This guide provides a comprehensive examination of phishing tests and simulations in 2026, covering how phishing simulations function, why they are critical for reducing human cyber risk, and how to select the most appropriate phishing simulation tools for an organization. Phishing remains the most frequently reported cybercrime, according to the FBI's 2025 Internet Crime Report, which recorded nearly 200,000 complaints. This finding underscores the importance of phishing simulations and testing as essential components of employee cybersecurity programs.
The following topics are addressed:
- What is a phishing test?
- Why are phishing tests important?
- How do phishing simulations work?
- What are the key benefits of phishing tests?
- What metrics should organizations track in phishing simulation tests?
- What are the best practices and advanced strategies for phishing simulations (including real tactics used by cybercriminals)?
- What are the common challenges in phishing simulations?
A phishing test is a simulated cyberattack designed to assess how employees respond to tactics commonly used by cybercriminals. It also serves as an educational tool, helping employees identify indicators of phishing attempts and raising awareness of the methods cybercriminals most commonly use.
Phishing attacks generally involve impersonating a trusted entity to induce employees to make errors, such as clicking a malicious link or disclosing sensitive information, including login credentials.
Simulated phishing tests are commonly conducted via email to reflect attack methods regularly deployed by cybercriminals, such as phishing scams targeting Meta users, with the objective of obtaining login credentials.
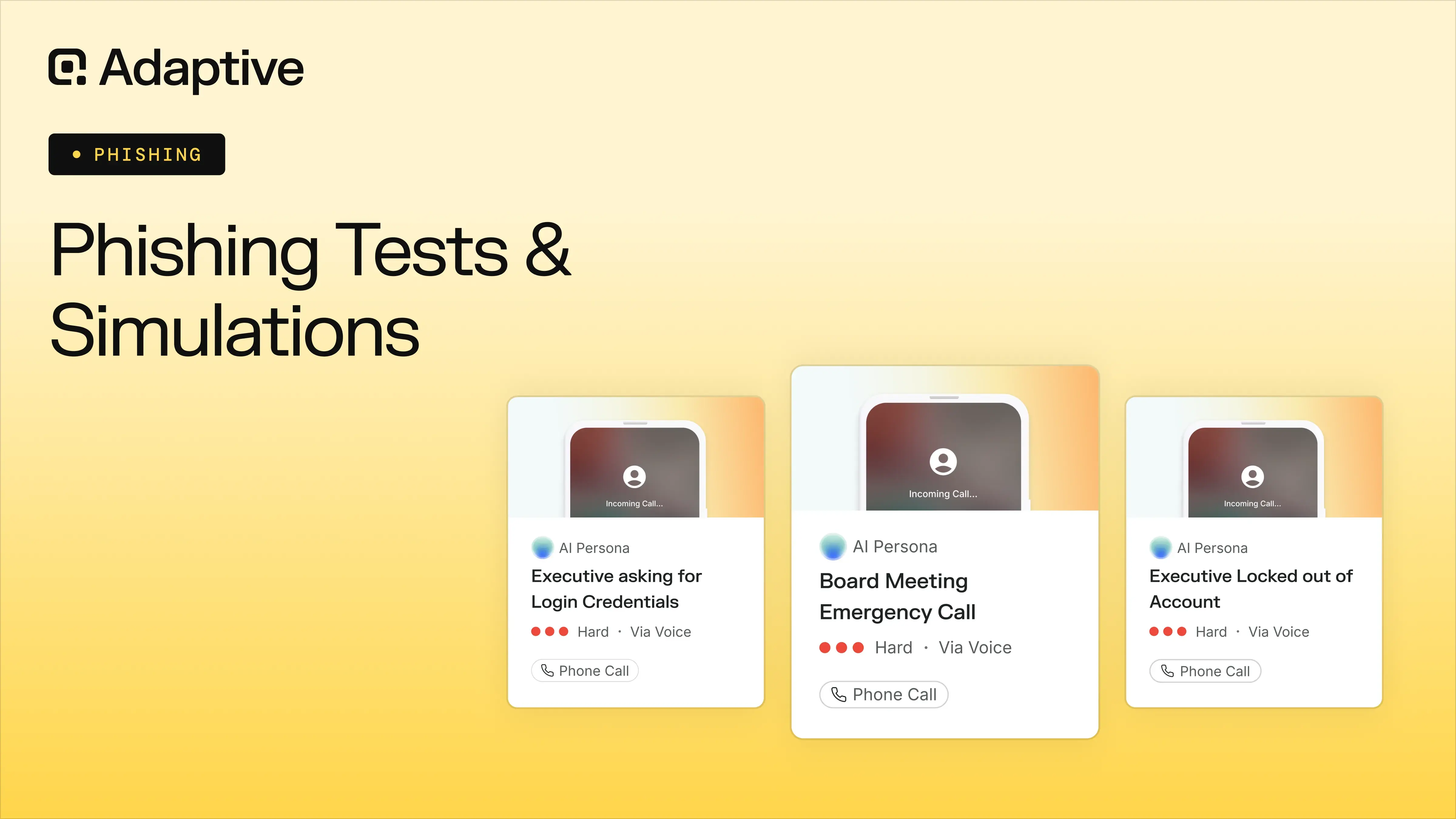
However, phishing simulations should extend beyond email to encompass SMS, voice, and deepfake phishing, all of which represent growing cyber threats. These simulations are particularly valuable for CISOs and security managers, as they provide measurable insight into employee behavior and organizational vulnerability.
Phishing Simulations Vs. Real Phishing Attacks
Phishing simulations should differ from actual phishing attacks only in their objective. Cybercriminals deploy phishing to obtain sensitive information such as credentials, credit card numbers, and proprietary organizational data.
Phishing is also frequently employed as a component of broader, multi-stage attacks. A recent example involves a hospitality company that suffered a data breach, after which cybercriminals used the compromised data to target the organization's customers in follow-on scams.
Beyond their objective, phishing simulations and actual phishing attacks should be indistinguishable. This requires employing the same tactics, exploiting the same psychological triggers, and using the same channels, including email, SMS, voice, and deepfake, while exercising appropriate judgment in execution.
Where the objective is to develop employees' ability to recognize phishing attacks, more realistic simulations produce better-prepared employees
A common comparison is between phishing simulations and fire drills. An organization would not set a building on fire to conduct a fire drill, but the closer the drill replicates actual emergency conditions, the better prepared participants will be in a genuine emergency. The same principle applies to phishing simulations.
Phishing Tests Vs. Security Awareness Training
Phishing simulations are typically a core component of security awareness training, but should not constitute the entirety of the program. They also deliver significant value by generating empirical data that enables consistent measurement of employee behavior and program effectiveness.
A common error is treating phishing simulations and security awareness training as entirely separate functions. Conducting phishing simulations independently is a sound practice, but a more comprehensive security awareness training program is necessary to build genuine organizational resilience.
Why Do Phishing Simulations Matter in 2026
Phishing simulations remain a critical component of organizational cybersecurity strategy in 2026, as the phishing threat continues to evolve. Although phishing attacks and their corresponding simulations are well-established practices, cybercriminals consistently develop new techniques, technologies, and approaches to compromise employees.
The natural evolution of workplace policies has also introduced new vulnerabilities; the widespread adoption of remote and hybrid work models, for example, has expanded the attack surface available to cybercriminals.
Phishing Simulations Test and the Rise in Social Engineering
Phishing simulations help prepare employees for social engineering scams, which represent the largest initial attack vector in security incidents, present in 36% of incidents according to SentinelOne.
Social engineering involves exploiting psychological triggers to manipulate individuals into taking a desired action, such as falling for a scam or compromising organizational infrastructure.
Effective phishing simulations must therefore address not only the attack methods deployed but also the psychological triggers cybercriminals exploit and the vulnerabilities they seek to leverage.
Key takeaway: The objective is to train employees to recognize manipulation, not solely to identify malicious emails.
The Impact of AI in Phishing Simulation and Tests
Phishing simulations are a critical component of organizational security in 2026. According to SlashNext's 2023 State of Phishing Report, phishing attacks have increased by 1,265% since the broader release of generative AI tools, underscoring the urgency of preparing employees to recognize and respond to this escalating threat. The rise of AI means that many traditional strategies for identifying phishing attacks are no longer sufficient.
Sift's 2025 Digital Trust Index reports a 456% increase in generative-AI-enabled scams between May 2024 and April 2025, attributable to improvements in both the quality and volume of attacks. As these attacks become increasingly convincing, maintaining employee preparedness represents a growing challenge for organizations.
AI-generated phishing emails can now incorporate specific contextual references, such as ongoing projects, colleagues, or vendors, drawing on publicly available information or data exposed in prior breaches. Cybercriminals can feed any available information into a generative model to produce highly convincing correspondence, and models can adapt interactions in real time based on employees' responses.
However, artificial intelligence extends beyond text generation. Its capacity to produce audio and images makes deepfake phishing and voice phishing (vishing) considerably more dangerous than conventional approaches. Additionally, artificial intelligence also offers a countermeasure. AI-powered phishing simulations are increasingly available and can realistically prepare employees for the attacks currently being deployed against organizations.
Main Benefits of Phishing Simulation Tests
The primary benefits of phishing simulation tests are their educational value and their capacity to reduce human risk. Their purpose is to demonstrate to employees how modern phishing operates and how they can protect themselves, equipping them with the knowledge necessary to recognize and respond to the threats they are most likely to encounter. However, the value of phishing simulations extends beyond employee education alone.
Phishing Simulators Help Reduce Human Cyber Risk
Phishing simulations reduce human risk by building awareness of cyber threats among one of cybercrime's most frequently targeted populations: employees. Human error remains one of the most prevalent entry points for cybercriminal activity.
Phishing simulations are most effective when grounded in the tactics cybercriminals actively use, as familiarity with these tactics substantially improves employee preparedness. Awareness of a specific threat significantly increases the likelihood that an individual will recognize and respond to it appropriately.
Critically, knowledge is measurable and can be translated into concrete action. When an employee completes a phishing simulation, the feedback received enables immediate learning and helps assess individual cybersecurity maturity over time.

Phishing Tests Improve Overall Cyber Hygiene
Phishing simulations are also an effective means of improving employee cyber hygiene. Analogous to its physical counterpart, cyber hygiene refers to a set of established practices that, when consistently applied, contribute significantly to overall digital security.
Phishing tests are particularly effective because they develop critical thinking skills in digital environments. A core principle of phishing awareness, for example, is to avoid accepting communications at face value and instead seek independent confirmation, particularly when recognized psychological triggers are present. This represents a transferable skill with broad applicability across digital interactions.
A further benefit is the reinforcement of deliberate behavior over habitual actions that are often taken without consideration. Over time, many users have been conditioned to click on links without scrutiny, a behavioral pattern that cybercriminals actively exploit. Consistent, long-term training can reshape these habits to align with cybersecurity best practices, such as hovering over links and inspecting attachments before clicking or opening them.
Phishing simulations also contribute to broader digital familiarity, increasing employee confidence and competence in navigating technology and online environments.
Phishing Attack Simulations Create a Ready-to-Report Culture
Phishing simulations include mechanisms for employees to report content they suspect is phishing. This reporting function is an integral component of the simulation and contributes to developing a security-conscious culture that extends across the entire organization.
Phishing simulations normalize threat reporting and promote a culture of shared responsibility, distributing cybersecurity accountability beyond the IT or security team alone.
This cultural shift carries significant operational value. Employee phishing reports can serve as an early warning indicator for security teams, signaling the potential presence of a more sophisticated or coordinated attack. A timely and accurate report can enable the security team to neutralize a threat before it escalates into a more serious incident.
Phishing Simulators Cover Basic Metrics
One of the primary advantages of phishing simulations is their capacity to generate quantifiable, concrete data. Most phishing simulations capture the following baseline metrics:
- Malicious link click rate
- Email open rate
- Credential submission rate
- Attachment interaction rate
- Threat report rate
- Time to report
- Failure rate
These metrics are readily tracked through a dashboard and provide a substantive initial assessment of employee performance in phishing simulations. They enable security teams to identify employees who demonstrate vulnerabilities and may require additional support or targeted training.
A Phishing Attack Simulation Helps Identify Higher Risk Users
As reported in Verizon's 2025 Data Breach Investigations Report, 8% of employees are responsible for 80% of security incidents. These numbers are partly explained by employees' roles, as executives are targeted far more often than lower-level employees.
However, tracking metrics like the ones above can also help identify which users pose the greatest risk. With that insight, organizations can create an environment that better supports and protects those individuals.
Phishing Simulations Expose Gaps in Your Digital Infrastructure
Phishing simulations are designed primarily to assess and build employee awareness, but they also indirectly expose gaps in an organization's digital infrastructure that might otherwise go unnoticed. For example, simulated phishing emails may bypass existing secure email gateways, revealing deficiencies in technical controls.
Simulations may also surface weaknesses in threat-reporting workflows and highlight areas where the security team's response times require improvement.
Key Takeaway: Regular phishing simulations reliably provide insights into the organization's broader cybersecurity posture.
How Phishing Tests and Simulations Work
Phishing simulations are exercises designed to replicate phishing attacks. Their structure and execution vary depending on the delivery channel, frequency, duration, the cybercriminal objective being replicated, and other organizational factors.
The central principle is to adapt the phishing simulation to the specific needs of the organization or individual user. AI-based phishing simulations enable a level of customization that can substantially strengthen and tailor the training experience.
Phishing simulations generally operate through three primary methodologies, each with distinct advantages and limitations.
How To Run an Effective Phishing Simulation Step by Step
Running an effective phishing simulation begins with defining the target population. Whether the simulation is intended for an individual, an entire organization, or a specific department determines the foundational step in selecting the appropriate phishing test design.
The next step is to define the simulation objectives, specifically what the exercise is intended to evaluate. This may include credential theft scenarios, fraudulent invoice attacks, or password reset scams. Separate simulations may be warranted for each distinct scenario.
Finally, the difficulty level of the phishing simulation must be calibrated to the experience and prior training of the participant population. The appropriate complexity will differ considerably between employees with no prior cybersecurity training and those who have completed previous awareness programs.
The following three questions represent the core pillars of a phishing simulation plan:
- Who is participating in the phishing simulation?
- What is the objective of the simulation?
- What level of difficulty is appropriate for the simulation?
Fake Email and Other Common Types of Phishing
The phishing simulation format must also be determined. Most free phishing simulation tools focus exclusively on email, which remains the primary phishing channel. However, with the proliferation of generative AI, additional channels, such as deepfakes and voice phishing, have become increasingly prevalent. The eight main types of phishing are as follows.
Type of Phishing Simulation #1: Fake Email
Email remains the predominant phishing channel. Also referred to as bulk phishing, email-based attacks offer a significant operational advantage: they can be distributed to millions of recipients simultaneously with minimal effort, a capability further amplified by the rise of phishing-as-a-service.

Given its broad targeting approach, email phishing operates on a volume basis. A phishing email sent to millions of recipients can result in a substantial number of victims, even at a click rate of 1%.
Type of Phishing Simulation #2: Spear Phishing
Spear phishing operates on the same fundamental principles as conventional phishing, but trades scale for precision. Rather than distributing generic messages to large populations, spear phishing targets a smaller, more specific group of recipients.
It is most prevalent in organizational settings, where attackers leverage publicly available information or previously compromised data to craft highly convincing communications.
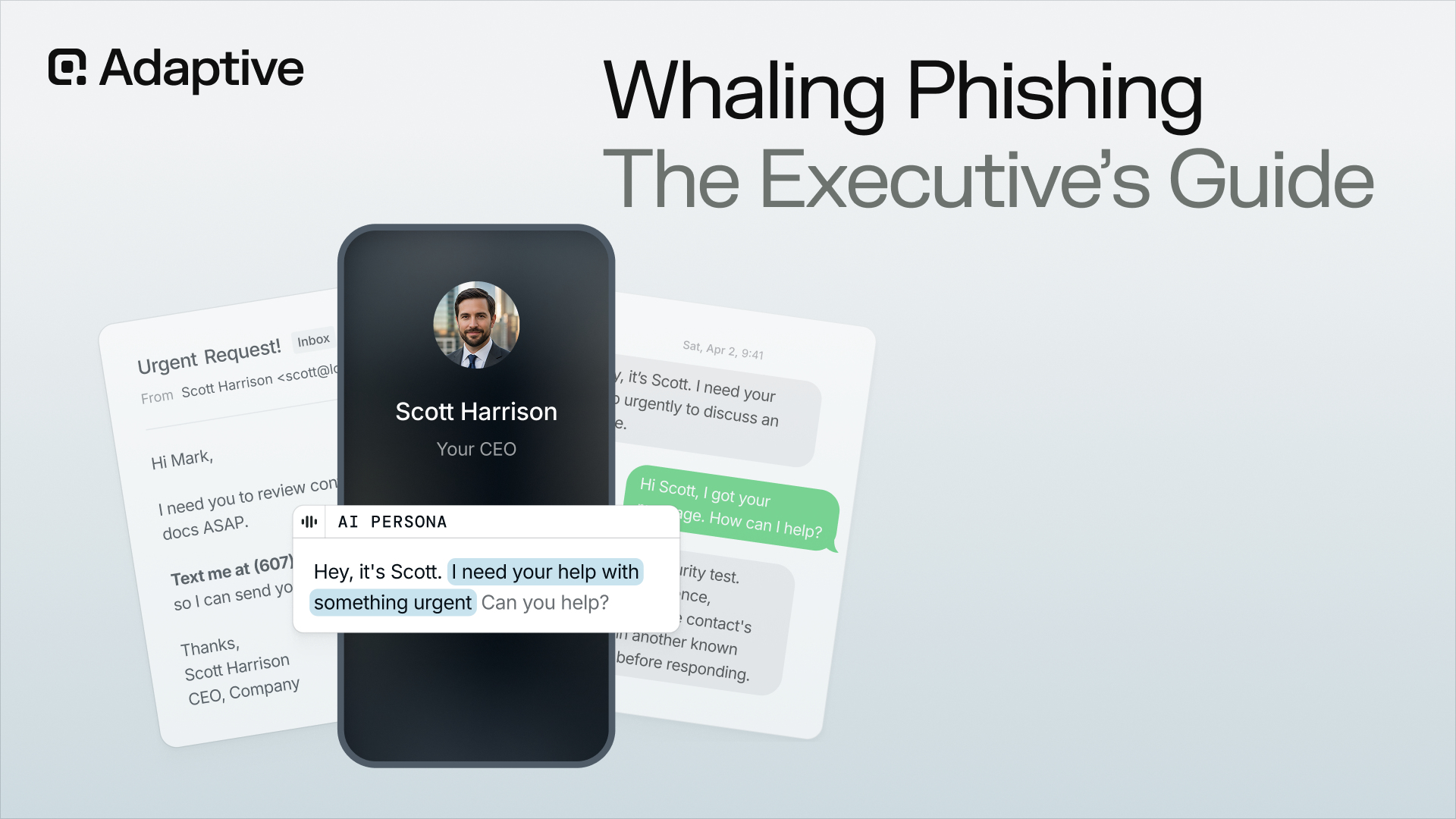
Type of Phishing Simulation #3: Executive Phishing
Executive phishing, commonly referred to as whaling, is a highly targeted form of spear phishing directed specifically at senior organizational leaders. Executives are frequently favored targets due to their elevated financial authority and the breadth of access they hold within the organization.
Where executives participate in phishing simulations, the complexity and scope of their assessments must exceed those designed for the general employee population.
Type of Phishing Simulation #4: Business Email Compromise
A sophisticated form of spear phishing, business email compromise (BEC) involves cybercriminals gaining unauthorized access to a legitimate email account to impersonate a vendor, executive, or other trusted party.
The primary danger lies in the attacker's position of established trust. Because the communication originates from a compromised legitimate account, the recipient is considerably more likely to act on the fraudulent request.
Type of Phishing Simulation #5: Smishing
Smishing refers to phishing attacks delivered via SMS and other messaging platforms. Like other forms of phishing, it adapts to the context in which it is deployed. Common examples include messages referencing delayed package deliveries or suspicious financial account activity.
In an organizational phishing simulation, smishing scenarios should reflect how cybercriminals actively employ this tactic, including attempts to circumvent multi-factor authentication by soliciting verification codes from employees.
Type of Phishing Simulation #6: Vishing
Vishing, or voice phishing, involves using voice-based communications to execute phishing attacks. According to Stephanie Carruthers, IBM's Global Lead of Cyber Range and Cyber Crisis Management and Chief People Hacker, vishing represents a cyberattack vector that "always works."
In phishing simulations, vishing scenarios are replicated by mimicking the voices of trusted organizational figures, such as executives, to assess whether employees can identify and resist this form of social engineering.
Type of Phishing Simulation #7: Deepfake Phishing
Deepfake video phishing represents an evolution of vishing, introducing an additional layer of deception through video. In addition to replicating voices, AI-generated deepfakes can now impersonate individuals in video format. An increasingly prevalent attack involves placing an employee in a virtual meeting with a deepfake rendering of a senior colleague or executive to manipulate them into taking a harmful action.

Phishing simulations must incorporate this threat vector. According to the Resemble AI Q3 2025 Deepfake Incident Report, 2,031 verified deepfake incidents occurred between July and September 2025, with 980 cases involving corporate infiltration, representing the second-highest incident category recorded.
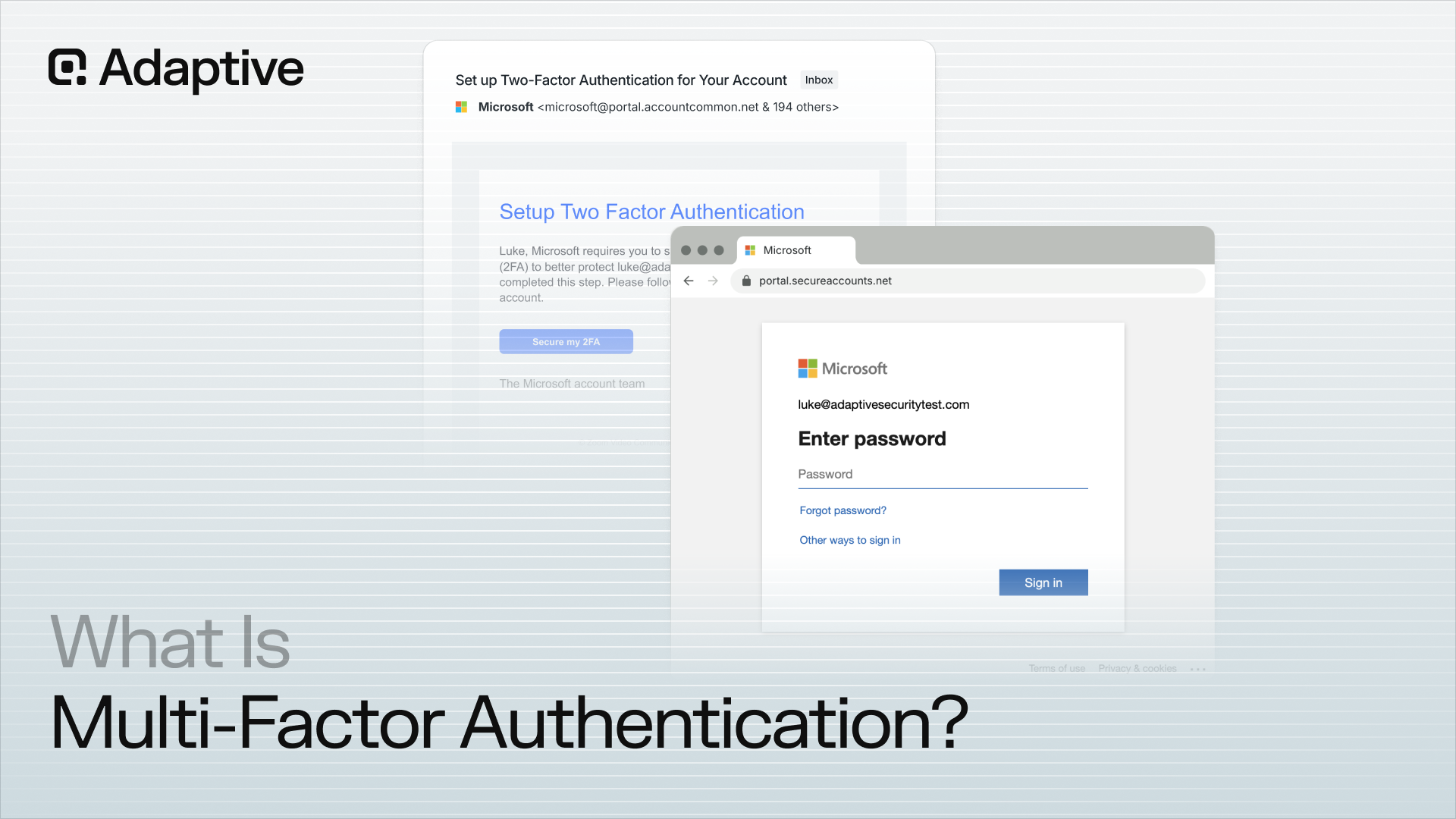
Type Of Phishing Simulation #8: Credential Harvesting Pages
Credential harvesting pages are fraudulent login portals created by cybercriminals to intercept employee credentials. They are commonly deployed under the guise of widely recognized brands used by organizations worldwide. Phishing simulations can replicate credential-harvesting pages to assess whether employees submit their login credentials when presented with a convincing but fraudulent portal.
How Often To Run Phishing Simulations
The appropriate frequency of phishing simulations depends on an organization's risk profile, cybersecurity maturity, and exposure to attacks. According to the Mandiant M-Trends 2026 Report, the high-tech industry was the most frequently targeted sector in 2025, accounting for 17% of incidents, surpassing the financial industry at 14%, which had been the leading target in both 2023 and 2024. Organizations operating in high-risk industries require more comprehensive and frequent simulation programs.
Regardless of industry, every organization should pursue the same overarching objective: sustaining a long-term phishing simulation campaign rather than relying on periodically scheduled or isolated phishing tests.
The primary advantage of a campaign-based approach is its capacity to iterate. Each simulation builds on the preceding one, not only in terms of frequency but also in content and participant targeting.
A practical benchmark is monthly simulations for the full workforce, with frequency increased to biweekly for high-risk or high-value employees. Varying the types of phishing simulations across cycles also ensures that the same scenarios are not repeated consecutively, maintaining training relevance and employee engagement.
Key Metrics to Observe in Phishing Simulation Tests
Phishing simulations generate critical data that can be used to extract meaningful insights about both individual employees and the organization as a whole. Analyzing an individual employee's performance across simulations reveals behavioral patterns and, when tracked over time, demonstrates how those patterns evolve as training progresses.

Examining results across the employee population within a broader organizational context enables organization-wide risk monitoring and the identification of systemic vulnerabilities.
The focus should be placed on behavioral trends, whether positive or negative, rather than on isolated simulation scores.
Click Rate in Email Phishing Test
The click rate in phishing simulations measures the proportion of employees who engage with a simulated phishing link. It is the most fundamental indicator of organizational risk: a higher click rate reflects greater exposure. Click rate can also be tracked at the individual level to monitor performance and improvement over time.
Credential Submission Rate in Phishing Simulators
The credential submission rate measures the number of employees who submit login credentials, such as usernames and passwords, during a phishing simulation. This metric provides a more direct measure of organizational risk than click rate alone, as credential theft represents one of the primary objectives of phishing attacks. Accordingly, it is among the most critical metrics tracked in a phishing simulation program.
Time to Click on Phishing Simulation Tests
Response times are valuable metrics that many phishing simulations do not track. They measure, for example, how quickly an employee interacts with a simulated phishing email. This metric identifies habitual behaviors that cybercriminals exploit.
Role-Based Risk Metrics on Phishing Simulation Tests
Role-based phishing simulations provide a key measure of employee behavior within the context of their specific organizational role. The resulting data enables security teams to tailor training programs to the distinct risk profiles of different positions and departments.
Report Rate of Simulated Phishing Attacks
The report rate in phishing simulations measures the proportion of employees who identify and report a simulated phishing attempt. This metric is particularly valuable because its implications extend beyond immediate organizational protection. Proactive threat reporting reflects a meaningful shift in cybersecurity culture, transforming employee awareness into an active first line of defense.
High reporting rates enable faster incident response by the security team, reducing the window of exposure during genuine attacks.
Time To Report Simulated Phishing Attacks
Closely related to the report rate, time to report measures how quickly employees identify and report a simulated phishing attempt, rather than the overall volume of reports. This metric is a key indicator of incident containment capability, as faster reporting enables security teams to address genuine threats more effectively and limit potential damage before it escalates.
Failure Rate of Simulated Phishing Attacks
The failure rate in phishing simulations is a broad metric that tracks overall employee failure across all forms of interaction with a simulated attack. It is most useful for providing an organizational overview, supporting executive-level reporting, and monitoring the overall effectiveness of the security awareness training program over time.
Rate of Repeat Failures in Phishing Tests
The repeat failure rate tracks employees who have failed phishing simulations on multiple occasions. This metric is important for identifying high-risk individuals who demonstrate persistent vulnerability. Where repeat failures are identified, targeted intervention or additional training may be warranted to address the underlying behavioral patterns.
Best Practices and Advanced Strategies in Phishing Simulation Tests
The most effective phishing simulations extend well beyond a cycle of deployment, assessment, tracking, and repetition. They serve as a core component of a broader security awareness training strategy, developing employees' capacity to approach cybersecurity with a more comprehensive, holistic perspective.
Adaptive and Personalized Phishing Tests
AI-based phishing tests allow companies to personalize and customize their simulations to improve overall learning. Not only are personalized tests more engaging, but they also place employees in scenarios most relevant to their daily work.
The most important facet of customization is the ability to shift gears mid-training. Different users learn at different paces, and organizations can design optimal phishing simulations for each participant, without prohibitive effort.
Appropriate Challenge in Phishing Simulation Tests
Initiating phishing simulations with advanced scenarios risks alienating employees and undermining engagement. Conversely, overly simplistic simulations may compromise training credibility, giving employees the impression that the threats presented bear little resemblance to real-world attacks.
A universal pass rate of 100% is not necessarily a positive outcome. It may indicate that simulations are insufficiently challenging or that employees are avoiding interaction with content altogether. A practical benchmark is an average employee accuracy rate of 70% to 80%, a range that acknowledges room for improvement while providing sufficient positive reinforcement to sustain engagement and motivation.

Multi-Channel Phishing Simulations
Multi-channel phishing simulations reflect an established cybercriminal trend of combining email, SMS, voice, and deepfake video communications into coordinated, simultaneous attacks.
Cybercriminals frequently follow an initial email with a voice or video call to lend additional credibility to the deception and increase the likelihood of eliciting a harmful response. Simulating these coordinated attacks is an effective way to prepare employees for them. Without prior exposure, it is considerably more difficult for employees to recognize that an email and a subsequent call referencing the same issue may constitute a single, orchestrated attack.
Even where multi-channel simulations are not combined into fully coordinated attack scenarios, training across multiple channels remains a valuable practice, introducing variety that sustains employee engagement throughout the program.
Immediate Feedback After a Phishing Simulation Test
Phishing simulations should be followed by immediate training wherever possible, particularly when an employee fails a test. Delivering training at the moment of failure is the most effective way to reinforce information, as the experience is immediate and directly relevant.
Most phishing simulation tools provide some form of instant feedback following each interaction, including basic contextual information such as sender details, URLs, tone, and psychological triggers employed. Training should be tailored to the severity of the error, with more serious failures prompting more substantive intervention.
The same principle applies to positive outcomes. Employees who report simulated phishing attempts should receive immediate positive reinforcement. Where personal acknowledgment is not feasible, an automated response serves as an effective alternative. Programs that formally recognize employees with the highest volume of accurate threat reports further reinforce a culture of proactive security awareness.
Key takeaway: Learning is most effective at the moment of error, and positive reinforcement remains the most powerful behavioral motivator.
Realistic Phishing Simulation Questions
Grounding phishing simulations in realistic scenarios is essential for improving learning outcomes. This can be achieved through a range of approaches, from basing simulations on current events to replicating techniques actively used by cybercriminals. Examples include the following:
- Including legitimate links within a simulated phishing email alongside a single fraudulent one, replicating a technique cybercriminals use to build trust in malicious links.
- Sending an email that appears to have been forwarded by a member of organizational leadership, requesting a specific action related to an ongoing conversation. This replicates a technique known as thread hijacking.
- Distributing an organization-wide email offering a gift card to a coffee shop as recognition for performance, with a fraudulent redemption link included. Employees who report the email within the first 2 hours receive a gift card.
- Collaborating with the security operations team to obtain examples of phishing emails previously reported within the organization and incorporating them into simulations, with an explanation that the scenario reflects a real incident.
- Coordinating with the HR team to use them as a simulated sender, ensuring thorough internal alignment to avoid unintended disruption.
All simulations must remain strictly ethical. Scenarios based on legitimate organizational topics such as HR updates, invoices, and IT alerts are appropriate. Scenarios that exploit sensitive themes, such as layoffs, health crises, or other manipulative subjects, should never be used.
Employees should be familiar with phishing attack patterns before those patterns are used in simulations.
Psychological Triggers Behind Phishing Simulation
No phishing simulation program can fully prepare employees for every possible attack scenario. For this reason, every simulation should be grounded in the psychological triggers that underpin these attacks. The six primary triggers cybercriminals employ in an organizational context are as follows:
- Urgency: Pressuring employees into making decisions under artificially imposed time constraints.
- Authority: Coercing employees through the impersonation of figures with organizational or institutional authority.
- Trust: Deceiving employees through the use of fraudulent but convincing sources or identities.
- Cognitive Overload: Exploiting employee fatigue by timing attacks to coincide with periods of high workload or stress.
- Fear and Loss Aversion: Generating a sense of threat or potential loss to prompt hasty or unconsidered action.
- Curiosity: Enticing employees with the prospect of accessing information they would not ordinarily be privy to.
Additional psychological triggers exist but are more prevalent in personal rather than organizational contexts, including scarcity, social proof, reciprocity, and emotional manipulation.
Common Challenges and Mistakes to Avoid in Phishing Tests
Phishing simulations are an effective means of improving security awareness and generating actionable insights into an organization's cybersecurity maturity. However, a number of common challenges and errors can produce false confidence, employee backlash, or unreliable data. The most frequently observed pitfalls, drawn from extensive practical experience, are outlined below.
Low Engagement on Phishing Simulations
Low participant engagement is one of the most significant challenges in phishing simulation programs. Disengaged employees are likely to complete simulations with minimal effort, substantially diminishing their learning value.
At the employee level, this challenge can be addressed by varying themes and scenarios and by running engagement initiatives that communicate the importance of the simulations, particularly by using real-world cyberattack case studies to illustrate the consequences of phishing.
The same challenge applies to executive leadership, whose lack of active engagement can restrict program budgets and impede broader organizational adoption.
Educating employees on the purpose and importance of phishing simulations is as critical to program success as the simulations themselves.

Craft Useful Phishing Simulation Questions
One of the most demanding aspects of designing effective phishing simulations is developing scenarios that genuinely challenge employees, requiring a move beyond predictable formats.
Many phishing simulation tools rely on well-worn scenarios, such as password expiration alerts, that employees have encountered so frequently they respond automatically, either reporting them immediately or disregarding them entirely. While these responses are not inherently problematic, simulations built exclusively around such patterns provide limited insight into genuine employee preparedness.
Repeated use of the same scenarios or structural patterns produces fatigue and, over time, yields metrics that reflect pattern recognition rather than authentic behavioral improvement. Employees learn to identify the simulation rather than the underlying threat.
Striking the appropriate balance in scenario design requires ongoing refinement and a willingness to introduce genuinely challenging scenarios.
Go Beyond the Basic Metrics on Phishing Simulations
Standard phishing simulation metrics provide a valuable measure of training progression but rarely reflect the complete picture. These metrics are tracked because they are quantifiable, but what cannot be measured is equally important.
A fundamental limitation is that employees may become adept at recognizing the organization's specific phishing simulations rather than developing the broader capacity to identify phishing attacks in general. Fully addressing this limitation would require exposure to an unlimited range of attack scenarios, which is not operationally feasible.
This is significant because phishing simulations measure more than outcomes alone. They are designed to assess behavior, learning, cognitive processing, and decision-making. Measuring these dimensions has long presented challenges for educators. The most effective response to this challenge is direct observation and dialogue: engaging with employees to assess how they discuss and process the simulations they encounter.
Phishing simulation tools that generate varied and diverse scenarios also help organizations move beyond templated exercises and institutional bias in simulation design. Automated, diverse scenario generation encourages employees to develop genuine decision-making skills rather than memorizing the characteristics of recurring simulations.
The objective extends beyond measuring whether an employee clicked on a simulated phishing link. The deeper goal is to determine whether the employee applied sound judgment in reaching that decision.
Be Careful of Behavioral Bias in Phishing Simulations
Behavioral bias represents a significant risk to the validity of phishing simulations and can produce a false sense of security. These behavioral biases alter how individuals respond across different situations.
The Hawthorne Effect illustrates this dynamic clearly: employees tend to modify their behavior when they are aware they are being observed or assessed. In a professional context, this is particularly pronounced, as employees are reluctant to be perceived as a cybersecurity liability within their organization.
This bias can be mitigated by making the program unpredictable, combining structured, scheduled simulations with unannounced assessments. Surprise simulations deployed without contextual preparation should be avoided, as employees may perceive this approach as unfair or experience concern regarding the professional implications of failure.
Creating a Negative Culture Around Phishing Simulations
Cultivating a punitive culture around phishing simulations is a consequential error. Shaming or penalizing employees who fail simulations invariably suppresses threat reporting rates and generates distrust and resentment toward the security team.
Once this dynamic is established, rebuilding employee trust is significantly harder, and the conditions necessary for effective learning are undermined. The most effective countermeasure is to focus the program on learning and positive behavioral change, rather than emphasizing negative outcomes.
Request an Adaptive Security Demo to understand how the platform supports the development of effective, tailored phishing simulations.
Future Trends in Phishing Tests
Phishing simulations have evolved considerably in recent years to keep pace with emerging cybercriminal trends, and this evolution will continue as cybercriminals persistently refine their methods. Key developments shaping the future of phishing simulations include the following:
- AI-Based Personalized Phishing Simulations: Simulations will be tailored to individual employees rather than to organizations or roles, incorporating general organizational information, personal behavioral history, prior communications with colleagues, and significant contextual events
- AI-Based Adaptive Phishing Simulations: Complementing the training process, artificial intelligence will enable simulations to adapt in real time based on individual employee behavior during the exercise
- Simulation of Current and Advanced Techniques: Legacy phishing training will continue to lose relevance as attack methods evolve
- Behavioral Risk Scoring: Rather than relying on potentially misleading quantitative metrics, human risk scoring will be grounded in behavioral data, generating individual risk profiles that more accurately reflect genuine vulnerability
- Multi-Channel AI Threats: Deepfake phishing, vishing, and related attack variations will continue to grow in prevalence and sophistication
Phishing Simulation Tools: How to Choose the Best One?
A range of phishing simulation tools is available, spanning both free and paid options, enabling organizations to conduct simulations that align with their objectives and available resources.
The first step in selecting the most appropriate phishing simulation tool is to assess the organization's cybersecurity maturity level and define its objectives. Organizations initiating phishing simulations for the first time will generally require less sophisticated tools than those operating at a more advanced level of security maturity.
Phishing Test Tools: Must-Have Features
The following capabilities should be evaluated when assessing a phishing simulation tool.
- Phishing Quality and Realism. Reviewing sample simulations to identify evidence of personalization and customization, and to determine whether they replicate current attack methods rather than outdated or predictable scenarios.
- Risk Monitoring and Assessment. Understanding how the platform captures and presents phishing simulation data, and assessing the depth and utility of the insights it generates.
- AI-Powered Phishing Simulations. Artificial intelligence integration is essential for adapting, personalizing, and customizing training, improving overall quality and realism without incurring prohibitive costs.
- Security Integration. A phishing simulation tool that integrates effectively with existing cybersecurity infrastructure will leverage available resources and reduce the complexity of implementation.
- Frictionless Reporting. Threat reporting is a core component of phishing simulation training. Minimizing friction in the reporting process improves report rates and contributes to broader organizational security.
- Multi-Channel Capabilities. As attacks increasingly span multiple channels beyond email, effective phishing simulation tools should support voice phishing, deepfake phishing, SMS phishing, and other emerging attack vectors.
The most reliable method for evaluating a phishing simulation tool is direct experimentation. Free tools carry no barriers to entry, and most paid platforms offer demonstrations. Where necessary, a proof of concept can be conducted after narrowing the selection to a small number of candidate tools.
Best Free Phishing Simulation Tools
A free phishing simulation tool provides an accessible way to introduce phishing simulation capabilities without a financial commitment, enabling organizations to conduct pilot programs and assess the initiative's potential value. A range of free resources is available, including the following.
- GoPhish. A free, open-source tool designed to assess an organization's exposure to phishing.
- Microsoft Attack Simulation Training. Available through Microsoft Defender 365, accessible via a free trial.
- Google Phishing Quiz. A free phishing assessment offered by Google, oriented toward individual users rather than organizational programs.
- Adaptive Security Free Phishing Test. A free phishing assessment that organizations can use to evaluate their phishing exposure.
However, CISOs and security managers frequently encounter limitations when deploying free phishing simulation tools. The configuration effort required is often substantial, and in many cases, the staff time necessary to fully implement a free tool manually exceeds the cost of a paid alternative.
A further limitation is that free tools are generally not equipped to generate the formal training reports that executive leadership requires, adding an additional layer of complexity and administrative effort.
Deploying a free phishing simulation tool nonetheless retains value, as designing and running an independent assessment yields significant organizational insight.
How Does Adaptive Security Help with Phishing Simulations
Adaptive Security incorporates phishing simulation as a core component of a comprehensive security awareness training strategy, delivering multi-channel simulations across voice, SMS, and email that reflect the realism of current attack methods.
Artificial intelligence generates customized phishing simulations fully tailored to the organization's workforce. AI also enables fully automated simulation campaigns that can be executed with minimal manual input, reducing the administrative burden on security teams.
Adaptive Security has an established record of delivering measurable outcomes for its clients. The Adaptive Security and NerdWallet case study illustrates how the platform was used to transform an organization's cybersecurity culture through phishing simulation and complementary tools.
To evaluate the platform firsthand, request an Adaptive Security Demo.
Phishing Simulations Frequently Asked Questions
Are Phishing Simulations Legal and Ethical?
Yes. Phishing simulations are legal and ethical when designed and executed responsibly. This requires careful attention to simulation design, obtaining appropriate organizational consent, maintaining transparency with relevant stakeholders, and adhering to all applicable safeguards, including data privacy regulations, employee monitoring requirements, and labor laws.
Are Spoofing and Phishing the Same?
No. Phishing and spoofing are distinct but related concepts. Phishing is a social engineering attack that uses impersonation to manipulate individuals into taking unintended actions. Spoofing is a technique commonly used in phishing attacks, in which a cybercriminal impersonates a trusted source. Domain spoofing is a representative example in which attackers impersonate a legitimate website to intercept or steal sensitive information.
How To Check If an Email Is Legit or a Phishing Email?
Several established methods for identifying phishing emails remain relevant.
- Hovering over all links and the sender's email address to verify their legitimacy before engaging.
- Inspecting attachments and refraining from downloading any file without independent verification from a trusted source.
- Checking for inconsistencies throughout the content, including grammatical errors and poor writing quality.
However, as generative AI produces increasingly convincing phishing communications, identifying the psychological triggers cybercriminals employ has become as important as scrutinizing email content. Key indicators include the following.
- Urgency
- Authority
- Fear
- Curiosity
- Alignment with peak stress moments, as cybercriminals deliberately time attacks to coincide with periods of heightened vulnerability
What Is a Good Phishing Click Rate?
The click rate of an effective phishing simulation varies according to an organization's cybersecurity maturity level. According to Verizon's 2025 Data Breach Investigations Report, the average click rate on phishing stands at 2.7%. This figure represents a solid initial benchmark for organizations designing their simulations.
What Happens If an Employee Fails a Phishing Test?
In a well-designed phishing simulation, failure is not only unsurprising but expected. Phishing simulations are intended to serve as learning experiences, and failures identify the specific areas where an employee requires development. This learning opportunity is most effective when corrective instruction follows the failure immediately.
Can an Employee Be Fired for Failing a Phishing Test?
In most cases, failing a phishing simulation does not result in termination. However, repeated failures, combined with additional factors such as a high-risk organizational role, insufficient evidence of improvement, or operations within a heavily targeted industry, may warrant more serious consequences.
Can Phishing Access Your Phone?
Phishing does not directly compromise a device but can do so indirectly. The objective of phishing is to obtain sensitive information through communication channels, many of which are accessible via mobile devices, including email, SMS, and voice. Through these channels, cybercriminals can acquire data that may subsequently be used to compromise the device itself.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents