Selecting the right cybersecurity awareness training platform determines whether employees become a prepared line of defense or remain exposed to social engineering cyberattacks. Cyberattackers now use open-source intelligence (OSINT) to craft hyper-personalized spear phishing campaigns, deploy deepfake video impersonations of executives, and launch coordinated vishing and smishing sequences. Email-only tools cannot address this surface area, and the gap is widening every quarter.

This guide gives security leaders a structured framework on how to choose a cybersecurity awareness training platform across every dimension that affects outcomes. It explores:
- How to choose a cybersecurity awareness training platform that defends against multi-channel cyber threats, including deepfake video and AI voice cloning;
- How to evaluate phishing simulation depth, OSINT personalization, and risk scoring quality;
- How to assess compliance coverage across SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001;
- How to compare deployment speed, integration architecture, and admin overhead;
- How to run a meaningful pilot before committing to any cybersecurity awareness training program;
- How to build the internal business case using measurable ROI metrics.
Stop guessing whether the cybersecurity awareness training program is moving the needle on human risk; let Adaptive Security demonstrate the full platform live.
What a Cybersecurity Awareness Training Platform Does in 2026
A cybersecurity awareness training platform is software that teaches employees to recognize and respond to cyber threats, ranging from phishing and social engineering to AI-generated deepfakes, vishing, and smishing. Modern platforms unify phishing simulation, microlearning, automated phish triage, and human risk management (HRM) inside a single system, connecting employee behavior directly to measurable security outcomes. The defining feature is operational scope rather than content volume.
A purpose-built cybersecurity awareness training platform actively tests employees with live simulated cyberattacks, tracks individual risk scores, and triggers remediation automatically. Generic learning management systems simply log course completions. The distinction shows up in the outcome data: platforms designed for behavior change produce defensible reductions in click rate and reporting time, while compliance-only tools produce certificates.
Why Modern Cybersecurity Awareness Training Differs From Legacy Compliance Tools
Legacy compliance tools were built to satisfy checkboxes through annual modules, static slide decks, and completion certificates. They were never engineered to change behavior under pressure from a real cyberattack. According to the Verizon 2025 Data Breach Investigations Report, roughly 60% of breaches still involve a human element, including errors, social engineering, and misuse, which static training has consistently failed to address.
A purpose-built cybersecurity awareness training program treats training as a continuous cycle. It delivers microlearning immediately after a failed phishing simulation, personalizes content by role and risk profile, and runs multi-channel simulated cyberattacks across email, voice, SMS, and deepfake video. The shift from annual modules to continuous, adaptive programs reflects the operational reality that today's cyberattackers do not wait for the next compliance cycle.
Why Platform Selection Now Defines Organizational Risk Posture
Choosing how to protect the human layer through phishing simulations and security awareness training directly determines whether employees can recognize and stop AI-powered cyberattacks before damage occurs. A cybersecurity awareness training platform that covers email phishing but ignores voice cloning, deepfake video, or coordinated SMS cyberattacks leaves the majority of the modern threat surface undefended.
That gap is the difference between a workforce that catches a deepfake CFO call and one that wires funds before anyone asks a second question. Selecting the right platform begins with one recognition: defensive coverage must match the channels cyberattackers actually use, such as email, voice, SMS, and deepfake video.
Equip the workforce against AI-driven impersonation by deploying Adaptive Security's multi-channel phishing simulations that mirror real attacker tradecraft.
Why How One Choose a Cybersecurity Awareness Training Platform Determines Whether Training Works
Choosing the wrong cybersecurity awareness training platform does not just waste budget; it leaves the human layer exposed to precisely the cyberattacks that technical controls cannot stop. Knowing how to choose a cybersecurity awareness training platform requires understanding where legacy designs structurally fail, what compliance-checkbox training actually costs in risk terms, and which evaluation criteria correlate with measurable behavior change. This section frames why platform fit, more than feature count, drives outcomes.
Why Legacy Email-Only Cybersecurity Awareness Training Platforms No Longer Match the Threat
AI-powered cyberattacks have outpaced the platforms built to defend against them. According to CrowdStrike's 2025 Global Threat Report, a 442% rise in voice phishing (vishing) cyberattacks between the first and second halves of 2024, yet most legacy cybersecurity awareness training programs still route every phishing simulation through email alone.
That design assumption made sense when phishing arrived as a clumsy mass email with a misspelled sender domain. It does not hold when the same cyberattack arrives as an AI-cloned voice call from the "CFO," a smishing text with a spoofed internal number, or a deepfake video placing an executive on a live Zoom call requesting an urgent wire transfer. AI is now embedded in the attacker toolkit at scale: ENISA Threat Landscape 2025 found that more than 80% of observed social engineering activity worldwide by early 2025 used AI-supported phishing campaigns, with adversaries leveraging jailbroken models, synthetic media, and model poisoning to enhance operational effectiveness.
What Compliance-Checkbox Cybersecurity Awareness Training Actually Costs
Most cybersecurity awareness initiatives succeed only at increasing knowledge rather than at changing the behaviors that determine whether an employee wires funds, clicks a link, or picks up a suspicious call. Knowledge without behavior change does not reduce breach risk; it only satisfies an audit requirement.
That distinction matters acutely for security leaders accountable for outcomes. According to the SANS Institute 2025 Security Awareness Report, 80% of organizations rank social engineering as the number one human-related risk, and the report concluded that technology alone cannot mitigate behavioral risk without continuous program effort behind it. The criteria that separate cybersecurity awareness training platforms built for genuine behavior change from those built for checkbox compliance carry direct relevance to the AI-powered threat environment employees now face.
Replace static **cybersecurity awareness training** that ages out within months by adopting Adaptive Security's continuously updated AI-driven content engine.
The 8 Criteria That Separate Effective Cybersecurity Awareness Training Platforms From Checkbox Tools
Choosing a cybersecurity awareness training platform on feature count alone is how organizations end up with expensive software employees ignore. The right evaluation framework focuses on whether a platform changes behavior under realistic cyberattack conditions. According to the APWG Phishing Activity Trends Report Q2 2025, the group observed 1,130,393 phishing attacks in a single quarter, the largest quarterly volume since 2023. The criteria below form a practical evaluation framework that should be applied across every vendor under consideration.

- Cyberattack channel coverage: Does the platform test employees across email, voice, SMS, and deepfake video, or only email? Email-only platforms fail to build the detection instincts employees need when the cyberattack arrives as a voice call or video message from a convincing AI clone of their CEO.
- Content quality and relevance: Is cybersecurity awareness training content personalized by role and behavior, or pushed identically to the entire organization? A finance manager facing business email compromise (BEC) wire fraud needs different preparation than a developer targeted through credential theft.
- AI and adaptive learning: Does the platform use AI to tailor phishing simulation difficulty, personalize cyberattacks using OSINT, and generate new content automatically? Static libraries go stale within months as cyberattacker techniques evolve.
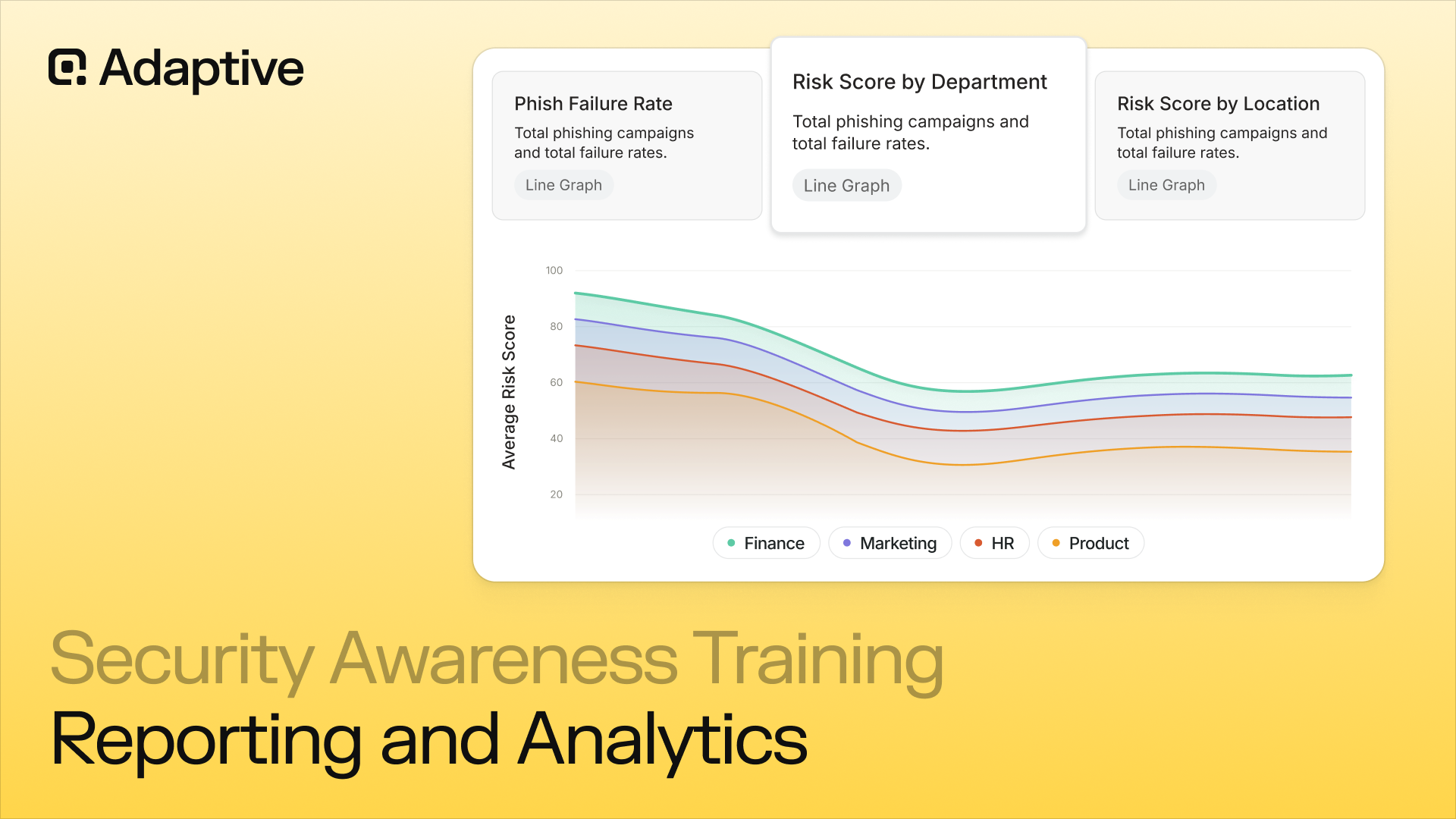
- Reporting and analytics: Does the platform provide individual risk scores, department-level dashboards, click-through rate trends, and board-ready reports, or only completion rates? Security leaders need reporting that connects investment to measurable risk reduction over time.
- Compliance framework coverage: Does the platform map content to SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001, and produce audit-ready documentation that auditors will recognize?
- Integration and deployment speed: How quickly does the platform connect to Microsoft 365, Google Workspace, HRIS systems, and SSO providers including SAML, Okta, and Azure AD? Two-click integration with no MX record disruption is the standard.
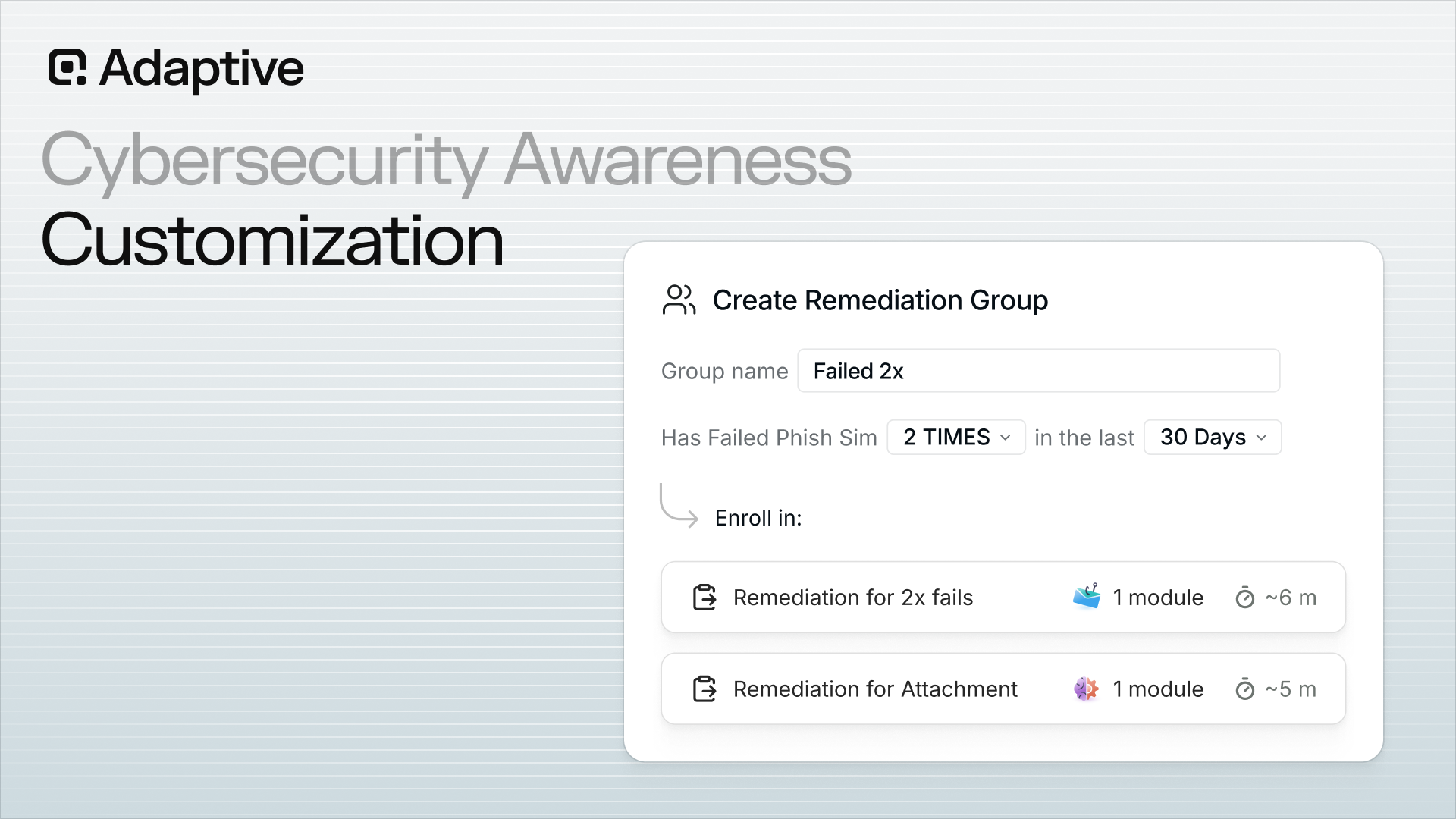
- Admin overhead and automation: Does the platform automate enrollment, phishing simulation scheduling, remediation, and phish triage, or does it generate manual work? Automated remediation that triggers targeted training without human intervention separates programs that scale from those that stall.
- Vendor support and architecture: How fast does the vendor ship new phishing simulation types and threat scenarios? AI-native platforms purpose-built for this era evolve in lockstep with cyberattacker techniques; retrofitted tools spend their cycles fighting their own technical debt.
Phishing simulation quality is where the gap between checkbox cybersecurity awareness training platforms and genuinely effective ones becomes most visible.
Cut through marketing claims by holding every shortlisted vendor to the eight criteria; Adaptive Security welcomes side-by-side evaluation.
How to Evaluate Phishing Simulation Depth Inside a Cybersecurity Awareness Training Platform
Choosing a cybersecurity awareness training platform on phishing simulation capability requires assessing six concrete dimensions: channel coverage, OSINT personalization, multi-channel coordination, phishing simulation difficulty calibration, deepfake realism, and post-click microlearning quality. The most important checkpoint is that phishing simulations are only as useful as the data they generate, which makes platform evaluation inseparable from evaluating reporting and risk scoring. Vendors should be required to demonstrate every claim live rather than through marketing decks.
1. Audit Channel Coverage: Email Is Table Stakes for Any Cybersecurity Awareness Training Platform
Every cybersecurity awareness training platform on the market runs email phishing simulations. The question is what happens beyond the inbox. Modern cyberattacker playbooks combine email with vishing, smishing, and deepfake video, treating them as layered pressure channels. A platform that lists "vishing" as a feature may mean nothing more than a static voicemail script played from a pre-recorded file.
A platform with genuine vishing capability delivers self-serve, real-time AI voice cloning, where security teams configure a phishing simulation, select an executive to impersonate, and the platform generates a live AI-cloned voice call that reaches the employee's actual phone. The operational gap between those two descriptions separates a marketing claim from a measurable security outcome.
2. Evaluate OSINT Personalization Depth

OSINT is how cyberattackers already operate. Before a spear phishing email reaches a target's inbox, adversaries have scraped LinkedIn profiles, conference speaker bios, company news, and social media to personalize the lure with real names, real colleagues, and real organizational context. Generic template libraries cannot replicate this because they reference fictional scenarios rather than an employee's actual digital footprint.
Cybersecurity awareness training platforms that use OSINT pull real public data about each employee to build phishing simulation scenarios that mirror what a real cyberattacker would construct. Employees cannot recognize the result as training content, which produces more accurate behavioral data and drives stronger behavior change than any template can deliver.
Match cyberattacker tradecraft instead of replaying generic templates by activating Adaptive Security's OSINT-powered phishing simulations across the entire workforce.
3. Test for Multi-Channel Coordinated Phishing Simulation Capability
Real cyberattacker playbooks rarely stop at one message. The Arup wire fraud executed in Hong Kong in 2024 combined email, a video call, and perceived social proof from multiple "colleagues," all deepfakes, to override an employee's instinct to verify, resulting in a $25 million loss.
Platforms that simulate only isolated incidents give employees an incomplete picture of how pressure actually builds. Coordinated multi-channel phishing simulations chain email, voice, and SMS into a single sequence: an email arrives referencing an urgent vendor invoice, a follow-up vishing call from the "CFO" confirms the request, and an SMS adds a final push. Evaluating whether a platform can run these sequenced campaigns reveals whether it was designed for the threat landscape that exists today.
4. Apply the NIST Phish Scale to Assess Phishing Simulation Difficulty
Click rate alone is misleading without context about phishing simulation difficulty. A 30% click rate on an easy template tells security leaders very little; a 30% click rate on a high-difficulty phishing simulation tells them something actionable. The NIST Phish Scale, published by the National Institute of Standards and Technology, provides a structured framework for rating the detectability of simulated phishing emails based on persuasion cues and premise alignment.
When comparing cybersecurity awareness training platforms, ask vendors to score a sample of their template library against the Phish Scale and show click rate data segmented by difficulty tier. Platforms that cannot provide this breakdown are measuring activity rather than risk.
5. Distinguish Genuine Deepfake Phishing Simulation From Marketing Claims
Deepfake phishing simulation is the highest-realism option available in the cybersecurity awareness training category and the most frequently overclaimed. A genuine deepfake video phishing simulation means the platform can generate a real-time AI impersonation of a named company executive using publicly available reference material. Employees who experience it cannot distinguish it from legitimate communication without a verification protocol, which is the entire point.
According to Signicat's The Battle Against AI-Driven Identity Fraud Report 2025, deepfake fraud attempts have grown by 2,137% over the last three years. To verify a genuine capability, ask the vendor to run a live deepfake phishing simulation using an executive from the buyer's own organization during the evaluation. Platforms that redirect to pre-recorded examples or decline the request are not offering authentic deepfake phishing simulation.
6. Examine Fail Screen Quality and Microlearning Triggers
What happens in the first 60 seconds after an employee clicks a simulated phishing link determines whether the phishing simulation produces behavior change or just a data point. A high-quality fail screen delivers a precise, contextualized explanation of the specific technique used in that phishing simulation, rather than a generic warning. Effective phishing simulations trigger immediate microlearning modules tied to the exact vulnerability the employee demonstrated: clicking a spoofed domain, responding to artificial urgency, or failing to verify a voice request through a secondary channel.
This immediate reinforcement loop, rather than a separate training assignment sent days later, is where measurable risk reduction happens. When evaluating cybersecurity awareness training platforms, click a test phishing simulation directly and time the fail screen response. Both the speed and specificity of what follows the click reveal how seriously the vendor has engineered the behavior-change outcome.
The depth of a platform's phishing simulation capability directly shapes the quality of the risk data it generates, which connects back to the reporting capabilities security leaders rely on to demonstrate program ROI.
What Risk Scoring and Reporting Should Look Like in a Modern Cybersecurity Awareness Training Platform
Choosing a cybersecurity awareness training platform on reporting capabilities alone is one of the most consequential mistakes security leaders make. Compliance-oriented reporting tracks who completed a course; behavior-based reporting tracks whether the organization is actually safer. Only the second answers the question a board cares about: is human risk going down? This section walks through the reporting capabilities that close that gap.
What a Modern Human Risk Management Dashboard Includes
A modern human risk management dashboard generates individual employee risk scores computed from four inputs: phishing simulation behavior across email, voice, SMS, and deepfake channels; cybersecurity awareness training completion rates; OSINT exposure based on publicly available data; and credential breach history. That combination reflects actual susceptibility rather than just participation. Department-level and role-level breakdowns let security teams identify whether finance, the executive team, or a specific office location is running above acceptable risk thresholds.
Executive exposure monitoring adds a critical layer that standard dashboards skip. Senior leaders are the highest-value impersonation targets, yet most platforms treat them identically to frontline employees in reporting. A platform with genuine human risk management capability profiles executive digital footprints, flags credential exposures, and surfaces the OSINT signals cyberattackers are most likely to exploit. Automated remediation workflows complete the picture: when an employee crosses a risk threshold, the platform enrolls them in targeted cybersecurity awareness training without requiring a manual ticket from the security team.
Replace point-in-time completion reports with live risk scoring through Adaptive Security's executive exposure monitoring and dynamic human risk dashboards.
Why Completion Rates Alone Fail Security Leaders
A cybersecurity awareness training platform delivering only completion rates cannot demonstrate whether training is actually changing behavior. The metrics that close that gap are specific:
- Phishing simulation click-through rate reduction measured quarter over quarter;
- Employee risk score improvement at the individual and team level;
- Reduction in repeat offenders who fail multiple phishing simulations;
- Mean time to triage reported phish, capturing how quickly employees act on suspicion rather than whether they felt trained.
Verizon 2025 Data Breach Investigations Report documented that the human element appeared in roughly 60% of breaches and noted that researchers found phishing simulation click rates were largely unaffected by training, underscoring why completion-rate dashboards fall short of what security leaders need. The gap between "trained" and "resistant" is measurable only through phishing simulation performance and behavioral trend data over time.
How Industry Benchmarking Justifies Cybersecurity Awareness Training ROI
Industry benchmarking converts cybersecurity awareness training program investment into a board-ready argument by comparing the organization's phish-prone percentage against sector peers. A CISO who can show that a finance organization dropped from a 28% phish-prone rate to 9% while the industry average sits higher has made an ROI case without a single spreadsheet. The comparison ties the budget line directly to competitive risk posture, which is the language boards and CFOs use.
Regulators share this orientation. HIPAA, PCI-DSS, and SOC 2 all require documented evidence that training is happening and that it is working. Platforms built around human risk management produce the behavioral trend data, remediation logs, and risk score histories that auditors are trained to recognize. That documentation gap is where compliance-only cybersecurity awareness training platforms consistently fall short.
How to Assess Compliance Coverage Inside a Cybersecurity Awareness Training Platform
Choosing a cybersecurity awareness training platform on compliance grounds requires evaluating each framework's specific training mandates, verifying that platform content is mapped to those requirements, and confirming the platform produces audit-ready documentation. This section walks through the core requirements buyers should test against before signing a contract. One rule applies throughout: always evaluate whether content is mapped to a framework, since that is a fundamentally different claim from a platform claiming it is certified for one.
1. Know What Each Framework Actually Requires
Each major framework imposes distinct obligations that go beyond generic security training. SOC 2 requires documented evidence that employees are trained on security policies and that training is tracked and demonstrable to auditors. HIPAA mandates workforce training on privacy and security safeguards for protected health information under 45 CFR §164.308(a)(5).
GDPR requires that employees who handle personal data receive appropriate data protection training, with the obligation specific to function rather than blanket across the workforce. PCI-DSS Requirement 12.6 mandates a formal cybersecurity awareness training program for all personnel with access to cardholder data, with annual training and acknowledgment required. ISO 27001 requires documented awareness programs covering information security policies and employee responsibilities within the scope of the information security management system.
2. Verify Content Mapping Inside the Cybersecurity Awareness Training Platform
The most important distinction buyers overlook is the difference between a cybersecurity awareness training platform whose content is mapped to a framework and a vendor that claims to be certified for it. A vendor claiming SOC 2 certification for its platform is making a statement about its own internal security controls; that is not a statement about whether its training content satisfies the buyer's SOC 2 obligations.
The question to ask every vendor is: "Can you show which training modules map to specific controls under HIPAA Security Rule 45 CFR §164.308, PCI-DSS Requirement 12.6, and SOC 2 CC1.1?" Platforms that cannot answer with documented control mapping are not compliance-ready, regardless of marketing claims.
3. Build the Audit-Ready Documentation Checklist
Compliance frameworks do not just require training to happen; they require proof. A compliance-ready cybersecurity awareness training platform must produce, at minimum, the following four artifacts:
- Completion records by employee: Individual timestamped records showing which modules each employee completed and when;
- Phishing simulation results tied to individuals: Documentation linking phishing simulation attempts, click outcomes, and remediation training back to specific employees by name and role;
- Policy attestation tracking: Records confirming that employees read and acknowledged security policies, required for SOC 2 and ISO 27001 audits;
- Timestamped training history: A full audit trail of every training event, exportable in formats auditors and GRC tools can ingest.
Platforms that track only aggregate completion rates rather than individual records with timestamps will fail audit scrutiny under any of these frameworks.
4. Treat Compliance as the Floor, Not the Ceiling
Organizations that optimize for compliance minimums end up choosing a cybersecurity awareness training platform that satisfies auditors while leaving employees unprepared for real cyberattacks. Annual training satisfies PCI-DSS Requirement 12.6 on paper, but a workforce trained once per year on static content will not recognize an AI-generated spear phishing email or a deepfake vishing call.
The correct posture is a platform that delivers compliance coverage as a baseline while running continuous, behavior-changing security awareness training that measurably reduces susceptibility between audit cycles. The two goals are not in conflict.
Satisfy auditors and stop real cyberattacks with the same platform; Adaptive Security maps every module to SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 controls.
Integration, Deployment Speed, and Admin Overhead in a Cybersecurity Awareness Training Platform
Choosing a cybersecurity awareness training platform is both a training decision and an infrastructure decision. The integration requirements, deployment model, and ongoing administrative burden a platform imposes determine whether the security team spends its time reducing human risk or managing vendor complexity. Platforms that earn their place are invisible to IT during rollout and largely self-managing once live. The five operational checkpoints below should be applied before signing any contract.
1. Verify Integration Requirements Before Anything Else
Microsoft 365 and Google Workspace compatibility is required. These are the email environments employees use daily, and any cybersecurity awareness training platform that cannot integrate natively with both immediately limits coverage. Beyond email environment compatibility, confirm SSO support via SAML, Okta, and Azure AD; SCIM provisioning for automated user lifecycle management; and HRIS or GRC integrations that keep employee rosters current without manual CSV uploads.

One requirement serves as an immediate red flag: platforms that require MX record changes to deliver phishing simulations introduce DNS risk, add IT overhead, and signal an architecture built for a pre-cloud era.
2. Set a Deployment Speed Benchmark
The time between contract signed and first phishing simulation live is a reliable proxy for a cybersecurity awareness training platform's overall operational simplicity. Platforms that deploy via two-click integration with Microsoft 365 or Google Workspace require no infrastructure changes and no multi-week implementation sprint. The first phishing simulation campaign should be reachable within days of deployment rather than weeks.
3. Audit Admin Overhead for Sustainability
Manual administrative burden is what causes most cybersecurity awareness training programs to stall. Platforms that require security teams to hand-configure every campaign, individually enroll employees in remediation training, and manually review each reported phish create an operational model that does not scale beyond one or two dedicated headcount.
According to the SANS 2025 Security Awareness Report, lack of time and staffing remain the two biggest challenges limiting practitioners from building and managing an effective program. Sustainable programs run with minimal manual touchpoints, and Phish Triage automation in particular should be a given rather than a queue someone reviews by hand.
Free analyst hours every week by routing reported emails through Adaptive Security's AI-powered phish triage with configurable auto-resolution thresholds.
4. Demand AI-Powered Phish Triage Automation
Phish triage automation is the operational force multiplier that separates modern cybersecurity awareness training platforms from legacy tools. AI-powered triage automatically classifies every employee-reported email as safe, spam, or malicious, with configurable auto-resolution thresholds.
One-click org-wide inbox remediation eliminates the need to manually retract malicious messages from individual inboxes, and built-in VirusTotal integration provides independent URL and attachment verification without requiring analysts to pivot between tools. The net effect is that a high-volume phishing report queue resolves in minutes rather than hours.
5. Decide Between Self-Serve and Managed Service
The right delivery model depends on team size and security maturity. Self-serve platforms give security teams full configuration control and suit organizations with dedicated cybersecurity awareness training program managers. Managed services abstract that configuration layer and assign a vendor-side team to build and run campaigns, making them a practical fit for mid-market organizations without dedicated awareness headcount. Neither model is universally superior. The wrong choice creates either frustration from loss of control or an unsustainable internal workload.
How to Run a Pilot Before Committing to a Cybersecurity Awareness Training Platform
Choosing a cybersecurity awareness training platform without running a structured pilot is one of the most expensive procurement mistakes security teams make. A meaningful pilot tests the vendor against real operational conditions: actual employee workflows, realistic cyberattack channels, and the admin experience the team will live with every day. The four workstreams below structure that evaluation: what to test, what to ask vendors, what to ask their customers, and what onboarding support to expect.
1. Define What the Pilot Will Actually Test
Run at least one phishing simulation per channel the vendor claims to support. A vendor that advertises email, voice, and SMS coverage but only delivers a convincing email phishing simulation during a pilot is signaling something important about depth. Test how quickly new phishing simulation content can be created by asking the cybersecurity awareness training platform to generate a custom spear phishing scenario from scratch, timed.
Then experience the fail screen and immediate microlearning from an employee's perspective: does the remediation feel like skill-building, or does it read like a compliance warning? Load the admin dashboard with a realistic reporting use case. Pull a department-level risk report as if presenting to a board. If that workflow takes more than a few minutes, the platform will create friction at scale.
2. Ask Vendors the Questions Feature Lists Don't Answer
Push beyond the demo script. The questions that generate real comparative signal are:
- How long does full deployment actually take, measured from contract signed to first phishing simulation live?
- When an employee fails a phishing simulation, is remediation automated or does someone on the team trigger it manually?
- How often are new phishing simulation templates and threat scenarios added to the library?
- Can the vendor demonstrate the phish triage workflow end-to-end, including auto-resolution confidence thresholds?
- How is individual employee risk scored, and what specific behaviors trigger automated remediation?
- Can the platform run a coordinated multi-channel campaign as a single sequenced cyberattack?
- Can the vendor build an OSINT-personalized phishing simulation from real public employee data, live, during the call?
The OSINT-personalization request is the most revealing of the seven. A platform that cannot demonstrate OSINT-personalized phishing simulation in real time almost certainly does not do it automatically at scale.
3. Ask Vendor References What the Vendor Will Not Tell
Reference calls are the highest-signal source of information in any cybersecurity awareness training platform evaluation. Ask existing customers about actual time-to-value, from contract signature to first phishing simulation running. Log customer success responsiveness when something breaks mid-campaign. Check whether the platform has kept pace with new cyberattack techniques (specifically deepfake or voice phishing simulation additions), and what measurable behavior change they have observed and over what timeframe. References that cannot point to specific metrics signal a vendor that does not make measurement easy.
4. Know What Onboarding and Ongoing Support Should Look Like
Onboarding quality determines whether the cybersecurity awareness training platform delivers value in the first 90 days or stalls in implementation. At minimum, expect a dedicated customer success manager (CSM) for any enterprise-tier contract, defined SLA terms in writing, a structured onboarding playbook, and a knowledge base maintained as the product evolves. The strongest vendors pair the buyer with an onboarding specialist for the first phishing simulation campaign rather than handing over a self-serve dashboard on day one.
Run the pilot questions against Adaptive Security to see live OSINT personalization, deepfake vishing, and automated remediation in a single session.
How Organization Size, Maturity, and Industry Shape Cybersecurity Awareness Training Platform Choice
Knowing how to choose a cybersecurity awareness training platform starts with an honest acknowledgment: no single configuration serves every organization. The right cybersecurity awareness training platform for a 50-person fintech startup pursuing SOC 2 differs fundamentally from what a Fortune 500 CISO needs across 20,000 employees. Selecting the wrong fit produces exactly the outcome both organizations are trying to avoid: training that does not change behavior. Three dimensions structure the decision: organization size, security program maturity, and industry vertical.
How Organization Size Affects Cybersecurity Awareness Training Platform Requirements
Enterprise organizations need platforms built for complexity. Multi-team administration, role-based access controls, custom content creation, deep HRIS and GRC integrations, and board-ready risk reporting are not optional features at scale. A cybersecurity awareness training program running across 10,000 employees in five business units cannot be managed manually from a single admin account.
Mid-market organizations face a different tension: enterprise-grade protection without enterprise-grade administrative overhead. The right platform for this segment scales with growth, integrates with Microsoft 365 or Google Workspace without MX record changes, and delivers results without requiring a dedicated security team to operate it. SMBs need fast onboarding, out-of-the-box compliance coverage, and minimal configuration; time-to-value is the defining metric.
How Security Maturity Changes What a Cybersecurity Awareness Training Platform Must Deliver
Early-stage programs should prioritize ease of deployment and baseline compliance coverage. A startup that has never run a phishing simulation needs a cybersecurity awareness training platform that launches a campaign in days and maps content to SOC 2, HIPAA, or GDPR from day one. Checking compliance boxes is a legitimate starting point; it just cannot be the finish line.
Mature security programs outgrow static content libraries and annual training cycles. They require AI-powered personalization, multi-channel phishing simulation depth, OSINT-based risk profiling, and automated remediation workflows that enroll high-risk employees in targeted cybersecurity awareness training without manual intervention. Adaptive Security's human risk monitoring and mitigation capabilities, including dynamic employee risk scoring and OSINT-powered executive exposure monitoring, are purpose-built for organizations at this maturity stage.
What Cybersecurity Awareness Training Content Each Industry Vertical Needs
Industry vertical determines threat profile, and threat profile determines what cybersecurity awareness training content has to cover. Finance teams face business email compromise (BEC), wire fraud, and deepfake executive impersonation; according to the FBI Internet Crime Complaint Center 2024 Annual Report, BEC drove $2.77 billion in reported losses across 21,442 incidents.
Healthcare organizations must satisfy HIPAA workforce training requirements, and IBM Cost of a Data Breach Report 2025 found healthcare remained the most expensive sector with an average breach cost of $7.42 million. Technology companies confront credential theft and OSINT-personalized spear phishing targeting engineers whose access to source code and infrastructure makes them extraordinarily high-value targets. Government and public sector teams face nation-state social engineering and must align content with NIST CSF requirements.
Content breadth matters as much as phishing simulation realism. Every vertical needs coverage beyond phishing: password hygiene, MFA adoption, ransomware awareness, secure data handling, remote work security, and physical security. A hospital's exposure to ransomware via phishing is acute and immediate, while a law firm's greatest risk may be credential theft enabling unauthorized access to client matters. Content relevance drives engagement; engagement drives the behavior change that determines whether employees stop a real cyberattack or just complete a module.
How a Cybersecurity Awareness Training Platform Prevents Awareness Fatigue
Engagement collapse is the silent failure mode of most cybersecurity awareness training programs. High completion rates are a false metric when employees click through modules just to clear a mandatory screen. Cybersecurity awareness training that employees do not absorb does not change behavior, and unchanged behavior is what cyberattackers exploit. This section covers the three failure drivers, what engagement-driven training looks like in practice, and how to calibrate phishing simulation frequency without creating predictability.
What Actually Drives Disengagement With Cybersecurity Awareness Training
Generic content is the primary driver of disengagement. When an employee in finance receives the same phishing awareness module as someone in facilities, neither encounters a scenario that reflects the cyber threats they actually face. Annual-only training compounds the problem because skills fade within days of completion, leaving the workforce unprepared for the remaining 364 days of the year.
Punitive framing makes it worse. When phishing simulation failures trigger public humiliation or performance consequences, employees learn to fear the training program rather than the cyberattacker. Every phishing simulation failure should be treated as a skill-building moment, since the employee who almost fell for a deepfake today is the one most primed to catch a real one tomorrow.
What Engagement-Driven Cybersecurity Awareness Training Looks Like
- Bite-sized modules under 10 minutes: Short-format microlearning respects employees' time, maintains attention, and fits into the workday without requiring calendar blocks.
- Personalized content by role and exposure profile: A finance employee rehearsing invoice fraud attempts learns something directly applicable; an IT administrator practicing spoofed credential-reset requests does the same.
- Immediate remediation at the moment of failure: The lesson is most salient the instant an employee falls for a phishing simulation, converting a near-miss into a training opportunity while the experience is still vivid.
- Gamification that rewards progress: Leaderboards, risk score improvements, and positive recognition create forward momentum and convert training from a compliance penalty into skill development.
How Often Phishing Simulations Should Run
Phishing simulation frequency is a calibration problem rather than a scheduling one. Testing employees once a quarter at the same difficulty level teaches pattern recognition for that specific test rather than building adaptability against novel AI-generated cyberattacks. Monthly phishing simulations across rotating channels (email, voice, SMS, and deepfake video) expose employees to the full range of methods cyberattackers use without creating the predictability that lets people pass simulations while remaining vulnerable to real cyber threats.
Difficulty calibration matters as much as frequency. Employees who face phishing simulations that are too simple develop false confidence; phishing simulations that are persistently too difficult demoralize rather than develop. Automated difficulty adjustment removes the manual burden from program managers while keeping each employee at the edge of their competency, which is exactly where durable behavior change happens.
The right cybersecurity awareness training platform removes the friction that causes programs to stall. Automated enrollment for high-risk employees, adaptive phishing simulation difficulty, and real-time risk scoring mean that engagement stops depending on a program manager remembering to manually adjust content; it becomes structural.
Sustain engagement past the first quarter by letting Adaptive Security's adaptive difficulty and instant microlearning carry the **cybersecurity awareness training program** forward.
What 'AI-Powered' Actually Means in a Cybersecurity Awareness Training Platform
"AI-powered" has become the most overused phrase in cybersecurity marketing, applied to everything from basic template randomizers to genuine machine learning systems. A cybersecurity awareness training platform that uses AI in name only delivers the same static content as legacy tools with a modern label attached. The question to ask vendors is not whether they use AI, but where AI operates inside the platform and what it specifically changes about the outcome. This section maps the four genuine AI use cases and how to test for them.
The Four Places AI Actually Works in a Cybersecurity Awareness Training Platform
Real AI integration shows up in four distinct, testable places:
- Content generation: A genuine AI engine builds new training modules and phishing simulation templates from prompts or uploaded policy documents in minutes, eliminating the static library problem because content stays current.
- Phishing simulation personalization: OSINT engines that evaluate hundreds of public data points per employee craft spear phishing simulations that mirror what real cyberattackers already know.
- Phish triage: Machine learning classifiers that automatically categorize every reported phishing email as safe, spam, or malicious, with confidence scoring and configurable auto-resolution thresholds.
- Risk scoring: Dynamic models that update individual employee risk scores continuously based on phishing simulation behavior, training completion, OSINT exposure, and credential breach history.
How to Distinguish Genuine AI From a Marketing Label
The only reliable test is a live product demonstration rather than a slide deck. Ask vendors to show each claimed AI capability in real time. A cybersecurity awareness training platform with genuine OSINT-powered phishing simulations should be able to pull a specific employee's public profile and generate a personalized phishing simulation on screen during the demo. A platform with genuine AI triage should show the classifier categorizing a submitted email with a confidence score and an auditable rationale.
Why Platform Architecture Determines Long-Term Effectiveness
According to the IBM Cost of a Data Breach Report 2025, 16% of breaches involved cyberattackers using AI, with phishing accounting for 37% of those AI-powered cyberattacks and deepfake impersonation accounting for another 35%. AI-native cybersecurity awareness training platforms built specifically for this era update their phishing simulation engines, risk models, and content generation in lockstep with evolving cyberattacker techniques.
Legacy platforms retrofitted from email security tooling cannot adapt at that speed because their architecture was not designed for it. The platform chosen to train employees today is also the platform that will need to defend them against cyber threats that do not yet exist, which is why the underlying architecture matters as much as the current feature set.
How to Build the Internal Business Case for a Cybersecurity Awareness Training Platform
Building the business case for a cybersecurity awareness training platform requires translating security risk into financial terms that finance teams, CTOs, and boards understand. Anchor the argument in breach cost data, total cost of ownership, and measurable program outcomes. The strongest budget conversations pair a concrete risk number with proof that the investment reduces that number over time. The five steps below structure that case.
1. Frame ROI in Financial Terms Boards Recognize

Security investment decisions stall when the ask is framed in technical language rather than business risk. According to the IBM Cost of a Data Breach Report 2025, the global average breach cost reached $4.44 million, while in the United States the average climbed to $10.22 million, a record high driven by regulatory penalties and slower detection times. A cybersecurity awareness training platform subscription is a fraction of one incident's cost.
Business email compromise compounds the picture. A well-designed cybersecurity awareness training program is among the highest-return security investments available when measured against that exposure, not because it eliminates all risk, but because it measurably reduces the frequency of human error that makes these cyberattacks succeed.
2. Calculate Total Cost of Ownership Beyond Per-Seat Pricing
Per-seat subscription cost is one line item in a larger ownership equation. Factor in admin time spent building and maintaining phishing simulation campaigns, the ongoing cost of content that never refreshes, and the labor cost of manual phish triage. Security analysts who spend hours per week classifying reported emails represent a measurable productivity drain that platforms with automated triage eliminate. Cybersecurity awareness training platforms that handle phishing simulations and triage automation together generate compounding returns by reducing both breach risk and analyst workload simultaneously.
3. Present to the Board in Plain-Language Business Terms
Boards respond to risk framing tied to outcomes they already care about: regulatory exposure, cyber insurance posture, reputational damage, and documented due diligence. Lead with the financial floor: what does a single incident cost versus the annual platform investment? Follow with operational metrics that show the program is working: phishing simulation click-through rate reduction over 90 days, employee risk score improvement by department, and cybersecurity awareness training completion rates that satisfy audit requirements. Documented program activity is also increasingly relevant to cyber insurers, who scrutinize awareness programs during underwriting.
4. Address Employee Privacy Concerns Proactively
Employees and HR teams sometimes push back on individual click-behavior tracking, reading it as surveillance rather than skill-building. Get ahead of this by communicating program intent before launch: cybersecurity awareness training exists to strengthen skills rather than to discipline anyone for failing phishing simulations. Configurable privacy controls matter; platforms that allow administrators to set thresholds for individual data visibility, aggregate department-level reporting, and anonymize early-stage phishing simulation results give HR and legal teams the flexibility to run programs that build confidence rather than fear.
5. Use Industry Benchmarking Data as an External Reference Point
Internal risk arguments gain credibility when anchored to external comparisons. According to the Verizon 2025 Data Breach Investigations Report, 22% of breaches began with credential abuse and 88% of basic web application attacks involved stolen credentials, often originating from social engineering. Benchmarking the organization's phish-prone percentage against external sector data shifts the conversation from "why should we spend this?" to "how quickly can the gap close?"
Translate cyber risk into board-ready ROI by exporting Adaptive Security's benchmarked risk scoring and phish-prone trend data directly into the next board deck.
Frequently Asked Questions on How to Choose a Cybersecurity Awareness Training Platform
The criteria that determine cybersecurity awareness training platform quality have shifted substantially as AI-powered cyber threats have moved from theoretical to routine. The questions below cover the most common buyer concerns: what to evaluate, how to measure effectiveness, which compliance frameworks apply, how to test vendor claims, and how to size a platform against organizational maturity. Each answer is written for security leaders making evaluation decisions in 2026.
What is cybersecurity awareness training?
Cybersecurity awareness training is a structured cybersecurity awareness training program that teaches employees how to recognize and respond to cyber threats, including phishing, social engineering, AI-generated cyberattacks, deepfakes, and voice cloning. Modern cybersecurity awareness training platforms deliver interactive modules, multi-channel phishing simulations, and behavior-based remediation to change how employees react to real cyber threats.
Why does the cybersecurity awareness training platform that gets chosen matter?
Not all cybersecurity awareness training platforms defend against the same channels. Legacy tools were built for email-only phishing in a pre-AI environment and cannot simulate deepfake executive impersonation, AI-cloned voice calls, or coordinated SMS cyberattacks. A platform that only covers email phishing leaves employees unprepared for the majority of how cyberattackers now operate.
What features should a cybersecurity awareness training platform include?
An effective cybersecurity awareness training platform must cover multi-channel phishing simulations across email, voice, SMS, and deepfake video. It must also deliver role-specific personalized cybersecurity awareness training modules, compliance-mapped content for SOC 2, HIPAA, GDPR, and PCI-DSS, automated remediation that enrolls high-risk employees in targeted training, and continuous risk scoring so security teams can track behavioral improvement over time. Generic, one-size-fits-all libraries are insufficient against AI-powered cyberattackers who personalize every cyberattack using OSINT.
How is the effectiveness of a cybersecurity awareness training platform measured?
Effectiveness is measured through phishing simulation click-through rates over time, cybersecurity awareness training completion rates, employee risk scores, and reduction in reported security incidents. The most meaningful signal is behavioral change: whether employees caught a simulated cyberattack, reported it quickly, and improved over successive phishing simulations. Cybersecurity awareness training platforms should provide department-level and individual-level risk dashboards, board-ready reporting, and behavioral trend data that ties investment directly to measurable risk reduction.
How often should cybersecurity awareness training run?
At minimum annually to satisfy compliance requirements; best practice is continuous training. That means phishing simulations monthly, microlearning modules quarterly, and real-time remediation training triggered immediately when an employee fails a phishing simulation. Cyberattackers do not limit campaigns to once per year, and neither should the cybersecurity awareness training program.
What compliance frameworks require cybersecurity awareness training?
SOC 2 requires organizations to demonstrate that employees are trained on security policies and procedures. HIPAA mandates workforce training on privacy and security safeguards for protected health information. GDPR requires employees who handle personal data to receive appropriate data protection training. PCI-DSS requires annual cybersecurity awareness training for all personnel with access to cardholder data. ISO 27001 requires documented awareness programs covering information security policies and responsibilities. Always confirm that a cybersecurity awareness training platform documents completion records in an audit-ready format.
What is the difference between cybersecurity awareness training and human risk management?
Cybersecurity awareness training focuses on delivering content and measuring completion rates. Human risk management encompasses the full lifecycle: identifying individual risk through OSINT and phishing simulation behavior, delivering personalized training based on that risk profile, automating remediation for high-risk employees, and providing continuous reporting that ties security investment to measurable behavior change. An awareness tool tells the security team who completed a module; a human risk management platform tells them who is most likely to be compromised next week and takes automatic action to close that gap.
How much does a cybersecurity awareness training platform cost?
Cybersecurity awareness training platforms are priced as annual SaaS subscriptions on a per-seat, per-month basis, with cost varying by organization size, feature tier, and contract terms. The more important calculation is ROI: the cost of a cybersecurity awareness training platform is a fraction of a single prevented incident, particularly given the regulatory penalties that now drive U.S. breach economics.
What is a cybersecurity awareness training platform, and how is it different from a basic LMS?
A cybersecurity awareness training platform is purpose-built software that trains employees to recognize and respond to social engineering cyber threats, covering phishing simulations, microlearning modules, phish triage, and human risk management in one system. A basic LMS tracks course completions and delivers static content but cannot simulate real cyberattacks, score individual employee risk, or automate remediation based on behavior. The critical difference is outcome orientation: an LMS confirms that training happened, while a dedicated platform measures whether behavior actually changed.
What are the most important features to look for when choosing a cybersecurity awareness training platform in 2026?
The most important features are: multi-channel phishing simulation coverage; OSINT-powered personalization that crafts simulations from real public data; AI-driven risk scoring that updates continuously; automated remediation that enrolls high-risk employees without manual intervention; compliance mapping across SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001; and fast deployment via native Microsoft 365 and Google Workspace integrations with no MX record changes required. The NIST Phish Scale provides a vendor-neutral framework for evaluating phishing simulation difficulty during platform comparisons.
How do phishing simulations work, and why should they go beyond email-only testing?
Phishing simulations send employees realistic, controlled cyberattack messages across one or more channels to measure click rates, credential submission, and reporting behavior, then trigger immediate microlearning when an employee fails. Email-only testing misses the full surface that modern adversaries use. Vishing, smishing, and deepfake video calls are now standard tools in cyberattacker playbooks, and employees who pass email phishing simulations regularly fall for voice or video-based impersonation cyberattacks they have never been trained to recognize.
How often should phishing simulations run inside a cybersecurity awareness training platform?
Organizations should run phishing simulations at least monthly for most populations, with higher-risk roles tested more frequently. Frequency matters less than difficulty calibration: sending the same low-complexity template repeatedly produces diminishing returns, while sending highly sophisticated cyberattacks to employees who have never received baseline cybersecurity awareness training produces failure rates that demoralize rather than build skill. Cybersecurity awareness training platforms with automated difficulty adjustment remove this calibration burden by raising phishing simulation complexity as employee risk scores improve.
What metrics prove a cybersecurity awareness training program is actually working?
The metrics that prove a cybersecurity awareness training program is working are behavioral: phishing simulation click-through rate reduction over rolling 30, 60, and 90-day periods; employee risk score improvement at the individual and department level; mean time to report a suspicious message; repeat offender rate reduction among high-risk employees; and cybersecurity awareness training completion rate paired with post-training phishing simulation performance. Completion rates alone confirm that training was delivered; they do not confirm that behavior changed.
How are vendor claims of 'AI-powered' tested?
Ask vendors to demonstrate each claimed AI capability live during the demo rather than through slides or screenshots. Genuine AI integration in a cybersecurity awareness training platform includes generative content creation, OSINT-personalized phishing simulation, AI-driven phish triage with confidence scoring, and dynamic risk scoring. If a vendor cannot demonstrate any of these live, the AI claim is marketing language applied to a static content library.
Which compliance frameworks require cybersecurity awareness training, and what documentation do auditors typically need?
Five major frameworks explicitly require cybersecurity awareness training: SOC 2, HIPAA under the HIPAA Security Rule, PCI-DSS, GDPR, and ISO 27001. Auditors typically need timestamped completion records by employee, phishing simulation results tied to individual users, policy attestation records, and evidence that high-risk individuals received follow-up training. Evaluate whether a cybersecurity awareness training platform's content is mapped to a framework rather than whether the platform itself holds a certification, since these are materially different claims.
How long does it typically take to deploy a modern cybersecurity awareness training platform?
A modern cybersecurity awareness training platform should deploy in minutes rather than weeks. Best-in-class platforms connect to Microsoft 365 or Google Workspace via two-click OAuth integration with no MX record changes, no infrastructure modifications, and no involvement from network operations teams. Integration requirements include SSO via SAML, Okta, or Azure AD; SCIM provisioning for automated user roster sync; and HRIS integrations for department-level reporting alignment. If a vendor's deployment timeline runs longer than 48 hours for a standard environment, ask specifically why.
How to build an internal business case and budget justification for a cybersecurity awareness training platform?
Build the business case around breach cost avoidance and measurable risk reduction. Pair regulatory exposure data with the organization's phish-prone percentage benchmarked against industry peers, and translate click-through rate reduction directly into probability-weighted loss exposure. Total cost of ownership should factor in admin time, manual phish triage labor, and the cost of content that goes stale between annual refresh cycles. Boards respond to three framings: regulatory exposure, cyber insurance posture, and reputational risk.
What questions should be asked of a vendor during a cybersecurity awareness training platform demo?
Operational and specific questions generate the most signal: How long does deployment take from contract signed to first phishing simulation live? Show an OSINT-personalized phishing simulation built from real public data on one employee. What happens the moment an employee fails a phishing simulation; is remediation enrollment automated or manual? Show the phish triage workflow from an employee report to resolution. Can a coordinated multi-channel campaign be demonstrated combining email, voice, and SMS? Vendors with genuine product depth answer these questions with live demonstrations rather than feature lists.
How does organization size or security maturity affect which cybersecurity awareness training platform is the right fit?
Organization size and security maturity together define which capabilities are essential. SMBs typically need fast deployment, minimal admin overhead, compliance-ready reporting, and baseline phishing simulation coverage; the cybersecurity awareness training platform should run largely on autopilot once configured. Enterprise organizations need advanced reporting with multi-team administration, role-based access controls, custom content creation, deep HRIS and GRC integrations, and robust audit documentation. Security maturity matters independently of size: an early-stage program at any organization should prioritize ease of deployment and baseline compliance coverage, while a mature program needs AI-powered personalization and automated remediation workflows.
What cybersecurity awareness training topics should a platform cover beyond phishing?
A cybersecurity awareness training platform should cover, at minimum: password hygiene and credential management; multi-factor authentication adoption and resistance to MFA fatigue cyberattacks; ransomware awareness; secure data handling and clean desk practices; remote work security; physical security including tailgating; business email compromise recognition; and social media OSINT awareness. Topic coverage should map to the threat profile of the industry vertical. Platforms with static topic libraries that cannot be updated as new cyber threats emerge will fall behind the actual cyberattack landscape within months.
Why Adaptive Security Stands Out for Cybersecurity Awareness Training in 2026

The threat environment employees face today includes OSINT-personalized spear phishing, AI voice cloning, deepfake video calls, and automated phish triage — features that legacy cybersecurity awareness training platforms were never designed to handle. Adaptive Security addresses each of these directly: multi-channel Phishing Simulations, dynamic Risk Monitoring and Mitigation, and automated Phish Triage built into a single platform. Every capability traces back to the eight evaluation criteria covered in this guide, with no retrofitted modules and no marketing claims that fail under live demonstration.
What separates Adaptive Security operationally is the depth of AI integration across the four places it actually matters. Generative content creation produces new modules and phishing simulation templates from prompts in minutes, eliminating the static library problem. OSINT-powered personalization pulls hundreds of public data points per employee to build spear phishing simulations that mirror real cyberattacker tradecraft. AI-driven phish triage classifies every reported email with confidence scoring and configurable auto-resolution thresholds. Dynamic risk scoring updates continuously based on phishing simulation behavior, cybersecurity awareness training completion, OSINT exposure, and credential breach history. Each of these is demonstrable live during evaluation rather than promised on a roadmap.
The platform deploys in minutes via native Microsoft 365 and Google Workspace integrations with no MX record changes, maps every module to SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 controls, and produces the timestamped, individual-level audit documentation that satisfies regulators. Walking through every capability at evaluation pace is the fastest way to compare it against current tooling.
See every claim in this guide hold up under live testing; Adaptive Security's interactive product tours run without a sales call or commitment.
Key Takeaways
- Knowing how to choose a cybersecurity awareness training platform begins with matching defensive scope to attacker scope across email, voice, SMS, and deepfake video.
- A modern cybersecurity awareness training platform must move beyond completion rates to deliver individual risk scoring, OSINT-based exposure data, and automated remediation.
- Compliance coverage is the floor for a cybersecurity awareness training program, not the ceiling; content must be mapped to frameworks rather than vendors claiming certification.
- Phishing simulation depth, including multi-channel coordination and OSINT personalization, drives the quality of behavioral data the platform produces.
- Deployment speed, native integrations, and admin automation determine whether a cybersecurity awareness training platform scales or stalls inside the security team's workflow.
- AI claims should be tested live across content generation, phishing simulation personalization, phish triage, and risk scoring rather than accepted from marketing decks.
- Engagement-driven cybersecurity awareness training uses bite-sized modules, role-personalized content, immediate post-failure microlearning, and gamification rather than punitive framing.
- Pilot evaluations should test channel coverage, content generation speed, fail screen quality, and admin workflows under realistic conditions before any contract is signed.
- The business case for a cybersecurity awareness training platform translates breach cost data, total cost of ownership, and benchmarked phish-prone trends into language boards already use.
- Adaptive Security is built around how to choose a cybersecurity awareness training platform that holds up under every evaluation criterion modern security leaders apply.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents