This guide is designed to assist security teams in developing a comprehensive security awareness training program for a company.
The goal is to explain the purpose and significance of such programs, offer advanced insights from industry experts, and provide a practical implementation plan.
To explore the next-generation of security awareness training, consider viewing an Adaptive Security Demo.
A security awareness training program is a systematically designed initiative that delivers critical cybersecurity information to employees, ensuring they are well-equipped to recognize and respond to potential threats in their daily work.
Employees must understand cyber threats and the tactics cybercriminals use, as a lack of awareness can leave them unprepared, given the high level of sophistication these attacks employ. For instance, in 2025, a British retailer fell victim to a social-engineering attack via a third party, resulting in ransomware being installed on its systems.
According to Fortinet's 2025 Security Awareness and Training Report, 67% of organizations have observed moderate to significant reductions in intrusions, incidents, and breaches following the implementation of security awareness and training programs.
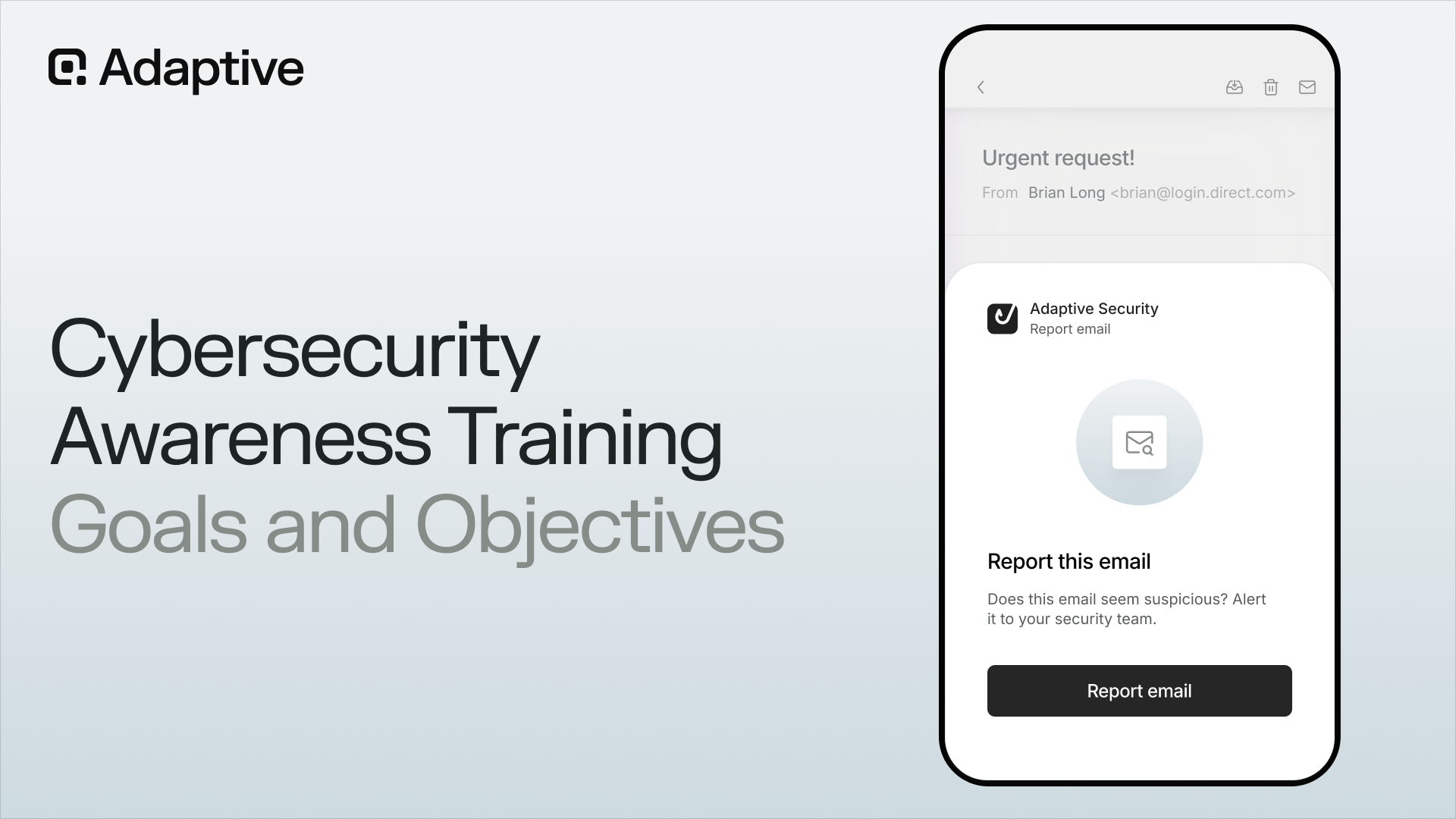
Following awareness training, employees must also understand how to safeguard themselves against cyberattacks. This includes recognizing phishing emails and deepfakes to prevent falling victim to them.
Lastly, employees also need to know what to do if they are ever put in that position. For instance, reporting a cyberattack they identified, or an incident or scam they might have been a victim of, too.
When building a security awareness training program, the three key goals are awareness, protection, and reporting.

Key takeaway: Cybersecurity is not just a technology problem: it is a human problem.
What Does A Security Awareness Training Program Teach?
A well-designed cybersecurity awareness training program educates employees about the most prevalent attack vectors used by cybercriminals.
The phrase "currently employed" is critical, as cyber threats are evolving rapidly. A pertinent example is deepfakes. According to UNESCO, 66% of fraud specialists have encountered voice and video deepfakes. One key lesson from our training emphasizes the severe impact of a deepfake scam targeting a company's CEO.
Another significant example is phishing. The 2026 Global Security Outlook, published by the World Economic Forum in collaboration with Accenture, indicates that 77% of respondents believe the threat of cyber-enabled fraud and phishing has increased.
Phishing, one of the most traditional forms of cyberattack, has evolved from misspelled emails with dubious logos and nonsensical domains.
Every second, cybercriminals are developing methods to make phishing more indistinguishable from legitimate workflows. Additionally, many emails are now sent from third-party services using domains that may seem unrelated to the company but are, in fact, authentic.
Key takeaway: The goal of a cybersecurity awareness training program is not just to teach about each threat, but to help build strong decision-making instincts.
Is Having A Security Awareness Training Program Enough?
A security awareness training plan is a vital component of a comprehensive cybersecurity strategy, though it cannot stand alone.
The same principle is applicable to all defensive elements. Human error is unavoidable, just as technical failures are possible. Implementing multiple safeguards significantly strengthens an organization's digital security.
Employees have been conditioned to open and click on emails since the advent of email technology. Sometimes, muscle memory takes over, leading them to click on the wrong link before they even realize it. Factors such as time pressure, stress, and context significantly influence these actions.
Deepfakes are increasingly difficult to distinguish from legitimate ones. AI-driven cyberattacks generate a continual flow of sophisticated threats. Multi-channel scams further complicate security efforts.
As the U.S. Cybersecurity and Infrastructure Security Agency (CISA) stresses, "Security awareness alone cannot prevent all attacks. Organizations must implement layered defenses and robust processes to mitigate risk."
The Importance Of A Security Awareness Training Plan
Security awareness training plans are essential because every organization has an attack surface: potential entry points that cybercriminals can exploit to breach defenses. For example, a Singaporean executive transferred nearly US$500,000 after what appeared to be a routine call, which was actually composed entirely of deepfakes.
According to the Global Cybersecurity Outlook 2026, 73% of respondents stated that someone in their professional or personal network had been a victim of cyber-enabled fraud, with phishing, vishing, or smishing involved in 62% of attacks.
Cybercriminals aim to cause maximum damage with minimal effort. They target the most vulnerable entry-points, and humans are among the most significant. Especially when lacking proper training.
A single employee can be the key to a cyberattack's success or failure. Conversely, one well-trained employee can prevent it. As researchers Shanée Dawkins and Jody Jacobs from the National Institute of Standards and Technology (NIST) explain, effective phishing awareness programs should consider real-world user contexts and help organizations understand why people click, so that training can enhance recognition and reporting rather than merely measure failures.
This concept is known as the "human firewall," where potential vulnerabilities are transformed into the first line of defense. The difference before and after cyber awareness training is quite evident.
Building cybersecurity awareness and training is essential for significantly reducing cybersecurity risks. Protecting valuable assets affected by cyberattacks is crucial:
- Revenue. Cybersecurity Ventures projects that ransomware damages will reach $74 billion by 2026.
- Reputation. Cybercrime is a prominent concern, with reputational damage often costing more than financial losses.
- Intellectual Property. Many cyberattacks are driven by espionage and theft of intellectual property.
Advanced Benefits Of A Security Awareness Training Program
A well-structured security awareness training program clearly outlines immediate benefits such as protecting company revenue, intellectual property, and reputation. Additionally, it offers numerous long-term advantages that may not be immediately apparent.
Security Awareness Training Program Benefit #1: Helps With Compliance And Regulations
Many regulations mandate or promote security awareness training. This ensures compliance, helps avoid penalties, and enhances public perception by adhering to key regulations.
- General Data Protection Regulation (GDPR).
- Health Insurance Portability and Accountability Act (HIPAA).
- International Organization for Standardization (ISO) 27001.

Security Awareness Training Program Benefit #2: Contributes To The Overall Organization Culture
Over time, through consistent cyber awareness training, knowledge translates into behavior, which ultimately becomes part of the organizational culture. This fosters a shared sense of responsibility for cybersecurity and encourages ongoing discussions on the topic.
Cybersecurity also presents an excellent opportunity to unify teams. As a company-wide responsibility, it allows different groups that may have limited interaction to collaborate effectively.
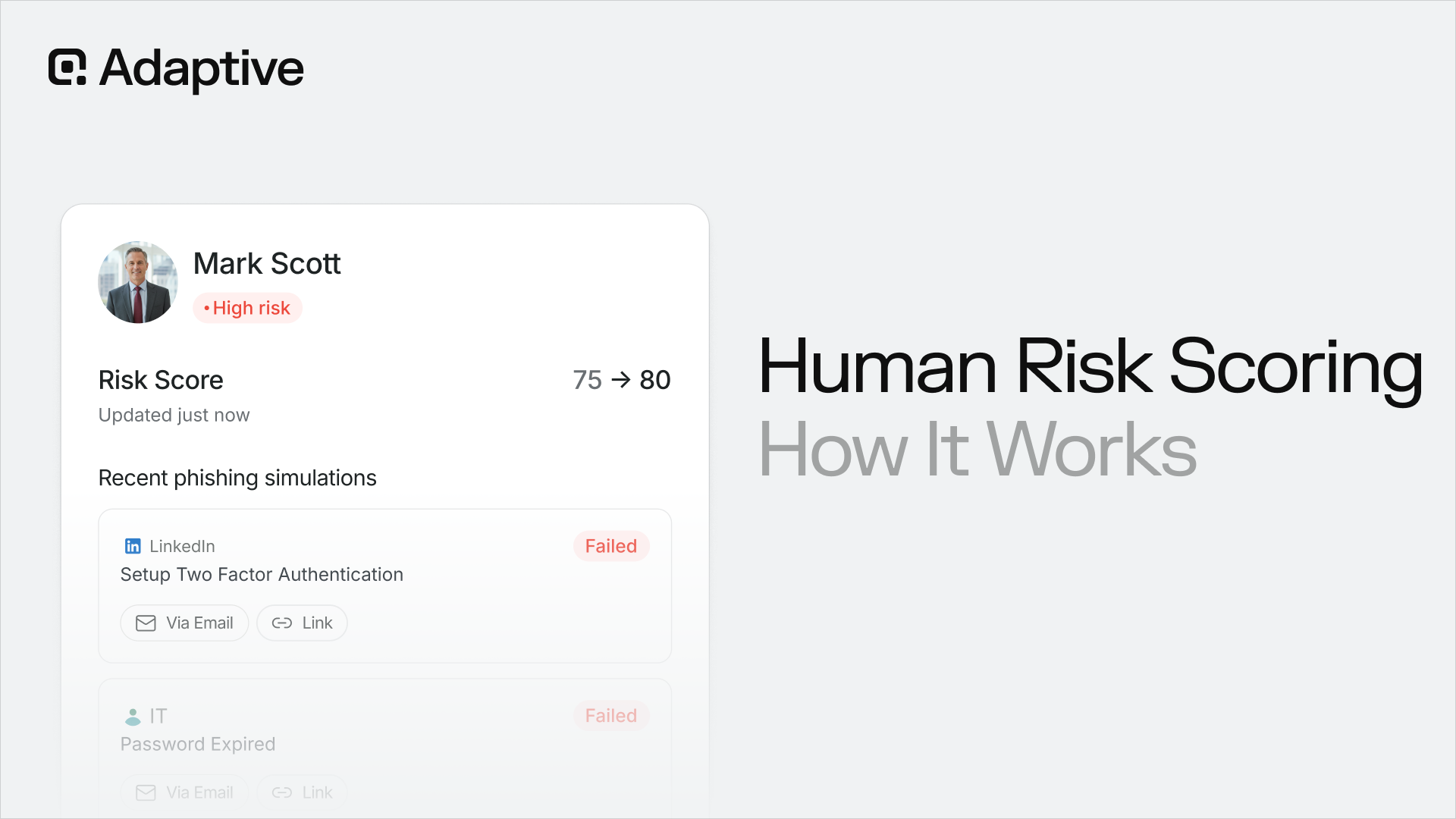
Security Awareness Training Program Benefit #3: Creates A Company-Wide Human Risk Profile
Developing a security awareness training program involves conducting tests, simulations, and quizzes. These tools not only enhance learning but also generate measurable data that accurately assesses a company's risk profile.
This information is valuable and has multiple applications. Security teams can regularly review these metrics to monitor overall improvement or to evaluate progress for individual employees. If there is no progress, make adjustments.
Additionally, these metrics serve as an effective means to demonstrate to leadership that training is producing results.
Security Awareness Training Program Benefit #4: Improves Overall Digital Skills
A well-designed cybersecurity awareness training plan not only improves specific knowledge but also leads to growth in overall digital skills.
Research by Professor Steven Furnell, a cybersecurity expert at the University of Nottingham, suggests that awareness training can offer benefits beyond security alone by improving people's understanding of technology, their ability to assess digital situations, and their confidence in responding online.
Also, it improves decision-making, pattern recognition, and other overall skills.
Security Awareness Training Program Benefit #4: Protects The Company From Internal Threats
Throughout this article, we focused heavily on external threats, such as cybercriminals, but internal cyber threats are also very real. Whether by mistake, negligence, or sometimes even malintent. For instance, in 2023, two former Tesla employees leaked company data to a media outlet.
A Cybersecurity Insiders 2026 study shows that only 10% of organizations reported zero insider incidents. In 2025, that number was 17%. This threat is only growing more real, driven by political, financial, and other motivations.
Cyber awareness and training directly help minimize mistakes and negligence by making employees more aware of their digital environment.
Dr. Deanna Caputo, Chief Scientist for Insider Threat Capabilities at MITRE, has emphasized the need for behavior-based, evidence-driven approaches to insider risk. That perspective reinforces the value of awareness training: it is not just about reducing accidental mistakes, but also about helping employees recognize warning signs, take concerns seriously, and report them through the proper channels.
How To Build An Effective Security Awareness Training Program Step-By-Step?
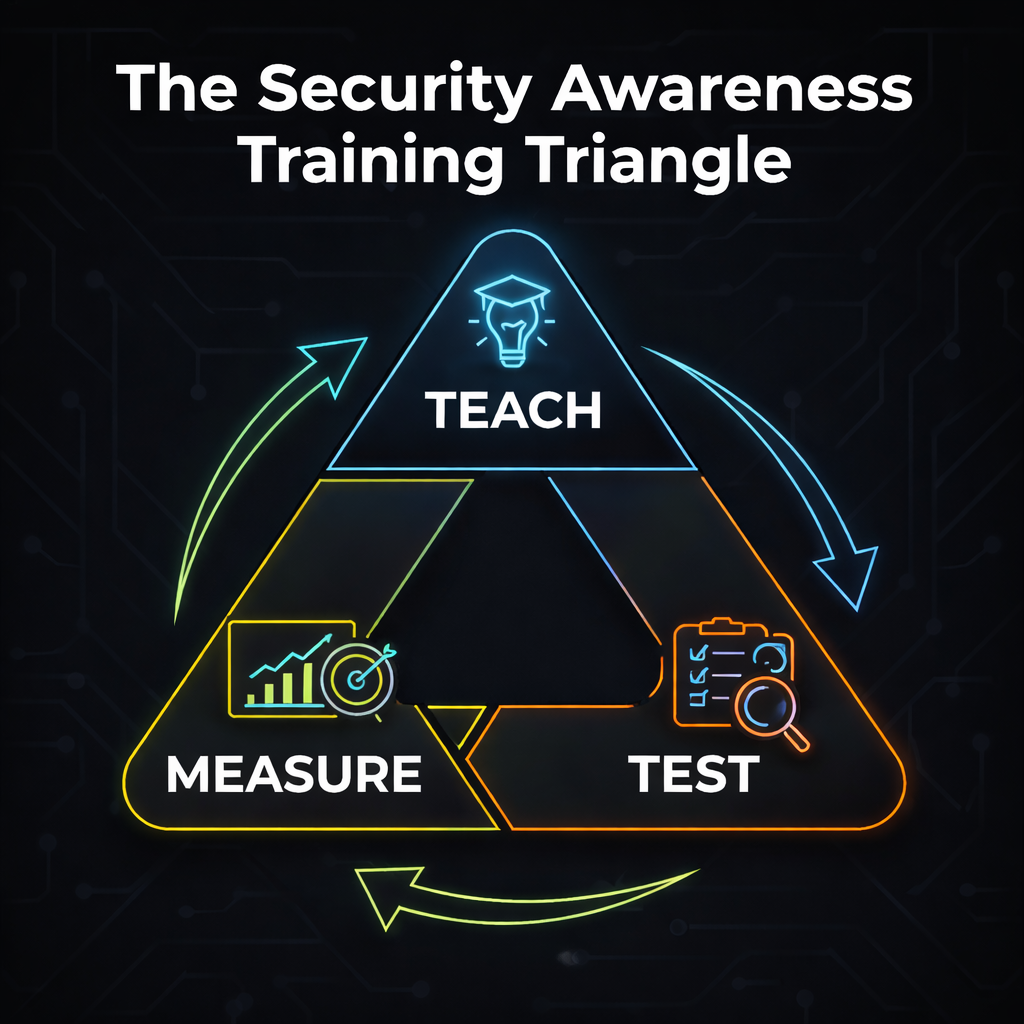
To build the best cybersecurity awareness training program, assess the company's maturity level, identify employees who may need advanced training, and plan how to deliver information in an engaging, personalized way.
It is also important to plan for the long term, measure results, and continuously improve the cyber awareness program based on results and emerging threats.
As Jen Easterly, Director of the Cybersecurity and Infrastructure Security Agency (and former CISO at Morgan Stanley), has emphasized, cybersecurity must be treated as a continuous process of improvement rather than a one-time effort. The same principle applies to awareness training, which is most effective when it evolves alongside new threats and employee behavior.
An interesting approach is to adapt a well-established sprint development cycle to the security awareness training management. It is a simple and quick framework that works well:
- Plan the security awareness training.
- Execute the lessons and put cyber awareness training into practice.
- Monitor results, especially behavior improvement.
- Review to begin planning for the next cycle.
Step 1: Adapt The Security Awareness Training Program To The Company's Current Maturity Level
The first step in building a successful security awareness training program is to determine where the company stands. Here, it is important to measure both quantitative data as well as qualitative data.
For quantitative data, answer questions like:
- Is security awareness training currently being provided? If yes, how often?
- How often do employees fall for phishing attacks?
- Are phishing attacks reported?
- Are there any cybersecurity policies in place?
- Does the team use security awareness training tools?
Qualitative is a bit more complicated, but just as important. The entire purpose of cyber awareness training is to protect people, so a part of the job is to understand them. Security teams should talk with employees to gauge their level of cybersecurity awareness.
Step 2: Create Role-Based Security Awareness Training
Now, shift the focus to the employees. The main idea is not to train everyone equally, but to train everyone appropriately.
There is no need to allocate the same level of effort to the intern as to the CEO, particularly when employing principles such as least privilege or minimum privilege. Below are some examples of scams that employees might encounter:
- Finance team: Transfer fraud, fake invoices, business email compromise. Cybercriminals find ways to impersonate vendors, partners, and executives to demand urgent payments.
- HR team: Fake résumés, sensitive data requests. Due to frequent contact with external sources, HR teams are fertile ground for malware disguised as files, such as résumés. Cybercriminals might also impersonate other people to request sensitive data.
- Executives: Spear phishing, whaling. Targeted with incredibly personalized attacks, pretty much from all sides, due to the authority, visibility, and access they carry.
- IT/Help desk: account and password reset. Help desk or IT departments can reset passwords and MFA. Cybercriminals use social engineering to obtain that information.
- General employees: All employees can be targeted by phishing, credential theft, AI-based attacks, and deepfakes. Create a more general end-user security awareness program.

Step 3: Incorporate Governance, Policy, And Compliance In Security Awareness Training Program
These are key components of security awareness training that guide a training curriculum. Cover cybersecurity and privacy compliance requirements, such as HIPAA, in healthcare security awareness training.
Also, create a security awareness training policy, including topics like:
- Objective: Create a clear, measurable training goal.
- Scope and frequency: Explain what needs to be covered and with what frequency.
- Monitoring and reporting: Disclose what the training scope will measure and how it will be measured.
It is important to leave room to update the policy, as the training scope might change throughout the planning phase.
Also, executive and leadership buy-in is a must. Not only for budgetary reasons, but also to ensure they will participate.
As MongoDB CISO Lena Smart has noted, leadership support can significantly impact the success of security culture programs, especially when senior leaders actively promote them and participate visibly. That kind of endorsement helps signal that security awareness is not just an IT initiative, but an organizational priority.
Lastly, clarify who is responsible for the security awareness training program. Who will lead, who will support, and which executive is sponsoring the initiative?
Below is a simple example of a team structure that works very well:
- Executive sponsor: CISO.
- Security awareness training program managers: 2 members of the security or IT team.
- Technical Support: Other members of the security or IT teams.
- HR support: One member of the HR team.
- Legal support: One member of the Legal team.
Step 4: Cover The Main Security Awareness Training Topics
Security awareness training topics should cover as much ground as possible, addressing all threats commonly used against employees.
It is not about inundating them with technical details. The goal is to inform employees of the risks, enable them to recognize those risks, understand the appropriate actions if they encounter such situations, and know how to report them.
Delve deeper into the key topics that are essential and, most importantly, what employees need to learn from training.
There are many topics to cover, so bringing external cybersecurity awareness training services might make the process easier.
Security Awareness Training Topic #1: Phishing, Social Engineering, Business Email Compromise, And Its Variations
The backbone of security awareness training programs, and one of the most common tools cybercriminals use.
CEOs now rank cyber-enabled fraud and phishing as the biggest cyber risk concern for their organizations in 2026, according to the Global Security Outlook 2026.
Carl Windsor, Global CISO at Fortinet, noted in his analysis of the World Economic Forum Global Cybersecurity Outlook 2026 that even as awareness of cyber risk rises, governance, visibility, and control continue to fall behind. In that environment, security awareness training becomes an important way to strengthen the human layer of defense.
Phishing training has evolved significantly over the years, as it used to be much simpler to identify phishing attacks by a quick glance at the message content, the domain, or the logo. Now, messages are increasingly sophisticated and come across multiple channels, including voice, SMS, and deepfake phishing. For instance, an SMS phishing scam cost a company's customer base over US$ 10 million.
Employees should learn:
- How to identify these cyber threats.
- Recognize human behavior triggers that cybercriminals seek to exploit (fear, authority, urgency).
- Understand all channels through which messages can arrive.
- Create a habit of questioning and seeking other ways to verify information.
Business Email Compromise is a variation of traditional phishing that uses a fake email to induce users to take action. The BEC is a more targeted attack, aimed at organizations, in which cybercriminals act as vendors, executives, or other context-heavy entities. For instance, a Utah-based company sent over US$ 1 million to a vendor impersonation.
Download our comprehensive phishing guide to access 10 expert tips for defending your team against AI-driven phishing threats.
Security Awareness Program Topics #2: Password Security And Hygiene
Teach employees good password habits, which are crucial for protecting identities and preventing cybercriminals from gaining unauthorized access at their expense. This means:
- Creating strong, unique passwords.
- Implementing multifactor authentication.
- Using and understanding password managers.
- Not sharing passwords and authentication codes without double-checking (even when it seems like they should)
An important note to keep in mind in 2026: do not use AI chatbots to generate passwords. A study published by Malwarebytes Lab shows that an AI bot repeated the same password 10 times when prompted to generate a random password. These systems are not designed to be truly random, making AI-generated passwords highly predictable and trivial for hackers to crack.
Key takeaway: Modern attacks mostly target accounts, rather than devices themselves.
Security Awareness Program Topics #3: Malware And Ransomware Awareness
Daniel Kwong, Field CISO at Fortinet, has noted that ransomware remains one of the most serious threats facing enterprises, with many attacks beginning through phishing or vulnerable endpoints. That is why employee awareness matters so much: people need to know how to spot suspicious attachments, fake updates, and early signs that a device may already be compromised. That means:
- Looking out for attachments or downloads.
- Paying attention to weird pop-ups and fake updates.
- Observing suspicious system behavior, like loud fan noises, system crashes, or slowdowns.
- Learning how to report and what to do if a system appears compromised.

Security Awareness Program Topics #4: Data Privacy Compliance
Employees who handle sensitive data need to be aware of how to do so safely. That means learning:
- What is sensitive data.
- How to handle that data on a day-to-day basis (including how to store, share, and dispose of)
- How to avoid an accidental leak.
- How to report immediately if a leak occurs.
Security Awareness Program Topics #5: Physical Hardware Security
While most attacks occur digitally, this is not always the case. Physical risks can also lead to incidents, especially on mobile.
That means learning:
- Tailgating and other unauthorized access.
- Securing laptops and documents.
- Clean desk practices.
- Business information on personal devices (including mobile).
Security Awareness Training Topic #6: General Safe Internet Usage
Regrettably, many employees develop unsafe internet habits that go unaddressed over time. Occasionally, these habits can serve as vulnerabilities exploited by cybercriminals, who often do not need to exert significant effort to take advantage of them.
That means learning about:
- Safe browsing.
- Avoiding downloads from untrusted or unverified sources.
- Avoid using public wi-fi.
- Keeping work and personal information as separate as possible.
Security Awareness Training Topic #7: Hybrid And Remote Work Positive Practices
According to Chase Cunningham, former CISO and cybersecurity expert, the shift to remote and hybrid work has fundamentally expanded the attack surface, making every employee environment part of the enterprise security perimeter. That shift means organizations must rely more heavily on employee awareness and secure behavior outside the traditional office, like:
- Locking devices.
- Protecting home networks.
- How to handle work on mobile, tablets, and other devices.
- Working through traveling or in public, like co-working and other spaces.

Security Awareness Training Topic #8: Cybersecurity Incident Reporting
Employees should be thoroughly trained on the proper procedures for reporting cybersecurity incidents, including false positives.
A quick remediation might be the difference between a small cyber incident and a major leak or a ransomware deployment. That means teaching:
- What to report.
- How to report.
- Why reporting quickly matters.
- Why should they do it, even if they are not totally sure.
When it comes to cybersecurity incident reporting, there is also a human touch element. Creating a no-blame culture is just as important as any knowledge. As Professor Angela Sasse of University College London has emphasized in her research on security behavior, people are far more likely to report mistakes and suspicious activity when they do not fear blame or punishment. Without that kind of environment, even well-trained employees may hesitate, turning small, containable issues into larger incidents.
Security Awareness Training Topic #9: AI Cybersecurity Threats
AI is already a major cybersecurity concern. Aside from AI-powered attacks, companies have experienced data leaks stemming from unsafe use of AI.
In the Global Security Outlook for 2026, 87% of respondents believe the risk of AI vulnerabilities has increased from the previous year, the highest among all mapped cyber risks.
Vishal Salvi, Chief Information Security Officer at Infosys, has warned that many organizations are still early in understanding the security implications of AI, even as adoption accelerates. As a result, new risks are emerging faster than policies and controls can keep up—especially when employees experiment with AI tools in ungoverned ways.
In certain cases, breaches occur when employees use personal accounts for some of the most popular models. They upload sensitive data that may be retained to train the model, and, in extreme cases, even appear in another user's answer. There was a recent example of an engineer who leaked data through the AI.
The most important recommendation is to treat chat models as public spaces and to ensure employees do not share sensitive information.
Step 5: Decide On The Format Of The Security Awareness Training Program
Content delivery can make or break security awareness training programs, as employees need to engage with the content in order to retain it.
It is essential that formats are tailored to the specific nature of the content, as certain topics require a more practical, hands-on approach rather than merely explaining fundamental concepts. Adaptive Security features an AI-powered content creator that can generate training materials in seconds.
A security awareness training platform helps create and deliver content as effectively as possible.
Instructor-Led Cybersecurity Awareness Course
Security awareness training courses conducted by cybersecurity professionals allow room for interaction and discussion, adding a human touch that makes them feel even more engaging. Also, it allows for deeper knowledge.
Its limitations include cost-effectiveness, scalability challenges, and occasional inconsistencies. Therefore, it is most suitable for highly strategic, high-value contexts, such as leadership cybersecurity awareness training or high-risk teams. This tradeoff explains why instructor-led training generally offers the greatest value in high-stakes environments.
As SANS instructor Frank Kim explains, leadership-focused cybersecurity training is most useful when it helps participants work through real-world scenarios, connect security decisions to business priorities, and communicate risk effectively across the organization. That makes live, expert-led sessions especially well-suited for executives, leadership teams, and other high-risk groups that need deeper discussion rather than standardized content.
Security Awareness Training Online Lessons
Security awareness training online lessons can be delivered via video, with complementary reading material, and are among the most common formats. Adaptive Security has a comprehensive compliance library with easy-to-digest, up-to-date training.
Its major benefits are the ease of assigning and tracking the most basic metrics, as well as its reach and flexibility, which deliver content across the entire company.
However, they can feel generic and stale, not including any meaningful interaction. This can lead to lower engagement, and employees may just "rush" through it, retaining little information.
It is a highly valuable tool, included in nearly all security awareness training programs, although it rarely functions independently.
Microlearning Security Awareness Training Sessions
Microlearning security awareness lessons consist of brief bursts of information, typically delivered through video or other media.
Their short duration makes them highly memorable and minimally disruptive to employees' routines, aligning well with natural information consumption habits.
However, this brevity limits the depth of content and lacks practical experience. While microlearning lessons can be engaging when integrated with other formats, they should not serve as the core of a comprehensive security awareness training program.
Adaptive Security's content can be adapted into shorter microlearning lessons to enhance your security awareness training program.
Phishing Simulation Tests And Scenario-Based Security Awareness Exercises
Phishing simulation tests and scenario-based exercises are highly effective in educating employees about cyber threats and evaluating their understanding. They are engaging and relevant, offering knowledge applicable to everyday situations.
Customizable security awareness training enhances engagement and effectiveness. Incorporating multi-channel phishing simulators into the curriculum is also crucial, as cyberattacks increasingly target email, SMS, voice, and video channels.
According to Harvard Kennedy School lecturer Bruce Schneier, new phishing techniques are spreading across these platforms, including SMS and voice phishing.
Adaptive Security employs a multi-channel approach, equipping employees to handle threats across the most commonly targeted communication channels. While cyber attack simulations require greater effort and coordination and are less scalable than other modules, the emergence of AI-based security awareness training significantly alleviates these challenges.
Deepfake Awareness Training
Deepfake-powered cyberattacks are becoming so sophisticated that it is practically impossible to distinguish them from the real thing. These attacks use video, audio, and images to impersonate executives and other people in positions of authority, tricking employees into making mistakes.
Adaptive Security develops a deepfake training program to help your company deal with this cyber threat.
A study developed by iProov reveals that only 0.1% of people can accurately detect AI-generated deepfakes. That finding helps explain why deepfake training cannot rely on "spot the fake" instincts alone. After Arup lost $25 million in a deepfake-enabled fraud, CIO Rob Greig said organizations "really do have to start questioning what we see," because audio and visual cues are now being weaponized against the trust people naturally place in them.
In practice, that means the goal of training is not just detection, but teaching employees to slow down, verify requests through another channel, and treat urgency from apparent authority figures with skepticism.
Seeing how realistic they are in training can be eye-opening for employees, fostering a sense of urgency that permeates the entire training. They also teach a very valuable lesson: nothing they see or hear can be taken as immediately true. A good example of an incident is a deepfake impersonation that tricked investors on what stock to invest in.
Cybersecurity awareness training platforms are essential for effective deepfake training. Due to their complexity, it is crucial to engage an external partner.
Step 6: Organize A Security Awareness Training Communication Plan
Employees need to know what to expect from security awareness training. So, establish a clear communication strategy to let them know about the overall project and each training model.
Starting with a launch message that answers the following questions very clearly:
- What is security awareness training?
- Why is awareness training important?
- What is expected of employees in security awareness training?
- What are the next steps of cybersecurity awareness training?
- Any extra context necessary, like role-based training for those involved.
That process should be repeated for every new cyber awareness training session or activity, with reminders about upcoming sessions, exercise deadlines, follow-up messages, and more.
Channels can include email, corporate messaging systems, intranets, and other standard communication channels a company might typically use. But it is also important to reach out at meetings.
An effective method is to personally reach out to leaders and ask them to let their teams know what is coming.
Step 7: Measure The Effectiveness Of The Security Awareness Training Program
From the planning phase onward, it is essential to establish metrics to assess the effectiveness of the security awareness training program. Initiating measurement early on is crucial for obtaining a comprehensive understanding of the entire process.
There are a number of key quantitative metrics to pay attention to, like:
- Cyber attack failure rates (e.g., phishing simulation failure rates, click-through rates on fake emails, and credential submission rates).
- Suspicious activity report rate (number of reports, percentage of suspicious emails reported, time to report).
- Security awareness training activities metrics (completion rates, time spent in training, quiz scores).
- Human risk scores.
- Overall reduction in cybersecurity incidents.
Just as important, if not more so, are qualitative indicators, such as an overall improvement in cybersecurity culture. The best way to do that is to talk to employees, monitor the number of security questions asked, and identify a rise in the adoption of best practices. Adaptive Security has extensive tracking to measure and reduce human risk.
After measuring results, review the numbers and the qualitative research, and begin again at step 1 for the next training cycle.
Advanced Security Awareness Training Program Tips
With the fundamentals established, these advanced tips elevate a solid security awareness training program to an exceptional level. They address more practical decisions and insights gained from our years of experience.
Cybersecurity awareness training is about people, which means it cannot be done by checking numbers alone. The goal is to get employees to engage, not just rush to complete. Also, AI-based attacks, deepfake-powered phishing, and other emerging threats mean companies need to go way beyond the basics.
Cybersecurity expert Bruce Schneier emphasizes that security is fundamentally a human issue, not just a technical one. As he puts it, "Trust is essential to society," which is exactly why modern phishing simulations need to prepare employees for manipulation across multiple channels.
Incorporate AI In Security Awareness Training Plan
A study by Deep Strike revealed a 72% increase in AI-powered cyberattacks over the past year. An even more incredible figure is a 1265% increase in phishing attacks driven by generative AI.
Carl Windsor, Global CISO at Fortinet, argues that AI is "upending cybersecurity in many ways, both positive and negative," and that the pace of AI innovation is moving faster than governance can keep up. That is exactly why AI now belongs inside security awareness training: employees need to understand not only how attackers are using AI, but also how everyday use of AI tools can create new data exposure and policy risks inside the business.
Most cybersecurity experts call AI a double-edged sword, and why employing AI security awareness training is no longer a choice. This technology can help by:
- Personalizing cybersecurity awareness training by role and risk.
- Customizing learning paths adapted to user behavior.
- Generating more realistic phishing and deepfake simulations.
- Creating a cyber risk profile by individuals and across the entire organization.
- Keeping security awareness training topics fresh and relevant with more constant updates.
However, the technology does not replace everything else. It should enhance and empower AI security platforms and tools.

Create An Engaging Security Awareness Training Program
The goal of security awareness and training is to get employees in touch with the most important concepts and the cyber threats they might encounter in their daily work routine. One way to do that is to make it mandatory, and that might work.
But the best way to ensure they retain information is to make it engaging. If training is delivered through a lecture model, it will likely grow stale and not hold their attention. This paradigm shift is occurring across general education, with concepts such as adaptive and interactive learning becoming increasingly prominent.
Adapting these concepts to security awareness training can improve employees' learning experience. Using realistic scenarios, role-based security awareness training, simulations, and tests all contribute to engagement. That is called adaptive security.
There is also the concept of engagement, which can absolutely be incorporated into security awareness training without detracting from its seriousness. Add elements of competition and cooperation between teams, and gamify content with a leaderboard.
Make The Security Awareness Training Program Fit Seamlessly In Work Routine
Awareness training also needs to fit as seamlessly as possible into employees' daily routine. If content is hard to access, time-consuming, or poorly timed, users might not engage with it or just rush it to mark it as completed.
When designing a security awareness campaign, think of the following:
- Make it mobile-friendly.
- Prioritize shorter sessions over longer ones.
- Try to minimize daily disruption as much as possible.
- Make it easy to access.
One way to achieve these goals is through coordinated leadership. Collaborate with overall leadership and by team to discover the least busy moments.
For instance, financial teams are traditionally less busy around the middle to the end of the month. That might be a good time to fit a longer training session or exercise without being too disruptive.
Incorporate The Security Awareness Training Program Into Onboarding
Integrating the security awareness training program from onboarding establishes a security-conscious culture from the outset.
When an employee joins a new organization, they are highly motivated and in a learning mindset. Additionally, it underscores that cybersecurity is an integral component of the company's culture.
This approach is also prudent, as new hires can be among the most vulnerable individuals. They may be overwhelmed by information and new access rights and lack a comprehensive understanding of the company's operational processes.
Security leaders often warn that new hires are especially vulnerable because they are overloaded, unfamiliar with normal workflows, and eager to respond quickly. As Lance Spitzner, Director of SANS Security Awareness, puts it, new employees are already overwhelmed by a new job, new technology, and a new boss, which is exactly why security expectations should be introduced clearly from day one.
Leverage The Right People In Cybersecurity Awareness Training Program
Positive reinforcement can also help with employee engagement in security awareness training. There are plenty of situations that will give the team an opportunity to reward good behavior. For instance:
- When users report phishing emails or other attacks.
- When they do well on cyber awareness training exercises or simulations.
- Every time there is a discussion or questions about the main cybersecurity awareness topics.
- Showing improvement over time, especially after making a mistake.
The objective is to ensure that the cybersecurity awareness program is proactive rather than reactive and to facilitate the normalization of the decision-making habits that the team is encouraged to develop.
When employees interact with the security team only after mistakes, it can create the perception that the program exists solely to penalize. Conversely, when communication occurs after successful actions or positive performance, it fosters a different impression, one that emphasizes support and constructive engagement.
Implementing tangible rewards, such as gift cards for achieving 100% scores on phishing or deepfake simulations, can effectively increase participation.
A strategic approach to enhancing engagement involves identifying and empowering employees who exhibit a genuine interest in cybersecurity. Recognizing these individuals as champions of cybersecurity awareness can significantly improve overall team engagement, as they are likely to influence and motivate their less-engaged colleagues.

Deploy The "Golden Phish" To Ensure Engagement In Security Awareness Training Program
The "Golden Phish" is a widely successful security awareness training exercise implemented across numerous teams. It integrates collaboration, competition, and unpredictability to enhance engagement.
The concept involves announcing that a "Golden Phish" will be randomly sent to an individual or group without prior notice. The first to correctly report it wins a reward. Such exercises are effective in revitalizing cybersecurity training and helping maintain employee interest.
Lance Spitzner, a security awareness expert at the SANS Institute, emphasizes that behavioral change is achieved through active engagement rather than passive information dissemination. Exercises like the "Golden Phish" succeed because they encourage ongoing reporting, reinforce desired behaviors during actual incidents, and create memorable experiences that promote lasting habits.
Use Examples Of Cybersecurity Attacks In Security Awareness Training Programs
Including examples of successful cyberattacks effectively enhances a security awareness training program. Colleagues will recognize how real and immediate these threats are. Additionally, it encourages discussions not only about the news presented but also about their own experiences. Here are three recent cyberattack cases:
- The fake résumé malware attack: Cybercriminals are targeting HR teams with fake résumés that actually contain malware.
- The $25 million deepfake phone call: A financial analyst fell for a deepfake video scam impersonating his Chief Financial Officer and forwarded $25 million to cybercriminals.
- The fake app: Cybercriminals trick employees into downloading a modified version of a common app to steal sensitive company data.
- The INTERPOL mega operation: An INTERPOL mega operation shut down more than 45.000 malicious IPs. News like this is interesting for showing the scale and organization of cybercrime.
Explore the Adaptive Security Demo to see how we can help your organization develop a program that drives meaningful behavioral change.
Study The Main Security Awareness Training Providers
There is plenty of information to consider when selecting a security awareness training provider, especially if a comprehensive approach is desired. Engaging external experts is the most cost-effective method to initiate a training program. Review the market to identify providers that best meet specific requirements.
Below, we will discuss some security awareness training platforms.
Common Challenges & Mistakes When Building A Cybersecurity Awareness Training Program
Even the most meticulously designed cybersecurity awareness training programs can encounter difficulties, particularly if the team is unprepared for the inevitable challenges.
A common mistake lies in how the security awareness program is constructed. Managers often view the necessary topics as a simple compliance checklist. Content should be created with the learners in mind and tailored to fit their needs.
This is where many programs falter. Professor Angela Sasse, a leading researcher in human-centered cybersecurity, emphasizes that security is most effective when it is designed to collaborate with people and organizations, rather than oppose them. Practically, this means that awareness content should be based on how employees actually work, the pressures they encounter, and the behaviors most crucial to strengthen within the organization, rather than merely fulfilling a list of requirements.
Not Getting People To Buy Into The Security Awareness Program
One of the primary challenges of cybersecurity awareness program is securing buy-in from the entire organization. This involves obtaining support both from leadership and employees.
Regarding employee engagement, it is crucial to demonstrate empathy and avoid making unfounded assumptions.
Initially, understand what could motivate employees to participate in security training that they might not find inherently interesting. Additionally, do not assume compliance solely based on directives; persuasion and understanding are key.
For leadership support, the main objective is to illustrate the value of the cyber awareness plan. Their endorsement is not merely about sponsorship but about active participation, which influences the entire team's engagement.
The level of support from leaders often hinges on their perception of security awareness as a strategic business priority rather than a mere compliance requirement. As Lance Spitzner of the SANS Institute notes, strong leadership support facilitates the expansion of awareness initiatives by underscoring security as a fundamental business value rather than merely a procedural obligation. Visible engagement from executives significantly increases the likelihood that employees will take the program seriously and commit to it.
Making The Content Of Security Awareness Training Program Too Sparse And Stale, Or Too Bloated And Boring
Finding the right balance in security awareness training topics is also a major challenge.
While general employees are not specialists, it will be evident to them if the content is outdated, generic, or lacking depth. It is essential to add substance, cover key concepts thoroughly, and allow space for practice.
However, including every detail in an awareness training plan is not advisable. Concentrate on the information employees need to know and ensure it is delivered effectively.
Finally, maintaining up-to-date content is crucial not only for engagement but also for preventing training from becoming a waste of time. Outdated training can mislead colleagues, potentially teaching them to defend against yesterday's cyber threats rather than current ones.
Purdue cybersecurity expert Gene Spafford has long emphasized that effective security must be grounded in real-world threats and continuously updated practices. Training that does not reflect how attacks actually evolve risks giving employees a false sense of preparedness.
Making Security Awareness Training Hostile Or A Chore
Considering employees' vulnerabilities as if they were technical flaws is a significant error that can jeopardize any cybersecurity awareness initiative, regardless of how carefully it has been planned. Here are some examples of pitfalls to avoid:
- Having a hostile tone towards mistakes.
- Creating content that feels like busywork.
- Phishing simulations or deepfake simulations that embarrass people (especially in front of their colleagues).
Key Takeaway: The worst outcome is not making boring or ineffective content, but creating a hostile, chore-like security awareness training environment that makes employees disengage, disconnect, and resent it.
Putting All Of The Focus On The Engagement Metrics Of Security Awareness Training
Relying exclusively on engagement metrics can create the illusion that the security awareness training program is operating flawlessly. However, these metrics often fail to capture the full context and overlook the most critical aspect: human behavior. Consider the following examples:
- Completion rates of security awareness training exercises
- Time invested in security awareness activities
- Scores from phishing and deepfake simulation assessments
While these figures are straightforward to measure, interpret, and present, they are only part of the picture. Relying solely on them may cause a significant insight gap. Therefore, it is also essential to assess behavioral changes and identify indicators of a strengthened security culture.
Lance Spitzner, Director of SANS Security Awareness, argues that teams should focus on measuring behaviors that actually reduce human risk, not just surface-level engagement. As he puts it, "Measure what you care about," meaning metrics should reflect whether employees are reporting suspicious messages, following verification steps, and making safer decisions over time
Key takeaway: If engagement metrics are low, the security awareness training program is probably failing. But if they are high, the program is not necessarily a success.
Overrelying On Gamification In Security Awareness Training Plan
Gamification is a highly effective training tool that can significantly enhance engagement. However, it is not a universal solution or a quick fix. Typically, it serves best as a supplementary strategy rather than the primary approach. Employees are unlikely to find the content meaningful solely because it is presented as a game.
Additionally, it is crucial to consider the tone. An overly playful or distracting style may detract from the credibility and seriousness of the security awareness training program. While gamification can be highly successful, its effectiveness depends on a solid foundational approach.
Future Trends In Cybersecurity Awareness Training
Future trends in cybersecurity awareness training are expected to emphasize personalized, tailored, and behavior-focused content. Organizations are increasingly leveraging artificial intelligence as an educational resource to stay ahead of cybercriminals, who also use AI to enhance their techniques.
According to Lance Spitzner of SANS Institute, modern security awareness programs are evolving beyond one-size-fits-all compliance modules and toward approaches designed to drive measurable behavior and culture change.
Below, we examine some of the upcoming trends.
- A stronger emphasis on culture rather than on individual threats: As threats continue to evolve, it is increasingly important to prioritize understanding overarching concepts over focusing solely on specific ones.
- Continuous learning: While mapping training sessions to a few times a year remains beneficial, delivering ongoing training is more effective.
- AI-driven and deepfake training: These represent the two emerging major technology trends. Training programs must increasingly incorporate these areas.
- Personalized and adaptive training: AI also enhances training by making it more personalized and adaptable, allowing content to be adjusted in real time based on employee engagement.
Adaptive Security's awareness training and phishing simulations are crafted to be future-proof, defending your company against both current and emerging threats.
What Are Security Awareness Training Platforms?
Security awareness training platforms are software or services that help organizations develop and deliver training content, test employee understanding, and evaluate outcomes.
They consolidate training data and leverage expert support to craft optimal learning paths, often integrating components such as phishing and deepfake simulations, human risk assessments, participation metrics, and content distribution.
Organizations seek security awareness training software because they frequently face challenges in creating, scaling, and quantifying training efforts independently across organizations of diverse sizes. Engaging an external partner is often the most cost-effective approach to establishing a comprehensive security awareness program.
Building an internal security awareness training program can be difficult without a clear framework, as Lance Spitzner notes in recent SANS guidance, arguing that organizations have long lacked "clear structure or strategy" for managing human risk.
What Features To Look For In Security Awareness Training Platforms?
Selecting the appropriate security awareness training software is essential for launching an effective program. Ideally, the chosen tool should be comprehensive, covering all critical aspects, rather than being limited to basic content delivery management. In summary, the ideal solution should allow companies to:
Security Awareness Training Topics
What is the quality of the security awareness training tools available? When considering the main topics in security awareness training, a chosen tool should adequately address them. The library should be current, practical, and easy to use, similar to the Adaptive Security full compliance library.
Additionally, it is crucial to evaluate the content from the perspective of the typical user—in this case, the general employee who is not an expert. For example:
- Simple, easy-to-understand language.
- Realistic scenarios.
- Offers both basic and advanced content.
- Varied delivery format, with a special focus on mobile.
Realistic And Role-Based Phishing Simulators
Phishing simulators and their variations are essential components of any security awareness platform. This includes email phishing, vishing, SMS phishing, deepfakes, and others. Such features are vital because they reinforce learning and introduce a practical, realistic dimension to the training content.
John Pescatore, Director of Emerging Security Trends at SANS Institute, argues that phishing simulations matter because phishing remains one of the most effective ways attackers compromise organizations, and as John Pescatore notes, successful phishing attacks continue to play a major role in enabling damaging security incidents.
Creating phishing simulators without the assistance of a security awareness training provider is a complex task. Building one from the ground up risks producing a shallow and outdated product.
To assess the effectiveness of phishing simulators, utilize demos, tours, and possibly a proof of concept. Adaptive Security solutions offer comprehensive phishing simulation capabilities, including deepfakes, voice, and email features.
Simple Role-Based Security Awareness Training
Role-based security awareness training is an essential tool, as it enables employees to recognize threats relevant to their daily responsibilities. When selecting a cybersecurity awareness training platform, ensure it supports customizing training programs by role, department, or industry.
Personalized Security Awareness Training
Personalized security awareness training involves customizing the experience for each individual, not solely based on role but also on their unique learning style. Recognizing that individuals learn at their own pace, the most effective tools facilitate the creation of a tailored learning path for each person.
Adaptive Security emphasizes this level of personalization, enabling teams to customize training both by role and by individual learning preferences.
Individual And Company-Wide Risk Measurement
Results should be straightforward to evaluate both on an individual basis and across the entire organization. Security awareness tools typically measure individual outcomes, particularly if they incorporate simulations and track performance.
Additionally, this data is valuable for developing a comprehensive risk assessment at the company level, which can be achieved through Adaptive Security risk management and human risk assessment.
Easy To Report Threats Functionality
Having a straightforward reporting process for cyber threats facilitates tracking the development of knowledge within the organization and for individual employees. In addition, it enhances overall security by allowing the security team to respond promptly to potential cyberattacks.
Adaptive Security features a Phish Triage tool that enables users to easily report phishing attempts.
AI-Based Security Awareness Training
Including AI security awareness training is essential to keep content current and relevant. Additionally, AI enables scalable and highly customizable training for a larger workforce.
It is also important to address both the benefits and risks of AI, as it increasingly presents potential vulnerabilities. Training should teach employees how to use AI responsibly.
User Experience On Security Awareness Tools
User experience encompasses both employees and administrators. When either party interacts with an inefficient interface, implementing cyber awareness training becomes more challenging, leading to reduced engagement. During the platform trial, consider the following:
- Ease of navigation.
- Lean and clear dashboards.
- Logical and direct workflows.
- Mobile access.
Automated Deployment And Security Awareness Campaign Scheduling
Automated deployment and scheduling streamline the use of security awareness tools, reducing the reliance on manual intervention. Administrators can efficiently automate significant portions of the process.
Security Awareness Platforms Vs. General Learning Management Systems
General learning management systems excel at organizing content distribution. Their strengths include covering a broad range of topics, though they often lack the ability to provide detailed content on niche subjects like security awareness training.
Conversely, specialized security awareness training platforms are designed to deliver the targeted, technical content required for such areas. These platforms often feature phishing simulators and detailed phishing reports, functionalities that are difficult to replicate within a general LMS.
Nonetheless, a traditional LMS can still support security awareness initiatives by effectively delivering basic information.
As Bruce Schneier has long argued in his work on human-centered security, cybersecurity training is not just about delivering information; it is about changing how people behave under pressure from real-world attacks. That is one of the biggest differences between a dedicated security awareness platform and a general LMS.
Key takeaway: Cybersecurity awareness platforms and general learning management systems each have their strengths, but they are not built for the same purpose. One aims to teach specific skills, while the other aims to host a broader range of topics.
Adaptive Security And The Security Awareness Training Vendors For 2026
Adaptive Security emphasizes AI-driven attack simulations, utilizing data and user behavior to tailor training in real time for optimal results.
Our security awareness services include a variety of simulations, such as deepfake training, which leverage some of the most advanced attack tools. This approach makes cyber awareness training engaging while effectively highlighting real threats. To learn more, review Adaptive Security's customer success stories.
Providers in security awareness training include KnowBe4, Proofpoint, Hoxhunt, and Ninjio. Feel free to compare Adaptive Security with these solutions.
Additionally, schedule an Adaptive Security demonstration to develop a defense program against the latest threats in phishing, vishing, deepfake attacks, and beyond.

Frequently Asked Questions
What Is Security Awareness Training?
Security awareness training is a structured project designed to teach employees how to recognize, avoid, and report the most common cyberattacks they might see in their work routine. It also aims to teach good cyber habits. The goal is to reduce a company's cyberattack surface by addressing human vulnerabilities and ultimately helping to create a company-wide cybersecurity culture.
How Can A Small Business Develop A Security Awareness Training Program?
Small businesses need to budget their time carefully. They need to focus on the biggest threats, like phishing attacks, password management, and data handling. A main goal is to make the program practical, direct, and consistent.
Is A Cybersecurity Training Program Hard To Understand For Non-Technical Employees?
No. The goal of a cybersecurity awareness training program is to teach non-technical employees how to respond to cybersecurity attacks they might encounter in their day-to-day work. If the program is hard to understand, it should be reevaluated. They do not need to know jargon and complex security concepts.
How Long Should A Security Awareness Training Program Be?
A security awareness training program should be an ongoing project, with constant training sessions throughout the year. Individual sessions can last as long as necessary, depending on the content to be delivered and how they fit into employees' daily routines. Combining longer sessions with shorter, more frequent exercises and reminders offers a good balance.
How Often Should Security Awareness Training Programs Be Conducted?
A security awareness program should be continuous and constant. However, training sessions can be run yearly for longer ones, or monthly or quarterly for shorter ones. The main takeaway is that a security awareness training program never ends. It is consistently delivered and upgraded.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents