Cybersecurity awareness training for employees is the most important layer of your organization's security defense. But for most organizations, it is also the most outdated. According to IBM's 2025 Cost of a Data Breach Report, the global average breach costs $4.4 million, and human error remains the leading root cause.
This guide provides a comprehensive breakdown of every type of cyberattack employees may face, a step-by-step cybersecurity awareness implementation framework, compliance coverage, real-world case studies (including a $25 million deepfake fraud), and a buyer's guide to evaluating the best cybersecurity awareness training platforms.
Attackers in 2026 are deploying AI-generated phishing threats, real-time deepfake video calls, and voice-cloned executives. If your current cybersecurity awareness training for employees hasn't been updated to account for AI-powered cybersecurity threats, this guide serves as the essential starting point.

See how to train against every AI-powered attack your employees will face
What Is Cybersecurity Awareness Training for Employees?
Cybersecurity awareness training for employees is a structured program designed to change the security behaviors of your workforce, not just inform them. It reduces human-layer risk by teaching employees to recognize cybersecurity threats, make better decisions under pressure, and respond correctly when a cyber attack reaches them.
Most organizations treat it as a cybersecurity compliance exercise. They deploy an annual cyber security awareness module, collect completion certificates, and proceed no further. It does nothing to change behavior, and only adds to their list of certifications. The gap between treating cybersecurity awareness training as a compliance exercise and genuinely reducing employee susceptibility to manipulation is where most of the current cybersecurity awareness training programs fail.
With the current fast-growing threat landscape, what you need is a constantly-updating cybersecurity awareness training for employees that runs continuously, not a click-and-finish module.
What Is the Difference Between Security Awareness and Security Training?
Security awareness is recognizing cyber threats, your employees know that phishing emails exist, social engineering happens, and that not every caller is who they claim to be.
Security awareness training for employees is knowing how to respond, your employees know exactly what to do when a suspicious email lands in their inbox, when a caller pressures them for credentials, or when a "colleague" on a video call asks them to authorize a transfer.
Security awareness without training leaves employees frozen at the moment that matters. Security training without awareness means cyber threats go unspotted before any response can even happen.
Why Cybersecurity Awareness Training for Employees Can't Wait
The financial case for cybersecurity awareness training for employees is no longer debatable. Financial losses from phishing hit $17.4 billion globally in 2024, representing a 45% year-over-year increase, according to NordVPN.
The Verizon 2025 Data Breach Investigations Report found that the human element was a factor in 60% of data breaches, a figure that has been consistent over the years. Attackers do not need to defeat your firewall if they can convince one employee to hand over exactly what they need.
What has changed in 2025 and 2026 is the sophistication of the cyberattacks reaching your employees. AI has industrialized social engineering. Phishing emails that once required skilled writers to craft are now generated at scale, personalized using publicly available employee data (OSINT), and indistinguishable from legitimate internal communications. The cyberattacks employees were trained to identify in 2022 look nothing like what is reaching inboxes today.Traditional cyber security awareness training for employees was built for a cyber threat landscape that no longer exists. If your program hasn't been updated to address AI-generated phishing attacks, deepfake video impersonation, and voice cloning, it is already outdated. And your staff members are being tested by cyber attackers every day, regardless of whether you're training them or not.
AI Cybersecurity Threats Employees Are Facing Right Now
The AI cybersecurity threats your employees face in 2026 are categorically different from anything previous training programs were designed to address. According to Microsoft's 2025 Digital Defense Report, people are 4.5 times more likely to click on phishing emails written with AI assistance, with AI-generated messages achieving a 54% click-through rate compared to just 12% for those written manually.
And, a 2024 survey reported by Forbes found that 80% of companies had no protocols in place to defend against AI-based cyberattacks, including deepfakes.
AI-generated spear phishing uses large language models to craft personalized attack emails at industrial scale. A cyber attacker feeds in an employee's LinkedIn profile, recent company announcements, and publicly available email patterns, and generates a message that references a real project, uses the right internal tone, and comes from a spoofed address that clears a quick visual check. There are no typos, no awkward phrasing, and no instant tells. Nothing to identify it as a phishing email at the first glance.
Voice cloning and vishing have moved from proof-of-concept to operational. A cyber threat actor needs as little as 30 seconds of audio, pulled from a public earnings call, a podcast interview, a webinar, or a conference recording, to clone an executive's voice convincingly enough to authorize a payment by phone. That attack vector is now accessible to any criminal with a laptop.
Types of Cyberattacks Your Security Awareness Training Program Should Cover for Employees

Most cybersecurity awareness training programs for employees are built around one threat: phishing. That is a problem, since phishing is only the entry point. The actual attack surface your employees face in 2026 spans across dozens of techniques over three tiers of sophistication.
Using IBM's taxonomy as a framework, we can categorize cyberattacks into three levels:
- Pervasive attacks: high-volume, daily cyber threats that exploit human behavior at scale: phishing, social engineering, malware, BEC, and account takeover.
- Advanced attacks: patient, multi-stage campaigns that combine technical and human exploitation: man-in-the-middle, supply chain compromise, and zero-day exploits.
- Emerging threats: AI-generated fraud, deepfake video impersonation, cloud misconfigurations, and data tampering in AI-powered workflows.
In every case, the employee is either the target, the entry point, or the last line of defense. Your cyber security awareness training program needs to cover all three tiers, not just the one that is easiest to simulate.
Simulate every attack in this guide—email, phone, SMS, and deepfake video—all in one platform.
Cyber Attacks Faced by Employees: Phishing, Spear Phishing, and Whale Phishing
Phishing is the most common cyberattack vector in the world, and it comes in three levels of precision.
- Mass phishing targets thousands of recipients with identical messages. Mismatched sender domains, generic greetings, and urgent language are the tells. These are the cyberattacks employees are most trained to catch, and still click on.
- Spear phishing targets a specific individual using personalized data pulled from LinkedIn, company websites, and public filings. In 2026, LLMs generate these emails at scale with no grammatical errors and accurate internal context. An employee receives what looks like a message from their manager referencing an ongoing project, and the only anomaly is the sender domain.
- Whale phishing targets executives specifically. A cyber attacker impersonates a board member, regulator, or legal counsel to pressure a senior employee into approving a transfer or sharing confidential data. The stakes are higher and the social pressure is engineered to bypass critical thinking.
According to Verizon's 2025 DBIR, phishing remains a factor in the majority of social engineering breaches. Recognition at the email level, before any clicks, is the behavior phishing awareness training for employees needs to build.
Cyber Attacks Faced by Employees: Social Engineering Awareness Training: Vishing, Smishing, and Pretexting
Social engineering is the umbrella. Vishing, smishing, and pretexting are the tools, and all three cyberattack methods have been supercharged by generative AI.
- AI vishing and voice cloning (voice phishing) uses phone calls to impersonate IT support, executives, or financial institutions. AI voice cloning now makes it easy to replicate a known colleague's voice using as little as 30 seconds of audio.
- Smishing (SMS phishing) delivers malicious links or fake authentication requests via text message. It is increasingly used to bypass MFA: an employee may receive a text appearing to be from their company's IT team asking them to approve an urgent login request, which is actually an attacker's session.
- Pretexting involves fabricating a believable identity or scenario to extract information or access. It is frequently the setup phase for BEC attacks, where a cyber attacker may spend weeks posing as a new vendor or IT contractor before making the actual request.
In 2026, these cyberattack techniques are often deployed together in a single chain of attack. Social engineering awareness training for employees to pause and verify through a separate, known channel breaks all three.
Cyber Attacks Faced by Employees: Business Email Compromise and Account Takeover
According to the FBI Internet Crime Complaint Center (IC3), business email compromise alone drained $2.77 billion from organizations in 2024 across 21,442 reported incidents. Despite this, business email compromise (BEC) remains one of the most underrepresented topics in cybersecurity awareness training for employees.
BEC works by impersonating a trusted person at work to trick an employee into transferring funds or sharing sensitive data.
Account takeover feeds directly into BEC. Attackers obtain credentials through:
- Fake login pages that mirror your SSO or email portal
- Brute force cyberattacks against weak or reused passwords
- Dark web purchases of credentials leaked in previous breaches
Once inside a legitimate account, a cyber attacker can monitor email threads for months before making a move, making the eventual request virtually indistinguishable from genuine communication. Training employees to verify payment detail changes out-of-thread, every single time, is the most effective cybersecurity defense.
Cyber Attacks Faced by Employees: Malware, Ransomware, and Fileless Attacks
Every malware infection has a human entry point. Training employees to recognize that moment is more effective than any endpoint cybersecurity tool applied after the fact.
- Ransomware typically begins with an employee opening a macro-enabled attachment or clicking a malicious link. According to IBM's 2025 Cost of a Data Breach report, ransomware cyberattacks cost organizations an average of $5.13 million per incident, not counting reputational damage or regulatory fines.
- Trojans disguise themselves as legitimate software, a fake Adobe update, a cracked utility, a document from "the IT team." Once installed, they open a backdoor to the hacker or drop additional payloads.
- Spyware runs silently in the background, collecting keystrokes, credentials, and session tokens without any visible sign of compromise.
- Scareware triggers fake security warnings designed to panic employees into downloading malicious "fixes" or calling fraudulent support lines.
- Fileless cyberattacks leave no traditional file on disk. They exploit legitimate tools already on the device, PowerShell, for example, to execute malicious code directly in memory. There is nothing for standard antivirus to scan.
Cybersecurity awareness training for employees trains them to detect malware, ransomware, and fileless attacks: anything that creates urgency, asks for elevated permissions, or arrives from an unexpected source warrants a stop-and-verify before any action on it.
See what OSINT-personalized phishing simulations look like for your own organization
Cyber Attacks Faced by Employees: Deepfake Impersonation & AI Security
Deepfake phishing cyberattacks are not a future risk. According to Pindrop's 2025 Voice Intelligence Report, deepfake fraud cases increased by 1,300% year-over-year. Employees encounter this threat in three forms:
- Fake video calls use live deepfake video calling technology to render a convincing visual impersonation of a known executive or colleague during a live video meeting, which makes most logical requests feel legitimate.
- Voice-cloned phone calls replicate the voice of a CEO, manager, or trusted colleague using publicly available audio. The caller references internal context, creates urgency, and requests action before the call ends.
- AI-generated written and visual content, forged documents, fabricated email threads, synthetic ID images, is used to build false credibility before a direct request is made.
What makes deepfake cyberattacks effective is that they weaponize trust, not technology. The employee isn't clicking a bad link, they're responding to what appears to be a legitimate human interaction.
Never approve any financial transaction or sensitive access over a phone call or video alone to avoid being damaged by deepfake attacks. Any such request requires verification through a separate, pre-established channel, regardless of how convincing the interaction appears.
See whether your employees can detect a deepfake before it costs you $25 million
See Deepfake Simulations in Action
Cyber Attacks Faced by Employees: Man-in-the-Middle, Supply Chain, and Zero-Day Attacks
These are the advanced-tier cyberattack techniques that most cybersecurity awareness training programs for employees never cover.
- Man-in-the-middle (MITM) cyberattacks intercept communications between two parties. The most common employee exposure point: unsecured public Wi-Fi in airports, hotels, or coffee shops. A cyber attacker on the same network can silently read or modify data in transit, including login sessions and file transfers. Never access corporate systems or sensitive accounts on public Wi-Fi without a VPN.
- Supply chain cyberattacks compromise software or tools before they reach your organization. Employees trust an update from a known vendor, because they've always trusted that vendor. But the update itself has been tampered with upstream. Training employees to report unusual software behavior after an update, rather than ignoring it, creates an early detection layer.
- Zero-day exploits target vulnerabilities in software that the vendor hasn't patched yet. Employees can't fix the vulnerability, but they can shrink the window. Applying updates promptly and reporting unusual system behavior immediately are the two actions every employee is taught to do in cybersecurity awareness training programs for employees.
Cyber Attacks Faced by Employees: Insider Threats, DDoS, and Newer Cyber Threats Employees Should Know About
Not every cyber threat comes from an outsider, and not every insider threat is intentional. Cybersecurity awareness training for employees aims to differentiate that.
Insider cyber threats are more often the result of negligence than malice. According to the Verizon 2025 DBIR, a significant proportion of insider incidents involve employees mishandling data, misconfiguring systems, or falling for social engineering rather than deliberately exfiltrating information. Behavioral signs that indicate "potentially an insider threat" are:
- Accessing files or systems outside of normal job scope
- Large data transfers to personal devices or external storage
- Login activity at unusual hours or from unexpected locations
- Attempts to access systems after permissions have been revoked
DDoS (Distributed Denial-of-Service) cyberattacks flood a system with traffic until it becomes unavailable. Employees typically experience this as sudden, unexplained system slowdowns or service outages. The trained response is escalation, immediately reporting the issue to IT rather than waiting to see if it resolves itself. Early reporting shortens response time significantly.
Other emerging cyberthreats worth flagging in your training program:
- Cloud misconfigurations caused by employees storing sensitive data in unsecured cloud environments or granting excessive access permissions.
- Data tampering and AI poisoning in organizations using AI-integrated workflows, where subtly corrupted inputs cause flawed outputs, a growing risk as AI tools become standard in business operations.
What Are the Key Topics to Include in Cybersecurity Awareness Training Modules for Employees?
A complete cybersecurity awareness training program for employees covers all attack vectors of an organization. Every key cybersecurity awareness training topic below addresses a real, documented cyber attack vector, and skipping any one of them leaves a gap that attackers will find.
- Phishing and spear phishing recognition is the non-negotiable foundation. Employees need to identify mass phishing attempts by their surface-level tells, and AI-personalized spear phishing by behavioral instinct, pausing to verify before acting, regardless of how legitimate the message looks.
- Password hygiene and MFA directly reduce account takeover risk. Training should cover why password reuse across accounts is a critical vulnerability, how to use a password manager correctly, and why MFA approval requests that arrive without a corresponding login attempt are a red flag, not a routine notification.
- Physical security is consistently undertrained. Tailgating (following an authorized person into a secured area), leaving sensitive documents on a desk, and shoulder surfing (visual eavesdropping in public or open-plan offices) are low-tech attack vectors that bypass every digital control you have.
- Remote work risks expanded the attack surface permanently. Employees working from home or public locations need to understand the risks of unsecured Wi-Fi networks, personal devices accessing corporate systems (BYOD), and the absence of the network-level protections that exist inside the office perimeter.
- Data handling and classification training ensures employees know what data they're responsible for, how to store and transmit it correctly, and what constitutes a reportable incident. Mishandling of sensitive data, not just deliberate exfiltration, is a leading cause of compliance violations.
- Device hygiene and patch compliance addresses one of the most consistently exploited gaps. Employees who delay software updates, ignore patch prompts, or install unauthorized applications create vulnerabilities that attackers actively scan for. Cybersecurity awareness training should make the connection between "update now" and actual breach prevention explicit.
- Social engineering in all forms, vishing, smishing, pretexting, and BEC, needs dedicated coverage beyond a single phishing module. Each cyberattack vector has distinct recognition cues and a distinct response procedure.
- AI-specific cyber threats are the fastest-growing gap in existing training programs. Deepfakes, voice cloning, and LLM-generated fraud require employees to understand that visual and audio confirmation of identity is no longer sufficient, and that verification through a separate channel is now a standard operating procedure, not an optional step.
- Incident reporting procedures determine how quickly your organization can contain a breach. Employees who know exactly how to report a suspicious email, an unexpected MFA request, or an unusual system behavior, and who believe they won't be blamed for reporting, are your earliest warning system.
- Safe browsing and software practices close the loop on endpoint risk. Employees should know how to identify suspicious URLs, why downloading software from unverified sources creates supply chain risk, and how browser extensions can be used as data harvesting tools.
Phishing Tests for Employees: The Metric That Actually Tells You Something
A phishing test for employees is a diagnostic tool, not a punitive measure. Phishing tests identify where an organization's human risk is concentrated and allow security teams to close that gap with cybersecurity awareness training before a threat actor exploits it.
A phishing simulation platform for employees that generates useful data looks like this:
- Varied, current templates that reflect deceptive attack techniques, not the same generic "you've won a prize" email sent annually.
- Regular cadence, quarterly at minimum, monthly for high-risk roles, so employees build consistent recognition instincts rather than one-off awareness.
- Immediate micro-training triggered the moment an employee clicks, rather than a delayed report that arrives weeks later with no behavioral connection.
- Click-rate trend tracking over 6 to 12 months across teams, roles, and departments.
The goal of AI-powered phishing simulations for employees is to see the click-through rate going down over time.
Deepfake Simulation Training for Employees: Preparing for AI-Powered Fraud
Deepfake simulation training platforms expose employees to synthetic media cyberattacks in a controlled environment before a cyber attacker does it first. It works the same way phishing simulation does, but for the next generation of threats.
In practice, this means employees receive simulated deepfake scenarios: a fake video call from a synthetic version of a senior executive, or an AI-cloned voice message requesting urgent action. The simulation is realistic enough to test genuine recognition instincts, and the employee receives immediate feedback on what the tell was and what the correct response looks like.
According to SQ Magazine's 2026 Deepfake Statistics report, human detection of high-quality deepfake videos is only 24.5% accurate. Hence, deepfake simulation-based cybersecurity awareness training is the only method that builds the muscle memory employees need to catch these cyberattacks instantaneously. Reading about deepfakes in a cybersecurity awareness training module does not prepare employees for a convincing live video call – Experiencing a controlled cyber attack simulation does.
Adaptive Security's cybersecurity awareness training platform delivers deepfake and voice clone simulations alongside phishing scenarios, giving your team exposure to the full spectrum of AI-powered attacks, not just the ones that arrive by email.
Train your employees on deepfake detection before an attacker uses one against them.
How Do You Identify a Deepfake in a Business Video Call?
Deepfake video calls are designed to be convincing. The person on screen looks familiar, sounds right, and references current internal context. Detection requires knowing what to look for, because your instinct to trust a familiar face is exactly what the cyber attacker exploits.
Here's how to tell if the person you're talking to is a deepfake:
- Audio-video desync: Slight delays between lip movement and speech, particularly noticeable during fast speech or the beginning of sentences.
- Unnatural blinking: Either too frequent, too infrequent, or with an irregular pattern not typical of natural eye movement.
- Lighting inconsistency: The face appears lit differently from the background, or shadows don't match the light source in the room.
- Lip movement artifacts: Edges of the mouth blur, smear, or shift unnaturally during certain vowel sounds.
- Inability to respond to unexpected physical prompts: Asking the person to turn their head sharply to the side, cover part of their face briefly, or hold up an object often causes visible rendering failure in real-time deepfake tools.
Real-World Deepfake Cyberattack Case Studies
The following case studies examine recent incidents with significant financial impact, illustrating the consequences of deprioritizing cybersecurity awareness training for employees.
Arup: $25 Million Lost to a Deepfake Video Call (2024)
In early 2024, multinational engineering firm Arup lost USD 25.6 million to a deepfake scam, not through a system breach, but through a single employee making a seemingly routine authorized transfer.
A Hong Kong-based employee received a phishing email from the supposed UK office requesting a confidential transaction. The employee joined a video call for verification, and recognized the CFO and several colleagues. What he didn't know was that every face and voice on that call was a deepfake. The employee then approved 15 transfers across five banks, totaling 200 million Hong Kong dollars before the fraud was discovered.
No systems were compromised or credentials stolen. People were simply convinced that they were talking to the right people.
The key takeaway: Visual and vocal recognition of colleagues is no longer a reliable verification method for financial requests. Out-of-band verification, a separate call to a known number, or a confirmed in-person check, is now a non-negotiable step in any abrupt wire transfer or sensitive approval process.
UK Energy Firm: $243,000 Lost to AI Voice Cloning (2019)
This incident occurred at a time when deepfake video technology was beginning to gain traction and deepfake awareness had not yet been established across the industry. Cybersecurity awareness training for employees had not yet been recognized as a critical organizational priority.
In 2019, the CEO of a UK energy company received a phone call from who he believed to be the CEO of the firm's German parent company. His accounts say that the voice carried the right accent, tone, and even the same "melody." On the first call, the "supposed German CEO" requested an urgent transfer of USD 243,000 to a Hungarian supplier. The UK CEO complied. A second call claimed the transfer had been reimbursed. The third one demanded another follow-up payment, but by then the UK CEO had already caught on.
Despite this, the target amount had already been moved from Hungary to Mexico and beyond, making recovery effectively impossible.
Key takeaway: Voice recognition is not authentication. This attack happened before generative AI made voice cloning accessible to any threat actor with an internet connection. In 2026, the barrier to replicating a voice is near zero. A callback to a verified number, regardless of the number you received the call from, is the only reliable defense.
BlueNoroff: Real-Time Deepfake Video Used to Deploy Malware (2025)
Even highly technical organizations are not immune to the social engineering tactics deployed by malicious actors. North Korea cyber threat group BlueNoroff's deepfake attack on cryptocurrency companies proves that fact.
In June 2025, an employee of a cryptocurrency company received a Calendly link for a meeting two weeks prior. The employee joined the meeting room seemingly full of higher executives—and was manipulated into installing a malicious script, disguised as a "Zoom extension." The script then hijacked all crypto wallets found on the infected PC. Each step was designed to feel routine, even to a technically proficient employee.
Key takeaway: Familiar faces on a video call are no longer a trust signal. When a meeting participant asks you to install or update anything, regardless of who they appear to be, you must verify the request through a third-party before acting on it.
Every attack in these incidents began with an unprepared employee. Adaptive Security makes sure yours won't.
Start Training Your Team Today
How to Implement Cybersecurity Awareness Training for Employees Effectively

If your current cybersecurity awareness training program is centered around annual cyber attack modules and completion metrics, it is already behind. Modern cyber threats, especially AI-driven ones, exploit behavior, not knowledge gaps.
Reducing that risk requires a cybersecurity awareness training program designed around how employees actually act under pressure. Here's how to implement a cybersecurity awareness training program for employees that works.
- Build the business case and secure executive buy-in. Lead with financial impact. Position the cybersecurity awareness training program as a breach cost reduction initiative, not a compliance expense.
- Establish a baseline risk profile. Assess your current exposure before rollout. Run unannounced phishing simulations, identify high-risk departments, and analyze incident history for repeat failures and reporting gaps. Use this data to prioritize efforts.
- Segment training by role and risk. One-size-fits-all training is ineffective. Align content with role-specific cyber threats and access levels to ensure relevance and impact.
- Define delivery format and frequency. Continuous, short-form cybersecurity awareness training outperforms annual sessions. Use 5–10 minute modules delivered monthly or triggered by risk events. Adaptive models reduce training load for low-risk users while focusing on high-risk behavior.
- Run phishing and deepfake video simulations concurrently. Realistic cyber threat simulations validate real-world readiness. Phishing tests email threat recognition, while deepfake scenarios assess response to AI-driven online fraud. Together, they provide a complete view of human risk.
- Measure behavioral outcomes, not completion. Cybersecurity awareness training completion rates are not indicators of effectiveness. Track click rate reduction, incident reporting rates, and repeat failure trends. If behavior doesn't change, the cybersecurity awareness training program isn't working.
- Continuously iterate based on cyber threat intelligence. Cyber threats evolve rapidly. Review and update training content, simulations, and targeting quarterly to reflect current cyber attack techniques and next generation risks.
Automate role-based training, simulation cadences, and risk remediation with Adaptive Security so your team can focus on edge cases, not routine execution.
Customizing Cybersecurity Awareness Training for Employees by Role and Risk
One-size-fits-all method is the default for many cybersecurity awareness training platforms for employees. It is also the reason most cyber security awareness training programs for employees plateau.
Your highest-risk employees need targeted cybersecurity awareness training, not the same module your lowest-risk employees receive.
This is what role-based cyber security awareness training for employees looks like:
- Finance teams: BEC drills, fraudulent invoice scenarios, wire transfer authorization procedures, and vendor bank detail change verification.
- Executives: executive impersonation scenarios, deepfake video call simulations, credential phishing targeting corporate email and SSO portals.
- IT administrators: privilege escalation attempts, credential theft via phishing, supply chain compromise through trusted vendor tools.
- Remote workers: unsecured network risk, BYOD hygiene, MFA fatigue cyberattacks (repeated push notification abuse designed to wear down approval resistance).
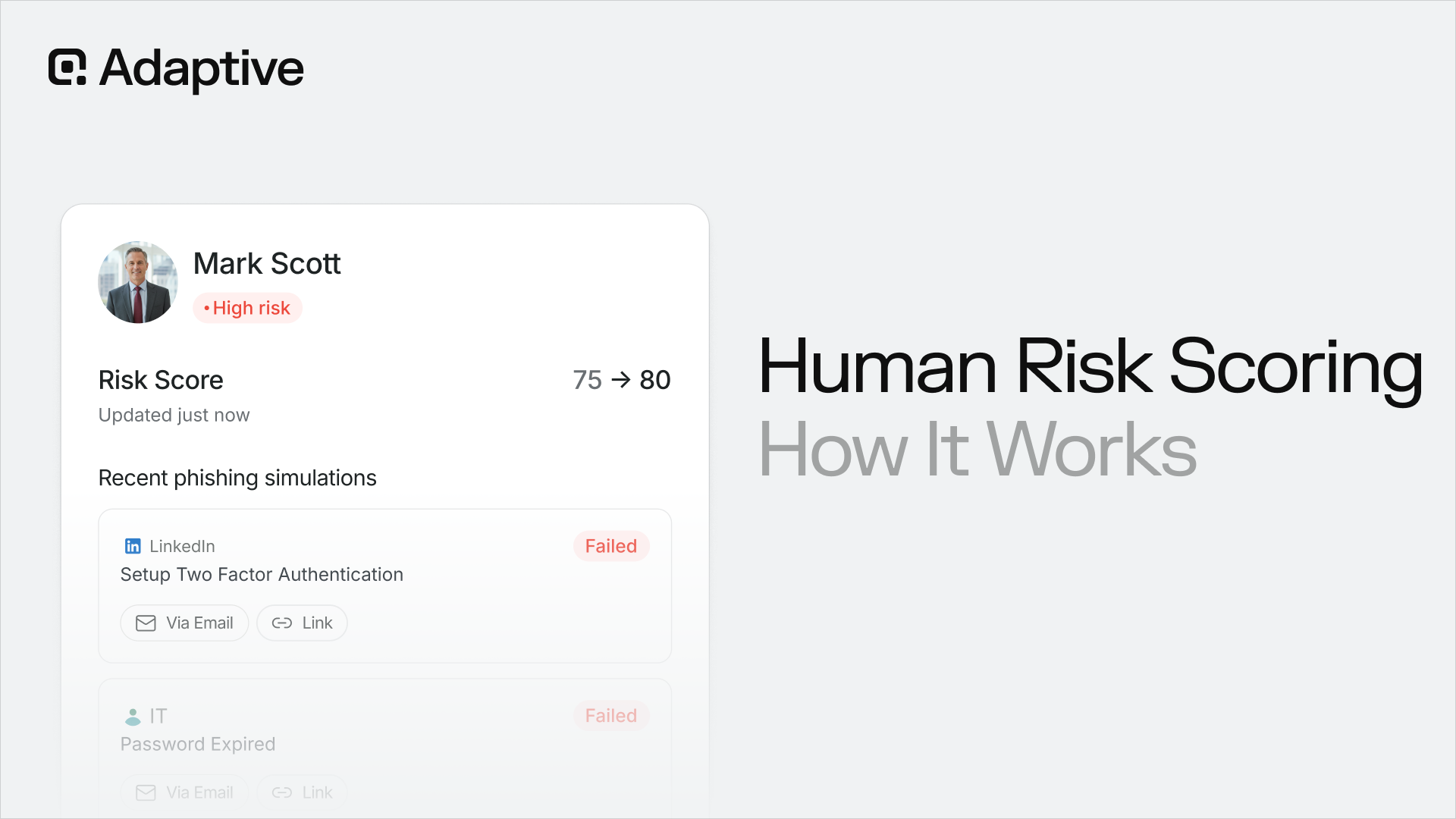
When using Adaptive Security, dynamic risk scoring surfaces individual employees who repeatedly fail realistic cyber attack simulations, handle sensitive data, or display access patterns that indicate elevated risk. Those employees receive more frequent, more targeted training automatically, without requiring manual intervention from your cybersecurity team.
How Often Should Employees Receive Cybersecurity Awareness Training?
Cybersecurity awareness training for employees should be conducted quarterly, minimum. But for most companies, however, a continuous training model is the recommended approach.
Annual cybersecurity awareness training is no longer sufficient. Effective online cybersecurity awareness training for employees uses three delivery mechanisms:
- Micro-training: short, five to ten minute modules tied to current threats, deployed monthly or triggered by new attack intelligence.
- Just-in-time learning: cybersecurity awareness training delivered immediately after a simulation failure, while the behavioral context is still active.
- Always-on behavioral nudges: live alerts and reminders that reinforce secure habits without requiring employees to log into a cybersecurity awareness training platform.
The goal is continuous risk reduction, not periodic compliance. The frequency of your cybersecurity awareness training for employees should match the frequency of the cyber threats your employees face: which is constant in 2026.
Compliance Mapping: Is Cybersecurity Awareness Training for Employees Required By Law?
The table below maps the five frameworks most relevant to cyber security awareness training for employees against their specific requirements.
NIS2 and DORA are the most prescriptive, both name cybersecurity awareness training explicitly and require it to be role-appropriate, not generic. If your organization operates in the EU financial sector, DORA compliance without a formal, documented cybersecurity awareness training program is an audit liability, not a grey area.
This table is a reference point, not legal advice. Requirements vary by jurisdiction, sector, and organizational classification. Consult qualified compliance counsel to determine your specific obligations.
Get audit-ready compliance reporting for GDPR, NIS2, DORA, ISO 27001, SOC 2, HIPAA, and PCI-DSS, built-in with our employee trainin.
What Are the Benefits of Cybersecurity Awareness Training for Employees?
The business case for cyber security awareness training for employees is measurable, not theoretical. Here is what the data shows.
- Breach costs are lower in organizations with formal training programs. According to IBM's 2025 Cost of a Data Breach report, organizations with high levels of cybersecurity awareness training for employees face significantly lower average breach costs than those without.
- Phishing click rates drop materially over time. Cyber security awareness training platforms consistently report that organizations running regular phishing simulations see click rates fall by 60 to 80% within the first 12 months of a continuous cybersecurity awareness training program. That reduction directly translates to fewer successful intrusions, fewer compromised credentials, and fewer breach investigations.
- Trained employees report incidents faster. The earlier a suspicious email, unusual login, or unexpected MFA request is reported to IT, the shorter your mean time to detect, and the lower your containment cost. According to IBM's 2025 report, breaches identified internally cost an average of $1 million less than those identified by external parties. Employee reporting is your fastest internal detection layer.
- Compliance posture improves measurably. A documented, ongoing cybersecurity awareness training program with tracked outcomes satisfies the audit requirements of GDPR, NIS2, DORA, and ISO 27001 simultaneously. Organizations that go into an audit with completion data, simulation results, and behavioral trend reports are in a materially stronger position than those presenting a single annual cybersecurity awareness training module.
How Do You Measure the ROI of Security Awareness Training for Employees?
ROI in cyber security awareness training is behavioral, not financial or administrative. Here's how to assess if your cybersecurity awareness training program for employees is working or not:
- Phishing test click rate: tracked before program launch and at regular intervals over 6 to 12 months. A downward trend is the primary signal of behavior change.
- Employee-reported incidents: the percentage of suspicious emails, calls, and requests reported to IT versus discovered after the fact. An upward trend here means your employees are functioning as a detection layer.
- Repeat cyber threat simulation failure rate: employees who fail multiple cyber threat simulations despite receiving training indicate a targeting or content problem, not just an individual performance issue.
- Average duration to report: how quickly employees escalate a suspected cyberattack after first contact. Faster escalation shortens your containment window.
Best Cybersecurity Awareness Training Platform: What to Look for in 2026
The cybersecurity awareness training platform market is crowded, and most platforms were built for yesterday's threats. Platforms like KnowBe4 and Proofpoint were designed around email phishing, which is only one channel among many. And AI has made every cyberattack vector far more dangerous. Knowing how to evaluate cyber security awareness training software makes matters much easier. Here are the criteria a cybersecurity awareness training platform for employees should meet:
- Cybersecurity awareness training simulation across all attack channels. Ensure the platform covers email, phone, SMS, and deepfake video. Limiting training to email leaves employees exposed to the fastest-growing attack vectors.
- Accessible from anywhere. Your employees should be able to access the training platform from any device. The less friction, the better. Web-based platforms are preferred; however, cross-platform programs are also viable alternatives.
- AI-personalized cyber attack simulations. Generic templates don't prepare employees for cyberattacks using public data like LinkedIn profiles, exec names, or recent company news. Look for live OSINT-driven simulations that feel authentic and current.
- Per-employee behavioral risk scoring. Cybersecurity awareness training completion rates don't reveal true risk. Effective platforms track behavior, OSINT exposure, and credential breaches to generate continuous, actionable risk scores per employee.
- Interactive and engaging. Employees manage significant workloads, and lengthy cybersecurity awareness training compounds that burden. For this reason, organizations benefit from platforms that support concise, easily digestible micro-lessons. Adaptive Security's 3-5 minute "micro-learning" format is designed to fit into busy schedules without causing more frustration.
- Automated remediation. High-risk users should automatically receive targeted training without manual intervention from your cybersecurity team.
- Compliance-ready reporting. Audit-ready reports for GDPR, NIS2, DORA, ISO 27001, SOC 2, HIPAA, and PCI-DSS should be built-in, not manual, to reduce team workload.
- Fast deployment and deep integration. Platforms should integrate natively with Microsoft 365 and Google Workspace, support SSO via Okta or Azure AD, and automate roster syncing via SCIM, no MX record changes or extended professional services required.
Best Security Awareness Training for Employees: Key Differentiators
Use these questions in every vendor evaluation. The answers will tell you immediately whether a cybersecurity awareness training platform for employees was built for the current threat landscape or the previous one.
- "Does your simulation engine cover email, phone, SMS, and video, or email only?" Any platform that cannot simulate vishing, smishing, and deepfake video calls is not a full-spectrum solution.
- "How are cybersecurity awareness training simulations personalized?" Generic templates test awareness of obvious attacks. OSINT-powered simulations test resilience against the cyber cyberattacks that actually work.
- "What does your risk scoring model factor in?" If the answer is only training completion and phishing click rates, the model is incomplete. Credential breach history and OSINT exposure are the data points that identify your highest-risk employees before an attack reaches them.
- "Where can we access the training and how easy is it?" In 2026, anything less than web-based, integrated, or cross-platform is a pass. Adaptive Security serves as an example: the platform is accessible from any browser, provides mobile-friendly micro-training sessions, and integrates with popular workplace tools such as Slack, Microsoft Teams, and leading email providers.
- "How does the platform respond when an employee fails a cyber attack simulation?" Immediate, targeted micro-training is the evidence-based response. A delayed report to a manager is not.
- "How frequently does your cyber attack simulation library update, and what drives those updates?" A library updated by live threat intelligence is categorically different from one updated quarterly by a content team.
- "What compliance frameworks does your reporting cover out of the box?" The answer should match your regulatory environment without requiring custom configuration.
How Adaptive Security Approaches Cybersecurity Awareness Training for Employees

Adaptive Security is a cybersecurity awareness training platform designed for the AI age, not patched onto it. Legacy platforms stop at email phishing simulations. Adaptive Security runs hyperrealistic, multi-channel cyberattacks across email, phone, SMS, and live deepfake video.
Each cyber attack simulation is personalized using OSINT from 1,000+ signals per employee, including public profiles, breach databases, and executive exposure points. When an employee fails a cyber attack simulation, a targeted micro-lesson triggers immediately, not months later.
Organizations may also build customized modules tailored to their specific industry or internal policies using next-generation AI tools.
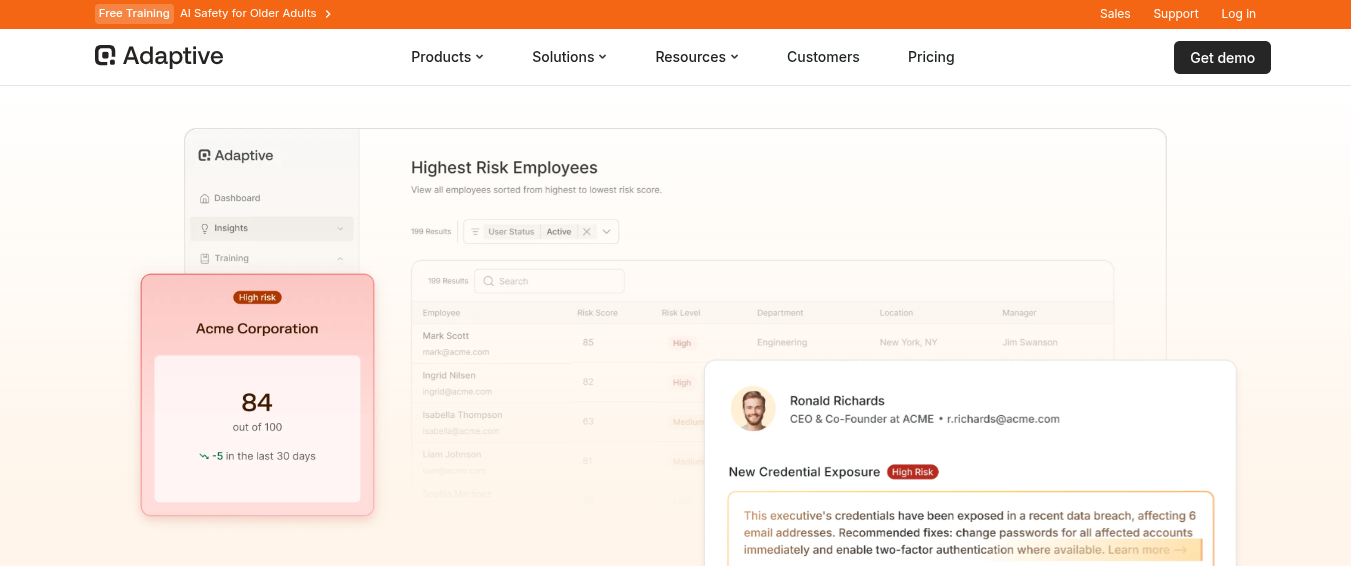
Rising risk scores from cyber attack simulation behavior, credential breaches, or OSINT exposure automatically enroll employees in role-specific training. Finance teams face invoice fraud and BEC scenarios. Executives encounter deepfake impersonations of their own voice and likeness. Developers get secure coding modules.
This creates a cybersecurity awareness training program tailored to each person's actual risk, rather than treating a CFO and a junior marketer the same.
See hyper-personalized simulations, individual risk scoring, and live deepfake scenarios tailored to your actual org structure.
Future Trends in Security Awareness Training for Employees
From cybersecurity awareness training for employees to behavioral change platforms. Completion rates are no longer enough. Behavioral risk scores, click-through-rate trends, and incident reporting metrics are now the standard, and regulators, insurers, and boards are asking for them. Platforms reporting only completion are already behind.
The AI-vs-AI dynamic is here. Cyber attackers use AI to create personalized phishing, real-time voice clones, and deepfake video fraud. Cybersecurity specialists use AI to simulate these cyberattacks continuously, at scale, and tailored to each employee's risk profile. This isn't future tech, it is operational now, and organizations should leverage AI to train employees before a cyberattack occurs.
Regulatory pressure is increasing. NIS2 is active across the EU, DORA enforcement is live for financial entities, and SEC cyber disclosure rules hold boards accountable for human risk. All three require "appropriate measures" for staff cyber security training, with auditors demanding evidence of continuous programs, not just annual completion logs.
Hyper-personalized cyber attack simulations are the new baseline. Effective programs now simulate the exact cyberattacks employees are most likely to face, based on role, public exposure, and past behavior. OSINT-driven personalization is moving from a competitive edge to a minimum expectation.
Frequently Asked Questions About Cybersecurity Awareness Training for Employees
What Is the Purpose of Phishing Awareness Training?
The purpose of phishing awareness training is to teach employees how to recognize, avoid, and report phishing cyberattacks before they compromise company systems or data. The training focuses on identifying suspicious emails, malicious links, fake login pages, and social engineering tactics so employees can prevent credential theft, malware infections, and financial fraud.
Which Behavior Indicates a Potential Insider Threat?
Behavior that may indicate a potential insider threat includes accessing sensitive data unrelated to a job role, downloading large amounts of company files, attempting to bypass security controls, or sending confidential information to personal accounts. Unusual login times, repeated access to restricted systems, or sudden changes in behavior can also signal insider risk.
How Can Employees Spot a Deepfake in a Business Video Call?
Employees can spot a deepfake in a business video call by looking for unnatural facial movements, slight delays between lip movements and speech, inconsistent lighting, or unusual blinking patterns. Suspicion should also increase if the caller urgently requests sensitive information, financial transfers, or password resets outside normal company procedures.
Does GDPR or CCPA Require Security Awareness Training for Employees?
The General Data Protection Regulation and the California Consumer Privacy Act do not explicitly require cybersecurity awareness training for employees. However, both regulations require organizations to implement reasonable security measures to protect personal data, and employee security training is widely considered part of those safeguards.
Is Cybersecurity Training Different for Remote Employees?
Yes, cybersecurity training for remote employees typically includes additional guidance on securing home networks, using VPNs, avoiding public Wi-Fi risks, protecting company devices outside the office, and safely using cloud collaboration tools. Remote work environments introduce new security risks that employees must understand to prevent data breaches.
How Do Cybercriminals Use AI in Phishing Attacks?
Cybercriminals use artificial intelligence in phishing cyberattacks to generate highly personalized emails, automate large-scale phishing campaigns, and imitate legitimate business communication. AI tools can analyze public data about targets, craft convincing messages, and even create deepfake voices or videos that impersonate executives during fraud attempts.
How Much Does Cybersecurity Awareness Training for Employees Typically Cost?
Cybersecurity awareness training typically costs between $20 and $100 per employee per year, depending on the platform and features offered. Basic programs include training modules and quizzes, while more advanced solutions add phishing simulations, reporting dashboards, compliance tracking, and automated training campaigns.
How Do You Create an Effective Cybersecurity Awareness Training Program?
To create an effective cybersecurity awareness training program, organizations should identify common cybersecurity threats, provide short and practical training sessions, use phishing simulations to reinforce learning, and deliver continuous education instead of one-time training. Programs should also encourage employees to report suspicious activity quickly.
Key Takeaways: Building a Security Awareness Training Program That Sticks
- Human error remains the #1 cyber attack vector in 2026. No firewall, endpoint tool, or email filter eliminates it. Your people are the target, and the last line of defense.
- AI-powered cyberattacks have made traditional cybersecurity awareness training for employees a liability. Deepfakes, voice cloning, and LLM-generated phishing bypass every tell employees were trained to spot. A program built for 2020 cyber threats does not protect against 2026 attacks.
- Effective programs are role-based, simulation-driven, and continuous. Annual generic cybersecurity awareness training modules produce completion certificates. Targeted, always-on programs produce behavioral change, which is the only outcome that reduces breach risk.
- ROI is measured in behavior, not completion. The metrics that matter are click-rate trends over time, incident reporting rates, and repeat-offender reduction, not how many employees clicked "finish."
- Compliance frameworks are tightening. NIS2, DORA, GDPR, and ISO 27001 all require evidence of ongoing staff cyber security training. "No formal program" is an audit liability and an insurance risk.
- Full-spectrum cybersecurity awareness training for employees, including simulations, deepfake video and voice clone scenarios, is now the baseline standard. Cybersecurity awareness training platforms that only simulate email phishing are no longer sufficient.
Ready to see what a cybersecurity awareness training program for employees built for the AI era looks like?
See Adaptive Security's multi-channel simulation suite—including live deepfake and voice clone scenarios—tailored to your actual org structure.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents