Security awareness training (SAT) platform customization is the practice of configuring a SAT platform to match an organization's specific threat profile. Regulatory requirements are a key driver for customization, as organizations must ensure their training aligns with industry standards and legal mandates.
This guide is written for security leaders, IT managers, and compliance officers who need to evaluate, configure, and continuously improve a customized SAT program. It will cover the full scope of customization decisions, including:
- Building role-based learning paths and dynamic segmentation
- Designing phishing simulations across email, vishing, smishing, and deepfake channels
- Mapping training content to frameworks such as SOC 2, HIPAA, and PCI-DSS, with a focus on data protection as a core compliance and training objective
- Using AI-generated modules to close content gaps without instructional design overhead
This guide also identifies which customization capabilities to prioritize, how to structure a program that satisfies auditors and reduces click rates, and how to measure whether configuration decisions are producing measurable behavioral outcomes.
Organizations seeking a fully customizable security awareness training platform are encouraged to explore the Adaptive Security demo to see how it adapts to the organization and the individual users.
What Is Security Awareness Training Platform Customization?
Security awareness training platform customization refers to the process of tailoring a SAT platform's content, simulations, delivery schedule, branding, and reporting to align with an organization's unique threat landscape, workforce composition, and compliance obligations, rather than implementing a one-size-fits-all program designed for a broad audience.
By enabling organizations to address their specific risks and user profiles, customization directly improves a company's security posture by reducing human error and aligning employee behavior with security best practices. It operates across two distinct dimensions.
Platform-level customization governs how training is delivered and to whom, through administrative configuration of settings, integrations, user provisioning, branding, and delivery rules.
Content-level customization determines what employees learn, through modified training modules, phishing templates, landing pages, and quizzes.
These dimensions are not interchangeable. Reconfiguring delivery rules without updating content still exposes employees to scenarios that bear no resemblance to the attacks targeting their roles, industries, or organizations. Customization is the mechanism that converts a compliance checkbox into a program that produces measurable behavioral change.
Why the Two-Dimension Distinction Matters
Platform-level and content-level customization address different problems, and conflating them produces programs that appear complete on paper but fail in practice.
An administrator can configure automatic enrollment, schedule quarterly delivery, and apply company branding, but if the underlying content depicts a generic executive requesting a wire transfer with no organizational context, a finance employee at a healthcare company will not recognize the scenario as realistic. The result is training that is completed and immediately forgotten.
Content-level customization closes that gap by ensuring scenarios reflect the actual attack patterns employees face. A spear phishing template built on open-source intelligence (OSINT), including publicly available employee data from LinkedIn, company websites, and social media, is considerably more effective than one built for a hypothetical organization because it mirrors what a real attacker would send.

[alt text: Security awareness training platforms adapt not only the platform but the content itself, providing users with the kind of personalized phishing simulations that real attackers employ.]
Off-The-Shelf SAT Programs and the Generic Content Problem
Off-the-shelf SAT programs use industry-agnostic content designed to satisfy the most common compliance frameworks across the widest possible customer base. That breadth is a structural limitation, as different organizations face distinct challenges.
For instance, a healthcare organization faces HIPAA-specific social engineering scenarios, including attackers impersonating insurance vendors, regulators, or patient portals, that a financial services firm or SaaS company never encounters. Running the same phishing test and simulation template across both industries trains employees to recognize the wrong threats.
Customization corrects this by aligning simulation themes, industry language, sender personas, and module content with the specific context in which employees operate every day.
Incorporating role-based training paths ensures that employees receive relevant, actionable guidance.
Security Awareness Training Platform Customization: Content
Security awareness training platform customization allows security teams to shape every layer of content, from individual training modules to simulation pretexts to landing-page feedback.
This includes the ability to deliver interactive training experiences, such as gamified modules, real-world attack simulations, and multimedia content, that drive user engagement and knowledge retention.
The range of available customization options directly determines whether employees encounter generic content or scenarios that reflect the attacks targeting their specific role, industry, and organization.
What Are Custom Training Modules, and How Does SCORM Import Work?
Organizations with existing policy documentation, proprietary videos, or internally authored courses can import that content directly into their SAT platform through SCORM-compliant module import.
SCORM (Sharable Content Object Reference Model) is the de facto technical standard for eLearning interoperability, governing how packaged course content communicates completion and scoring data back to any compatible platform.
In practice, a compliance team that has already built a secure data-handling course can import it without having to rebuild existing content. SAT platforms should also support integration with existing corporate learning management systems (LMSs) to facilitate seamless deployment and tracking of training effectiveness.
How Does AI-Generated Module Creation Change the Content Process?
AI content engines eliminate the instructional design bottleneck that historically made custom module creation a months-long project. Security teams can now describe a threat scenario and receive a structured, quiz-inclusive module ready for deployment. This capability is most consequential for fast-moving threat categories where pre-built content libraries are already outdated by the time employees encounter them.
Adaptive Security's AI Content Studio generates role-specific training modules from a plain-language prompt or an uploaded policy document in minutes.

How Do Custom Phishing Simulation Templates Improve Training Outcomes?
Custom phishing simulations allow security teams to build branded sender domains, realistic pretexts, and landing pages that mirror the vendor communications and executive personas employees recognize.
When an employee clicks, the custom landing page delivers immediate, context-specific feedback, providing a precise explanation of the indicators missed rather than a generic failure notification.
This point-of-failure education moment represents the highest retention interval in any training program, as employee attention is captured at the moment of greatest relevance.
Phishing simulations can span multiple attack vectors, including email phishing, spear phishing, vishing (voice phishing), and smishing (SMS phishing), each targeting employees through distinct channels.
Which Security Awareness Training Platform Customization Options Support Global and Industry-Specific Workforces?
Multilingual support and industry-specific scenario libraries address two distinct gaps that generic content cannot close. Leading platforms support multiple languages, and effective localization extends beyond translation to include region-specific threat scenarios.
For instance, a wire fraud pretext that resonates with employees in the United States does not automatically translate to teams in Germany or Singapore.
Delivering content at this level of specificity, however, represents only half of the equation. Ensuring that the right employee receives the right content at the right moment is where most programs break down.
Security Awareness Training Platform Customization: Phishing Simulations
Phishing simulations represent the point at which security awareness training converts into measurable behavior change. Effective customization requires configuring each channel independently:
- Email simulations using open-source intelligence (OSINT) and real vendor relationships
- Voice simulations using AI-cloned executive personas
- SMS simulations referencing actual internal systems
- Deepfake video simulations built around named organizational leaders.
Each channel requires its own setup logic, and simulation data that does not produce a change in behavior indicates a configuration that is not performing as intended.
1. Customize Email Phishing Simulations With OSINT and Organizational Context
Generic phishing templates are ineffective because employees recognize them as tests. OSINT-informed email simulations draw on publicly available employee data, LinkedIn profiles, published email signatures, and press coverage to construct pretexts that reference roles, projects, and relationships, mirroring actual threat scenarios.
An employee who receives a vendor impersonation email referencing their genuine accounts payable workflow cannot easily dismiss it as irrelevant or as a scam.
Configurable elements include:
- Sender domains that match real organizational communications
- Business email compromise (BEC) scenarios built around the organization's actual vendor list
- QR code phishing templates delivered in contexts employees already trust, such as onboarding packets or HR announcements
According to the Palo Alto Unit 42 Global Incident Response Report 2026, 65% of initial access is driven by identity-based techniques, such as social engineering and credential misuse, making OSINT-informed simulation the most direct preparation available for real-world threats.
2. Configure Voice (Vishing) Simulations Using AI-Cloned Executive Personas
Vishing simulations require a distinct configuration layer compared to email-based simulations. On vishing, the core customizable element is the voice persona, with additional configurations, such as:
- AI-cloned audio of company executives is constructed from publicly available recordings, including earnings calls, conference appearances, and corporate videos
- Scripts are configured to reference internal systems, active projects, and known organizational processes, eliminating the contextual gaps that allow employees to identify a fabricated call
- Call routing, scenario framing, and urgency escalation are all adjustable to address a wide range of social engineering narratives
These simulations expose employees to realistic social engineering tactics, including manipulation, impersonation, and psychological pressure, that adversaries employ in vishing attacks.
Multi-channel phishing simulations that incorporate voice place employees within the exact pressure conditions that vishing attacks exploit, in a controlled environment, before an actual attack occurs.
3. Set Up SMS (Smishing) Simulations Referencing Internal Systems
Smishing simulations succeed when the message content matches the cadence and vocabulary of internal communications employees already receive.
To accomplish this, configurations such as custom sender IDs allow simulations to appear as IT, HR, or a known vendor. Additionally, message templates reference real system names, the identity provider employees log into daily, the company-wide payroll platform, or the scheduling tool the operations team relies on.
As part of comprehensive phishing tests and simulated attack exercises, the link destination configuration determines whether employees are directed to a credential-harvest page, a QR code, or a fake login portal that captures click data without exposing real credentials.
4. Deploy Deepfake Video Simulations of Company Executives
Deepfake video simulations are among the highest-fidelity tests available within a security program. Configurable elements include:
- The executive persona is constructed from publicly available video
- The message script is tailored to a specific business scenario, such as a wire transfer approval or a data access request
- The delivery context is sent via a calendar invite, a platform message with a video link, or a simulated all-hands recording.
Defined safeguards govern this capability: simulations are restricted to named executives who have provided consent per the platform configuration; all sessions are logged; and no synthetic media is generated outside the simulation environment.

Deepfake simulation is one of the largest training gaps in organizations still running email-only programs. An employee who has never encountered a synthetic video of their own CEO has no frame of reference when one arrives in their inbox.
5. Measure Whether Simulation Customization Is Working
Customization yields value only when its effect on behavior is measurable, with relevant metrics including click rates by simulation type, time-to-report following a simulated attack, and changes in individual risk scores tracked across successive simulation rounds.
A well-configured program shows declining click rates on OSINT-informed email templates and increasing report rates on vishing and smishing simulations as employees build channel-specific detection skills.
These behavioral signals are essential for tracking employee performance and identifying content gaps that training modules, policies, and automated reinforcement workflows must address.
Security Awareness Training Platform Customization: Analytics and Reporting
Security awareness training platform customization also determines whether a program generates evidence of behavioral change or merely completion records.
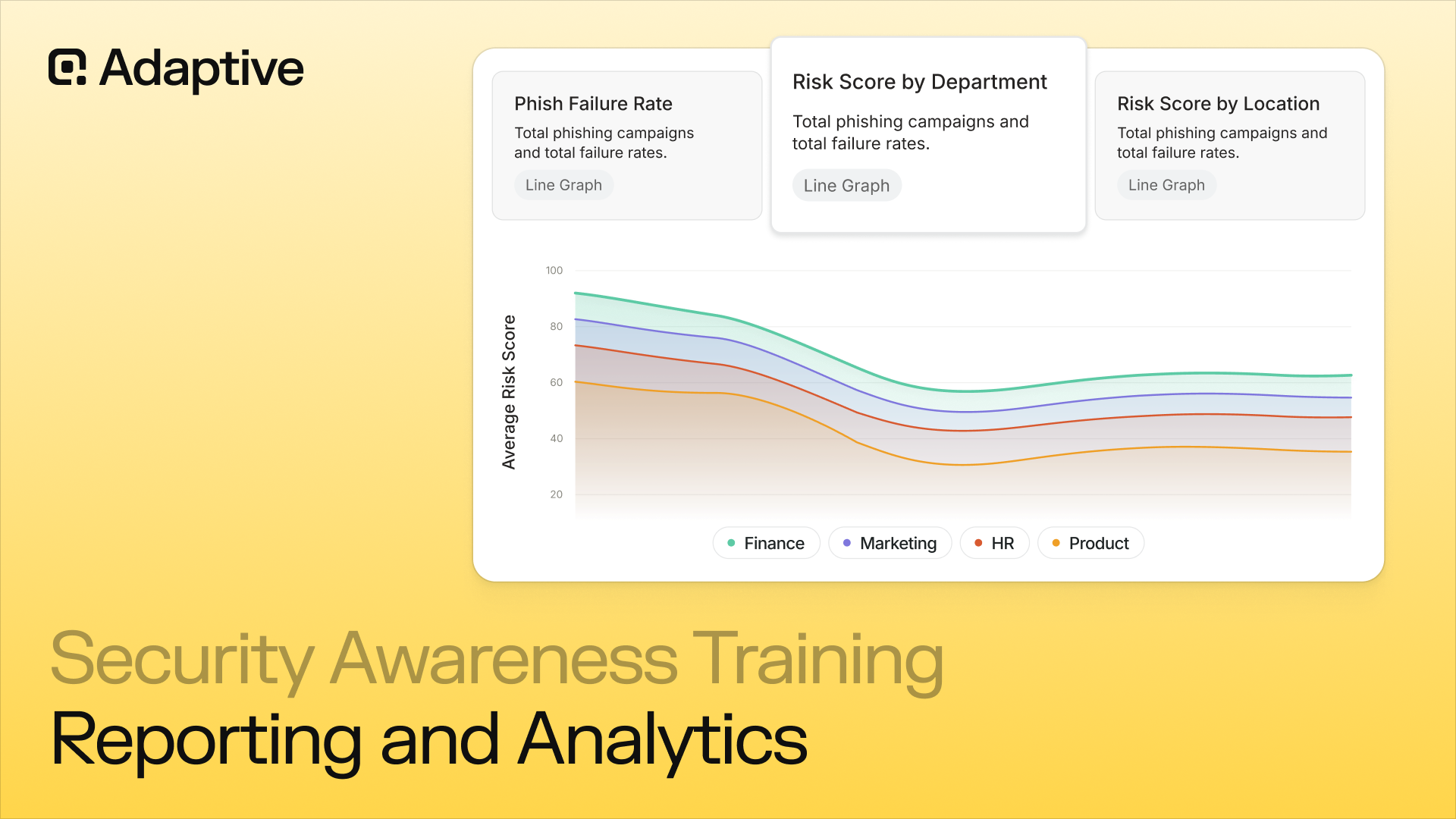
Effective analytics customization requires configuring dashboards for distinct audiences, defining KPIs that reflect real risk reduction, and building automated reporting schedules that keep stakeholders informed without manual effort.
Key metrics include the ability to track employee performance and assess user risk, enabling organizations to monitor behavior, identify vulnerabilities, and reduce the likelihood that human error contributes to security breaches. The critical discipline throughout is separating meaningful behavioral signals from activity metrics that appear reassuring but lack demonstrable value.
AI-driven analytics in security awareness training platforms can track user engagement and performance, enabling organizations to measure the effectiveness of their training programs and adjust strategies accordingly.
1. Configure Dashboards for Each Audience
Board-level reporting requires entirely different framing than a security operations dashboard. Executives need risk trend lines, department-level exposure scores, user risk scores, and comparisons against prior quarters, not raw click-through percentages. Security operations teams need granular data, including phishing simulation click rates by role, repeat-failure patterns by individual, and training completion rates by cohort.
Configuring separate views for each audience ensures every stakeholder sees the signal most relevant to their decision-making, reducing the risk that critical exposure data is obscured by less relevant information.
2. Define KPIs That Reflect Behavioral Outcomes
Generic completion rates indicate whether employees opened a module, not whether their behavior changed. Meaningful KPIs for a customized program include:
- Phishing simulation click rates broken down by department and role
- Knowledge assessment scores tracked across training cohorts over time
- User progress metrics that monitor how employees engage with and improve throughout the training
- Risk score trends at the individual and team level
- Repeat-failure rates that identify employees who require additional intervention
Tracking user progress over time is essential for measuring the impact of training. Each metric connects directly to a security outcome: a declining click rate signals genuine risk reduction, while a plateau indicates that content or simulation design requires adjustment.
3. Validate Whether Customization Outperforms Generic Content
Customizing training content is only a justified investment if outcomes demonstrate superior results. With this objective in mind, organizations should run parallel tracking, measuring phishing click-through rates and post-training knowledge assessment scores separately for employees receiving customized content versus those assigned generic modules.
Robust reporting tools are essential for measuring and demonstrating the effectiveness of customized security awareness training, enabling organizations to track user engagement, compliance, and overall program success.
Without cohort comparisons and the insights provided by reporting tools, there is no way to verify that investment in personalization is producing superior behavioral outcomes. This data gap not only weakens internal justification but makes it impossible to demonstrate return on investment to boards or compliance auditors.

In the article The User is Not the Enemy: How to Increase Information Security Usability, Lorrie Faith Cranor, Professor at Carnegie Mellon University's CyLab Security and Privacy Institute, argues that security training is more effective when applied at a contextually relevant moment.
4. Automate Recurring Report Delivery
Configuring automated reporting schedules delivers the right data to managers, department heads, and board stakeholders at defined intervals, without relying on the security team's bandwidth.
Adaptive Security's reporting dashboards include 35+ dashboards with prebuilt reports that can route department-level summaries to line managers, compliance-mapped training records to GRC teams, and executive risk summaries to the board, all on automated delivery schedules requiring no manual intervention.
Risk score data, not training completion logs, is the meaningful unit of measurement for a modern security awareness training program, as completion percentages only confirm participation, while risk scores confirm behavioral change.
That distinction sharpens further when organizations examine which content formats are driving the greatest risk reduction among their highest-exposure employee cohorts.
Security Awareness Training Platform Customization: Role-Based Segmentation and Custom Learning Paths
Security awareness training platform customization follows one foundational principle: not every employee faces the same threats, and not every employee should receive the same training.
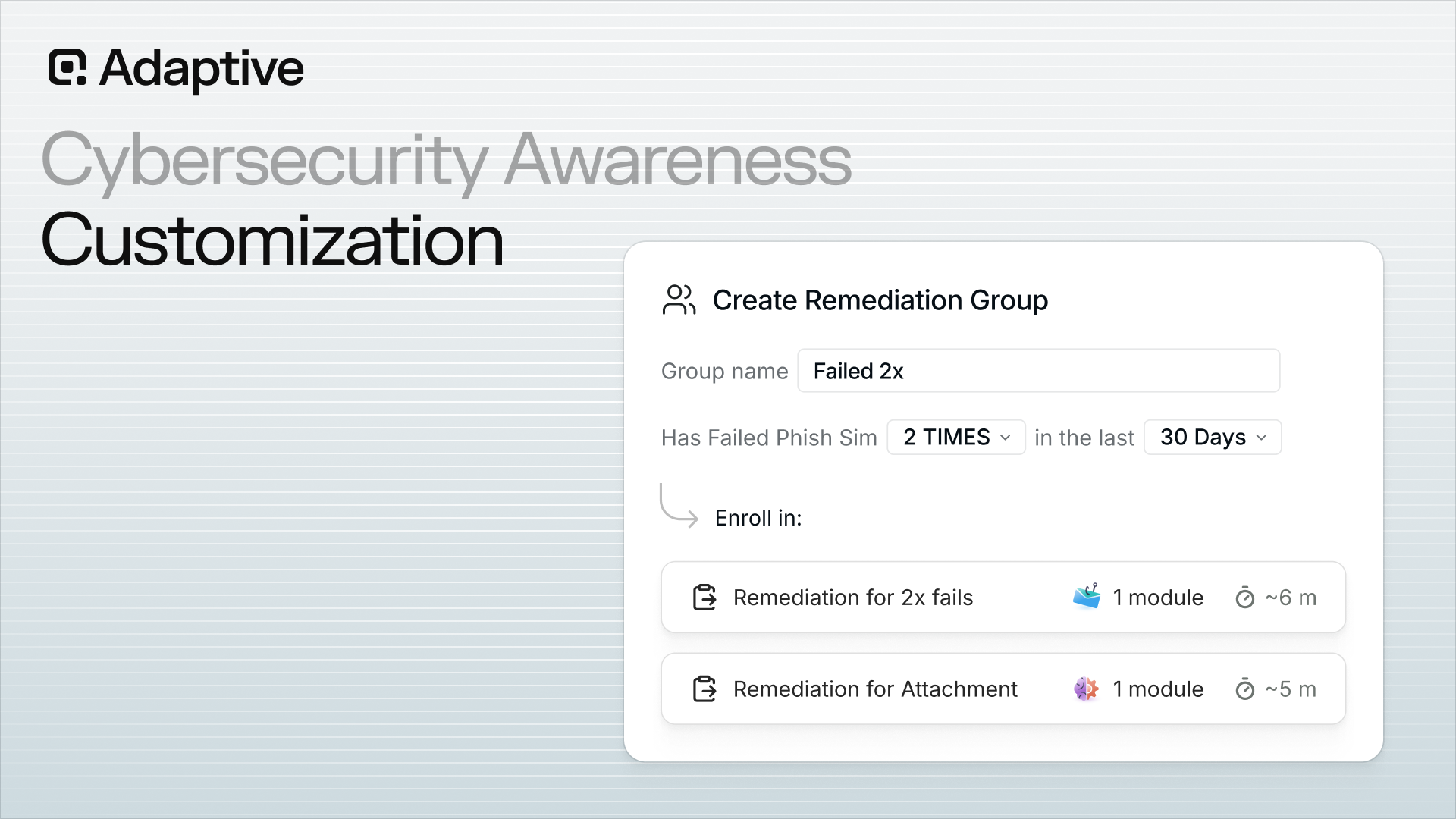
Modern platforms segment employees into dynamic cohorts, build tailored learning paths for each, and implement role-based training paths, structured programs designed for specific job functions, and supported by regular training campaigns and phishing simulations to enhance security awareness and ensure compliance.
These platforms progressively adjust simulation difficulty based on demonstrated performance. The final configuration layer, notification cadence, and delivery windows ensures training is delivered consistently without triggering the alert fatigue that causes employees to disengage. Segmentation, however, is only as reliable as the directory data feeding it.
1. Configure Smart Groups With Dynamic Segmentation
Dynamic groups are the structural backbone of any segmented training program. Administrators define group membership rules using attributes such as job title, department, geographic location, seniority level, user risk score, and HRIS data synced directly into the platform.
When an employee joins, changes roles, or departs, group membership updates automatically, eliminating manual list management and preventing stale cohorts from receiving incorrect content months after a role change.
The practical impact of this accuracy is significant. Voice phishing and email phishing collectively account for 17% of initial breach vectors, according to the Mandiant M-Trends 2026 Report, and attackers specifically tailor lures to job function, targeting finance teams with invoice fraud and executives with wire transfer requests. Dynamic segmentation ensures training mirrors that targeting precision.
Personalized, role-specific training has been shown to reduce human error in cybersecurity by ensuring employees receive targeted education that reflects the threats relevant to their specific functions.
2. Build Custom Learning Paths by Role
Administrators sequence training modules into ordered curricula, set prerequisites, and define completion windows aligned with each cohort's schedule and risk profile.
Role-specific training ensures that the finance team's curriculum prioritizes business email compromise (BEC) recognition and wire fraud verification protocols, executive tracks address deepfake video impersonation and vishing scenarios, and IT staff receive credential phishing and privilege escalation simulations.
Prerequisites serve an operational function: employees cannot advance to spear-phishing simulations without first completing foundational social-engineering modules, thereby closing knowledge gaps that attackers may otherwise exploit.
Effective personalized training programs use behavioral analytics to tailor content and simulations to each employee's specific needs and vulnerabilities, thereby strengthening overall security awareness.
3. Adjust Simulation Difficulty Based on Individual Performance
When an employee consistently passes baseline simulations, the platform automatically escalates the difficulty, progressing from generic credential phishing to open-source intelligence (OSINT)-personalized spear phishing that references the employee's LinkedIn title and employer.
Throughout this process, metrics such as user progress and risk scores are tracked to evaluate how individuals engage with training modules, respond to simulations, and develop security awareness over time.
Conversely, when an employee fails a simulation, that event triggers automatic enrollment in targeted remedial content, delivered within minutes of the failure, while the learning opportunity remains immediate.
Platforms that apply behavioral analytics adapt training content based on user performance and engagement, ensuring relevance and effectiveness over time.

4. Configure Notification Schedules and Training Cadence
Administrators control enrollment windows, reminder frequencies, and re-enrollment intervals independently for each segment. A high-risk finance team may receive monthly simulation cycles with 48-hour reminders, while a lower-risk operations cohort may train quarterly with a single notification at enrollment.
Aligning cadence to organizational culture prevents training from becoming background noise and sustains user engagement, ensuring employees remain attentive and responsive to security content.
Segmentation logic performs as designed only when the underlying employee data is accurate and continuously updated, a requirement that connects directly to how integrations and provisioning maintain system-wide consistency.
Organizations implementing security awareness training should measure user engagement and knowledge retention through regular testing and feedback mechanisms.
Security Awareness Training Platform Customization: Integrations, SSO, and SCIM
Connecting a security awareness training platform to HR and identity infrastructure enables program scalability without generating additional administrative overhead. For instance:
- Integrating HRIS systems enables user data to flow automatically into the platform
- Configuring SSO and SCIM manages the full employee lifecycle without manual input
- API-based workspace connections enable immediate deployment
For enterprise organizations managing thousands of users, each of these configuration decisions determines whether role-based learning paths execute automatically or depend on manually maintained records.
Seamless integration also supports audit readiness by ensuring that user provisioning, training assignments, and completion records are consistently tracked and readily accessible for compliance reviews.
Audit readiness is further supported by platforms that provide detailed reporting and documentation of training assignments and completion records, enabling organizations to demonstrate compliance during reviews.
1. Connect HRIS and Directory Systems to Automate User Provisioning
HRIS and Active Directory integrations eliminate the most common point of failure in enterprise security awareness training programs: the manual CSV upload. When third-party solutions feed employee records directly into the platform, training assignments automatically reflect the current organizational structure.
For instance, a new hire in the finance department receives finance-specific modules on the first day of employment, while a former employee no longer receives simulations or holds a license.
Enrollment records remain up to date without manual intervention, which is critical when auditors request documented proof of training participation and completion dates.
Robust reporting capabilities enable organizations to track, analyze, and demonstrate training effectiveness, user engagement, and compliance for audit requests and regulatory requirements.
2. Configure SSO and SCIM for Lifecycle Management and Audit Accuracy
Single sign-on (SSO) eliminates the separate login step that consistently contributes to training abandonment. When employees access the platform through the same identity provider used for all other work applications, completion rates increase as access friction is removed.
SCIM extends this capability by automating enrollment, profile updates, and deprovisioning in real time as HR systems change. Accurate enrollment records are not a convenience; they are essential for demonstrating compliance with regulatory requirements.
SOC 2, HIPAA, and PCI-DSS each require documented proof that specific employees completed specific training within defined timeframes, and SCIM-synced data provides that audit trail automatically.
Platform customization supports compliance with regulations relevant to an organization's operations, such as HIPAA or PCI-DSS, by aligning training initiatives with applicable governance and risk frameworks.
3. Deploy via Workspace API Integration
API-based integrations with widely adopted workplace platforms enable deployment without changes to MX records, eliminating the multi-week reconfiguration process that traditionally delays program rollouts. This approach compresses go-live timelines from weeks to minutes. Connecting to Microsoft 365 or Google Workspace via API enables automated security awareness training and phishing simulations, ensuring that simulations reach employees' inboxes and training modules appear in familiar environments from the first day of the program.
Adaptive Security's integrations architecture spans more than 325 tools across identity providers, HRIS, messaging, SIEM, and GRC systems.
4. Understand How Provisioning Configuration Controls Customization Scale
When user attributes flow automatically from HR systems, department, job title, location, and seniority level drive Smart Group logic without manual intervention. Role-based learning paths are assigned automatically, and high-risk employees are enrolled in remediation training without manual input.
Without this infrastructure, every customization decision becomes a manual task that must be executed and maintained. At 500 users, that overhead is manageable. At 5,000 users, it renders the program unworkable.
This integration layer enables content customization, role-specific modules, targeted simulations, training initiatives, and adaptive learning sequences to function as a unified system rather than a series of isolated configurations. The way this infrastructure routes simulations directly to employees' inboxes determines the overall effectiveness of phishing testing at scale.
Security Awareness Training Platform Customization: Branding, White-Labeling, and Multi-Tenant Configuration
Security awareness training platform customization at the identity and branding layer is more consequential than most security teams recognize.
The paper "Exploring the evidence for email phishing training: A scoping review" found that employees who perceive mandatory training as disconnected from their organization's culture are significantly less likely to engage with or complete it. The finding directly challenges the assumption that training content alone drives behavior change.
Branding configuration, notification design, and multi-tenant architecture all determine whether employees trust the program enough to participate fully. Effective awareness initiatives, encompassing training modules, simulations, and behavioral assessments, rely on this alignment to foster a security-conscious culture.
Security awareness training platforms offer diverse customization options to align with an organization's unique risks, brand identity, and technical environment.
How Does Branding Customization Affect Training Completion?
An employee who receives a training enrollment email from an unfamiliar domain, with no company logo, generic language, and a default color scheme, will likely treat it as a phishing attempt or disregard it entirely. This is an outcome that security programs cannot afford.
Effective branding customization applies the organization's logo, primary color palette, and verified email sender identity to every touchpoint, including enrollment emails, reminder notifications, escalation alerts to managers, and the training portal itself.
Custom notification templates extend this principle further. Security teams can configure the tone of automated reminders to match internal communication norms, whether a formal compliance directive or an informal nudge, and set escalation timing based on how aggressively the organization needs to close completion gaps.
Training that looks and feels like an authentic internal initiative earns the user engagement and participation that generic third-party tools consistently fail to generate. High user engagement is critical for measuring the effectiveness of security awareness programs and reducing cybersecurity risk.
How Does Multi-Tenancy Work for MSSPs and Resellers?
Multi-tenant platforms are well-suited for organizations managing multiple clients or business units with distinct security needs.
A properly configured security awareness training platform allows an MSSP to manage numerous client organizations from a single administrative portal, with tenant isolation ensuring that one client's data, simulations, and reporting remain inaccessible to another.
Co-branding capabilities allow MSSPs to deploy the platform under their own brand or the client's brand while maintaining centralized oversight.
The three configuration requirements that drive MSSP deployments are tenant isolation, client-specific reporting dashboards, and delegated administrator roles that allow client-side contacts to access their own data without exposing them to the broader environment.
Without these controls, service providers face both contractual liability and compliance exposure.
What Should SMBs Prioritize vs. Enterprise Organizations?
The configuration needs of a 75-person professional services firm and a 4,000-person financial institution are fundamentally different.
Small and medium-sized businesses benefit most from out-of-the-box branding templates and quick-launch programs that require minimal IT involvement, while deep API configuration eliminates the speed advantage that makes security awareness training accessible to smaller teams.
Enterprises require full API access, custom role hierarchies that reflect complex organizational structures, and deep HRIS integration to automate enrollment, offboarding, and department-level reporting.
Organizations should consider how customizable features, such as realistic simulations, behavioral insights, and analytics, can be tailored to their size and structure to effectively reduce human risk and improve organizational resilience.
Branding is the signal that tells every employee whether the training belongs to the organization or to a vendor. Programs that look and feel like authentic internal initiatives earn the attention that drives behavioral change, and behavioral change is the only outcome that reduces breach risk.
Security Awareness Training Platform Customization: Regulatory Compliance Requirements
For regulated organizations, security awareness training platform customization is the mechanism that connects training activity to documented, auditable compliance evidence and supports alignment with regulatory requirements.
Compliance auditors across every major framework now distinguish between generic annual training and content that demonstrably addresses the specific controls an organization is obligated to meet.
Customization ensures compliance with regulations relevant to an organization's operations, such as HIPAA or PCI-DSS. That distinction shapes audit outcomes, not training quality alone.
How Does Framework-Mapped Content Work in a SAT Platform?
Each compliance framework carries distinct control language that training content must address directly:
- SOC 2-mapped modules target access control awareness and incident response obligations
- HIPAA-mapped content addresses workforce training requirements under the Security Rule, specifically the need to protect electronic protected health information (ePHI) and ensure data protection as a core training objective
- PCI-DSS content covers cardholder data handling and phishing recognition for payment processing staff
- ISO 27001-aligned modules address information security policies and threat awareness under Annex A controls
- NIST CSF 2.0 (published February 2024) targets the Protect Function's Awareness and Training category (PR.AT)
- CMMC Level 1 and Level 2 training covers controlled unclassified information handling and workforce awareness requirements.
Using "maps to" language in documentation, rather than "certified for," helps keep compliance records accurate during audits.
What Compliance-Specific Configuration Options Matter Most?
Population-level configuration is the operational core of compliance customization:
- Healthcare organizations assign HIPAA modules as mandatory for all clinical and administrative staff
- Payment processing teams receive PCI-DSS content as a mandatory assignment, while other departments do not
- Completion deadlines can be aligned to audit cycles, quarterly for PCI-DSS, and annually for SOC 2 Type II preparation windows
- Reporting dashboards generate audit-ready completion records capturing which employee completed which module, when, and under which assignment rule, in the exact format compliance reviewers request.
This level of documentation directly supports audit readiness by providing detailed reporting and evidence of training assignments and completion, helping organizations demonstrate adherence to standards such as ISO and GDPR.
Why Do Auditors Now Scrutinize Customization Decisions Themselves?
Auditors expect documentation of why specific content was assigned to specific roles, a rationale trail linking employee population, risk level, and module selection to the applicable control.
Organizations that document their customization decisions, including identifying which groups received which content, on what schedule, and against what completion threshold, can address those questions directly.
Robust reporting capabilities are essential for demonstrating compliance, as they allow organizations to track, measure, and analyze the effectiveness of their security awareness programs. Organizations that cannot provide this documentation face audit findings even when completion rates are high.
What Is the Risk of Over-Customizing Simulation Templates?
Organizations that deviate too heavily from benchmark simulation templates lose the ability to compare their results against industry data. When a simulation is modified to the point where it no longer reflects a recognized attack pattern, click rates and failure rates become internal metrics only, with no external reference point to validate them.
Boards and auditors ask whether a program is performing relative to peer organizations, and that question cannot be answered without benchmark-comparable data. Calibrated customization means content relevant enough to resonate with specific roles and address an organization's unique security risks, yet structured enough to produce measurable results that hold up under external scrutiny.
Security Awareness Training Platform Customization: AI and Human Risk Scoring
Security awareness training platform customization, powered by AI-native capabilities, uses behavioral signals from simulations, open-source intelligence (OSINT) profiling, credential breach history, AI-driven analytics, and threat intelligence to generate a unified risk score.
At that point, the platform ceases to function as a content delivery system and becomes a self-adjusting defense layer, treating customization not as a configuration task but as a continuous, data-driven process.
Platforms that utilize AI can adapt training content based on user behavior and risk levels, providing a more personalized and effective learning experience for employees.
How Does AI-Generated Content Change What "Custom Training" Means?
Security teams can submit a prompt, an internal policy document, or details of a real incident directly to an AI content engine and receive a completed training module within minutes, built around their organization's specific context, terminology, and threat profile.
These AI content engines can also generate interactive training modules that are engaging, customizable, and compatible with standard learning management systems (LMS), facilitating scenario-based learning that improves user engagement and knowledge retention.
Role-specificity at this level is what generic library content cannot replicate, regardless of library size, with customized training positioning employees as proactive defenders against security threats.
What Happens When an Employee Fails a Phishing Simulation?
When an employee clicks a simulated phishing link, the platform automatically enrolls them in targeted remedial training without administrator intervention, matching the content to the exact attack vector involved.
Effective security awareness training programs incorporate continuous assessment and adaptive training to measure user behavior and track risk reduction over time. Simulation performance, training completion patterns, and OSINT exposure data, drawn from more than 1,000 data points per employee, all feed into a unified risk score that adjusts training assignments in real time.
Without AI-powered automation, adjusting training assignments in real time for thousands of employees would require manual intervention from administrators at every step.
How Does AI Governance Feed the Human Risk Score?
Detecting an employee pasting sensitive customer data into an unauthorized AI tool constitutes a behavioral risk signal, and modern platforms route that signal directly into the employee's risk score, triggering automatic security awareness training. This is the same mechanism that activates after a failed phishing simulation.
By continuously monitoring user behavior and assessing risk through behavioral analytics, security awareness platforms can adapt training content based on employee performance and engagement, ensuring that training remains relevant and effective over time.
Traditional data loss prevention and cloud access security broker tools were not designed to address this behavior, and human risk management platforms respond to the full spectrum of employee risk behavior, not just email-based threats.
When every signal, from a clicked phishing link to an unauthorized AI paste, flows into a single score, the platform's response becomes proportional to actual employee behavior rather than scheduled calendar events.
What to Look for When Evaluating Security Awareness Training Platform Customization
Evaluating security awareness training platform customization requires examining eight specific capabilities, from simulation channel coverage to reporting flexibility, to determine whether a platform produces behavioral change or merely satisfies a compliance requirement.
Leading security awareness programs offer diverse customization options to align with an organization's unique risks, brand identity, and technical environment. The sharpest predictor of long-term program success is not the number of configuration options a platform offers, but how directly each option connects to employee risk signals.
1. Confirm Multi-Channel Simulation Coverage
Email-only simulation leaves employees unprepared for the attacks most likely to succeed against them. Therefore, leading platforms support custom templates across email, voice, SMS, and deepfake video, giving security teams the coverage to prepare employees against the full attack surface, not just the most familiar one.
2. Assess AI Content Generation Depth
Platforms with a native AI content engine that builds training modules from a prompt or an uploaded policy document within minutes compress the training creation cycle to hours.
Customizable training modules allow organizations to tailor content to their specific industry needs, compliance requirements, and employee roles, enhancing the relevance and impact of training. This directly affects how quickly training content can reflect a live threat or a new regulatory requirement.
3. Evaluate Segmentation and Dynamic Group Logic
Attribute-based smart groups that sync automatically from an HRIS eliminate admin overhead and ensure the right training reaches the right employees without administrator intervention.
This enables the delivery of role-based training paths, ensuring that finance, HR, and IT teams each receive content and simulations relevant to their respective risks. Tailoring content to specific job functions enhances the effectiveness of security awareness training and supports ongoing compliance.
Platforms that require manual list management introduce lag between a risk signal and the training response, and that lag carries measurable consequences when phishing susceptibility increases.
4. Verify SCORM and LMS Compatibility
Organizations with existing compliance content or specialized training modules built outside the platform need assurance that content remains accessible.
Security awareness training platforms should support integration with existing corporate learning management systems (LMS) to facilitate seamless deployment and tracking of training effectiveness, including the ability to import interactive training modules and externally authored SCORM packages into a single training environment.
5. Check Compliance Module Mapping and Configurability
Security leaders need the ability to assign specific frameworks to particular employee populations, with healthcare staff receiving HIPAA-mapped modules and finance teams receiving PCI-DSS content, rather than deploying every framework to every employee.
This targeted approach ensures that data protection and regulatory requirements are addressed as core training objectives.
6. Test Branding and White-Label Depth
For cybersecurity awareness training to be effective, simulation sender domains, email display names, and portal styling must all reflect the organization's actual environment to create the psychological realism that drives behavioral change. Platforms that restrict sender domain customization reduce simulation fidelity and inflate false-detection rates.
7. Map the API and Integration Ecosystem
Platforms with a wide, documented integration ecosystem reduce administrative overhead and increase the signal value of risk data, while also enabling advanced reporting capabilities:
- HRIS integrations determine whether user management is automated or manual
- SIEM and SOAR integrations determine whether human risk signals flow into the broader security stack or remain isolated within the security awareness training platform
- SSO and Okta compatibility affects provisioning speed and access governance
These features allow organizations to track, analyze, and demonstrate the effectiveness of their security awareness programs by integrating data across systems.
8. Confirm Reporting Flexibility and Stakeholder Segmentation
Security awareness training platforms that support configurable dashboards for each audience eliminate manual report-building and demonstrate program return on investment without requiring a data analyst. A few examples include:
- A CISO requires board-ready risk trend data
- A security awareness manager needs simulation click rates by department, as well as metrics on user engagement and progress
- An auditor needs training completion records mapped to a specific framework
Tracking user engagement and progress is essential for measuring program success, as it provides actionable insights into learner participation, module completion, and overall improvement in security awareness.
Depth over breadth remains the governing principle: a platform that executes three customization types with precision and measurable behavioral outcomes outperforms one offering twenty configuration options that produce no actionable data.
Frequently Asked Questions About Security Awareness Training Platform Customization
What Is Security Awareness Training Platform Customization and Why Does It Matter for Reducing Breach Risk?
Security awareness training platform customization is the practice of configuring a security awareness training platform's content, simulations, delivery cadence, branding, and reporting to match an organization's specific threat profile, workforce structure, and compliance requirements.
It operates on two levels: platform-level configuration, which covers how training is delivered and to whom, and content-level configuration, which covers what employees actually learn and how.
Customization is the mechanism that closes the gap between a compliance checkbox and a program that changes how employees behave under real attack conditions, directly reducing human risk by targeting the specific vulnerabilities and behaviors most likely to contribute to security incidents.
Can Security Awareness Training Platforms Be Customized for Industry-Specific Threats Like Healthcare Phishing or Financial BEC Scenarios?
Modern security awareness training platforms support industry-specific customization at both the simulation and content levels, including role-based training paths and targeted training. The key mechanism is matching simulation pretexts to the language, systems, and workflows employees recognize. A simulation that references a real internal tool produces significantly higher engagement and retention than a generic IT alert template.
Role-based training paths allow organizations to structure programs tailored to specific job functions, supported by regular training campaigns and phishing simulations to enhance security awareness and ensure compliance. Customized training enables employees to apply security knowledge in practice through interactive simulations.
Organizations can also assign framework-specific training modules, ensuring every employee trains against the exact threat surface relevant to their role.
How Do Behavioral Triggers and Phish-Fail Events Automatically Assign Custom Remedial Training to Employees?
Behavioral trigger logic connects simulation outcomes directly to training enrollment without manual intervention by administrators. When an employee clicks a simulated phishing link, the platform automatically assigns a targeted remedial module tied to the specific attack type involved.
The automation is significant because the educational window immediately following a failure is when learning retention is highest. Platforms that require administrators to manually route employees who did not pass into remedial content introduce delays that reduce that advantage.
A similar logic applies to behavioral analytics. User risk scores are tracked and updated based on these behaviors, helping organizations identify high-risk individuals and groups, measure the effectiveness of training, and further customize security awareness efforts.
Behavioral triggers can also escalate responses. Employees who repeatedly fail can be routed to more intensive learning paths, while those who consistently pass simulations can be advanced to higher difficulty levels. The result is a program that self-calibrates to each employee's actual risk behavior and user risk scores rather than a fixed annual calendar.
Can Security Teams Import SCORM-Compliant Custom Training Modules Into a Security Awareness Training Platform?
Most enterprise-grade security awareness training platforms support SCORM module import, the standard interoperability mechanism that allows externally authored content to run within a platform's learning management system.
SCORM (Sharable Content Object Reference Model) packages content with completion tracking and assessment data, enabling the platform to record scores, time-on-module, and pass/fail status, producing the same reporting data as native content.
This is relevant for organizations that have internally authored compliance training, policy acknowledgment modules, interactive training modules, or third-party vendor-sourced training materials that they wish to deliver alongside their phishing simulation program.
The practical workflow involves packaging the authored content as a SCORM 1.2 or SCORM 2004 file and uploading it to the platform's content library, where it can be assigned to specific employee segments through the same role-based learning path logic used for native modules.
Organizations should verify that their platform supports both SCORM versions and that completion data flows into the same reporting dashboard used for native content, as gaps in reporting can create problems for audit documentation.
How to Measure Whether Customized Security Awareness Training Outperforms Generic Modules?
The most direct measurement approach is a split-cohort comparison. Role-specific custom content is delivered to one employee segment while generic off-the-shelf modules are assigned to a comparable segment, with phishing simulation click rates, knowledge assessment scores, user progress, and repeat-failure rates tracked across both groups over a 60-to-90-day window.
Customized simulations that mirror organizational context tend to produce higher initial click rates because they are more difficult, which is the intended outcome. The meaningful indicator is the rate at which click rates decline after targeted remedial training is delivered.
Beyond simulation data, organizations should track risk score trends at the individual and department level over time and use analytics to monitor user performance and engagement throughout the training lifecycle.
How Adaptive Security Maps Training to an Organization's Exact Threat Profile
Security awareness training platform customization allows security teams to measure behavioral change. When training content, simulations, and remediation logic are configured to match a workforce's actual risk surface, employees develop the specific recognition skills relevant to their role. This tailored approach fosters a security-conscious culture and measurably strengthens an organization's security posture. The Adaptive Security demo illustrates how the platform enables organizations to customize training to their specific requirements.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents