Whaling phishing has become the most financially devastating form of social engineering targeting enterprises today. According to the FBI's IC3 2025 Internet Crime Report, business email compromise generated over $3 billion in verified losses from 24,768 complaints, making it the second-most financially devastating cybercrime in the United States.

A single successful CEO fraud phishing incident can cost an organization millions in a matter of hours, and the human cost extends to terminated executives, lost jobs, and permanent reputational damage.
Unlike broad phishing campaigns that cast a wide net, whaling phishing is surgically precise. Cyberattackers invest weeks or months researching a single executive, crafting communications so convincing that traditional email filters and even seasoned security leaders struggle to identify them.
This guide provides C-level executives and security teams with the comprehensive knowledge needed to defend against whaling phishing attacks. It covers:
- What whaling phishing is and how it differs from standard phishing and spear phishing;
- Who within an organization is most vulnerable to whaling phishing;
- How whaling phishing attacks unfold across five stages;
- Documented real-world whaling phishing cases;
- The WHALE framework for detecting whaling phishing attempts;
- Prevention strategies and incident response protocols for whaling phishing;
- How Adaptive Security strengthens executive-level defenses against whaling phishing.
Adaptive Security's executive-grade simulations prepare your organization before the next whaling attack finds its target.
What Is Whaling Phishing?
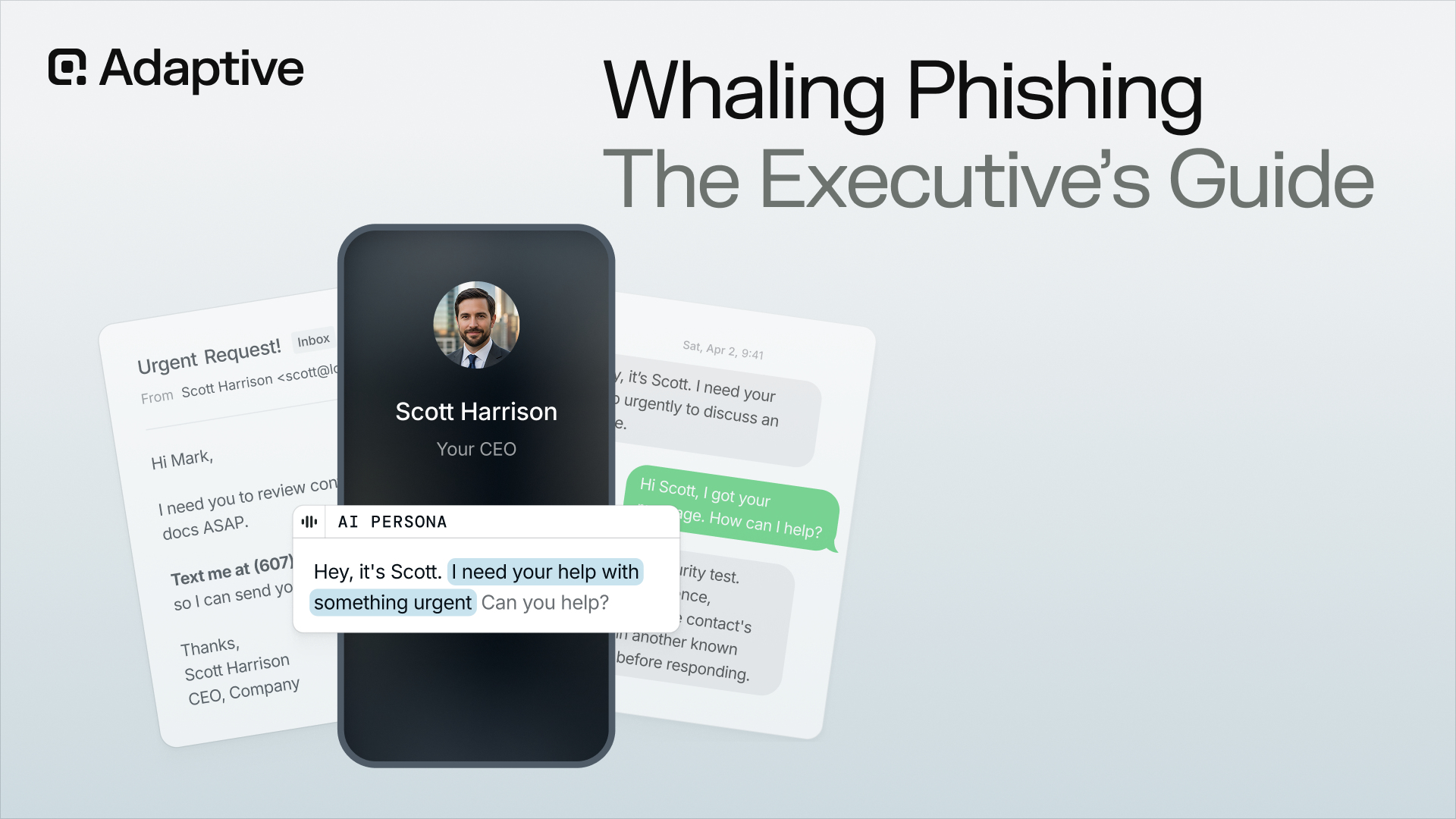
Whaling phishing is a highly targeted form of spear phishing that focuses exclusively on C-level executives, senior managers, board members, and other high-authority individuals within an organization.
The term "whaling" reflects the metaphor at the heart of this attack type: if standard phishing is a net cast into the ocean, whaling phishing targets the biggest fish in the sea. These are the leaders whose authority, access, and decision-making power make them uniquely valuable to cyberattackers.
Whaling phishing is also commonly referred to as CEO fraud phishing or executive phishing, though these terms carry slightly different meanings depending on context. What unites them is the profile of the target: individuals whose authorization can unlock large financial transactions, grant access to sensitive systems, or release confidential data without further approval.
According to GetApp's 2024 Executive Cybersecurity Survey, 72% of U.S. senior executives had been targeted by a cyberattack at least once in the previous 18 months, demonstrating that virtually every executive is on a cyberattacker's list.
What distinguishes whaling phishing from other forms of phishing is not simply the seniority of the target but the depth of preparation behind each attack. Before a single message is sent, cyberattackers:
- Conduct extensive open-source intelligence gathering, study the executive's communication style;
- Identify their direct reports;
- And craft messages that reference real projects, colleagues, and organizational context.
The resulting emails are often indistinguishable from genuine correspondence on first read, which is precisely why they succeed where broader phishing attempts fail.
Prepare executives with Adaptive Security's built-in, AI-powered, immersive whaling phishing simulations.
What Is CEO Fraud Phishing?
CEO fraud phishing is a specific subtype of whaling phishing where cyberattackers impersonate a CEO or senior executive to manipulate employees (typically in finance or human resources) into transferring funds or sharing sensitive data. The impersonation flows outward from the executive to their subordinates, weaponizing the authority and trust that employees extend to senior leadership.

CEO fraud phishing overlaps substantially with business email compromise (BEC), though the two are not identical. BEC is a broader category that includes vendor impersonation and other non-executive scenarios, while CEO fraud specifically exploits the executive-to-employee dynamic.
In a CEO fraud attack, the executive is not the direct victim; the victim is the staff member who receives the fraudulent request. In pure whaling phishing attacks, the executive is the one being deceived directly.
Train employees to recognize and shut down CEO fraud phishing attempts with Adaptive Security before a single dollar moves.
What Is a Typical Feature of CEO Fraud Phishing?
The defining feature of CEO fraud phishing is the near-total absence of the technical red flags associated with standard phishing. Most CEO fraud phishing emails contain no malicious links, no malware attachments, and no overtly suspicious payloads. Instead, they rely entirely on social engineering: the manufactured authority of a senior executive, combined with urgency and confidentiality framing that discourages the recipient from verifying the request out-of-band.
A typical CEO fraud phishing email requests a wire transfer, a change to vendor payment details, or the release of sensitive employee or customer data. The request is framed as time-sensitive and confidential, often citing a pending acquisition, an unexpected opportunity, or a regulatory deadline.
According to Crowdstrike's 2025 Global Threat Report, 79% of attacks to gain initial access are now malware-free, with adversaries relying on social engineering, stolen credentials, and impersonation rather than technical exploits. This is precisely why CEO fraud phishing evades conventional email security filters; there is no malicious payload to scan for.
Keep every employee sharp to the signs of CEO fraud phishing with Adaptive Security's continuously updated awareness training.
Whaling Phishing vs. Phishing and Spear Phishing
Whaling phishing sits at the apex of a three-tier targeting pyramid, with standard phishing at the base and spear phishing in the middle. Understanding how the three types of phishing attacks differ is essential for building proportionate defenses; because the controls that work against mass phishing often fail entirely against whaling phishing.
Whaling Phishing vs. Standard Phishing
Standard phishing is broad and opportunistic. Cyberattackers send millions of nearly identical emails to harvested address lists, hoping a small percentage of recipients will click a malicious link or enter credentials on a spoofed page. Personalization is minimal, and the attacks rely on volume rather than precision.
According to Malwarebytes' AI-Supported Spear Phishing Fools More Than 50% of Targets, generic phishing emails achieved just a 12% click-through rate (CTR) in controlled testing, reflecting the low conversion rate of mass campaigns. It's a stark contrast to the extremely high personalization and CTR of whaling phishing attacks.
Whaling Phishing vs. Spear Phishing
Spear phishing is the next tier up. Cyberattackers narrow their focus to specific individuals or departments, personalizing emails with details such as the recipient's name, role, current projects, or recent activities. This level of personalization increases credibility and, consequently, success rates.
Spear phishing campaigns typically target mid-level employees with meaningful access to financial systems, customer data, or network infrastructure, though the investment per target is still relatively modest compared to whaling phishing.
For a deeper examination of the mid-tier of this spectrum, organizations should consult the full guide to spear phishing detection, prevention, and mitigation.
Whaling Phishing vs. Vishing
Vishing, or voice phishing, has emerged as a critical adjacent channel in whaling phishing campaigns. Cyberattackers now routinely combine a fraudulent email with a follow-up phone call from someone posing as a CFO, CEO, or external auditor, using the call to reinforce the email's urgency and answer the target's natural skepticism in real time. A finance manager who might have paused to verify a wire transfer request via email will often proceed when a persuasive voice on the other end of the line confirms the instructions.
According to Vectra AI's Whaling Attacks Explained: How Executives Become High-Value Targets, deepfake-enabled vishing surged over 1,600% in Q1 2025 compared to the end of 2024, indicating that voice-based whaling phishing is no longer an emerging risk but an active and rapidly accelerating one.
Phone-based whaling phishing bypasses email authentication protocols entirely. DMARC, DKIM, and SPF provide no protection against a fraudulent phone call, which is why organizations must establish strict out-of-band verification protocols that do not rely on the channel used to deliver the initial request.
Expose your organization to hyperrealistic deepfake vishing simulations through Adaptive Security, so that an attack never catches anyone off guard.
These three categories frequently appear together in coordinated campaigns. A cyberattacker may begin with standard phishing to compromise a low-level employee account, use that access to conduct internal reconnaissance (a form of spear phishing), and then launch a whaling attack from the compromised insider address. Therefore, defending against whaling phishing requires understanding the full attack chain, not just the final phishing email that arrives in an executive's inbox.
Who Is Vulnerable to Whaling Phishing Attacks?
The primary targets of whaling phishing attacks are executives whose authority grants them the ability to authorize significant financial transactions, access sensitive data, or control critical systems.
- CEOs are the archetypal target, given their public visibility and broad authority, though they are not always the most frequently attacked.
- CFOs are often the higher-priority target because they directly control wire transfers and payment authorizations.
- COOs are the next priority as they command operational decision-making authority that can unlock contract signings and vendor changes.
- CHROs hold vast repositories of employee personal data, tax records, and payroll information.
Apart from the aforementioned high-priority individuals, board members are particularly attractive targets because they possess insider knowledge of strategic initiatives, pending acquisitions, and financial performance; yet they often operate outside the organization's internal security controls.
Give your executives rigorous, realistic whaling phishing simulations that cyberattackers fear most — built by Adaptive Security.
Senior IT and security leadership face their own distinctive risk profile. Their credentials can unlock access to the entire organizational environment, making them valuable not for direct financial fraud but as pivots into deeper network compromise.
Cyberattackers build target profiles through systematic open-source intelligence gathering.
- LinkedIn provides organizational hierarchies and direct reporting relationships.
- Press releases and company websites reveal project names, strategic priorities, and executive travel schedules.
- SEC filings and earnings call transcripts expose financial terminology and internal vocabulary.
- Personal social media accounts fill in the human details: family members, hobbies, travel patterns, and relationships that make impersonations convincing.
Why Are Executives Vulnerable to Whaling Phishing Attacks?
Executives are both the most powerful and least regulated actors in organizational security. They hold the most authority and the broadest access to sensitive systems. But they are also frequently granted exemptions from the standard security protocols applied to general staff.
Time pressure compounds this problem. Executives process hundreds of emails daily, often on mobile devices while traveling, and are conditioned to make rapid decisions with incomplete information.
Executive visibility also creates a research advantage for cyberattackers. A senior leader's public profile on LinkedIn, press releases, company bio pages, and across social media provides a richer intelligence base than any other role in the organization.
According to the GetApp's 2024 Executive Cybersecurity Survey, 37% of companies globally do not provide specialized cybersecurity awareness training to their senior executives, leaving a critical gap in their defenses exactly where a successful attack does the most damage.
Close the executive training gap — starting with Adaptive Security. Don't leave your most powerful targets as your most exposed ones.
Board Members and CISOs as Emerging Whaling Phishing Targets
Board members and CISOs are increasingly targeted by whaling phishing attacks. However, many organizations haven't updated their defenses to address this.
Board members operate largely outside the internal security controls applied to full-time staff. They conduct sensitive business through personal devices and non-corporate email accounts, review confidential materials on unmanaged laptops, and rarely participate in the phishing simulation cadences that reach regular employees. Their insider knowledge of pending mergers and acquisitions, earnings results, and strategic initiatives makes them exceptionally valuable targets for cyberattackers pursuing financial gain or market manipulation.
CISOs and senior security leaders face a different risk profile. They are not targeted for direct financial fraud, but they are used as network pivots. A compromised CISO account grants cyberattackers access to the full security stack, incident response playbooks, privileged access management systems, and the organization's most sensitive threat intelligence.
The contradiction between the importance and appropriate defense is alarming. Most corporate cybersecurity awareness training programs still exclude board members and CISOs from standard phishing simulations on the assumption that these roles are too senior or too security-aware to require routine testing. Cyberattackers are aware of this assumption and actively exploit it during attacks.
Bring board members and CISOs into Adaptive Security's simulation program before that gap is exploited.
Industries Most Targeted by Whaling Phishing Attacks
Whaling phishing targeting patterns vary meaningfully across industries, mostly shaped by the asset types each sector controls and the regulatory exposure that follows a breach.
- Financial services firms experience the highest volume of attacks. CFOs, treasury managers, and wealth advisors are most at risk because they control client funds and corporate assets. The speed and finality of transactions in this sector make recovery after a successful whaling phishing attack especially difficult.
- Healthcare organizations are targeted through multiple phishing attack vectors. CEOs and CFOs face wire-fraud attempts related to acquisitions and vendor payments, while CHROs and privacy officers are targeted for patient data that commands high prices on underground markets and increases exposure to regulatory enforcement under HIPAA.
- Manufacturing and industrial firms see a distinct pattern driven by vendor email compromise (VEC) schemes, in which attackers impersonate international suppliers and intercept supply-chain payments that often move across borders before the fraud is detected.
- Legal and professional services firms are targeted for the confidential client data they hold. Managing partners and client relationship leads receive fraudulent requests involving client trust accounts, M&A documentation, and privileged correspondence; reputational harm from a breach in this sector often exceeds the direct financial loss.
Get your industry-appropriate whaling phishing defenses live in minutes with Adaptive Security.
Whaling Phishing and CEO Fraud Statistics for 2025
- According to GetApp's 2024 Executive Cybersecurity Survey, 72% of U.S. senior executives had been targeted by a cyberattack at least once in the previous 18 months.
- According to GetApp's 2024 Executive Cybersecurity Survey, AI-generated deepfakes were involved in 27% of the cyberattacks targeting senior executives in the past 18 months.
- According to Vectra AI's Whaling Attack, whaling attacks targeting senior executives averaged $137,000 in losses per incident in 2024.
- According to Abnormal Security's BEC and VEC Attacks Continue to Surge, BEC attacks grew by more than 50% between H2 2023 and H1 2024, with organizations of 50,000 or more employees facing a near-100% weekly probability of experiencing at least one BEC attack.
- According to the FBI's IC3 2024 Internet Crime Report, phishing and spoofing led all crime categories with 193,407 complaints, the most reported crime type of the year, out of 859,532 total complaints filed.
- According to the FBI's IC3 2024 Internet Crime Report, BEC losses totaled $2.77 billion across 21,442 reported incidents, representing more than 17% of all $16.6 billion in recorded cybercrime losses for the year.
- According to the AFP's 2025 Payments Fraud and Control Survey Report, 63% of organizations experienced Business Email Compromise in 2024.
- According to IBM's Cost of a Data Breach Report 2024, the average global cost of a data breach reached $4.88 million, a 10% jump and the biggest year-over-year increase since the pandemic, with phishing ranking as the second-most costly initial attack vector at an average of $4.76 million per breach.
- According to the FBI's IC3 2025 Internet Crime Report, BEC generated over $3 billion in verified losses from 24,768 complaints, making it the second-most financially devastating cybercrime in the United States.
- According to Proofpoint's Email Attacks Drive Record Cybercrime Losses in 2024, the FBI's IC3 Recovery Asset Team reported a 66% success rate in freezing fraudulent BEC transfers, underscoring the critical importance of reporting incidents immediately.
- According to IBM's Cost of a Data Breach Report 2024, employee security awareness training ranked as the number one factor in decreasing the average cost of a breach, specifically for detecting and stopping phishing attacks.
- According to the GetApp's 2024 Executive Cybersecurity Survey, 37% of companies globally do not provide specialized cybersecurity training to their senior executives, leaving a critical gap in their defenses.
- According to Crowdstrike's 2025 Global Threat Report, AI-driven phishing and impersonation tactics fueled a 442% increase in voice phishing between H1 and H2 2024, as threat actors weaponized generative AI to supercharge social engineering operations.
- According to Crowdstrike's 2025 Global Threat Report, 79% of attacks to gain initial access are now malware-free, with adversaries relying on social engineering, stolen credentials, and impersonation rather than technical exploits.
- According to Malwarebytes' AI-Supported Spear Phishing Fools More Than 50% of Targets, LLM-generated spear-phishing emails achieved a 54% click-through rate in controlled testing, compared to just 12% for generic phishing emails, matching the effectiveness of human expert attackers.
- According to Vectra AI's Whaling Attack, deepfake-enabled vishing surged over 1,600% in Q1 2025 compared to the end of 2024, and deepfake fraud losses exceeded $200 million in North America in Q1 2025 alone.
- According to Vectra AI's AI Scams, AI-enabled fraud surged 1,210% in 2025, with projected losses reaching $40 billion by 2027 as AI tools continue to democratize social engineering at scale.
- According to Proofpoint's 2024 Voice of the CISO Report, 74% of CISOs identified human error as their organization's biggest cybersecurity vulnerability, making executive behavior and awareness training a board-level priority.
How Whaling Phishing Attacks Work
A whaling phishing attack is a multi-stage operation that unfolds over days, weeks, or even months. Unlike standard phishing (which relies on volume and probability), whaling phishing attacks are built on careful preparation, deliberate target selection, and patient execution. Each stage builds on the previous one, and the final fraudulent request arrives only after cyberattackers have assembled enough context and credibility to make the request appear routine.
The lifecycle of a whaling phishing attack can be broken down into five distinct stages: reconnaissance, target selection, impersonation setup, the fraudulent request, and execution and exfiltration.
Modern whaling phishing attacks increasingly span multiple interactions across these stages, with cyberattackers sending seemingly innocuous messages to build trust before escalating to the fraudulent ask. This multi-stage structure is what makes whaling phishing substantially harder to detect than single-email phishing attempts, since each individual message alone may appear unremarkable.
Adaptive Security's micro-lessons teach executives precisely what public exposure gives cyberattackers, and how to close that window before it becomes a campaign.
Stage 1 of a Whaling Phishing Attack: Reconnaissance
Reconnaissance is the foundation of every successful spear phishing and whaling phishing campaign. Cyberattackers gather open-source intelligence (OSINT) on the target organization and its executives through systematic research across publicly available sources.
- LinkedIn profiles reveal organizational hierarchies, direct reporting relationships, and recent role changes.
- Press releases and corporate blog posts expose strategic initiatives and executive priorities.
- SEC filings and earnings call transcripts provide financial terminology, vendor names, and insider vocabulary that later appear in fraudulent messages.
Personal social media accounts fill in the remaining gaps. A CEO's Instagram posts can reveal travel schedules, creating the perfect window for an impersonation attempt when the executive is known to be unreachable.
The objective of reconnaissance is to map the organizational landscape in sufficient detail that the cyberattacker can convincingly impersonate a trusted figure and select the optimal target for the fraudulent request.
Stage 2 of a Whaling Phishing Attack: Target Selection
Whaling phishing target selection converts reconnaissance into operational intent. Cyberattackers weigh several factors before committing resources to a campaign. Authority over financial transactions, access to sensitive data, public visibility, and the perceived likelihood of compliance under pressure all feed into the decision.
A CFO with sole signing authority on transfers above a certain threshold is more valuable than a CFO at an organization with mandatory dual-approval workflows. An executive with an active travel schedule visible on social media is more attractive than one who is consistently in the office and reachable for verification.
Make your executives harder to deceive with Adaptive Security's targeted simulations to recognize when they've been selected as a target.
Targets also fall into two operational categories: direct targets, where the executive is the one deceived; and indirect targets, where the executive is impersonated to deceive their subordinates (CEO fraud phishing).
An important distinction is that the direct target of a CEO fraud phishing attack is rarely the CEO themselves. More often, it is a finance manager, accounts payable specialist, or HR coordinator who reports to the executive.
The impersonated figure is chosen for their authority over the selected target. If the target is in accounts payable, the impersonated figure is likely the CFO or a senior finance leader. If the target is in HR, the impersonated figure may be the CHRO or the CEO. The power dynamic between the impersonated sender and recipient is what creates the psychological pressure in CEO fraud phishing to comply without verification.
Train finance and HR staff against the psychological pressure of CEO fraud phishing with Adaptive Security's role-specific training scenarios.
Stage 3 of a Whaling Phishing Attack: Impersonation Setup
Impersonation setup is where cyberattackers prepare the technical infrastructure for the whaling phishing attack. This stage includes registering spoofed domains that mimic the target organization's legitimate domain, often using character substitution tricks such as replacing the letter "m" with the letters "rn" to create the visual illusion of the original. Compromised insider email accounts, obtained through prior phishing of lower-level employees, are often preferred because they bypass email authentication checks entirely.
Cyberattackers also prepare lookalike login pages to capture credentials if the attack plan includes a credential theft component. Increasingly, AI-generated content is used to mimic the impersonated target's writing style, tone, and vocabulary. According to Malwarebytes' AI-Supported Spear Phishing Fools More Than 50% of Targets 2025, LLM-generated spear-phishing emails achieved a 54% click-through rate in controlled testing, matching the effectiveness of human expert whaling phishing attackers.
Stage 4 of a Whaling Phishing Attack: The Fraudulent Request

The fraudulent request is the centerpiece of the whaling phishing attack. The message is sent to the selected target, typically framed with two core psychological levers: authority and urgency. Common requests include wire transfers for acquisitions, changes to vendor payment details, release of employee tax records, and issuance of gift cards for client or staff recognition.
Modern whaling phishing campaigns rarely deliver the fraudulent request in a cold email. Cyberattackers often send multiple benign messages first, establishing rapport and creating a sense of ongoing correspondence. By the time the fraudulent ask arrives, the target perceives it as a continuation of a trusted thread rather than an isolated suspicious event.
Make it the standard for your team to interrogate even familiar-looking threads with the help of Adaptive Security — simulating the multi-stage trust-building tactics real attackers use.
Stage 5 of a Whaling Phishing Attack: Execution and Exfiltration
Execution is where the whaling phishing attack achieves completion.
- The victim completes the requested action, e.g. the wire transfer is sent, credentials are submitted on the spoofed page, or sensitive data is forwarded to the fraudulent address.
- Cyberattackers move stolen funds rapidly through layered accounts, often routing them through multiple jurisdictions within hours to frustrate recovery efforts.
- Stolen credentials are used to pivot deeper into the network, establishing persistence for future attacks or enabling lateral movement toward even higher-value targets.
The window for recovery narrows quickly. According to Proofpoint's Email Attacks Drive Record Cybercrime Losses in 2024, the FBI's IC3 Recovery Asset Team reported a 66% success rate in freezing fraudulent BEC transfers, underscoring the critical importance of reporting incidents immediately. Every hour of delay between execution and reporting reduces the probability of fund recovery.
How Whaling Phishing Attacks Are Evolving
Whaling phishing attacks are evolving faster than at any point in history, driven primarily by the democratization of generative AI.
- AI now produces whaling phishing and CEO fraud phishing messages and emails that mimic an executive's voice and tone with remarkable accuracy. Cyberattackers feed public correspondence, earnings call transcripts, and published articles into large language models to generate fraudulent emails that match the executive's distinctive style.
- Deepfake AI audio and video have added a new dimension to whaling phishing attacks. According to Vectra AI's Whaling Attack, deepfake-enabled vishing surged over 1,600% in Q1 2025 compared to the end of 2024, and deepfake fraud losses exceeded $200 million in North America in Q1 2025 alone. Cyberattackers now impersonate executives on live video calls, voicemails, and voice messages with convincing fidelity. According to GetApp's 2024 Executive Cybersecurity Survey, AI-generated deepfakes were involved in 27% of cyberattacks targeting senior executives in the past 18 months.
See an AI-generated deepfake of yourself in a controlled environment — Adaptive Security delivers the highest-fidelity executive impersonation simulations available.
- Compromised insider accounts are replacing fake addresses as the preferred delivery method. When a whaling phishing email arrives from a legitimate colleague's account, domain authentication provides no protection. Cyberattackers obtain these accounts through prior phishing, credential stuffing, or direct purchase on underground markets.
- Exploitation of ongoing events has also become systematic. Cyberattackers time whaling phishing attacks around announced mergers and acquisitions, earnings seasons, executive travel, regulatory deadlines, and public crises. These events create genuine urgency within the organization, which cyberattackers then mirror in fraudulent requests to blend into the noise of legitimate business activity.
Organizations facing these advanced impersonation threats should review how to detect and stop AI executive impersonation attacks as part of their executive protection program.
Types of Whaling Phishing Attacks
Whaling phishing manifests in several distinct attack patterns, each exploiting different organizational workflows and trust relationships. The variants below represent the most common and financially damaging forms. Most successful whaling phishing campaigns combine elements from more than one type, which is why understanding the full taxonomy is essential. Defensive controls effective against one variant of phishing attacks often provide little protection against another.
Business Email Compromise (BEC)
Business email compromise (BEC) is the broadest category, encompassing whaling phishing attacks. At its core, BEC involves cyberattackers either compromising legitimate executive email accounts through prior credential theft or spoofing those accounts using lookalike domains, then using the resulting access to manipulate employees, vendors, or business partners into transferring funds or sharing sensitive data. According to the FBI's IC3 2024 Internet Crime Report, BEC losses totaled $2.77 billion across 21,442 reported incidents, representing more than 17% of all $16.6 billion in recorded cybercrime losses for the year.
BEC and CEO fraud phishing overlap substantially in practice; CEO fraud phishing is best understood as a subset of BEC focused specifically on executive-to-employee impersonation.
Vendor Email Compromise (VEC)
Vendor email compromise (VEC) applies BEC techniques to the supplier and partner relationship layer. Cyberattackers impersonate a known vendor or compromise the vendor's actual email account, then send fraudulent invoices, altered banking details, or revised payment instructions to the finance and procurement teams at the target organization. The recipients are typically executives, controllers, and accounts payable specialists who routinely process supplier payments.
VEC attacks are often combined with whaling phishing style personalization, referencing real contracts, project codes, and prior correspondence to increase credibility. The longer-running the vendor relationship, the more damaging a successful VEC attack tends to be.
CEO Fraud Phishing Emails
The classic CEO fraud phishing email impersonates a CEO or senior executive to instruct finance or HR staff to carry out an urgent, confidential transaction. There are no malicious attachments, no embedded links, and no malware payloads of any kind. The attack relies entirely on authority and urgency.
The message typically arrives outside normal business hours, references a confidential matter the recipient cannot discuss with colleagues, and demands action within a small timeframe. Common requests include wire transfers for pending acquisitions, gift card purchases for client recognition, and the release of employee tax documentation. The absence of any technical indicator is precisely what allows CEO fraud phishing emails to bypass traditional email security controls.
Internal Payment Fraud and Payroll Diversion
Internal payment fraud and payroll diversion are closely related variants of whaling phishing that target the organization's payment infrastructure directly. In internal payment fraud, cyberattackers impersonate an executive with payment authority, typically the CFO or a senior finance leader, and instruct the finance team to redirect a corporate payment to a fraudulent account under the guise of an urgent vendor change or confidential transaction. Payroll diversion targets HR and payroll teams instead, with cyberattackers impersonating either an executive or an individual employee to reroute direct deposits to attacker-controlled accounts.
Both variants depend on the same psychological levers as broader CEO fraud phishing: the authority of the impersonated figure, manufactured urgency, and the discouragement of independent verification.
Malicious Payloads
Malicious payloads are less common in whaling than in standard phishing, but they have not disappeared from the threat landscape. Cyberattackers embed malware in seemingly legitimate documents such as PDFs, Word files, and Excel spreadsheets, often disguised as contracts, board presentations, or vendor invoices. Once opened by an executive or their assistant, the malicious payload installs ransomware, keyloggers, or remote access tools that grant cyberattackers persistent access to executive devices.
The relative rarity of payload-based whaling reflects the success of modern email security controls at detecting attachments, which is why most cyberattackers now favor pure social engineering instead.
Credential Theft and Account Takeover
Credential theft is often a precursor to larger whaling phishing attacks rather than the end goal itself. Cyberattackers craft emails that direct executives to spoofed internal portals, fake cloud login pages, or fraudulent multi-factor authentication prompts. Once the executive enters their credentials, cyberattackers gain access to the legitimate account and can launch further attacks from a trusted internal address.
Account takeover removes domain authentication as a defensive layer entirely, because subsequent emails genuinely originate from the compromised executive's mailbox. This is why credential theft is increasingly the opening move in multi-stage whaling campaigns rather than a standalone attack.
Email Spoofing
Email spoofing is the foundational technique behind many whaling phishing variants. Cyberattackers forge the sender's email address to make a message appear to originate from a trusted executive or vendor. The simplest form is display name spoofing, where the visible "from" name matches a trusted executive while the underlying email address is unrelated; this technique is cheap, requires no technical infrastructure, and remains effective against recipients who do not inspect full email headers.
Full domain spoofing is more sophisticated and succeeds primarily against organizations that have not properly configured DMARC, DKIM, and SPF authentication. Email spoofing rarely appears in isolation; it typically serves as the entry point for other whaling attack types described above.
Executive Smishing and SMS-Based Whaling Phishing
Executive smishing is an emerging whaling phishing variant that exploits the mobile channel. Cyberattackers send text messages to executives or their direct reports, posing as the CEO and typically claiming to be stuck in a meeting, traveling, or otherwise unable to use their normal email. The fraudulent request often involves an urgent gift card purchase, a confirmation of a wire transfer that supposedly went out earlier, or the verification of a banking detail.
Mobile devices lack the filtering infrastructure of corporate email environments, and the informal nature of SMS lowers the recipient's guard in a way that few corporate channels do. The rise of executive smishing reflects the broader shift toward mobile-first executive communication, with senior leaders increasingly conducting business via text outside normal working hours.
Documented Examples of Whaling Phishing Attacks
Documented whaling phishing cases provide a concrete view of how these attacks progress inside real organizations and what they cost when defenses fail. The cases below are framed as organizational risk studies, with attention focused on the operational mechanics and the consequences for the affected enterprise. Each illustrates a different facet of executive-targeted social engineering, from spoofed-domain BEC to long-running impersonation campaigns reinforced by external co-conspirators.
The Ubiquiti Networks CEO Fraud Incident
In 2015, Ubiquiti Networks disclosed a CEO fraud phishing scheme that cost the networking equipment manufacturer $46.7 million. Cyberattackers impersonated senior executives and external entities, then deceived finance staff at the company's Hong Kong subsidiary into transferring funds to overseas accounts controlled by the attackers. The fraudulent requests were structured around what appeared to be a confidential acquisition, a framing that discouraged the involved staff from seeking independent verification through normal corporate channels.
Ubiquiti disclosed the incident in an SEC Form 8-K filing, making it one of the most prominent publicly documented whaling phishing cases of its era. The company was able to recover or freeze approximately $8.1 million of the stolen funds, though the majority remained unrecoverable. The incident has since become a standard reference point in cybersecurity awareness training programs and a foundational case study in the financial scale that CEO fraud phishing can achieve against publicly traded enterprises.
The FACC AG CEO Fraud Case
The Austrian aerospace components supplier FACC AG lost approximately €50 million in 2016 after cyberattackers impersonated the company's chief executive officer in a CEO fraud phishing campaign. The fraudulent emails instructed finance staff to transfer funds for what was framed as a confidential acquisition project, and the requests bore enough hallmarks of executive authenticity that internal controls did not catch the deception before the funds had moved.
The case is notable not only for its financial scale, but also for the leadership consequences that followed. The supervisory board subsequently dismissed the CEO, citing severe violations of duty in connection with the incident.
The FACC case stands as the clearest publicly documented illustration that whaling phishing carries reputational and governance consequences extending well beyond the immediate financial loss. The board-level response highlighted that responsibility for executive-targeted social engineering attacks is increasingly being assigned to the executives whose authority was exploited, regardless of whether they personally authorized the fraudulent transactions.
The Scoular Company Wire Transfer Fraud
The Nebraska-based commodities trader Scoular Company lost $17.2 million in 2014 after a controller received fraudulent emails impersonating the CEO and authorizing what was presented as a confidential acquisition wire transfer. The attack stood out for the depth of its impersonation strategy.
Cyberattackers reinforced the fraudulent CEO fraud phishing emails by posing as an outside auditor from a recognizable accounting firm, providing the controller with what appeared to be independent confirmation of the legitimacy of the transfer instructions.
By presenting a coordinated narrative across multiple apparent sources, cyberattackers eliminated the verification path that the controller might typically have followed. The Scoular case remains an instructive example of how sophisticated whaling phishing attacks can defeat single-channel verification simply by spoofing additional channels in parallel.
What Are the Signs of Whaling Phishing Emails?
Identifying a whaling phishing email under time pressure is one of the most consequential cybersecurity skills any executive or finance team member can develop. Cisco's WHALE acronym provides a structured detection framework that gives security teams a fast, memorable checklist for evaluating suspicious emails before acting on them. The five letters represent five distinct evaluation steps:
- Who sent the email;
- Have a look at the subject line;
- Attachment inspection;
- Look at the content;
- Enquire about the request.
The framework works because it forces deliberate evaluation across multiple attack surfaces. Cyberattackers can defeat any single check in isolation, but defeating all five simultaneously is significantly harder. The sections below walk through each step in detail.
Adaptive Security strengthens executive defenses with simulations built for the exact tactics the WHALE framework is designed to catch.
For organizations seeking a deeper treatment of email-level detection beyond the WHALE framework, the comprehensive guide to identifying a whaling phishing email offers an expanded reference.
W: Who Sent the Whaling Phishing Email?
The first evaluation step in any whaling phishing assessment is the sender domain. Cyberattackers routinely register visually similar domains that defeat casual inspection, such as substituting the letters "rn" for "m" to turn "amazon.com" into "arnazon.com," or replacing a capital "I" with a lowercase "l" in legitimate-looking corporate domains. Recipients reading on mobile devices are particularly vulnerable to these substitutions.
Free webmail domains such as Gmail, Yahoo, and Outlook are also common in whaling phishing attacks because they pass standard email authentication checks. A message claiming to originate from a CEO but sent from a personal Gmail account should always trigger verification, even if the display name and signature appear legitimate. The full email address must be inspected, rather than just the display name shown in the inbox preview.
H: Have a Look at the Subject Line in Whaling Phishing Emails
Subject lines in whaling phishing attacks weaponize urgency and false familiarity. Words such as "Urgent," "Confidential," "Wire Transfer Required," "Action Needed," and "Important" are standard manipulation tools designed to push the recipient to act before verifying. Cyberattackers also exploit threading prefixes such as "Re:" and "Fwd:" to create the impression of an ongoing conversation that the recipient may simply not remember.
The defensive principle is straightforward: a subject line designed to compress decision-making time is itself a red flag. Legitimate executive requests rarely require the recipient to bypass standard verification timelines.
A: Attachment Inspection in Whaling Phishing Emails
Attachments appear less frequently in whaling phishing than in standard phishing campaigns, but they remain a consistent threat vector. Unexpected PDFs, Word documents, Excel spreadsheets, and compressed archives should be scrutinized carefully, particularly when the message arrives outside normal business hours or from a sender who does not typically include attachments.
Cyberattackers also increasingly direct targets to third-party forms hosted on services such as Google Forms or Typeform. These platforms can bypass corporate email security filters because the link itself points to a legitimate domain, while the form is engineered to harvest credentials, banking details, or personally identifiable information.
L: Look at the Content of Whaling Phishing Emails
The body of a whaling phishing email is engineered to feel familiar. Cyberattackers populate the message with personal details sourced from open-source intelligence:
- The names of colleagues the recipient works with regularly;
- References to active internal projects;
- Mentions of executive travel schedules;
- Acknowledgments of upcoming corporate events.
The familiarity is manufactured. The most reliable signal remains the request itself. Wire transfers, credential entry on portals reached through email links, and requests to share sensitive data such as employee tax records or customer lists should always trigger verification, regardless of how credible the surrounding context appears. Modern AI-generated CEO fraud phishing attempts are nearly indistinguishable in tone from genuine executive correspondence, meaning the polish of a message is not evidence of its authenticity.
E: Enquire About the Whaling Phishing Request
The final step in evaluating a potential whaling phishing attempt is verification through a separate, trusted channel. Acceptable verification methods include:
- Calling the sender on a phone number obtained from the corporate directory;
- Walking to their desk if they are physically present;
- Messaging them on a verified internal communication platform such as corporate Slack or Microsoft Teams.
Replying to the suspicious email itself is never an acceptable verification method. If the email is fraudulent, the reply reaches the cyberattacker's inbox and confirms that the impersonation is succeeding. Calling a phone number listed within the suspicious email is equally unsafe, as cyberattackers frequently embed attacker-controlled numbers in their messages to intercept verification attempts.
Whaling Phishing Email Examples
The two examples below are fictional and illustrative. They are designed to show what a typical whaling phishing email looks like in practice, with specific red flags annotated for training purposes.
Example 1: CEO Acquisition Wire Transfer Request
From: Daniel Reyes
To: Sarah Chen, Senior Controller
Subject: Re: Confidential — Wire Transfer Required Today
Sarah,
I'm in meetings with legal all day finalizing the Aldridge acquisition we discussed last week. I need you to process a $1.85M wire transfer to the seller's escrow account before 4 PM EST so we can close on schedule. Please don't loop in anyone else on this — the transaction is under NDA and we need to keep the circle small until announcement.
Wire details attached. Let me know once it's sent.
Daniel
Red flags in Example 1:
- Sender domain manipulation: "adaptive-security.co" instead of the legitimate "adaptivesecurity.com";
- Manufactured urgency: "before 4 PM EST" creates artificial time pressure;
- Confidentiality framing: "don't loop in anyone else" discourages standard verification;
- Threading prefix abuse: "Re:" implies a prior conversation that may not exist;
- Bypassed approval workflow: request for single-person authorization on a high-value transfer;
- Unverified attachment: wire details delivered as an attachment rather than through standard treasury channels.
Example 2: CFO Vendor Banking Detail Change
From: Marcus Whitfield
To: Accounts Payable Team
Subject: Urgent: Updated Banking Details for Northwind Logistics
Team,
Northwind just contacted me directly because they've changed banking providers and our last payment was returned. I need you to update their record with the new account information below and reissue the $312,000 payment today. They're holding our shipment until this is resolved.
If you have any questions, text me — I'm traveling and can't take calls.
Marcus
Sent from my iPhone
Red flags in Example 2:
- Free webmail domain: "outlook.com" instead of the corporate domain;
- Channel restriction: "text me, can't take calls" defeats voice verification;
- Vendor banking change: banking detail changes represent a high-fraud-risk category;
- Operational pressure: an invented consequence ("holding our shipment") to force speed;
- Unverified vendor contact: the vendor allegedly contacted the executive directly rather than through standard procurement channels;
- Mobile-device framing: the "Sent from my iPhone" signature is a common tactic used to excuse informality and lower recipient scrutiny.
CEO Fraud Red Flags Checklist
The checklist below provides a reference for evaluating any email or message requesting financial action, credential entry, or sensitive data sharing. Each red flag represents a feature documented across thousands of analyzed CEO fraud phishing emails. The presence of any single item does not automatically indicate fraud, but two or more should always trigger formal verification before any action is taken.
- Unusual sender domain variations. The sender address contains subtle character substitutions ("rn" for "m," lowercase "l" for capital "I"), uses a free webmail provider when a corporate address is expected, or relies on a top-level domain that differs from the organization's standard (".co" instead of ".com");
- Unexpected urgency or confidentiality framing. The message demands action within hours, frames the matter as confidential, instructs the recipient to exclude colleagues or supervisors, or invokes time-sensitive deadlines tied to deals, regulatory matters, or executive travel;
- Requests to bypass standard approval processes. The message asks the recipient to skip dual-approval workflows, override segregation-of-duties controls, or process transactions outside normal procurement channels under the justification of time pressure or executive authority;
- Vague or time-pressured justifications. The reason for the unusual request is described in general terms ("a confidential acquisition," "a regulatory matter") without documentation, contracts, or reference numbers the recipient can verify independently;
- Reply-to addresses differing from the visible sender. The displayed sender appears to be a legitimate executive address, but the reply-to header routes to a different domain or a free webmail account, ensuring replies reach the cyberattacker rather than the impersonated executive;
- Language inconsistent with the executive's known style. The message contains phrasing, formality, or vocabulary that differs from how the impersonated executive normally communicates. Sudden tone shifts, unusual greetings, or atypical sign-offs are early warning signs, particularly for recipients who correspond regularly with that individual;
- Requests for wire transfers, gift cards, or cryptocurrency. Wire transfers to new accounts, bulk gift card purchases, and cryptocurrency conversions are the three most common payout methods in CEO fraud phishing emails. Any such request should trigger formal verification regardless of the apparent sender;
- Refusal to verify via phone or alternate channel. The sender resists confirmation by phone, claims to be in meetings or traveling and unreachable, or insists that all communication remain within email. Legitimate executives expect and support verification on high-value requests;
- Vendor banking detail changes delivered via email. Changes to vendor account numbers, routing information, or payment destinations arriving through email rather than verified treasury or procurement channels represent one of the highest-fraud-risk request types in any organization;
- Executive impersonation outside business hours or during travel. Many CEO fraud phishing emails arrive when the impersonated executive is known to be unreachable or in extended meetings. The deliberate timing is an attack design choice intended to discourage verification.
Provide your team with the pattern recognition skill to catch CEO fraud phishing before it ever reaches execution.
Impact of Whaling Phishing Attacks on Organizations
The total cost of a successful whaling phishing attack typically exceeds the headline financial figure, as remediation, regulatory response, and trust restoration generate substantial secondary expenses. Whaling phishing produces consequences across four interconnected categories:
1. Financial Loss
Financial loss is the most immediate impact. According to Abnormal Security's BEC and VEC Attacks Continue to Surge, BEC attacks grew by more than 50% between H2 2023 and H1 2024, with organizations of 50,000 or more employees facing a near-100% weekly probability of experiencing at least one attack.
2. Data Loss
Data loss compounds the financial impact when whaling phishing involves credential theft or executive account takeover. Compromised executive accounts grant cyberattackers access to intellectual property, trade secrets, employee personally identifiable information, customer records, and confidential strategic documents. The downstream value of stolen data often exceeds the direct fraud loss, particularly when data is sold on underground markets or used for follow-on extortion.
3. Operational Disruption
Operational disruption follows almost every successful whaling phishing attack. According to IBM's Cost of a Data Breach Report 2024, the average global cost of a data breach reached $4.88 million, a 10% year-over-year increase, with phishing ranking as the second-most costly initial attack vector at an average of $4.76 million per breach. The figure includes forensic investigation, system remediation, executive time diverted to incident response, regulatory cooperation, and lost productivity across affected teams.
4. Reputational Damage
Reputational damage is the longest-lasting consequence. Public disclosure of a whaling phishing attack, particularly through SEC filings or breach notification statutes, can erode customer trust, depress stock prices, and trigger boardroom turnover. The FACC AG case, in which the supervisory board dismissed the CEO following a €50 million whaling loss, illustrates that reputational consequences can extend to the executives whose authority was exploited, regardless of personal culpability.
Measure your organization's exposure to whaling phishing before a successful attack forces you to — Adaptive Security's risk monitoring surfaces vulnerabilities across every leadership tier.
Legal and Regulatory Consequences of Whaling Phishing Attacks
The regulatory exposure following a successful whaling phishing attack frequently exceeds the direct financial loss in long-term cost and complexity. Multiple overlapping disclosure requirements can apply simultaneously, each with distinct timelines, thresholds, and reporting formats.
The summary below is informational and does not constitute legal advice; organizations should consult qualified counsel for specific guidance on their obligations.
SEC cybersecurity disclosure rules, effective December 2023, require public companies to disclose material cybersecurity incidents within four business days on Form 8-K, Item 1.05. Whaling phishing attacks resulting in significant financial loss, operational disruption, or compromise of sensitive corporate information typically meet the materiality threshold. Public companies must also describe their cybersecurity risk management strategy and governance in annual Form 10-K filings, meaning a whaling phishing incident often surfaces in subsequent annual disclosures even after the initial 8-K has been filed.
GDPR breach notification requirements apply to any organization processing the personal data of individuals in the European Union. When a whaling phishing attack results in unauthorized access to personal data, supervisory authorities must be notified within 72 hours of awareness, and affected individuals must be notified when the breach poses a high risk to their rights and freedoms. Penalties for non-compliance can reach €20 million or 4% of global annual revenue, whichever is higher.
State-level breach notification laws apply across all 50 U.S. states, with varying thresholds, timelines, and definitions of personal information. Organizations operating across multiple states must navigate overlapping obligations simultaneously, with notification windows ranging from immediate to 60 days depending on jurisdiction.
Director and officer liability has emerged as a significant area of exposure following high-profile cybersecurity incidents. Caremark-style duty-of-oversight claims allow shareholders to pursue board members and senior executives when board-level negligence on cybersecurity governance is alleged. Successful whaling phishing attacks that reveal gaps in board oversight, executive training, or incident response preparation can support these claims.
Industry-specific obligations layer on top of general regimes:
- HIPAA imposes notification and penalty requirements on healthcare organizations whose whaling phishing incidents expose protected health information;
- GLBA imposes safeguarding obligations on financial services firms;
- PCI DSS imposes contractual obligations on any organization handling payment card data;
- Sector-specific regulators, including state insurance commissioners, banking regulators, and FERC for energy infrastructure, may impose additional reporting and remediation requirements.
How to Protect Organizations from Whaling Phishing Attacks
Effective defense against whaling phishing requires a layered architecture that combines technical controls, process controls, and human controls. Email authentication blocks spoofed messages but cannot stop compromised insider accounts. Approval workflows catch fraudulent transfers but not credential theft. Security awareness training builds judgment but does not replace infrastructure. The nine controls below, applied together, materially reduce the probability and impact of a successful whaling phishing attack.
1. Implement Email Authentication (DMARC, DKIM, SPF) to Block Whaling Phishing
Email authentication is the foundation of whaling phishing defense:
- SPF defines which mail servers are authorized to send email on behalf of a domain;
- DKIM cryptographically signs outgoing messages so recipients can verify authenticity;
- DMARC ties the two together and instructs receiving servers how to handle messages that fail authentication.
Deployment alone is insufficient. DMARC must be enforced at the "reject" policy level, as organizations operating at "none" gain reporting visibility but receive no active protection. Most successful domain-spoofing whaling phishing attacks exploit organizations that have published DMARC records without escalating to enforcement.
2. Require Multi-Person Approval for High-Value Transactions
Multi-person approval is the single most effective process control against CEO fraud phishing. Wire transfers, vendor payment changes, banking detail updates, and sensitive data release requests above defined thresholds must require dual or triple authorization across separate individuals. No single employee, regardless of seniority, should be able to authorize material transactions based on an email instruction alone.
Threshold structures should be calibrated to organizational risk tolerance, with lower thresholds for vendor banking changes, where fraud rates are highest. The approval workflow must be enforced through system controls rather than policy alone, as policy-only controls tend to fail under executive pressure.
Pair process controls with the human layer that makes them stick even under executive pressure.
3. Deploy Phishing-Resistant MFA Across Executive Accounts

Multi-factor authentication (MFA) is a baseline cybersecurity control, but not all MFA methods provide equivalent protection against whaling phishing:
- SMS-based MFA is vulnerable to SIM-swapping attacks, in which cyberattackers convince mobile carriers to transfer the executive's phone number to attacker-controlled SIM cards;
- Email-based MFA fails when the executive's email account is compromised;
- Adversary-in-the-middle phishing kits can capture and replay both SMS and email codes in real time.
Executives, board members, and finance staff should use phishing-resistant MFA based on FIDO2 hardware security keys or platform-bound passkeys. These methods cryptographically bind authentication to the legitimate domain, defeating credential phishing at the protocol level.
4. Adopt a Zero Trust Architecture for Executive Access
Zero Trust replaces the implicit trust granted to authenticated accounts with continuous verification of every access request. For executive accounts in a whaling phishing risk environment, this means:
- Device posture checks before granting access to sensitive systems;
- Session-level risk scoring that detects anomalous behavior in real time;
- Just-in-time access to financial systems that expires automatically after an authorized task is complete.
Compromised executive credentials become significantly less valuable in a Zero Trust environment because the credential alone does not unlock downstream actions. Cyberattackers who obtain an executive's password through credential phishing still face device-level, session-level, and application-level checks before they can issue payment instructions or access regulated data.
5. Enforce Out-of-Band Verification Protocols Against CEO Fraud Phishing
Out-of-band verification is the operational backbone of CEO fraud phishing defense. Any financial or sensitive data request received via email must be confirmed through a separate channel: a verified phone number from the corporate directory, an in-person confirmation, or a secure internal messaging platform. The verification channel must differ from the channel used to deliver the original request.
This protocol must be embedded in standard operating procedure rather than delivered through training material alone. Standard operating procedures survive personnel turnover, executive pressure, and high-stress incidents in ways that training alone cannot. Finance teams should be empowered to delay or refuse transactions until verification is complete.
6. Deliver Executive-Targeted Cybersecurity Awareness Training
Standard phishing awareness training programs are insufficient for C-suite whaling phishing risk. The social engineering tactics used against executives differ meaningfully from those applied to general staff:
- Deeper personalization using open-source intelligence;
- AI-generated executive impersonation that replicates individual writing styles;
- Multi-stage trust-building campaigns conducted over weeks or months;
- Exploitation of current corporate events such as acquisitions, restructuring, or earnings periods.
According to IBM's Cost of a Data Breach Report 2024, employee security awareness training ranked as the number one factor in decreasing the average cost of a breach, specifically for detecting and stopping phishing attacks. The return on training investment is highest at the executive level, where successful whaling phishing attacks carry the largest financial consequence. Organizations building executive awareness programs can consult security awareness training (SAT) reference material to align program design with current standards.
Run executive-grade whaling phishing simulations that reflect how real attacks are built.
7. Run Whaling Phishing Simulations for the C-Suite
Phishing simulations are the operational counterpart to awareness training. Generic simulations targeting general staff fail to test executive risk because the attack scenarios are insufficiently sophisticated. Effective C-suite whaling phishing simulations replicate genuine attack tactics:
- Fabricated merger and acquisition communications;
- Impersonated board correspondence;
- Fraudulent vendor payment change requests;
- AI-generated CEO fraud phishing attempts that closely mimic executive writing styles.
Simulation results should drive iterative refinement of training content, with particular attention to scenarios where executives engaged with rather than reported the message. Organizations building executive simulation programs can consult phishing tests and simulations reference material when designing cadence, scenario complexity, and reporting structure.
Run sophisticated C-suite simulations to reflect how whaling phishing attacks take advantage of human vulnerabilities.
8. Apply Privileged Access Controls
Privileged access controls limit what any single account can authorize unilaterally, including executive accounts. Key controls relevant to whaling phishing defense include:
- Least-privilege principles that restrict access to the minimum systems and data required for a role;
- Payment system segmentation to prevent a compromised account in one system from authorizing actions in another;
- Secondary authentication for high-impact actions such as wire transfers above defined thresholds or sensitive data exports.
The defensive value is proportionally high: privileged access controls cost relatively little to implement and dramatically reduce the blast radius of even a fully successful whaling phishing attack.
9. Maintain a Whaling Phishing-Specific Incident Response Plan
A whaling phishing-specific incident response plan accelerates recovery during the critical first hours after an attack is discovered. The plan should include:
- Pre-established contacts at the organization's banks for wire recall procedures;
- Retained legal counsel familiar with relevant disclosure obligations;
- Forensic partners available under standby agreements;
- A defined escalation path to the board and audit committee.
The plan must also cover regulatory reporting obligations across relevant jurisdictions, with templates and timelines prepared in advance for SEC, GDPR, state-level, and industry-specific notifications. Annual exercises that walk the response team through realistic whaling phishing scenarios surface gaps before a live incident does. Integrating these exercises into the broader cybersecurity awareness training program ensures that both people and playbooks are tested on a continuous cadence.
How to Stay Safe from Whaling Phishing Attacks as a C-Level Executive
For C-level executives, the technical controls described in the previous section are necessary but insufficient on their own. Personal-level behaviors matter as much as corporate infrastructure in whaling phishing defense. The largest enterprises in the world have lost tens of millions of dollars to CEO fraud phishing despite robust technical controls, because cyberattackers ultimately target executive judgment rather than organizational infrastructure. The four practices below define what sustained executive vigilance looks like in practice.
Find out how Adaptive Security's executive-targeted simulations close the gap before a real whaling phishing attack does.
Limit Public OSINT Exposure in Whaling Phishing Scenarios
Every publicly available detail about an executive becomes potential fuel for a whaling phishing attack:
- Review LinkedIn and remove or redact role-change details, org charts, and direct-report listings that reveal internal hierarchies.
- Monitor press releases and redact or delay publication of sensitive strategic initiatives that could be quoted in fraudulent messages.
- Lock down personal social accounts and remove or postpone posts that reveal travel dates, family members, or lifestyle details that enable believable impersonation.
- Audit company bio pages and strip unnecessary operational or project specifics.
- Limit LinkedIn connection visibility and adjust privacy settings to reduce profile exposure.
- Treat any planned travel or internal project information as confidential: avoid posting it publicly or share only with vetted recipients.
Executives should audit and restrict what is publicly visible: limiting LinkedIn connection visibility, reviewing company bio pages, and applying caution to any personal content that reveals travel plans or internal project details. The principle is straightforward: anything an executive does not want a cyberattacker to know should not be publicly accessible. The comprehensive guide to identifying a whaling phishing email provides further reference on how cyberattackers convert OSINT into convincing attack content.
Establish a Personal Verification Protocol Against CEO Fraud Phishing
A personal verification protocol is the single most effective defense an executive can deploy against CEO fraud phishing. Executives should agree with their direct reports, finance leaders, and assistants on a verification phrase, a secondary channel, or a codeword that must be used for any financial or sensitive-data request appearing to originate from the executive. The protocol should cover:
- Wire transfers;
- Banking detail changes;
- Gift card purchases;
- Employee data releases;
- Any other action a fraudulent message might attempt to trigger.
The protocol must be documented in writing, distributed to everyone who might receive a request claiming to come from the executive, and reinforced during onboarding for new finance and HR staff. Critically, executives must communicate that bypassing the protocol is unacceptable even under apparent urgency pressure. The protocol only works if subordinates trust that following it will be supported when an executive is genuinely unreachable and a deadline is tight.
Let Adaptive Security help your organization build verification habits through role-specific awareness training.
Treat Urgency as a Red Flag in Whaling Phishing Attempts
Manufactured urgency is the most common feature of CEO fraud phishing. Executives should treat any communication demanding immediate action, confidentiality, or bypass of normal controls as suspect by default, even when the apparent sender is a known colleague, vendor, or board member. Legitimate executive requests rarely require the recipient to skip verification or compress decision-making timelines; cyberattackers, however, depend on exactly that.
The key shift is in default posture. Instead of treating urgency as a reason to act faster, executives should treat it as a reason to slow down and verify. The few minutes spent on out-of-band confirmation are negligible compared to the recovery effort required after a successful whaling phishing attack. As whaling phishing increasingly leverages AI-generated content and deepfake voice or video reinforcement, this posture becomes even more critical. Executives can review how to detect and stop AI executive impersonation attacks for additional context on the AI-driven threat landscape.
Report Suspicious Whaling Phishing Emails Immediately
A suspicious email reported quickly becomes intelligence that protects the entire organization. Even when an executive is uncertain whether a message is fraudulent, the security team should always be the first point of contact. Forwarding the message through a standardized reporting process allows analysts to:
- Investigate the indicators;
- Share findings across the organization;
- Warn other potential targets before the same campaign reaches them.
Delayed reporting is the most common reason whaling phishing attacks spread laterally within an organization. Cyberattackers running coordinated campaigns often target multiple executives or finance staff in parallel; the first report enables defense for everyone still within the attack window. Executives should treat uncertainty as a reason to report promptly, and should not hesitate to flag messages that turn out to be legitimate.
Turn every reported message into an actionable signal with Adaptive Security's phish triage capabilities.
What to Do After Falling Victim to a Whaling Phishing Attack
The first 24 to 72 hours after a whaling phishing attack are critical for both financial recovery and evidence preservation. Wire transfers can often be reversed within this window, evidence remains intact before automated cleanup processes overwrite it, and law enforcement coordination is most effective when initiated quickly. The five steps below should be executed in parallel where possible.

Notify the Security Team and Legal Counsel Immediately After a CEO Fraud Phishing Attack
The first internal action should be to contact security leadership and legal counsel simultaneously. The security team coordinates the technical response, including credential resets, account isolation, and forensic preservation. Legal counsel preserves attorney-client privilege on sensitive communications, manages regulatory notification obligations across overlapping jurisdictions, and advises on disclosure timing for public companies. Executives should resist the impulse to handle the incident quietly until more information is available; that delay almost always reduces both recovery probability and legal protection.
Contact the Bank to Halt or Reverse Whaling Phishing Transfers
Contacting the bank is the most time-critical action after a fraudulent wire transfer. Most wire transfers can only be recalled within 24 to 72 hours, and international transfers may be unrecoverable once funds move through correspondent banks. Organizations should:
- Request a SWIFT recall;
- File a formal fraud report with the bank;
- Ask the bank to coordinate with the receiving institution.
According to Proofpoint's Email Attacks Drive Record Cybercrime Losses in 2024, the FBI's IC3 Recovery Asset Team reported a 66% success rate in freezing fraudulent BEC transfers, underscoring the critical importance of reporting incidents immediately. Every hour of delay materially reduces the probability of fund recovery.
Preserve All Evidence from the Whaling Phishing Incident
Evidence preservation begins as soon as the attack is identified. The following must be retained in their original form:
- The phishing email with full headers intact;
- Any attachments;
- Log files from affected systems;
- Complete records of the fraudulent transactions.
Suspicious messages must not be deleted or forwarded in ways that strip headers, and automated retention policies must not be allowed to age out relevant data. This evidence supports both the internal forensic investigation and any potential criminal prosecution or civil recovery action. Organizations that attempt to clean up before preserving evidence frequently lose the ability to pursue cyberattackers or recover funds through insurance claims.
Report the Incident to the FBI's IC3 or Relevant Authority
In the United States, organizations should file a complaint with the FBI's Internet Crime Complaint Center (IC3). The IC3 Recovery Asset Team can coordinate with banks to freeze fraudulent transfers, and the complaint contributes to law enforcement intelligence on active cybercriminal groups. Outside the United States:
- European Union: notify the relevant national cybercrime authority and the data protection authority if personal data was exposed;
- United Kingdom: report to Action Fraud and the National Cyber Security Centre;
- Australia: report to the Australian Federal Police and ReportCyber.
Reporting is not optional from a regulatory standpoint in many jurisdictions, and the operational benefit is substantial. Law enforcement coordination has produced fund recovery in numerous documented CEO fraud phishing cases, and emergency wire transfer reversal procedures depend on official complaint filings.
Conduct a Forensic Review After a Whaling Phishing Attack
A successful whaling phishing attack rarely affects only the immediately visible transaction. Internal or external forensic specialists should be engaged to determine:
- Whether executive credentials were exposed;
- Whether lateral movement occurred to other systems or accounts;
- Whether data was exfiltrated alongside the financial fraud;
- Whether persistent access mechanisms were established for future attacks.
The findings should drive concrete updates to controls, training programs, and the incident response plan. Organizations that treat the post-incident review as a one-time exercise miss the opportunity to convert a costly incident into durable defensive improvement.
How to Report CEO Fraud and Whaling Phishing Incidents
Prompt and complete reporting is the single largest factor determining fund recovery probability after a whaling phishing attack. The reporting chain involves multiple authorities operating under different mandates, and effective response requires notifying all relevant parties in parallel. The structure below covers internal escalation, U.S. federal authorities, and international reporting channels.
Internal escalation comes first. The security team, CISO, and legal counsel should be notified immediately, followed by the audit committee or board if the incident meets materiality thresholds. Internal escalation runs in parallel with external reporting; waiting to complete an internal investigation before notifying external authorities is among the most common errors that reduces recovery probability.
FBI's Internet Crime Complaint Center (IC3) is the primary reporting channel for U.S. organizations. File the complaint at ic3.gov as soon as the attack is identified, with full details on the fraudulent transaction, the impersonated party, and the suspected destination accounts.
FinCEN receives suspicious activity reports when financial institutions are involved in the fraudulent transaction chain. While SAR filing is typically the responsibility of the financial institution, victim organizations should confirm their banks have filed and reference the SAR in subsequent regulatory communications.
CISA is the appropriate channel for critical infrastructure organizations, particularly when the whaling phishing attack involves operational technology, sector-specific systems, or compromise of personnel with access to designated critical infrastructure.
State attorneys general must be notified under state breach notification laws when the whaling phishing incident exposes personally identifiable information of state residents. Multi-state organizations face overlapping notification obligations with varying timelines; these notifications should be coordinated through legal counsel to ensure consistency.
International reporting channels apply to organizations operating outside the United States:
- United Kingdom: file with Action Fraud and notify the National Cyber Security Centre;
- European Union: notify Europol's European Cybercrime Centre (EC3) for cross-border coordination, along with the relevant national CERT and supervisory authority under GDPR;
- Australia: report to the Australian Federal Police and ReportCyber.
Start monitoring executive risk before the next whaling phishing campaign finds your organization first, with Adaptive Security.
Future Trends in Whaling Phishing
The whaling phishing landscape is evolving faster in 2025 and 2026 than at any prior point, driven primarily by generative AI capabilities reaching cyberattacker workflows at scale. According to Vectra AI's AI Scams, AI-enabled fraud surged 1,210% in 2025, with projected losses reaching $40 billion by 2027 as AI tools continue to democratize social engineering. The four developments below define the near-term threat trajectory and require adaptive, AI-driven defenses.
AI-Powered Deepfakes Enable Advanced Whaling Phishing
Real-time deepfake audio and video has crossed the threshold from emerging risk to active attack vector. The Arup engineering firm incident in Hong Kong, in which an employee wired $25 million after participating in a deepfake video conference call featuring a fabricated CFO and multiple synthetic colleagues, is the leading documented example. The attack succeeded despite the employee's initial suspicion, because the realism of the multi-participant deepfake overcame the verification instinct.
According to GetApp's 2024 Executive Cybersecurity Survey, AI-generated deepfakes were involved in 27% of cyberattacks targeting senior executives in the past 18 months. The trajectory indicates that deepfake-enabled whaling phishing will become standard rather than exceptional within two to three years. Organizations should add liveness checks, multi-channel verification, and synthetic media detection to their executive defense stack.
Hyper-Personalized LLM-Generated CEO Fraud Phishing Emails
Generative AI now produces CEO fraud phishing emails that match an executive's writing style, tone, and vocabulary with remarkable precision. Cyberattackers train large language models on publicly available executive correspondence, including earnings call transcripts, published articles, and leaked email archives, then generate fraudulent messages nearly indistinguishable from genuine executive output.
The implication is that content review alone is no longer a reliable detection method. The stylistic anomalies that previously flagged whaling phishing emails as suspicious are systematically eliminated by modern large language models. Technical authentication, out-of-band verification protocols, and behavioral analytics become disproportionately more important as content-based detection becomes less reliable.
Multi-Channel Whaling Phishing Campaigns
Cyberattackers increasingly combine email, SMS, voice, and messaging applications into coordinated campaigns rather than relying on a single channel. A fraudulent email may be preceded by a phone call from a synthetic CFO confirming the upcoming request, or followed by a text from a fabricated assistant reinforcing the urgency. Single-channel defenses miss these multi-vector attacks because each individual touchpoint appears legitimate when evaluated in isolation.
The defensive response requires extending verification protocols across all channels simultaneously and treating cross-channel reinforcement as a red flag. When an email is followed by a phone call from a different number that "confirms" the email, the coordination itself is a strong indicator of CEO fraud phishing.
Expanding Target Profiles Beyond Traditional Executives
The definition of a high-value target is expanding well beyond the traditional CEO and CFO. The following roles now represent significant attack surfaces:
- Chief AI Officers, who hold authority over significant AI infrastructure budgets and proprietary model assets;
- Chief Privacy Officers, who control access to regulated personal data at scale;
- Chief Data Officers, who oversee the data architectures containing the organization's most valuable analytical assets;
- Procurement leaders, treasury managers, and senior wealth advisors, all of whom sit within reach of meaningful financial authority.
Security programs designed around CEO and CFO protection alone leave these emerging high-value roles undefended. Comprehensive whaling phishing programs in 2026 and beyond should treat the full executive bench, board, and senior functional leadership as in-scope for the same protections previously reserved for the C-suite top tier.
See how Adaptive Security extends executive-grade whaling phishing defenses to every high-value role in your organization.
How Adaptive Security Prevents Whaling Phishing
Adaptive Security helps organizations build sustained defenses against whaling phishing by combining executive-targeted simulation, role-specific awareness training, and rapid threat triage in a single platform. Technical email controls block the easiest attacks, but the harder ones reach human inboxes, and the human layer is where most whaling phishing losses originate. Adaptive Security is designed to address exactly that gap.
The platform delivers phishing simulations tailored to C-suite scenarios, including:
- AI-generated executive impersonation;
- Fraudulent vendor banking changes;
- Multi-channel campaigns that combine email with voice and SMS.
Simulation results inform iterative training that addresses the specific tactics each executive's team has been most vulnerable to, rather than defaulting to generic content. Role-specific cybersecurity awareness training extends the same principle to board members, finance staff, HR teams, and emerging high-value roles such as Chief AI Officers and Chief Privacy Officers.
Phishing triage and reporting capabilities allow employees to flag suspicious messages directly from their inboxes, with security teams receiving structured intelligence that supports rapid investigation and lateral threat containment. Reporting dashboards provide visibility into campaign trends, employee risk scores, and remediation progress, giving security leaders the data needed to demonstrate measurable program improvement over time.
Stop waiting for a whaling phishing incident to expose gaps; build defenses across every leadership tier with Adaptive Security today.
Frequently Asked Questions About Whaling Phishing
What Is an Example of a Whaling Phishing Attack?
A whaling phishing attack typically involves a high-pressure email sent to a Chief Financial Officer (CFO), designed to appear as though it originates from the CEO. The message requests an urgent wire transfer to close a confidential acquisition. These emails commonly use spoofed addresses and incorporate specific corporate terminology to establish credibility and circumvent standard security protocols.
What Is the Difference Between Whaling Phishing and Spear Phishing?
The primary distinction between whaling phishing and spear phishing lies in the seniority of the intended target. Spear phishing targets any specific individual or group within an organization through the use of personalized information. Whaling is a specialized form of spear phishing that exclusively focuses on high-value targets, such as C-suite executives including Chief Executive Officers, Chief Financial Officers, and Chief Operating Officers, as well as board-level leadership.
What Are the Four Types of Phishing?
The four most widely recognized types of phishing are as follows:
- Bulk Phishing: Mass emails distributed to thousands of random recipients with the expectation that a small percentage will respond.
- Spear Phishing: Targeted cyberattacks directed at a specific individual or organization using personalized information to increase the likelihood of deception.
- Whaling phishing: A sophisticated form of spear phishing that targets senior executives and high-level decision-makers within an organization.
- Vishing and Smishing: Phishing conducted through voice calls (vishing) or SMS text messages (smishing), rather than email.
What Type of Phishing Targets CEOs?
Whaling is the specific category of phishing attack designed to target Chief Executive Officers and other senior executives. These attacks are highly sophisticated and extensively researched, engineered to exploit the elevated access and organizational authority that executives hold. Because of the high-value nature of these targets, whaling phishing campaigns are among the most carefully constructed social engineering threats in the cybersecurity landscape.
What Are the Signs of CEO Fraud?
Common indicators of CEO fraud include the following warning signs:
- Extreme Urgency: Requests that pressure recipients to bypass established approval procedures immediately.
- Secrecy: Instructions to keep the communication confidential or to conduct the transaction outside of standard channels.
- Irregular Timing: Emails sent during off-hours, on public holidays, or while the executive is known to be traveling or otherwise unavailable.
- Spoofed Addresses: Email addresses that closely resemble the CEO's legitimate address but contain minor misspellings, additional characters, or alternative domains.
How Do Cyberattackers Use Phishing Messages in BEC and CEO Fraud Attacks?
In Business Email Compromise (BEC) attacks, cyberattackers use phishing messages to harvest login credentials or impersonate executives within an organization. Once access is established or trust is built, fraudulent communications are sent to employees in finance or human resources, directing them to authorize wire transfers, modify payroll direct deposit information, or share sensitive employee documentation.
What Type of Phishing Attack Is CEO Fraud?
CEO fraud is a form of whaling phishing, also referred to as executive impersonation. It operates as a sub-type of Business Email Compromise (BEC), in which the threat actor assumes the identity of a high-ranking executive to deceive subordinates into executing fraudulent actions, such as transferring funds or disclosing confidential information.
How Can Organizations Reduce the Risk of a CEO Fraud Attack?
Organizations can significantly reduce exposure to CEO fraud by implementing the following controls:
- Implement Multi-Factor Authentication: Require MFA across all corporate accounts to reduce the risk of unauthorized access resulting from compromised credentials.
- Establish Out-of-Band Verification: Require a secondary confirmation, such as a phone call or in-person verification, before processing any significant financial transaction.
- Deploy Email Security Protocols: Implement DMARC, SPF, and DKIM to prevent domain spoofing and reduce the likelihood that fraudulent emails reach employee inboxes.
- Conduct Regular Security Awareness Training: Run ongoing CEO fraud and whaling phishing simulations and training programs to ensure employees can identify and appropriately respond to executive impersonation attempts.
Key Takeaways on Whaling Phishing and Next Steps
Whaling phishing has matured into the most financially devastating category of social engineering targeting enterprises, and the trajectory points toward greater sophistication rather than diminishing risk. The takeaways below distill the core defensive principles covered across this guide.
- The scale of the threat is enterprise-wide and accelerating. With BEC losses exceeding $3 billion in 2024 and AI-enabled fraud projected to reach $40 billion by 2027, whaling phishing is no longer an edge-case risk reserved for the largest organizations.
- Modern whaling attacks defeat content-based detection. AI-generated emails, deepfake voice and video, and compromised insider accounts have eliminated most of the stylistic anomalies that once flagged fraudulent messages. Defense must shift toward technical authentication, out-of-band verification, and Zero Trust access controls.
- Executive-specific training and verification protocols are non-negotiable. Standard cybersecurity awareness training programs do not address C-suite risk, and personal verification protocols between executives and their direct reports prevent the majority of attempted CEO fraud phishing attacks regardless of how convincing the impersonation is.
- AI is reshaping both sides of the equation. The same generative capabilities that enable hyper-personalized CEO phishing emails also enable adaptive defensive simulations and behavioral analytics. Organizations that match attacker AI with defensive AI retain security; the ones that rely on static controls fall behind.
Explore Adaptive Security's phishing simulations to benchmark your organization's whaling phishing defense maturity.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents