program Ownership
The most common reason awareness programs stall is ambiguous ownership. Security teams understand threat modeling but often lack the instructional design and communication skills required to run training campaigns.
HR and learning and development (L&D) understand learning design but may underweight the threat intelligence that should drive simulation scenarios.
A shared model, where IT Security owns simulation cadence and risk scoring while HR owns scheduling, communications, and completion tracking, captures both strengths without creating a single point of failure.
Translate Security Goals Into Board-Level Business Risk
Executives approve budgets in the language of business risk rather than click rates. The ROI argument is direct, as the average cost of a data breach substantially exceeds a multi-year platform investment.
One effective framing organizes the program around the five Cs:
- Change (reducing risky behavior)
- Compliance (meeting regulatory requirements)
- Cost (avoiding breach costs)
- Continuity (reducing operational disruption)
- Culture (building a security-first workforce)
This framing positions the program as a risk-mitigation instrument that boards can evaluate in terms of regulatory fines and reputational damage, two consequences that no technical control can fully offset.
With goals, ownership, and executive alignment established, the organization's actual risk posture, including who is most exposed, through which channels, and why, becomes the data that shapes all initial curriculum requirements.
How to Build a Cybersecurity Awareness Training Program Step 3: Design a Role-Based Training Curriculum Covering the Right Topics
Building a cybersecurity awareness training program that changes behavior requires organizing the curriculum into three distinct layers:
- Universal baseline content
- Role-specific modules
- Compliance-mapped tracks
Effective programs also implement spaced learning schedules, embed training into new-employee onboarding, extend coverage to third-party vendors, and reinforce habits through gamification and ambient content.
Every curriculum layer ultimately feeds into phishing tests and simulations, which serve as the behavioral testing mechanism that reveals whether training is producing measurable results.
The training is specifically designed to assist employees in preventing cyberattacks by helping them understand cybersecurity countermeasures and recognize social engineering tactics.
Build a Universal Baseline for Every Employee to Complete First
Every employee, regardless of title or department, carries baseline human risk. The universal layer of a cybersecurity awareness training program should cover five core competencies:
- Recognizing phishing and social engineering across email, SMS, deepfake, and voice channels
- Password hygiene and credential management
- Multi-factor authentication (MFA) setup and proper use
- Safe data handling and classification
- Incident reporting, specifically when and how to flag a suspicious email or call before acting on it
Training users to recognize and address vulnerabilities in their daily work is essential to reducing risk and strengthening the organization's overall security posture.
Every module should remain under 10 minutes, as attention declines sharply beyond that threshold, and shorter formats produce completion rates that reflect genuine engagement rather than employees clicking through to satisfy a requirement.
The objective at this stage is to build a shared security vocabulary and a reporting instinct that holds across the entire organization.
Layer in Role-Based Modules for High-Risk Functions
Generic training fails high-risk roles because it describes threats abstractly rather than placing employees in the specific scenarios they will actually encounter. To illustrate:
- Finance teams require modules on business email compromise (BEC) and wire fraud verification procedures, as the FBI's IC3 2024 Annual Report recorded 21,442 BEC complaints totaling $2.77 billion in losses
- Executives require deepfake video impersonation scenarios and spear phishing simulations built from their own publicly available data
- IT staff require credential theft and insider threat modules that reflect the access privileges they hold
- HR and onboarding teams require identity verification protocols for communicating with new hires, where impersonation risk is highest
- Insider threats are a significant cybersecurity risk, as they involve current or former employees with direct access to sensitive data and networks
Role-based design is not optional in an AI-threat environment, as an attacker who builds a deepfake of a CFO has already engaged in role-specific targeting. The training program must match that precision.

Map Compliance-Specific Content to the Applicable Framework
Regulated industries have mandatory training requirements that generic programs consistently fail to address:
- Healthcare organizations require training content mapped to HIPAA's workforce security awareness requirements
- Payment processors and retailers require modules addressing PCI-DSS cardholder data protection obligations
- Organizations processing data from EU residents require GDPR-aligned data handling and breach notification content
Audit-ready completion records must accompany each track so compliance officers can demonstrate coverage during assessments.
Match Delivery Formats to Context and Audience
Format selection directly affects whether employees learn or simply comply:
- Short scenario-based video modules under 10 minutes are appropriate for asynchronous baseline and role-based content
- Interactive simulations, in which an employee decides how to respond to a suspicious vendor invoice or an urgent wire transfer request, provide behavioral experience that passive viewing cannot replicate
- Microlearning nudges, triggered automatically when an employee fails a simulation, deliver targeted remediation at the moment of highest receptivity
- Posters, newsletters, and team-messaging reminders create ambient reinforcement that keeps security visible between formal training cycles
- Live workshops are most valuable for high-risk teams, including finance, executive assistants, and IT, where complex threat scenarios benefit from facilitated discussion.
Apply Spaced Practice Schedules Instead of Annual Sessions
A UCSD Psychology compilation of over 200 research studies on spaced practice demonstrates that multiple shorter sessions distributed over time produce stronger long-term memory retention than a single session of equivalent total duration.
Applied to security awareness, this means rotating simulation themes quarterly, delivering brief refresher modules monthly, and revisiting high-risk scenarios before periods of elevated risk, such as tax season or major organizational announcements.
Integrate Security Training Into Day-One Onboarding
New employees represent acute risk during their first 90 days, as unfamiliarity with internal communication norms increases the likelihood of compliance with an impersonated "IT helpdesk" request.
Security awareness training should be assigned on day one rather than deferred to the next quarterly training cycle. First-day onboarding content should cover incident reporting procedures, password and MFA requirements, and the organization's verification protocol for any request involving credentials or fund transfers.
Use Gamification to Reinforce Engagement, Not Replace It
Gamification increases training completion and repeat engagement when implemented correctly. Points, recognition, and department-level leaderboards create social motivation without reducing the program to a competition.
The critical distinction is that gamification should reward reporting and detection behaviors, such as flagging a simulated phishing email or completing a refresher module, rather than rewarding course completion alone. Programs that reward simulation clicks avoided without building underlying recognition skills teach avoidance behavior rather than threat detection.
Include Third-Party Vendors and Contractors With System Access
Vendors and contractors with access to internal systems, customer data, or payment infrastructure carry the same human risk profile as full-time employees.
To account for that risk, a defined policy should specify minimum training requirements for third-party access, verification of completion before provisioning credentials, and periodic refreshers aligned with access renewal. Cyberattackers exploit the vendor access pathway specifically because organizations frequently exempt it from awareness requirements.
According to the SecurityScorecard 2025 Global Third-Party Breach Report, 35.5% of all breaches in 2024 were third-party related. A compelling example of a third-party attack involves the US Treasury Department, which suffered an incident in which cybercriminals gained access through a third-party vendor.
How to Build a Cybersecurity Awareness Training Program Step 4: Build a Phishing Simulation Program That Tests All Attack Channels
An effective phishing simulation program requires configuring realistic attack scenarios across email, voice, SMS, and deepfake video channels, personalizing each simulation using OSINT, and running tests at least quarterly, with continuous testing for high-risk roles.
Scenario-driven training helps employees recognize how a single click or unverified request can cascade into a multi-million-dollar incident.
When employees engage with a simulated lure, the appropriate response is an immediate just-in-time microlearning module rather than a disciplinary action. Repeat failures should be treated as training data rather than performance issues.
Fortinet's 2025 Security Awareness and Training Global Research Report found that 67% of organizations reported moderate or significant reductions in incidents after implementing programs.
Why Phishing Simulations Serve a Different Purpose Than Training Modules
Phishing simulations are the most critical behavioral measurement tool in any security awareness training program, as they test whether employees apply that knowledge under pressure: the only condition that matters when an attack occurs.
To be most effective, simulations should present multiple vantage points on large-scale cyber events, enabling employees to understand threats, vulnerabilities, and countermeasures from multiple perspectives.
Additionally, knowledge without a tested response creates a false sense of preparedness. An employee who completes a module on business email compromise (BEC) may still transfer funds to a fraudulent account when a deepfake CFO call is followed by a spoofed email 30 seconds later. Simulations close that gap by requiring employees to make real-time judgment calls.

Why Email-Only Simulation Is No Longer Adequate
Attackers now combine email with vishing (AI-cloned executive voice calls), smishing (SMS-based lures), and deepfake video calls, often across the same campaign, to overwhelm verification instincts.
An instructive example occurred in 2024, when a UK engineering firm lost $25 million after a finance employee joined a video call in which every participant was a deepfake. Email filters provided no protection.
Therefore, phishing simulations should cover the following vectors:
- OSINT-personalized spear phishing and BEC scenarios via email
- AI-cloned executive personas via voice
- Credential-harvesting lures via SMS
- Executive impersonation via deepfake video
How OSINT Personalization Makes Simulations More Effective
OSINT (Open Source Intelligence) personalization is a training exercise that uses publicly available information to mimic cybercriminal techniques for personalizing attacks, making them increasingly effective. Attackers might use:
- Publicly available employee data, including LinkedIn job titles
- Conference speaker bios
- Company org charts
- Social media posts
The information is used to craft spear phishing lures that reference projects, colleagues, and business processes. Simulations that ignore this reality train employees to identify generic phishing while leaving them exposed to the targeted attacks most likely to reach them.
Effective programs mirror attackers' methodologies by incorporating OSINT signals to personalize each scenario based on role, department, and digital footprint. For instance, an employee whose LinkedIn profile identifies a specific vendor relationship should receive a vendor impersonation simulation rather than a generic credential reset email.
How Often Phishing Simulations Should Run, and How Failures Should Be Handled
Quarterly simulation, at a minimum, maintains behavioral sharpness without causing fatigue. Finance teams, executives, HR, and IT administrators face disproportionate attack volume and require continuous or triggered simulations rather than scheduled-only testing.
When an employee clicks a simulated phishing link, the appropriate response is a just-in-time microlearning module: a brief, relevant lesson delivered at the exact moment of the error, as immediate contextual feedback produces stronger retention than retrospective training.
Simulation outcomes only create value when they connect directly to how an organization measures and tracks human risk over time.
Organizations seeking to maximize the effectiveness of training through phishing simulations are encouraged to explore the Adaptive Security demo.
How to Build a Cybersecurity Awareness Training Program Step 5: Measure Program Effectiveness With Metrics That Prove Behavioral Change
Measuring the effectiveness of a cybersecurity awareness training program requires tracking primary behavioral metrics, including phishing simulation click rates, report rates, time-to-report, and knowledge assessment scores, then layering in secondary metrics such as human risk score trends and security incident reduction.
Furthermore, risk scoring data should be used to build board-level dashboards that translate security operations into business language. Training completion, assessment results, and simulation records must be documented to meet audit requirements under GDPR, HIPAA, PCI DSS, and SOC 2.
The distinction between a meaningful program and a compliance checkbox is whether the data demonstrates behavioral change over time rather than simply confirming that training was delivered.
Track the Metrics That Reveal Actual Behavior
Phishing simulation click rate and report rate are the two metrics that expose the gap between what employees know and what they do under pressure.
A declining click rate across successive simulation rounds confirms that training is building genuine resistance. Time-to-report is equally important: an employee who flags a suspicious email within five minutes provides the security team a meaningful response window, while a 48-hour delay does not.
Training completion rate by department and role, paired with pre- and post-training knowledge assessment scores, completes the primary picture. These metrics reveal which teams are engaging and whether content is transferring into retained knowledge.

Build Secondary Metrics That Connect Training to Business Risk
Secondary metrics address another fundamental question: Is the program reducing actual security incidents? Relevant indicators to answer that question include:
- Reduction in human-error-attributed incidents quarter over quarter
- Volume of emails classified through Phish Triage and associated resolution time
- Decline in the number of high-risk employees auto-enrolled in remediation training
- Changes in OSINT exposure scores at the individual and team level.
These signals transform a training report into a risk management narrative. To demonstrate, when a board inquires whether the security investment is producing results, a response indicating that the human risk score improved 40% in a given quarter carries substantially more weight than confirmation that 92% of employees completed the annual training module.
Create Board-Level Dashboards That Speak Business Language
Risk scoring data is the bridge between security operations and executive decision-making. Individual risk scores aggregated by department, role, and organization reveal trends that boards can evaluate without a technical background.
Pairing those scores with incident reduction figures and OSINT exposure changes produces a dashboard that answers whether the organization is more or less exposed than the previous quarter.
Security leaders can use the security awareness training maturity model, which comprises five stages ranging from compliance-focused to culture-driven, to assess their organization's current standing. Programs that reach the top two stages demonstrate measurable behavior change and a sustained security culture rather than annual checkbox completion.

Document Training for Regulatory Audits
GDPR, HIPAA, PCI DSS, and SOC 2 each require documented evidence that employees received security training and that the training was effective. Audit-ready documentation includes:
- Timestamped training completion records
- Assessment scores by employee and role
- Simulation participation logs
- Records of remediation training triggered by simulation failures
Storing these records on a centralized platform with exportable reports eliminates the manual evidence-gathering that consumes compliance teams' time before each audit cycle.
Measurement is not the final step. It is the input for the next iteration of the program. The data collected feeds directly back into the starting point: reassessing the organization's security posture with current behavioral evidence rather than assumptions.
How to Build a Cybersecurity Awareness Training Program Step 6: Keep Training Content Current as Threats and Regulations Evolve
A cybersecurity awareness training program remains effective only when its content keeps pace with the threat landscape. The update cadence should be anchored to data signals, including CISA advisories, FBI IC3 alerts, and NCSC UK guidance, rather than a calendar.
New training content should be added within days of a documented emerging tactic rather than deferred to the next annual review. A program that trains employees on prior-year threats cannot defend against current attacks.
Why Annual Update Cycles Fail
The speed gap between attack development and training content is now measurable. The CrowdStrike 2026 Global Threat Report recorded the fastest eCrime breakout time on record, just 27 seconds, and a 65% increase in average breakout speed.
Those numbers indicate adversaries move from initial access to lateral movement before most organizations can respond. Annual training refreshes cannot keep pace with a threat landscape that evolves every quarter.

How to Build an Intelligence-Driven Content Update Cycle
A designated team member should monitor CISA advisories, FBI IC3 alerts, and NCSC UK bulletins on a weekly basis.
As soon as a new social engineering tactic is documented, including a new deepfake delivery method, a novel voice cloning script, or an AI-generated spear phishing variant, that tactic should become a simulation template and a microlearning module within 30 days.
Threat intelligence data must directly drive the training content backlog rather than remain isolated in a security operations silo.
What AI-Threat Modules Should Training Include
Deepfake video, AI-generated phishing emails, and voice cloning require training content that did not exist a few years ago. Employees cannot recognize a threat they have not encountered in a controlled setting.
Phishing simulations that incorporate deepfake video calls, AI-cloned executive voices, and generative AI spear-phishing provide employees with the direct experience needed to identify those attacks before a real incident occurs.
How to Prevent Training Fatigue in a Continuous Program
Continuous training is only effective if employees complete it. In order to ensure that, every module should remain under 10 minutes, and formats should rotate between:
- Short videos
- Scenario-based exercises
- Single-question knowledge checks
To reinforce content, each training module should be connected to a threat that employees have encountered, whether from a recent simulation failure, a reported phishing attempt, or an incident affecting a comparable organization.
Repetition without variety creates disengagement, while variety tied to incidents builds recognition that holds when it matters most.
How to Build a Cybersecurity Awareness Training Program for Human Risk Management
Building a security awareness training program is not equivalent to building a human risk management (HRM) architecture, but each is incomplete without the other.
Training is necessary, but organizations also need a system that measures, scores, and continuously reduces human-layer exposure rather than simply a program that delivers content.
Why Behavioral Data From Training Matters Beyond Completion Rates
Simulation results, repeat failure patterns, and training completion data are not simply administrative metrics; they are behavioral signals.
Hypothetically, when an employee engages with a phishing simulation three months in a row, that pattern identifies a specific, quantifiable risk that a blanket annual training schedule cannot address.
That data feeds directly into employee risk scoring, enabling automated, targeted interventions for the individual who needs them most, rather than pushing the same module to an entire department.
How OSINT Exposure Shapes What Training Must Cover
Training that ignores OSINT exposure is addressing the wrong problem. An employee whose LinkedIn profile identifies them as a finance approver faces a fundamentally different threat than a general staff member, and the training they receive should reflect that reality. Platforms that incorporate human risk monitoring map OSINT exposure directly to personalized training priorities rather than relying on role assumptions alone.
What Phish Triage Data Reveals About Training Effectiveness
What employees report via a phishing alert workflow is one of the clearest signals of whether training translates into real behavior change. High report rates on realistic simulations indicate that employees are applying detection skills rather than simply completing modules. Low report rates on sophisticated simulations, combined with high click rates, identify the exact threat vectors where training content has not yet changed behavior.

How to Build a Cybersecurity Awareness Training Program: Challenges and Mistakes
Understanding how to build a cybersecurity awareness training program is only part of the challenge. Building one that actually changes behavior is where most organizations fall short.
SANS Institute's Security Awareness Metrics – What to Measure and How identifies a persistent gap between programs that measure completion and those that reduce real-world susceptibility, confirming that high completion rates often coexist with unchanged phishing-click rates.
A program that earns a checkmark in every compliance audit can still leave employees unprepared when a convincing deepfake video or an AI-generated vishing call arrives.
Many programs also fail to address the range of cyber intrusion methods and vulnerabilities organizations face, making it critical to understand attack techniques and the specific threats targeting IT systems. Closing that gap requires diagnosing exactly where programs break down before committing resources to build one.
The Most Common Reasons SAT Programs Fail to Change Behavior
Eight failure patterns account for the majority of ineffective programs, and each has a documented corrective:
- Generic, one-size-fits-all content: Training built for all employees delivers nothing actionable to any of them. Implement role-based modules tied to actual threat exposure for each job function
- Annual-only delivery: Security knowledge decays within weeks of a single training session, meaning organizations that run training once a year leave a 50-week window of unchallenged vulnerability. Replace annual cycles with monthly microlearning and continuous simulation
- Measuring completion instead of behavior: A 95% completion rate paired with a flat phishing click rate is not a success metric; it is a warning sign. Track click rates, reporting rates, and human risk score changes over time
- Punitive simulation responses: Penalizing employees who click a simulated phishing link leads to disengagement rather than behavioral improvement. Deliver immediate, non-punitive microlearning at the moment of failure and treat every click as a coaching opportunity
- No executive sponsorship: Programs without C-suite visibility are chronically underfunded and culturally invisible. Tie program outcomes to board-level risk metrics and secure named executive ownership before launch
- Email-only coverage: Attackers operate across multiple channels, including vishing, smishing, and deepfake video attacks, which are active, documented threats that most legacy platforms do not simulate. Extend phishing simulations across voice, SMS, and video to match the real attack surface
- Content disconnected from live threat intelligence: Training built on static, outdated scenarios teaches employees to recognize prior-year attacks. Refresh simulation content continuously using current threat intelligence, rather than relying on an annual content calendar.
- Minimal programs with no simulation component: Budget-constrained small and mid-market organizations frequently deploy training without hands-on simulation, removing the most effective mechanism for building real-world detection instincts. Treat simulation as a non-negotiable program component rather than an optional add-on.
How Remote and Hybrid Workforces Change the Program Requirements
Distributed teams introduce failure modes that did not exist in office-first environments. Employees working remotely operate on home networks, use personal devices alongside corporate ones, and encounter unique attack surfaces, including unsecured Wi-Fi exploitation, personal email credential theft, and SMS-based impersonation, that office-centric training scenarios do not address.
Simulation scenarios must reflect home-office conditions, and delivery formats must be asynchronous and mobile-accessible to reach distributed teams without creating scheduling friction that drives completion theater rather than genuine engagement.
The corrective is straightforward: design training delivery for digital-first access from the outset, build simulation scenarios that reflect home-office attack vectors, and recognize that physical proximity to a security team does not substitute for a structured program.

Frequently Asked Questions About How to Build a Cybersecurity Awareness Training Program
How Long Does It Take to Build a Cybersecurity Awareness Training Program From Scratch?
Building a cybersecurity awareness training program from scratch typically requires 4 to 12 weeks, depending on organizational size, compliance requirements, and whether a platform is being deployed or content is being built in-house.
A small- to midsize organization using a dedicated SAT platform can complete a baseline assessment, configure a role-based curriculum, and launch its first phishing simulation in under 30 days.
Larger enterprises with complex compliance obligations across HIPAA, PCI-DSS, GDPR, and SOC 2 simultaneously should budget 8 to 12 weeks to align stakeholders, map training to frameworks, and establish reporting workflows.
The assessment and goal-setting phases consistently determine the timeline more than content production does. Programs launched without a baseline risk assessment tend to require significant rework within the first quarter.
What Compliance Frameworks Require Cybersecurity Awareness Training, and What Do They Mandate?
Five major compliance frameworks explicitly require or strongly mandate security awareness training as a control:
- HIPAA requires covered entities to implement a security awareness and training program for all workforce members
- PCI-DSS mandates a formal security awareness program with at least annual training and phishing-awareness content
- ISO 27001:2022 requires organizations to ensure that all personnel receive appropriate awareness education and training.
- SOC 2 expects personnel to receive training relevant to their roles and responsibilities. GDPR requires Data Protection Officers to promote awareness and training on data protection obligations.
Frameworks differ in specificity: HIPAA prescribes training at hire and when procedures change; PCI-DSS requires documented records. Organizations operating across multiple jurisdictions must map training completions, assessment scores, and simulation records to the audit requirements of each applicable framework.
How Do Organizations Measure the ROI of a Cybersecurity Awareness Training Program?
The ROI of a cybersecurity awareness training program is measured by comparing the program's cost to the quantified reduction in human-layer risk exposure.
Primary ROI metrics include reductions in phishing simulation click rates over time, increases in employee report rates for suspicious emails, reductions in security incidents attributable to human error, and time-to-report for actual threats. Secondary metrics include avoided regulatory fine exposure, reduced incident response costs, and lower cyber insurance premiums tied to demonstrable security controls.
These figures should be translated into board-level language. For instance, a program that reduces click rate from 24% to 4% across 500 employees directly reduces the pool of viable entry points for attackers.
Pairing behavioral metrics with a human risk score that aggregates individual employee risk data into a single trend line produces an ROI narrative that is auditable and repeatable across reporting cycles.
How Often Should Employees Receive Cybersecurity Awareness Training and Phishing Simulations?
Employees should receive security awareness training at least quarterly, with phishing simulations running continuously or on a monthly cadence for the general population and more frequently for high-risk roles.
Annual-only training is structurally inadequate: research in cognitive psychology consistently demonstrates that knowledge retention decays sharply within 90 days without reinforcement, leaving a 10-month window during which employee behavior is untested.
Monthly or continuous phishing simulations expose employees to current attack patterns rather than outdated templates, and just-in-time microlearning triggered by a simulation click delivers correction at the moment of highest receptivity.
High-risk roles, including finance, executives, HR, and IT staff, warrant additional targeted simulations covering business email compromise (BEC), spear phishing, vishing, and deepfake scenarios. New employees should receive baseline training on their first day and a phishing simulation within their first 30 days.
How Should a Cybersecurity Awareness Training Program Address AI-Generated Threats Like Deepfakes and AI-Powered Phishing?
A cybersecurity awareness training program must treat AI-generated threats as a distinct category requiring dedicated modules, rather than as additions to existing phishing content.
Effective programs must address three AI-specific skills:
- Recognizing AI-generated text
- Identifying deepfake audio and video
- Responding to vishing calls that clone executive voices
Simulations must reflect this reality, as email-only phishing programs leave employees unprepared for the attack vectors adversaries are actively deploying.
Role-based modules for finance and executive teams should include scenario-based training on verifying wire transfer requests through out-of-band channels, regardless of how convincing the initiating communication appears.
Building this verification habit, confirming via a known phone number rather than the one provided in the message, is the behavioral outcome that makes deepfake and vishing scenarios operationally containable.
Embedding that response pattern into employees' approach to every unusual financial or access request is precisely what distinguishes a program that satisfies a compliance requirement from one that demonstrably reduces organizational risk.
Understand How to Build a Cybersecurity Awareness Training Program in Practice
AI-generated threats have changed what a cybersecurity awareness training program must cover, and most legacy platforms have not kept pace.
Adaptive Security's platform combines multi-channel phishing simulations, role-based security awareness training, and individual human risk scoring, enabling security teams to identify exactly where behavioral gaps exist and address them before adversaries exploit them.
Organizations are encouraged to explore an Adaptive Security Demo to experience the platform firsthand.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents