Cybersecurity awareness training is a structured program that teaches employees to recognize and stop the social engineering threats technical controls cannot: phishing, vishing, smishing, deepfake impersonation, business email compromise, and AI-generated spear phishing. It is the primary defensive layer standing between an organization and the human vulnerabilities cyberattackers exploit most reliably. As AI-enabled fraud has scaled in volume, realism, and financial damage, cybersecurity awareness training has become a board-level priority.

This cybersecurity awareness training guide covers:
- What cybersecurity awareness training is and how the modern definition differs from legacy compliance training;
- Why cybersecurity awareness training matters more in 2026 than at any previous point;
- What a complete cybersecurity awareness training program must include across topics, delivery, and role-based scenarios;
- How a modern cybersecurity awareness training program runs as a continuous lifecycle;
- Best practices for building an effective cybersecurity awareness training program;
- How to measure cybersecurity awareness training effectiveness in business terms;
- How Adaptive Security operates as a cybersecurity awareness training platform built for AI-era cyber threats.
According to Verizon's 2025 Data Breach Investigations Report, 60% of breaches involved a human element through error, social engineering, or credential abuse. That single figure defines the scope of the problem cybersecurity awareness training exists to solve.
Adaptive Security delivers AI-era cybersecurity awareness training that prepares every employee for the cyberattacks technical controls cannot intercept.
What Is Cybersecurity Awareness Training in 2026?
Answering what is cybersecurity awareness training in 2026 implies more than a content library. Today's cybersecurity awareness training is a structured, continuous program that teaches employees across the organization to recognize, resist, and report the cyber threats most likely to bypass technical defenses. These include email phishing, voice-cloned vishing calls, deepfake video impersonation, and OSINT-personalized spear phishing. It targets sustained behavioral change in every employee, from frontline staff to executives, and is distinct from technical certification programs that build tooling expertise rather than threat-response instincts.
Cybersecurity Awareness Training Versus Security Awareness
Cybersecurity awareness and cybersecurity awareness training are related concepts that produce different outcomes. Awareness means an employee knows phishing exists; cybersecurity awareness training means that same employee, under pressure from a convincing executive impersonation on a voice call, pauses, verifies through a second channel, and escalates before taking action.
Organizations that invest only in awareness through annual compliance videos and policy attestation checkboxes create employees who can define a cyber threat but freeze when one arrives. Programs that meaningfully reduce breach risk combine concept and response: they teach the threat type, then build the recognition skill through repeated practice.
Modern Cybersecurity Awareness Training in the AI Era
Legacy compliance modules were designed for a cyber threat environment that no longer exists. Annual videos and static email phishing tests were adequate when cyberattacks were generic and easily spotted, but AI-generated deepfake video impersonations, voice-cloned executive calls, and OSINT-personalized spear phishing now fool employees who passed every prior training checkpoint.
According to CrowdStrike's 2025 Global Threat Report February 2025, voice phishing (vishing) cyberattacks surged 442% between the first and second halves of 2024, as cyberattackers turned to AI-generated voice content to impersonate IT help desks and executives at scale. Modern cybersecurity awareness training platform software addresses this through three components working together: role-specific modules matched to each employee's actual exposure, realistic phishing simulations across email, voice, SMS, and video channels, and automated remediation that triggers targeted follow-up the moment an employee fails a test.
The cyber threat landscape has changed; cybersecurity awareness training built for yesterday's environment leaves entire categories of AI-era cyberattacks unaddressed.
Why Cybersecurity Awareness Training Matters More Than Ever
Cybersecurity awareness training has become a foundational organizational imperative because the human layer is now where the majority of cyberattacks succeed. According to IBM's Cost of a Data Breach Report 2025, the global average breach cost reached $4.44 million; in the United States, the average reached a record $10.22 million. When that financial exposure depends so heavily on what employees do when targeted, the value of cybersecurity awareness training moves from an optional control to a critical business priority.
Why Technical Controls Cannot Stop Cyberattacks That Exploit Trust
Technical controls stop technical cyberattacks. No firewall intercepts a phone call from a voice that sounds exactly like a CFO, and no email filter flags a spear phishing message personalized with details pulled from a LinkedIn profile.
Social engineering is designed to bypass technical defenses; it targets the person on the other end of the screen, not the system. Cybersecurity awareness training is the primary defensive control at the human layer.
How AI Has Reshaped the Cyber Threat Landscape
Generative AI has fundamentally restructured what cyberattackers can do with publicly available information. Large language models now turn open-source intelligence (OSINT) scraped from LinkedIn, earnings calls, and social profiles into grammatically flawless, contextually accurate spear phishing emails in seconds, replacing hours of manual research.
According to the World Economic Forum Global Cybersecurity Outlook 2025 January 2025, 72% of organizations reported a rise in cyber risks, driven in part by ransomware, supply chain cyberattacks, and AI-enhanced tactics including phishing, vishing, and deepfakes. Voice synthesis tools can clone an executive's vocal pattern from as little as 30 seconds of publicly available audio, and real-time deepfake video generation enables cyberattackers to impersonate executives live on a video call.
These capabilities are no longer theoretical either. A finance employee at engineering firm Arup approved a $25 million wire transfer in 2024 after joining a video call where every participant was a deepfake.
Compliance, Cyber Insurance, and the Business Case for Cybersecurity Awareness Training
HIPAA, GDPR, SOC 2, PCI-DSS, and ISO 27001 all require documented cybersecurity awareness training programs, making the discipline both a risk management imperative and a legal obligation. According to the Association for Financial Professionals 2025 Payments Fraud and Control Survey, 63% of organizations experienced business email compromise activity in 2024, underscoring how directly social engineering translates into financial fraud exposure for regulated industries.
Cyber insurance underwriters increasingly factor demonstrated employee vigilance into premium assessments, and organizations with mature cybersecurity awareness training programs cite those programs directly in policy applications. Cybersecurity awareness training has become an asset that extends well beyond the security team.
Security leaders documenting cybersecurity awareness training outcomes gain leverage with insurers, auditors, and the board in a single motion.
What a Cybersecurity Awareness Training Program Includes
A complete cybersecurity awareness training program combines topic-based education with multi-channel phishing simulations to build behavioral habits, then layers role-based content on top so each employee practices the cyberattacks most likely to target their function. According to Verizon's 2025 Data Breach Investigations Report, a small fraction of employees account for the majority of risky behavior, with roughly 8% of users driving 80% of phishing-related incidents in observed organizations, making targeted role-based cybersecurity awareness training more efficient than uniform mass deployment.
Core Curriculum Every Cybersecurity Awareness Training Program Must Cover
A complete cybersecurity awareness training program spans six domains:
- Phishing recognition, covering email-based cyberattacks, vishing calls, smishing messages, and QR code phishing;
- Social engineering defense, addressing pretexting scenarios, business email compromise (BEC), vendor impersonation, and authority-based manipulation;
- Password hygiene and credential security, training employees to use unique credentials with a password manager and to recognize credential harvesting attempts;
- Data handling and privacy, equipping staff to classify sensitive information correctly under GDPR, HIPAA, and similar regimes;
- Physical security and insider risk, covering tailgating, clean desk policies, device security, and recognition of anomalous internal behavior;
- Incident reporting procedures, training employees on exactly what to do and how fast to do it when something looks wrong.
AI-Era Cyber Threats Every Cybersecurity Awareness Training Program Must Address
The cyber threat scope that any modern cybersecurity awareness training program must address has changed fundamentally since 2023. According to the FBI's Internet Crime Report, internet crime losses reached $16.6 billion in 2024, a 33% year-over-year increase, with cyber-enabled fraud accounting for nearly 83% of total losses.
AI-generated deepfake video now enables cyberattackers to impersonate executives in live video calls with enough realism to authorize fraudulent transactions. Voice cloning replicates a CEO's exact cadence from a few seconds of publicly available audio, making vishing cyberattacks dramatically more convincing than traditional phone fraud.
Coordinated multi-channel attacks pair a spoofed SMS (smishing) message with a fake email and a follow-up call, with each channel reinforcing the others. According to the same report, business email compromise alone produced $2.77 billion in reported losses across 21,442 complaints in 2024, making it the second-largest dollar category of internet crime; no cybersecurity awareness training library built before 2023 contains realistic scenarios for these channel-mixing techniques.
Why Role-Based Cybersecurity Awareness Training Matters

A finance team member approving a wire transfer faces a fundamentally different attack surface than an IT administrator resetting credentials or a C-suite executive targeted by deepfake impersonation. Role-based cybersecurity awareness training assigns relevant scenarios to each group, so every employee practices the exact decision they will face under pressure.
Invoice fraud phishing simulations for finance teams, credential reset pretexting for IT staff, and deepfake executive impersonation drills for senior leadership are the difference between cybersecurity awareness training that reduces risk and cybersecurity awareness training that merely satisfies a compliance checkbox.
Adaptive Security tailors cybersecurity awareness training content to each employee's role, so finance teams practice wire fraud while executives practice deepfake recognition.
How a Cybersecurity Awareness Training Program Works
A modern cybersecurity awareness training program runs as a continuous lifecycle rather than a one-time event. It moves from roster setup and risk baselining through multi-channel phishing simulations, just-in-time microlearning, role-specific cybersecurity awareness training campaigns, and automated remediation that adjusts without manual intervention. The design principle that separates effective cybersecurity awareness training from compliance checkboxes is spaced learning: distributing reinforcement across repeated touchpoints over time produces measurably better retention than a single annual session.
1. Sync the Employee Roster and Establish a Cybersecurity Awareness Training Risk Baseline
Every cybersecurity awareness training program starts with knowing who needs training and what specific risks they carry. Modern cybersecurity awareness training platform software connects directly to Microsoft 365, Google Workspace, or HRIS systems via SCIM provisioning to automatically sync employee rosters, eliminating manual uploads and stale lists.
Simultaneously, an OSINT profiling engine evaluates publicly available data to quantify each employee's exposure: their LinkedIn role, the executive content they appear in, and the data points cyberattackers could weaponize against them. This baseline defines which phishing simulations to run and which employees need urgent attention.
2. Launch Multi-Channel Phishing Simulations
With the roster live and risk data in place, the cybersecurity awareness training program begins running phishing simulations across every channel cyberattackers actually use: email, voice (vishing), SMS (smishing), and deepfake video. Each phishing simulation mirrors real cyberattack patterns including spoofed executive personas, OSINT-informed spear phishing, and BEC scenarios targeting finance teams.
The metrics that matter go beyond whether someone clicked. Effective cybersecurity awareness training platform software measures click-through rates, credential submission rates, and whether the employee reported the phishing simulation as suspicious; reporting behavior is the clearest signal of genuine vigilance.
3. Deliver Just-in-Time Microlearning Within the Cybersecurity Awareness Training Flow
When an employee fails a phishing simulation, the ideal cybersecurity awareness training moment is immediate. Just-in-time microlearning delivers a brief, targeted module the moment after failure, while the experience is fresh and the lesson is most likely to stick.
A compliance program measures whether an employee completed a module; a behavior-change cybersecurity awareness training program measures whether that employee responds differently the next time a real cyberattack arrives. Modules under 10 minutes that connect directly to the cyberattack type the employee just encountered produce far stronger retention than annual slideshows consumed in bulk.
4. Run Ongoing Role-Specific Cybersecurity Awareness Training Campaigns
Phishing simulations test employees; structured cybersecurity awareness training campaigns build their skills between tests. Effective programs personalize content based on each employee's phishing simulation history, risk score, and job function, delivering relevant scenarios in preference to generic awareness slides.
According to research published in F1000Research on cybersecurity students, using spaced repetition and distributed practice together produced significantly higher concept retention than massed‑learning approaches. The study also found a statistically significant interaction effect between the learning‑strategy intervention and gender on concept retention, with a reported p‑value of 0.011. This makes cybersecurity awareness training scheduling as important as content design.
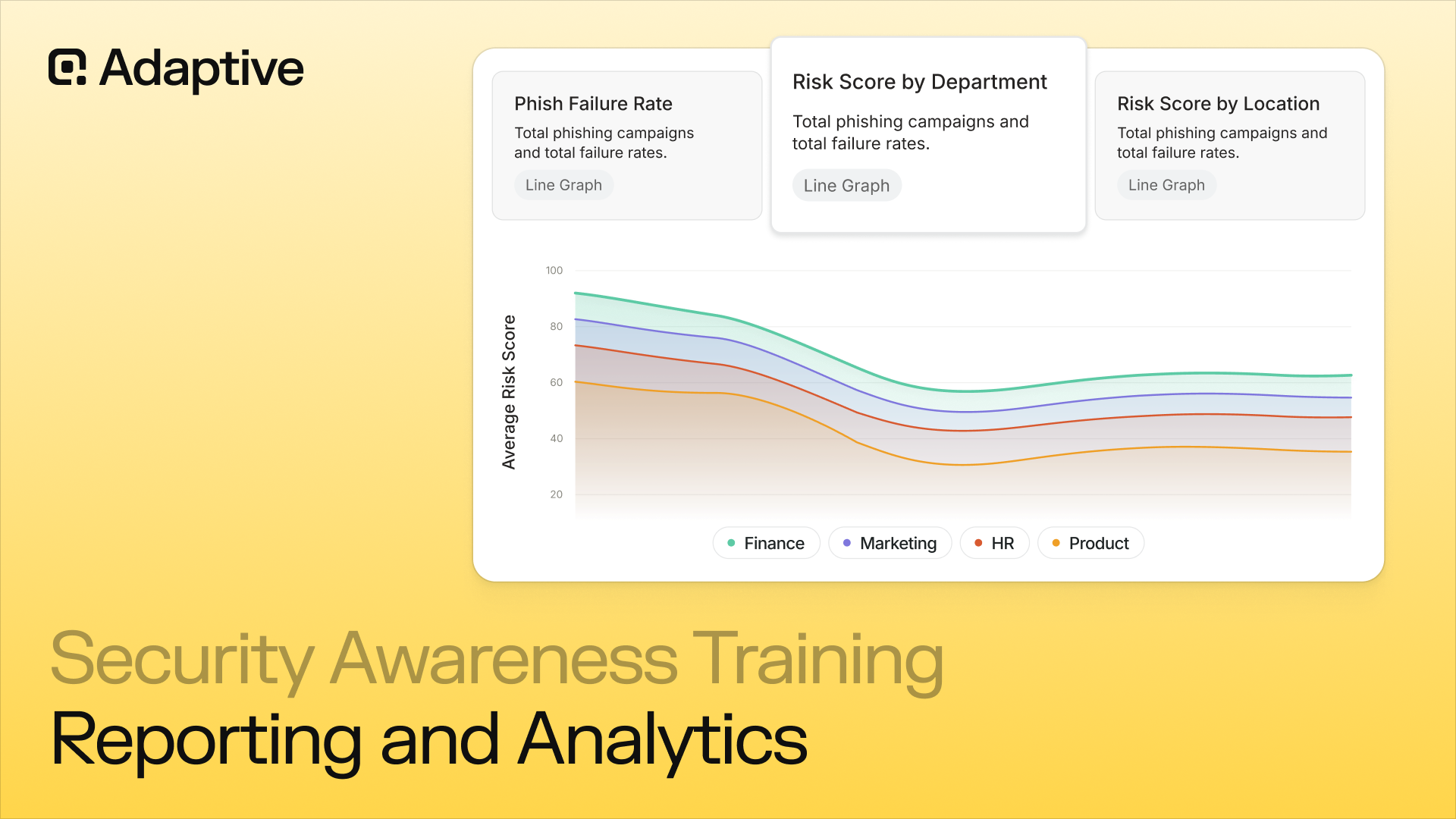
5. Track Cybersecurity Awareness Training Risk Scores Continuously
Measuring completion rates tells security leaders who sat through training; risk scoring tells them whether behavior changed. Modern cybersecurity awareness training platform software maintains dynamic risk scores at the individual, department, and organizational level, updated in real time as phishing simulation results, training completions, OSINT exposure changes, and credential breach history shift.
According to IBM's Cost of a Data Breach Report 2025, organizations now take an average of 241 days to identify and contain a breach, a nine-year low driven by faster detection. Continuous risk scoring helps accelerate detection by surfacing human-layer risk before it escalates into an incident.
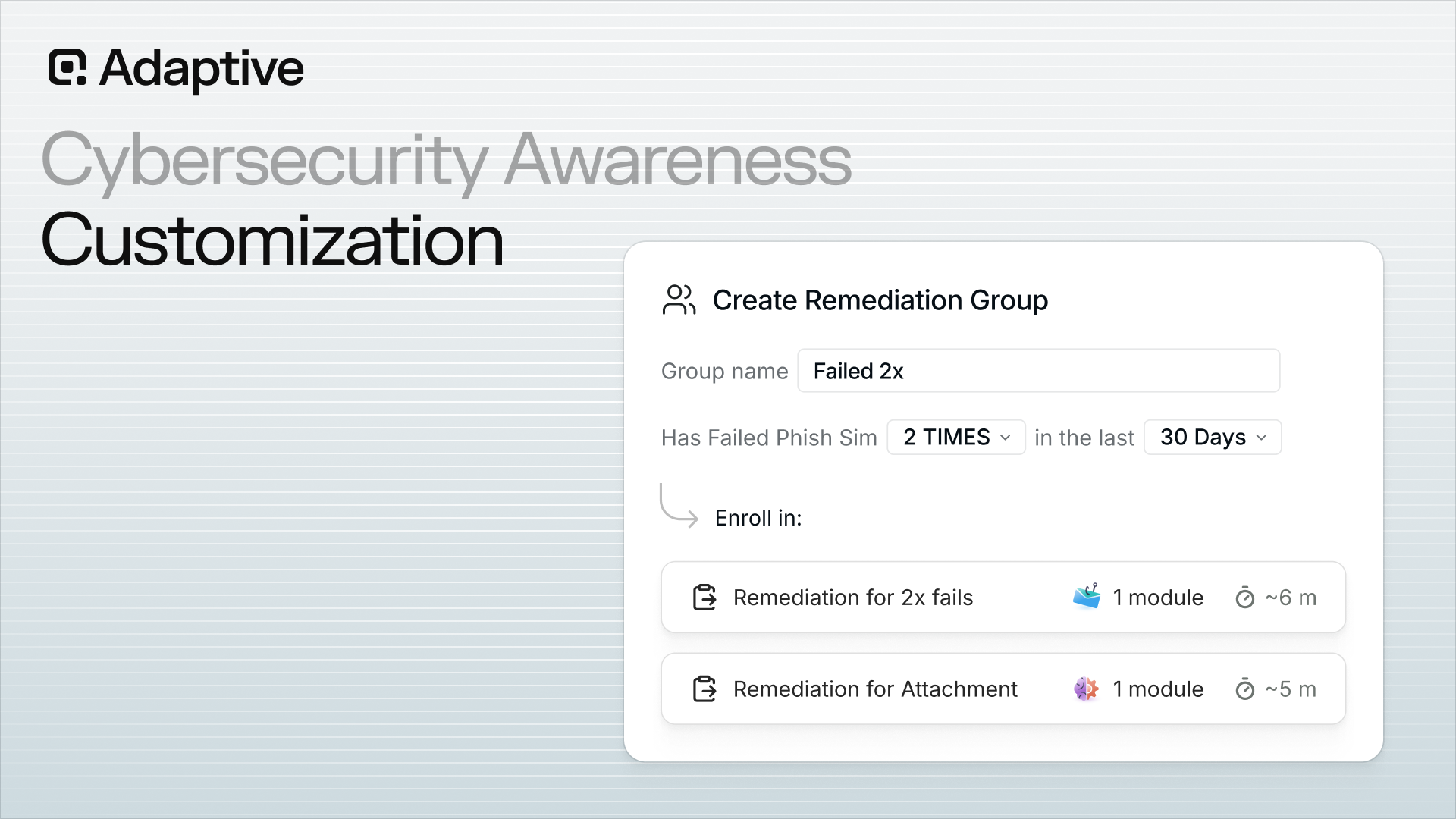
6. Automate Remediation for High-Risk Employees
The final stage of the cybersecurity awareness training lifecycle closes the loop without requiring analyst intervention for every at-risk employee. Automated remediation uses risk score thresholds to enroll high-risk individuals in targeted cybersecurity awareness training sequences, with no manual review required.
This is the operational difference between a modern cybersecurity awareness training program and a legacy compliance program: the cybersecurity awareness training platform acts on data automatically, before a security manager has to flag the issue manually.
Adaptive Security's Risk Monitoring and Mitigation capability turns every phishing simulation result into a personalized cybersecurity awareness training action.
Best Practices for Building an Effective Cybersecurity Awareness Training Program
Building an effective cybersecurity awareness training program requires securing leadership buy-in, baselining employee risk before designing content, and delivering phishing simulations and modules across the full cyber threat spectrum. The factor that most clearly separates cybersecurity awareness training programs that change behavior from those that check a compliance box is measurement of what changes, rather than who completed a module.
1. Secure Executive Sponsorship for Cybersecurity Awareness Training
Executive visibility determines whether cybersecurity awareness training is treated as a real organizational priority or ignored. Programs without visible leadership endorsement consistently produce lower completion rates and weaker behavioral change.
Route executive sponsorship through concrete actions: a recorded message from the CEO at program launch, visible leadership participation in phishing simulations, and security metrics included in all-hands reporting.
2. Baseline Risk Before Designing Cybersecurity Awareness Training Content
Cybersecurity awareness training content built without risk data misses the highest-risk employees entirely. Run a baseline phishing simulation and OSINT exposure assessment before designing a single module.
The results reveal which departments are most susceptible, which cyberattack channels pose the greatest risk, and which employees need immediate targeted intervention. This data becomes the foundation for every content and frequency decision that follows.
3. Simulate the Full Cyber Threat Spectrum in Cybersecurity Awareness Training
Email-only phishing simulations create a false sense of coverage. In 2026, cyberattackers operate across voice, SMS, and deepfake video; cybersecurity awareness training that stops at inbox testing leaves employees unprepared for vishing calls, smishing texts, and AI-generated executive impersonations.
Multi-channel phishing simulations replicating all four cyberattack channels are the only way to build recognition skills that hold up when cyberattackers switch methods.
4. Deliver Short, Role-Specific Modules
Bite-sized cybersecurity awareness training modules under 10 minutes drive measurably higher completion and retention than annual all-hands sessions. NIST SP 800-50r1, NIST's guidance on building cybersecurity learning programs, specifically recommends role-based training tailored to each employee's responsibilities.
A finance team member's risk profile looks nothing like a developer's, and cybersecurity awareness training content should reflect that. The closer the cybersecurity awareness training scenario mirrors real job context, the more durable the behavior change.
5. Trigger Microlearning Immediately After Phishing Simulation Failures
The most effective teaching moment is the one immediately following a mistake. Just-in-time microlearning, delivered within seconds of clicking a simulated phishing link, converts a failure into a learning event before the employee moves on to the next task.
Research in usable security suggests that cybersecurity awareness training is most effective when tied to real behavioral triggers and immediate feedback, rather than generic calendar‑based reminders. As noted by usable‑privacy and security researchers such as Dr. Lorrie Faith Cranor, training that intervenes at the moment of failure tends to produce stronger retention than one‑off scheduled instruction.
6. Use Positive Reinforcement, Not Shame

Every employee who fails a phishing simulation and receives constructive feedback becomes better at identifying real cyberattacks. Shame-based mechanics including public failure notices, punitive messaging, or score-shaming damage psychological safety and reduce voluntary engagement.
Leaderboards, recognition programs, and team-level progress tracking build competitive engagement that drives cybersecurity awareness training participation without penalizing honest mistakes.
7. Map Cybersecurity Awareness Training to Compliance Frameworks
The NIST Cybersecurity Framework 2.0 and CIS Controls both formally incorporate cybersecurity awareness training as a required organizational control. Cybersecurity awareness training content should be mapped to the specific frameworks an organization is accountable to: SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 each carry documented training requirements.
According to IBM's Cost of a Data Breach Report 2025, organizations using AI and automation extensively throughout security operations saved an average of $1.9 million per breach and reduced the breach lifecycle by 80 days, making the ROI case for an integrated cybersecurity awareness training platform with AI-driven automation concrete and defensible.
8. Align Frequency to Risk Level
Minimum compliance thresholds call for annual cybersecurity awareness training, but annual-only programs leave 11 months of exposure between reinforcements. Best practice is continuous phishing simulation with quarterly module refreshes, adjusted upward in frequency for high-risk roles such as finance, executives, and IT administrators.
Integrating cybersecurity awareness training into existing HR onboarding workflows and learning management systems removes adoption friction and ensures every new employee is trained before becoming a target.
Adaptive Security builds cybersecurity awareness training programs around best practices that change behavior, in preference to filling audit checkboxes.
How to Measure Cybersecurity Awareness Training Effectiveness
Measuring cybersecurity awareness training effectiveness means tracking the right behavioral metrics over time, calculating ROI against industry breach cost baselines, and translating technical data into board-ready risk language. Measurement data is increasingly a business asset for cyber insurance underwriting and regulatory audits, rather than only an internal management tool.
1. Define the Core Behavioral KPIs of Cybersecurity Awareness Training
Seven metrics define a complete picture of cybersecurity awareness training effectiveness:
- Phishing simulation click-through rate, the percentage of employees who clicked a simulated phishing link;
- Credential submission rate, the subset who entered credentials after clicking;
- Phishing reporting rate, the employees who correctly flagged a simulated cyberattack;
- Cybersecurity awareness training module completion rates by department and role;
- Mean time to report a suspicious email;
- Employee risk scores at both individual and organizational levels, ideally trending downward across each cycle;
- Reduction in real-world security incidents attributable to human error.
2. Calculate Cybersecurity Awareness Training ROI Against Breach Cost
ROI calculation requires one core formula: compare the annual cost of the cybersecurity awareness training program against the statistical reduction in breach probability, multiplied by the industry-specific average breach cost. According to IBM's Cost of a Data Breach Report 2025, phishing remained the most common initial attack vector at 16% of breaches, with an average cost of $4.8 million per incident, making any cybersecurity awareness training investment that measurably reduces phishing susceptibility directly defensible to a CFO or board.
3. Build Board-Ready Cybersecurity Awareness Training Risk Dashboards
Security leaders who present raw click-through percentages to boards fail to land the message. For example, an '18% click rate on executive impersonation phishing simulations' can be reframed as 'nearly one in five employees would have exposed credentials in a deepfake CFO cyberattack."
Effective board reporting frames metrics as business risk statements; "employee susceptibility to executive impersonation cyberattacks dropped 40% in Q2" communicates both the cyber threat and the trajectory in language executives act on. Platforms with human risk scoring dashboards surface department-level and individual-level trends in plain-language formats.
4. Treat Cybersecurity Awareness Training Documentation as a Business Asset
Cyber insurance providers increasingly require evidence of cybersecurity awareness training effectiveness as part of the underwriting process. Underwriters want documented proof that employees are measurably less susceptible over time, in preference to confirmation that a program exists.
Organizations with well-documented cybersecurity awareness training metrics, including declining click rates, improving reporting rates, and consistent completion records, have a tangible advantage at renewal. Measurement documentation belongs in the audit file alongside compliance records as evidence of due diligence.
5. Acknowledge Cybersecurity Awareness Training Measurement Challenges Honestly
Three obstacles reliably undermine cybersecurity awareness training measurement programs. Low employee engagement produces skewed completion rates that mask actual skill gaps, while isolating training's specific contribution to risk reduction is genuinely difficult given the many variables that influence breach rates.
According to CrowdStrike's 2025 Global Threat Report February 2025, 79% of detections were malware-free, meaning identity-based and social engineering cyberattacks now dominate the threat surface; this shift makes static cybersecurity awareness training libraries obsolete faster than annual update cycles can address. These challenges do not invalidate measurement; they sharpen the argument for continuous, adaptive cybersecurity awareness training that updates phishing simulation scenarios in real time.
Adaptive Security translates cybersecurity awareness training signal into the board-ready risk language that security leaders need at every quarterly review.
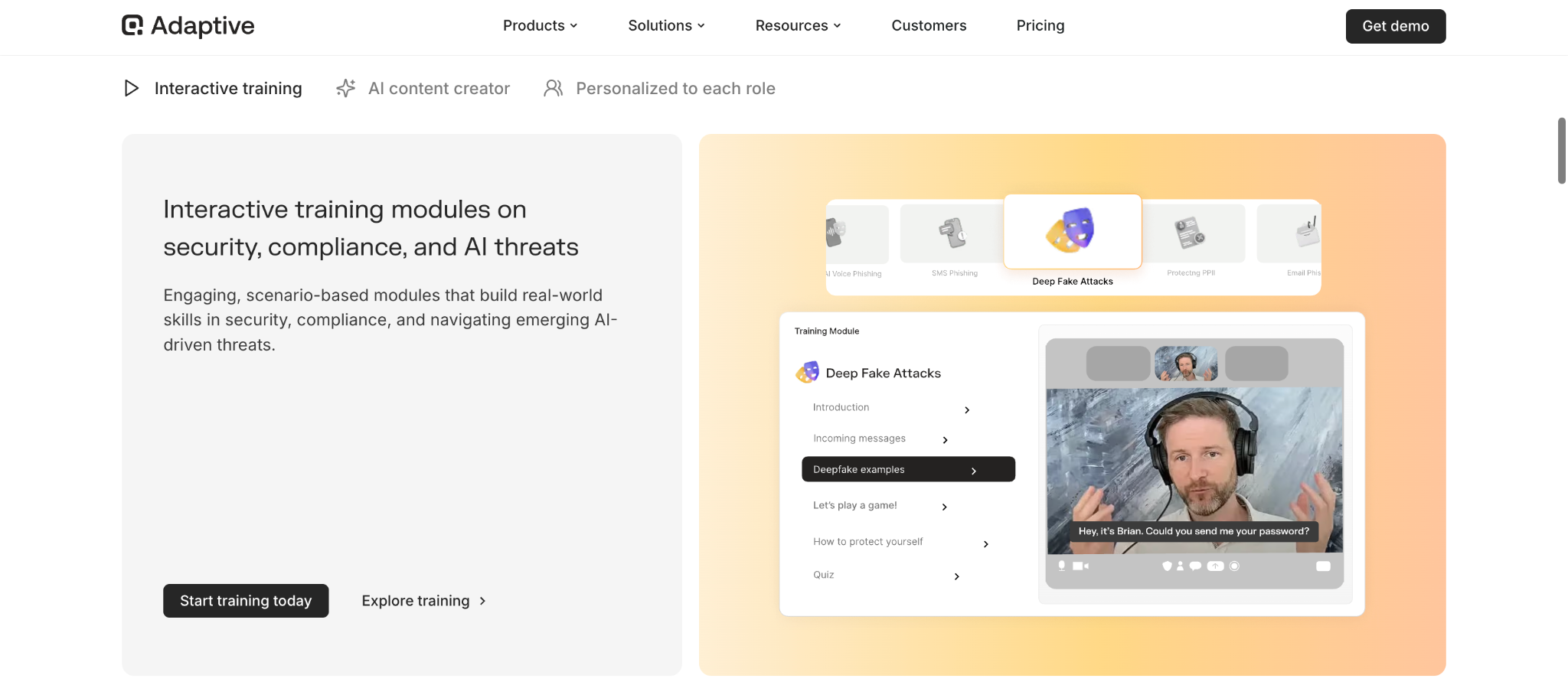
Adaptive Security: A Cybersecurity Awareness Training Platform Built for the AI Era
Adaptive Security is a cybersecurity awareness training platform built specifically for the cyber threat environment that emerged after generative AI made deepfakes, voice cloning, and OSINT-personalized spear phishing accessible to every cyberattacker. Legacy cybersecurity awareness training vendors retrofitted email phishing simulation tools onto compliance content libraries built for a pre-2023 world; Adaptive Security was engineered from the start to address the multi-channel, AI-generated cyberattacks that now produce the majority of high-value fraud incidents.
[alt text: Adaptive Security's cybersecurity awareness training platform was built specifically for the cyber threat environment of the future]
The cybersecurity awareness training platform integrates four capabilities that legacy programs typically deliver separately or not at all. Multi-channel phishing simulations cover email, voice, SMS, and deepfake video in a single interface, replicating how real cyberattacks unfold in coordinated sequences. OSINT profiling evaluates each employee's public exposure to personalize phishing simulation realism, matching cyberattacker methodology rather than relying on generic templates. Dynamic human risk scoring updates continuously as phishing simulation behavior, cybersecurity awareness training completion, and credential breach exposure shift, surfacing the specific employees who need immediate intervention. According to IBM's Cost of a Data Breach Report 2025, 16% of breaches studied involved cyberattackers using AI tools, most often for phishing and deepfake impersonation, validating the need for cybersecurity awareness training that addresses these vectors directly.
The outcome focus separates Adaptive Security from compliance-first cybersecurity awareness training platform software. Automated remediation enrolls high-risk employees into targeted cybersecurity awareness training sequences without requiring analyst review, while board-ready reporting translates phishing simulation data into the risk language CFOs and audit committees actually use. The result is a cybersecurity awareness training program that measurably reduces susceptibility over time, produces audit-ready documentation for SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001, and gives cyber insurance underwriters the evidence they need at renewal.
Adaptive Security closes the gap between AI-powered cyberattacks and AI-powered cybersecurity awareness training, with full visibility into where organizational exposure lives.
Frequently Asked Questions About Cybersecurity Awareness Training
What is cybersecurity awareness training?
Cybersecurity awareness training is a structured program that teaches employees how to recognize and respond to cyber threats including phishing, social engineering, deepfake impersonation, vishing, and smishing. It targets behavioral change across the entire workforce in preference to building technical skills in IT professionals, and modern cybersecurity awareness training combines short-form interactive modules, multi-channel phishing simulations, and just-in-time remediation triggered by real behavior. The goal is measurable, sustained behavior change that reduces an organization's human-layer risk.
What is the difference between cybersecurity awareness training and technical security certifications?
Cybersecurity awareness training targets every employee and focuses on behavior change including recognizing cyber threats, reporting incidents, and avoiding social engineering. Technical certifications such as CISSP, CEH, or CompTIA Security+ are designed for security professionals who build and operate security infrastructure. Cybersecurity awareness training does not require technical backgrounds and is typically delivered in modules under ten minutes; certifications involve deep technical curricula and formal assessments. Both matter to organizational security, but they serve entirely different audiences and objectives.
Who should receive cybersecurity awareness training?
Every employee should receive cybersecurity awareness training, not only IT staff. Cyberattackers target the path of least resistance, which is often finance teams (for business email compromise), HR departments (for credential harvesting), executives (for deepfake and spear phishing), and remote workers operating outside the corporate network perimeter. Role-based cybersecurity awareness training ensures each employee group practices against the scenarios most likely to target them.
How often should employees complete cybersecurity awareness training?
Annual cybersecurity awareness training satisfies minimum compliance requirements under frameworks including HIPAA and PCI-DSS, but annual-only programs do not change behavior at scale. Knowledge retention declines sharply within weeks of a single session. Best-practice cybersecurity awareness training programs run continuous phishing simulations year-round, deliver quarterly module refreshes, and trigger just-in-time microlearning immediately after a failed phishing simulation. Frequency should scale upward for employees with access to financial systems, sensitive data, or executive communications.
What topics should a cybersecurity awareness training program cover in 2026?
Cybersecurity awareness training in 2026 must cover phishing across all channels (email, SMS, voice, and QR code), social engineering tactics including pretexting and BEC, password hygiene and multi-factor authentication, data handling and privacy obligations, physical security, and incident reporting procedures. Cybersecurity awareness training must also address AI-era cyber threats: deepfake video and voice impersonation, OSINT-personalized spear phishing, and coordinated multi-channel cyberattacks combining smishing and vishing. Content libraries built before 2023 do not cover these categories adequately.
How have AI-generated deepfakes changed cybersecurity awareness training requirements?
AI-generated deepfakes have transformed social engineering from a recognizable cyber threat into a near-undetectable one, requiring cybersecurity awareness training programs to teach employees an entirely new recognition skill set. The $25 million wire fraud executed against engineering firm Arup using a deepfake video call of its CFO is now the benchmark for why deepfake scenarios must appear in every active phishing simulation library. Cybersecurity awareness training that addresses only email-based cyberattacks leaves employees unprepared for the dominant attack vectors in use today.
What is the difference between compliance-only training and a behavior-change cybersecurity awareness training program?
A compliance-only approach measures module completion rates and checks a regulatory box; it does not measure whether employees actually respond differently to real cyber threats. A true behavior-change cybersecurity awareness training program tracks phishing simulation click-through rates over time, monitors credential submission rates, measures how quickly employees report suspicious messages, and delivers targeted remediation based on individual risk signals. Compliance programs are annual, generic, and passive; behavior-change cybersecurity awareness training is continuous, role-specific, and adaptive.
How do organizations measure the effectiveness of cybersecurity awareness training?
Primary metrics for measuring cybersecurity awareness training effectiveness are phishing simulation click-through rate reduction over time, credential submission rate trends, phishing reporting rate, completion rates by department, mean time to report a suspicious message, and individual employee risk score improvement. Boards need these translated into business language, such as "executive impersonation susceptibility dropped 38% in Q3," in preference to raw click-through percentages. The SANS Institute Security Awareness Program Benchmarks provide industry-standard baselines for each of these cybersecurity awareness training metrics.
How does cybersecurity awareness training support GDPR, HIPAA, SOC 2, and PCI-DSS compliance?
Each major compliance framework explicitly requires documented cybersecurity awareness training for the workforce. HIPAA's Security Rule mandates workforce security training and periodic reminders. PCI-DSS Requirement 12.6 requires formal cybersecurity awareness training programs with annual training for personnel with access to cardholder data. GDPR Article 39 and its associated guidance from the European Union Agency for Cybersecurity (ENISA) require organizations to train staff in data protection obligations. SOC 2 Trust Services Criteria CC1.4 and CC2.2 require demonstrated security awareness activities. Cybersecurity awareness training completion records and phishing simulation logs serve as audit evidence across all four frameworks.
What are phishing simulations and how are they used in cybersecurity awareness training programs?
Phishing simulations are controlled, realistic attack scenarios delivered to employees through the same channels real cyberattackers use, including email, SMS, voice, and deepfake video, to measure and improve susceptibility before an actual cyberattack occurs. In a cybersecurity awareness training program, phishing simulations establish a behavioral baseline on day one, then run continuously to track improvement. Employees who click a simulated link receive immediate just-in-time microlearning explaining what they missed. Phishing simulation data feeds individual risk scores and drives automated remediation, replacing guesswork with real behavioral evidence.
What is the difference between cybersecurity awareness training and human risk management?
Cybersecurity awareness training is a component of human risk management. It delivers content and measures completion. Human risk management (HRM) encompasses the full lifecycle: identifying individual risk through OSINT profiling and phishing simulation behavior, delivering personalized cybersecurity awareness training based on that profile, automating remediation for high-risk employees, and producing continuous reporting that ties security investment to measurable behavior change over time.
Adaptive Security operates as the cybersecurity awareness training platform where every employee becomes a measurable, tracked, and improving line of defense.
Key Takeaways
- Cybersecurity awareness training is the structured, continuous program that teaches employees to recognize and respond to phishing, social engineering, deepfake impersonation, and AI-generated cyberattacks across every channel;
- Modern cybersecurity awareness training targets sustained behavioral change in every employee through interactive modules, multi-channel phishing simulations, and just-in-time remediation;
- The cyber threat landscape has shifted decisively toward AI-generated social engineering, and a cybersecurity awareness training program built before 2023 leaves multiple cyberattack channels unaddressed;
- A complete cybersecurity awareness training program covers phishing recognition, social engineering defense, password hygiene, data handling, physical security, and incident reporting;
- Effective cybersecurity awareness training runs as a continuous lifecycle: roster sync, risk baselining, multi-channel phishing simulations, just-in-time microlearning, role-specific campaigns, continuous risk scoring, and automated remediation;
- Role-based cybersecurity awareness training outperforms generic content because finance, executives, IT, and HR each face fundamentally different cyberattack profiles;
- Measurement is the difference between cybersecurity awareness training that changes behavior and cybersecurity awareness training that checks a compliance box;
- Compliance frameworks including SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 require documented cybersecurity awareness training, and cyber insurance underwriters increasingly factor it into premium decisions;
Adaptive Security closes the gap between AI-powered cyberattacks and the cybersecurity awareness training every workforce needs to recognize them at the moment.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents