This comprehensive 2026 guide to cybersecurity awareness training is designed for security professionals across small, medium, and enterprise organizations, seeking to safeguard their companies against the persistent threat of cybercriminals.
The goal is to cover the fundamentals of cybersecurity awareness training, its importance, and all essential information to begin implementing an effective program today. To learn more, schedule an Adaptive Security Demo to see how the right tools can facilitate a successful training initiative.
What Is Security Awareness Training? What Does Cybersecurity Awareness Training Mean?
Security awareness training means educating employees on cybercrime threats that they might be exposed to or targeted by. The goal is to teach them, through a structured program, to be aware of, recognize, report, and remediate the most common vectors cybercriminals use.
Each of these 4 steps is crucial:
- Security awareness: Employees need to know what they are up against. Otherwise, they will be more vulnerable to cyberattacks.
- Avoiding common threats: Arm employees with the knowledge to avoid falling for the most common ones. What to look for? What scenarios are common?
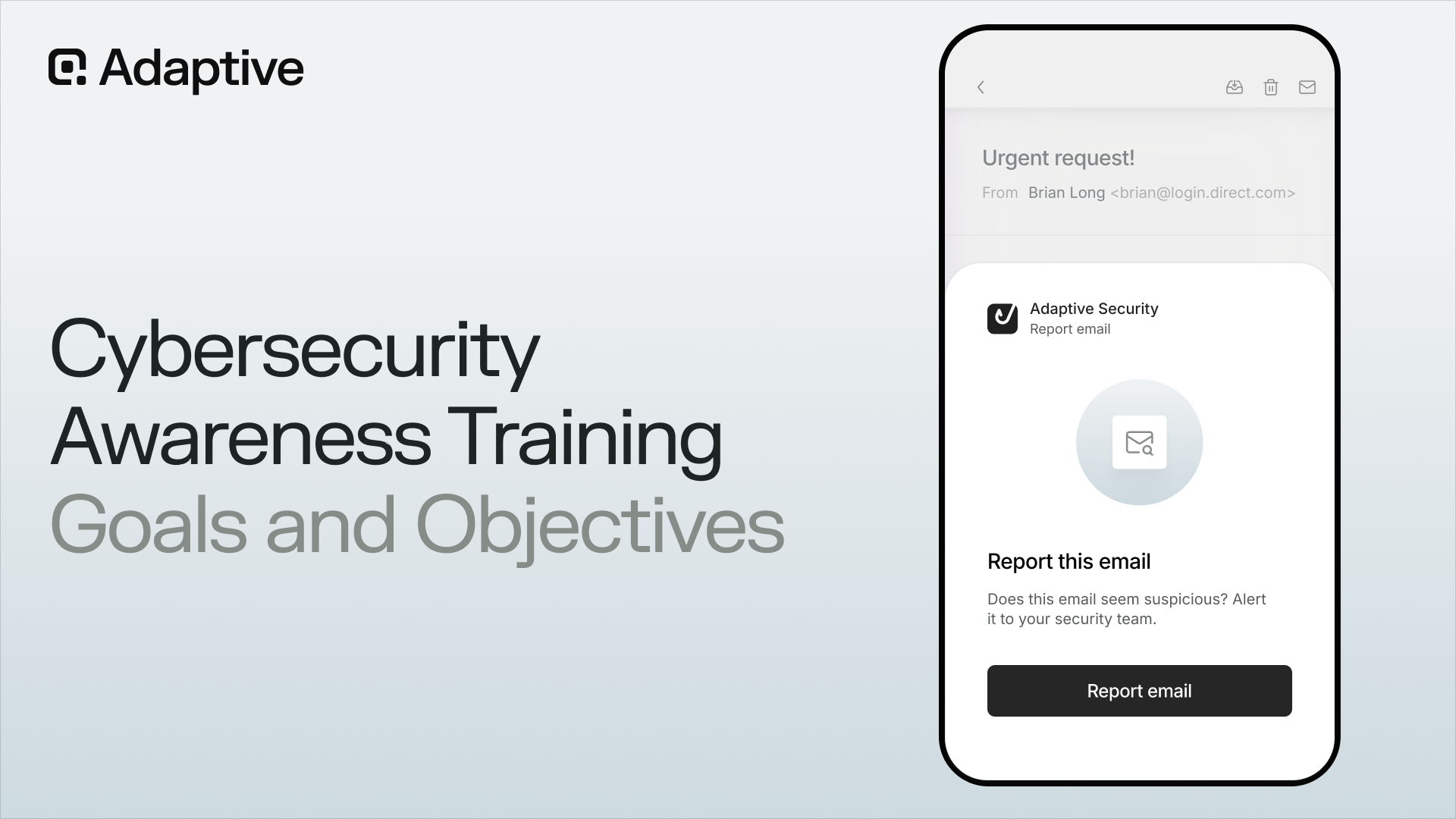
- Reporting potential incidents: Employees need a secure, clear channel to report problems, including potential ones.
- Remediation: Employees need to know what to do immediately after an incident. Having them lost and panicked is the worst-case scenario.
Common Misconceptions In Cybersecurity Awareness Training

There are plenty of misconceptions about cybersecurity awareness training:
- Security awareness training eliminates cyberattacks: Attacks can still occur even in very well-trained organizations. The goal is to reduce the cyberthreats as much as possible, especially on the human front.
- One-time training is enough: Threats evolve every day. Training should be constant and consistent.
- Confusing awareness campaigns with training: Campaigns typically address only the awareness component. Basically, only the "Why?" while training also brings the "How?"
- Leaving cybersecurity solely to IT: Cybercriminals often target people outside of the IT team, who are less prepared to handle attacks.
- Employees are safe: Employees can be a major target for cyberattacks, especially if they are not well protected or well educated.
- Having a single training process: Training varies from company to company and even from role to role. A customizable cybersecurity awareness training program is always best.
- Technology will handle it all: Technology is a pillar of cybersecurity, but it can fail when cybercriminals attack human behavior.
- Cybersecurity awareness training is optional: With all the money and potential risks at stake, this is far from the truth.
What Are Some Security Awareness Training Frameworks?
Here are some of the most effective security awareness training frameworks, by some of the most reputable organizations on the planet:
- Center for Internet Security (CIS) Security Controls: This complete framework has a chapter dedicated to training.
- International Organization for Standardization (ISO): More specifically, ISO/IEC 27001, which discusses information security, cybersecurity, and privacy protection.
- MITRE ATT&CK Framework: MITRE is not strictly a framework, but it provides extensive guidance on conducting training.
- National Institute of Standards and Technology: Another widely used framework, developed by one of the top US agencies.
- OSINT: Using Open-Source Intelligence, especially with AI automation, is another widely common practice.
In practice, most organizations do not need to be fully versed in all of these frameworks. While they can serve as useful reference points, it is often more effective and efficient to engage external expertise.
The Importance Of Cybersecurity Awareness Training In 2026
Cyber awareness in 2026 is important to directly address one of the most common entry points for cyberattacks: employees. Cybercriminals target employees with phishing, social engineering, credential theft, and many more, focusing as much on human vulnerabilities as on technical ones. And it works.
According to the 2025 Verizon Data Breach Investigations Report, 68% of all breaches involved a non-malicious human element, such as falling victim to a social engineering attack or a simple mistake.
And the costs are evident.
A study by Cybersecurity Ventures projected that cybercrime will cost the global economy over $10.5 trillion annually by 2025. This figure is nearly three times the worth of the world's most valuable company. If cybercrime were a country, its economy would rank as the third largest, behind only the United States and China.
Meanwhile, the average cost of a data breach is approximately US$4.88M, according to IBM's Cost of Data Breach Report. In the US, those numbers reach up to US$10.22M.
Those costs might include ransom payments, response costs, lost revenue from downtime, fraud, legal costs, and, worst of all, reputational damage.
The outlook remains concerning: cybercrime shows no signs of slowing, quite the opposite. The rise of AI-powered attacks, cybercrime-as-a-service, deepfakes, and related innovations enables threat actors to operate at greater scale, with greater sophistication and efficiency, while expending significantly less effort.
How Can Awareness Of Cybersecurity Threats Help Employees?

Cybersecurity awareness training must keep pace with evolving threat actor objectives. Namely, to inflict maximum impact with minimal effort. How is this typically achieved?
1. Initial Access: Cybercriminals use publicly available, legally obtainable information, or compromised data such as phone numbers or email addresses, to launch a phishing email campaign.
2. The Power of a Single Victim: Even if only one employee falls for the scam, it is sufficient for the attackers to achieve their objective.
3. Planning Stage: Following the initial breach, cybercriminals do not rush. They take their time, collect extensive information, and meticulously plan their subsequent actions. They operate covertly within a company's systems, continuously browsing for valuable data, targeting recovery paths, and planning the next stage.
4. Escalation Process: Using privilege escalation techniques and the information already acquired, cybercriminals gain unauthorized access to additional sensitive data, expanding their control.
5. Action: Armed with detailed information about an organization's defenses, cybercriminals can launch targeted attacks designed to inflict maximum damage.
The result? An average of US $10M lost.
Add to this the current geopolitical landscape, the fact that the United States is a primary target for cybercriminals worldwide, and the prevalence of attacks motivated by corporate espionage.
To be frank, attacks are continuous and originate from multiple directions. Employees must be fully aware of potential targets and the methods used.
Why Does Security Awareness Training Need To Constantly Evolve?
Awareness training must adapt to stay ahead of cybercriminals and the continually evolving AI-related security threats.
Cybercrime functions as an ongoing cycle: threat actors discover new phishing tactics or vulnerabilities, and cybersecurity professionals respond by developing new defenses, in a never-ending process.
Movies and television programs frequently misrepresent the methods employed by cybercriminals. The common stereotype depicts a hacker diligently working at a computer, typing continuously until they breach security defenses.
Cybercrime is a professional industry, with sophisticated organizations and nation states plundering billions of dollars a year from communities, countries, and private businesses. They exchange information and technology and buy and sell leaked data. Their methods are far more sophisticated than we can readily comprehend.
Efforts are currently underway to dismantle these criminal enterprises by organizations worldwide, like the FBI and Interpol. For example, in March 2026, the United States successfully dismantled one of the world's largest hacker forums.
However, a dismantled organization creates a power vacuum that soon is filled by another. That is the cycle in organized crime.
The Two Pillars Of Cybersecurity: Technology And Cyber Awareness
The conclusion is clear: technology alone is insufficient without cybersecurity awareness. Implementing the latest security infrastructure is ineffective if cybercriminals can trick employees into revealing sensitive information.
The principle is similar to house security: even the most advanced security system and the sturdiest door are useless if the intruders know where the spare key is.

Remember, cybercriminals aim to maximize damage with minimal effort. Therefore, targeting employees remains the simplest and most effective strategy for them.
Why Are Employees Targeted For Cyber Attacks? Cyber Awareness Training And The Human Factor
Humans are a primary target of cyberattacks because they can be easy marks, particularly if they lack basic cyber awareness.
Consider the following scenario:
A financial analyst is working in the middle of the afternoon. They are overworked, fatigued, and facing multiple urgent demands. Simultaneously, they receive an email, a voice message, a text, and a phone call from the company CEO.
All the messages reference the same issue and appear entirely legitimate. However, they are, in fact, deepfakes of the C-level executives. The analyst, deceived by the scam, transfers tens of millions of dollars to cybercriminals.
The most striking point is that this scenario is not hypothetical; it is similar to a real-world case.
So, what should companies do in such a scenario? They need to prioritize human-centric security.
Businesses must provide their employees with the necessary tools and knowledge to safeguard the organization effectively.
Watch an Adaptive Security Awareness Training demo to learn how to protect a company from AI scams.
What Are The Main Types Of Cybersecurity Awareness Training Methods?
Cybersecurity awareness and training methods can vary according to the company's needs and budget. In this section, we outline some of the most common paths to implementing a security awareness training program.
Security Awareness Training Online Courses
How it works: Online cybersecurity awareness training courses can be offered in various formats, including live sessions or on-demand modules, delivered through dedicated learning platforms or other content distribution channels.
Strengths: Easy to implement and assess, scalable to larger organizations, and capable of covering a broad spectrum of topics.
Weaknesses: It can lead to fatigue more quickly, offers no effective way to measure knowledge retention, provides limited opportunity for interaction, lacks meaningful practice, and does not offer a hands-on approach.
Microlearning Lessons For Improving Security Awareness
How it works: Shorter training sections focusing on specific topics.
Strengths: Easily engaging, particularly given the format. Enhances knowledge retention and maintains interest. Also straightforward to deliver and compatible with work schedules.
Weaknesses: Limited in content depth. Requires consistent scheduling. Focuses on raising awareness rather than on the depth required to equip individuals to handle threats.
Newsletters And Security Awareness Campaigns
How it works: Provides employees with regular updates through email or alternative channels. While not traditional training, it is often mistaken for it.
Strengths: Facilitates ongoing communication and boosts awareness. Simple to deliver updates regarding new threats to staff. Cost-effective, quick to implement, and straightforward, fostering an active security culture.
Weaknesses: Easily overlooked or ignored, with limited means to gauge true engagement. Offers minimal educational depth.
Instructor-Led Security Awareness Training
How it works: Workshops dedicated to training, hosted by security professionals.
Strengths: Highly interactive and engaging, allowing room for discussion. Delivers more quality learning, with material built and conducted by the professional.
Weaknesses: Difficult to organize; costly and time-consuming, as it requires the involvement of a highly compensated professional.
Phishing And Simulated Threat Exercises
How it works: Delivers exercises through simulated cybersecurity incidents, demonstrating how to respond at each stage of a cyberattack, from detection to resolution.
Strengths: Creates scenarios that teach practical and valuable lessons. Highly engaging and interactive, incorporating hands-on learning. Different exercises ensure the training remains fresh rather than repetitive.
Weaknesses: Demands more time and preparation. Typically limited to specific team members.
Role-based training for Security Awareness
How it works: Exercises tailored for specific job roles.
Strengths: Relevant to employees' daily routines. Teaches the risks of specific roles. Especially useful in high-stakes departments.
Weaknesses: Requires greater investment and is more complex to organize, particularly in larger organizations with highly specialized roles.
AI-based Security Awareness Training
How it works: Uses artificial intelligence to develop and adapt lessons, as well as to simulate attacks, creating engaging and effective content.
Strengths: Can be highly personalized, simulate attacks, and apply adaptive learning techniques to cybersecurity training. It also offers greater scalability and supports continuous training at a lower cost.
Weaknesses: It can be costly and difficult to develop, often requiring external expertise for proper implementation and use.
How To Choose And Implement The Best Cybersecurity Awareness Training Option For A Company?
Each method of security awareness training operates within the scope of its intended purpose.
For instance, microlearning lessons can be highly effective, but they often lack the depth required to serve as the sole training method for employees. Instructor-led training, by contrast, may provide the strongest learning experience, but it is more difficult to scale and typically involves higher costs.
How does cybersecurity awareness training work?
Cybersecurity awareness training utilizes a combination of methods and resources to empower employees to recognize, identify, avoid, and report cybersecurity threats.
The training is conducted according to a comprehensive long-term plan, beginning with an assessment of the team and the introduction of essential concepts.
Subsequently, exercises and interactive tools, including AI-based security training, serve to reinforce learning and enhance engagement.
Additionally, cybersecurity experts should continuously evaluate training through KPIs that measure engagement and behavioral changes to determine its effectiveness. Clear communication channels must also be established to support employees effectively.
How to build an effective security awareness training program?
The best security awareness training for a company takes into account budget, risk profile, and team profile.
Identify Who Needs To Take Part In Cybersecurity Awareness Training
Essentially, everyone, from entry-level employees to executives, should participate in and undergo security awareness training.
Organizations should not invest the same level of effort in training an intern as they would for a CEO or CFO. However, all employees should participate in at least basic security awareness training.
The ideal approach is to review the company's organization chart and develop training models tailored to each employee. Break it down by job position or by team:
- Executives: The most valuable targets within any organization. They typically have access to most, if not all, of the company's data and systems and the authority to approve significant transactions.
- IT and security teams: In addition to managing highly sensitive tasks across the organization's systems, they are usually responsible for threat detection and remediation. Due to the technical expertise required, they often undergo specialized training that differs from general security awareness programs.
- Finance and accounting: As the saying goes, "follow the money", and cybercriminals do. Financial teams are prime targets for scams involving fraudulent payments and related schemes.
- HR: Often overlooked, HR teams manage highly sensitive personal data. Information such as social security numbers can cause significant harm if leaked.
- Developers, product managers, and digital engineers: Individuals involved in digital product development must be particularly vigilant about cybersecurity to create resilient tools.
- Remote workers: Often face additional risks because the company has little control over their personal networks and devices.
The simplest and most effective method is to have a more general training that everyone needs to attend. Complement that with specialized training and information dedicated to each role.
List The Main Cybersecurity Awareness Training Topics That Need To Be Covered
The following are among the most critical security awareness training topics employees should understand. Certain topics, such as executive phishing, are specific to particular job roles.
The challenge is to be strategic regarding time. It is impossible to cover everything, so prioritizing the most important information is essential. For example:
- Phishing and its variants, like spear phishing or executive phishing
- AI-powered security awareness training
- Deepfake security awareness training
- Business email compromise scams
- Social engineering
- Multi-factor authentication
- Passwords and best practices
- Credential theft and account takeover
- Malware and ransomware
- Malicious websites and safe web browsing
- Remote work and device security
- Smart handling of sensitive data (personal, customer, and company)
- File sharing and cloud usage
- Recognition, reporting, and remediation
Create The Most Customizable Security Awareness Training Possible
We covered the types of cybersecurity awareness training in the topic above and concluded that the best security awareness programs combine these approaches. The question then becomes: how should organizations select the right combination?
The optimal approach largely depends on budget and risk profile.
For example, a company might conduct monthly micro-sessions, complemented by more in-depth AI or expert-led sessions each semester. Between these, incorporate phishing simulation exercises with leaderboards to motivate top performers.
The key is to blend cost-effective, quick reminder sessions with comprehensive, detailed training. Vary the formats to maintain engagement.
Customize training based on roles and individual users, leveraging AI tools that tailor content to each person's learning pace and style. Develop industry-specific scenarios using examples to enhance relevance for employees.
Measure The Effectiveness Of Cybersecurity Awareness Training
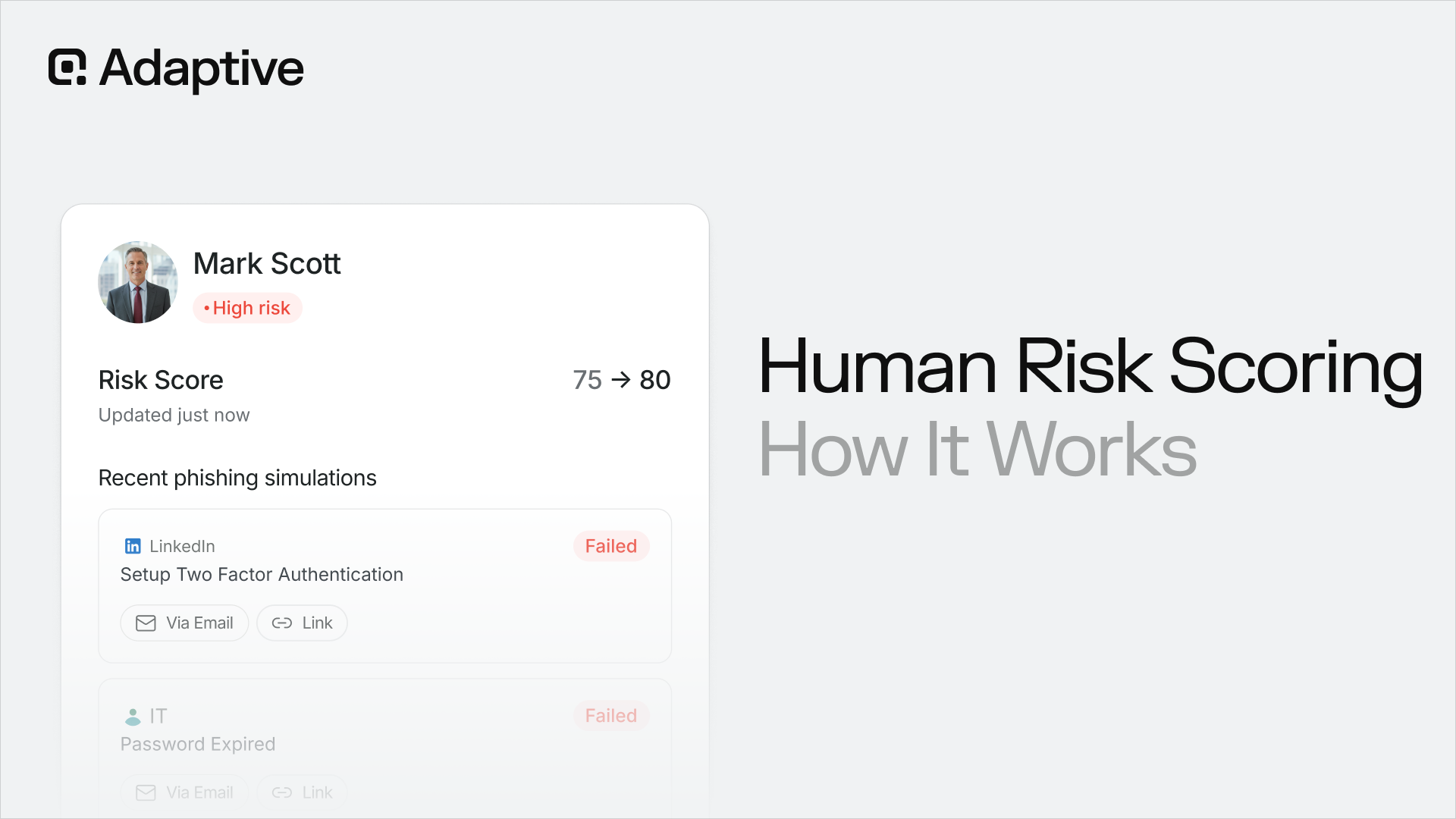
Several KPIs can help assess the effectiveness of a security awareness training. The goal is to measure both engagement and behavioral changes across short-, mid-, and long-term periods.
Below are some key performance indicators for Cybersecurity Awareness Training.
- Training completion and participation rate.
- Quiz rate and knowledge retention score
- Simulation scores results (such as phishing click rate or information sent rate), with the main focus on improvement over time.
- Threat report rate, in simulations and in actual cyberattacks. Good training, done consistently, results in an overall improvement in threat reports, even if some false positives fall through.
Three very important points:
Avoid focusing solely on participation metrics. While these metrics are important and security teams should monitor them, they are not the only indicators. The primary objective of training is to alter behavior, which is better assessed by other metrics.
For instance, training delivered via video or over a call can be easy to overlook. It is common for the employee to do other work while training happens in the background.

Measure consistently and reliably. Measure consistently and reliably, and maintain a documented history of key performance indicators (KPIs). The primary objective is to track improvement over time. Without this approach, it is difficult to determine whether the training is truly effective.
Conduct regular phishing and AI-generated deepfake video simulations. Organizations should devote most of their effort to simulations, as phishing remains by far the most significant threat to employees and the most common attack vector targeting them directly.
Deepfakes and AI-generated video attacks are becoming increasingly sophisticated. Without a clear understanding of this threat, individuals are far more susceptible to being deceived.
Prioritize Getting Customized Security Awareness Training
Customizable security awareness training involves designing exercises and lessons specifically tailored to a company's unique needs. Include considerations of the industry, workforce, threats, and, occasionally, examples to develop realistic simulations.
Awareness training becomes significantly more effective when it shifts from general knowledge to role-specific, actionable knowledge. This approach better prepares employees to respond to the threats they are most likely to encounter in their day-to-day work.
Not only is this approach more effective from a learning perspective, but it also makes training more engaging. Employees are generally more invested in training when the content feels relevant and familiar to their day-to-day responsibilities.
Finally, this is a lesson we have learned through our work with customers at Adaptive. When employees undergo training that includes a deepfake of someone they personally know, it serves as a powerful reminder of how realistic and close to home these threats can be.
All of these factors have a significant impact on training effectiveness.
Build A Company Culture Based On Information Security Awareness
Cybersecurity awareness must extend far beyond a few lessons and exercises throughout the year. It should be a fundamental aspect of a company's culture.
The most effective approach is to foster a sense of ownership among employees. Cybersecurity is everyone's responsibility, not just a select few. Here are several strategies to achieve that.
- Leadership support: Executives should prioritize cybersecurity as a key discussion point in meetings. Recognize and celebrate cybersecurity successes as accomplishments.
- Ensure regular training: As previously mentioned, regular training and exercises keep the team prepared. Avoid neglecting these vital activities.
- Establish a clear communication channel: Arguably, this is the most crucial aspect of cultivating a strong organizational culture. Its significance warrants dedicated attention.
- Gamification helps: The advantages of gamification are well established, and this holds in the cybersecurity domain.
Provide Clear Channels Of Communication (With A Human Touch)
To be effective, awareness training must include two-way communication; without it, the program risks becoming little more than a compliance exercise. Employees need a clear channel to ask questions, report incidents, and raise concerns.
However, there is an important caveat: effective communication requires more than simply creating a Slack channel titled #security. While that may be one component of the process, it is not sufficient on its own.
Cybersecurity is a sensitive subject, and employees may feel embarrassed, uneasy, or reluctant to admit they lack understanding or have been targeted by a scam.
Consider the employee's perspective: after investing time and effort in cybersecurity awareness training, they nonetheless fall victim to a scam. At a minimum, this can lead to embarrassment; at worst, it may create fear about job security, an outcome organizations should strive to avoid.
It is essential to add a more human touch to these conversations. Designate an individual or team responsible for responding to direct messages and private conversations with employees. Reward people for reporting, and always, always establish a no-blame reporting culture.
Make Security Awareness Training Future-Proof
Threats evolve so rapidly that it is not feasible to rely on a single awareness training program for more than a year. The question, then, is how organizations should respond. There are three effective ways to address this challenge and ensure that training remains relevant and up to date.
Focus on broad concepts. It does not matter which phishing scams are most common; they always rely on the same triggers: a sense of urgency and authority. For example, a deepfake of a senior executive requesting immediate action can be highly persuasive.
Ensure that training is continuous and consistently improved to promote knowledge retention, keeping it current and pertinent.
Utilize tools such as AI to enhance customization and maintain freshness. AI integration adds a level of agility that is difficult to achieve through traditional methods.
Look Into The Best Security Awareness Training Companies
Engaging external experts can be an effective way to improve efficiency, particularly in a highly technical domain. A range of specialized providers can assist organizations in implementing effective security awareness training programs.
Adaptive Security offers a comprehensive suite of training tools. The platform uses AI to simulate deepfake attacks, vishing, smishing, and email phishing, helping employees remain aware of the threats they may encounter. It also provides personalized learning paths and a full library of training frameworks.
Tools like KnowBe4, Hoxhunt, Proofpoint, and others can also help. Look into all of them to find the best fit.
For organizations seeking a security awareness platform that addresses both current and emerging threats, we invite you to explore our Adaptive Security demo.
What Is Cybersecurity Awareness Training Maturity, And How To Measure It?
Cybersecurity awareness maturity is a framework for measuring how effectively an organization's training program reduces human risk. It extends beyond basic indicators to assess employee behavior, organizational culture, and risk management practices.
First, there is no definitive mathematical formula for determining an organization's cybersecurity awareness maturity level.
For example, conducting three training sessions per quarter, along with monthly microlearning lessons, does not automatically place an organization at an advanced level. While tracking these metrics is valuable and can help indicate progress, our experience suggests that cybersecurity awareness maturity is driven more by behavior and culture than by training volume alone.
If an organization does only the minimum required for compliance, it is likely to have a low level of cybersecurity awareness maturity. Conversely, an organization may maintain a high volume of training and remain immature if employee behavior does not change.
The following section outlines the four stages of maturity, with a focus on the most critical factor: employee behavior.
Security Awareness For Compliance Check
The first stage is a minimal, compliance-driven approach. The organization does only what is necessary to satisfy compliance requirements, and outside of those meetings and training sessions, cybersecurity is not a topic. Advancing to the next stage is relatively straightforward.
Developing a Cybersecurity Awareness Training Program
In the second stage, organizations begin to understand the critical importance of cybersecurity awareness. They start developing a program and initiating discussions about it. To progress further, they need to refine and optimize their program.
The organization must determine what is most effective and what keeps employees engaged and genuinely learning. It begins to monitor participation and behavioral metrics and gather feedback through ongoing conversations. Once these elements are in place, the next stage is within reach.
Established cybersecurity awareness training
The third stage reflects a well-established and effective program. Employees actively engage with it, discuss it, and demonstrate measurable improvement across key metrics. They understand the most common threats and know how to respond to them appropriately. At this stage, cybersecurity awareness has become meaningfully embedded in the organization.
However, progressing from good to great is often the most challenging stage and the most important objective.
Achieving this level requires time, sustained effort, and a highly engaging training program. People will see the results for themselves, and, when done well, the learning will only create the need to learn more.
Make training engaging, personalized, practical, and enjoyable to sustain employee interest in learning. Encourage group activities, healthy competition, and collaboration. Continually innovate to ensure the learning experience remains fresh and effective.
Cybersecurity awareness culture
The organization has successfully built a culture of cybersecurity awareness. Employees proactively report threats, support one another, and demonstrate an active interest in learning more about the topic. Cybersecurity has become an organization-wide conversation and an established part of day-to-day operations.
Employees discuss cybersecurity news and breaches, and are proactive in asking questions. While these behaviors may not always be evident, the key indicator is that cybersecurity remains an ongoing presence in the organization's day-to-day culture, rather than something discussed only during formal training.
Who Is Responsible For Creating A Security Awareness Program In A Company?
Responsibility in security awareness training varies with company size and complexity. For instance, in a small business, responsibility might fall on the CEO or the COO. In more organizationally mature companies, the CTO or even the Chief of Security might lead this project.
The next section indicates how each role handles this challenge.
Chief Information Security Officer (CISO)
For many organizations, the Chief Information Security Officer (CISO) serves as the key representative of the cybersecurity awareness initiative. While they may not handle the training sessions directly, their responsibilities include approving the overall strategy, ensuring alignment with organizational goals, and managing the budget. The program's ultimate success or failure largely depends on them.
Security Awareness Manager
This position is not necessarily a formal role. Regardless of the title, the individual will be responsible for developing, organizing, and delivering training sessions. This includes designing and hosting campaigns, simulations, and exercises, evaluating outcomes, and updating content accordingly.
This individual takes a more hands-on approach to training.
IT or Security team
As much as there is always a person primarily in charge, training is the responsibility of the entire IT or Security team. In most cases, that means providing support and technical expertise.
In practice, that means contributing new information to enrich the content and helping design attack simulations, which can be an engaging exercise.
HR, Legal, and Compliance
These teams must all participate, each for their own reasons. For example, HR should incorporate this into onboarding processes and, if applicable, offer support with engagement, communication, and rewards.
Legal and compliance teams ensure compliance with all regulatory requirements.
Executives and leadership
Executives and leadership play a vital role. They must actively participate not only to learn but also to demonstrate best practices and emphasize the importance of security awareness to all staff.
How Is Cybersecurity Awareness Training Done By Industry?
Most organizations encounter similar cybersecurity risks, including attacks targeting financial fraud, sensitive data theft, or ransomware. Nonetheless, certain industries face distinct cybersecurity challenges, primarily due to the data they handle or the operational sectors they serve.
- Financial services are especially vulnerable to fraud, ransomware, and related threats, given their direct link to a valuable asset: money.
- Healthcare institutions are also prime targets because of the personal medical and insurance information they hold.
- Technology companies face threats such as espionage, intellectual property theft, and ransomware attacks aimed at cloud infrastructure, which can significantly disrupt client operations.
- Hospitality companies that handle substantial third-party data, including hotel records, are at risk. Their extensive client and partner networks, spanning the globe, expand their attack surface.
- Sports broadcasters face heightened challenges due to the public and live nature of events, making them susceptible to cybersecurity threats that could disrupt major events.
- Educational platforms, traditionally designed to foster openness for research and collaboration, unfortunately, also provide fertile ground for scams and malicious activities.
- Government entities are often the focus of sophisticated cyberattacks related to warfare, espionage, or terrorism.
Regulations And Compliance For Cybersecurity Awareness Training
Several regulations and compliance standards identify awareness training as a key topic. These rules range from broad to industry-specific. This section highlights the most significant ones.
GDPR
The GDPR, or General Data Protection Regulation, is a comprehensive legal framework that governs the processing of personal data of individuals within the European Union. All organizations conducting business within Europe are required to adhere to these regulations.
HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) governs all healthcare entities and their affiliates within the United States. This federal legislation aims to safeguard patient information, ensuring privacy and security.
SOC 2 Type 2
Developed by the American Institute of Certified Public Accountants, the Service Organization Control Type 2 ensures that a company effectively manages client data securely.
PCI DSS
The Payment Card Industry Data Security Standard mandates specific security measures for organizations that store or process payment information, ensuring the protection of financial data.
SEC
While SEC rules do not explicitly mandate training, they recommend governance and risk management practices that typically involve training.
Alternatives To Complement Cybersecurity Awareness Training
There are multiple methods to enhance cybersecurity awareness training and develop a more comprehensive cybersecurity strategy. As previously noted, training is a key component of cybersecurity, but it is not the sole element.
Cybersecurity Awareness Training & Security Automation And Controls
Security automation and controls are tools that automatically detect security threats without any manual intervention. They are effective alternatives that can detect and automatically block many malicious actions in real time.
Another benefit is that they can diminish the cognitive load on both employees and the cybersecurity team. Solutions like endpoint protection software can use AI to detect phishing and anomalous user behavior.
However, they are always catching up to the latest scams and struggle to detect the most sophisticated and targeted threats.
Cybersecurity Awareness Training & Behavior Security Nudges
Behavioral security nudges are prompts used by various tools to encourage users to think more carefully before taking a specific action. Such alerts are common, for example, when a user clicks a suspicious link.
These tools can be useful for employees when they overlook something. However, they cannot substitute the comprehensive knowledge and mindset developed through proper training. Additionally, relying exclusively on them can be quite risky if they fail to identify certain issues.
Cybersecurity Awareness Training & Official Company Security Policy
Having an official company security policy is important. Similar to a company's core values, it serves as a guiding principle for all decisions. However, it can be risky to accept these policies at face value or to use them solely as an external symbol of cybersecurity awareness.
Training supports these policies by helping to implement them effectively and enhancing a company's digital security.
What Are The Benefits Of Cybersecurity Awareness Training?
The benefits of security awareness training extend beyond making a company more digitally secure. That alone is reason enough to do it, because it can prevent millions in losses, damage to the company's reputation, and data breaches, and improve governance and regulatory compliance.
However, some benefits go beyond that and are not immediately obvious.
Safely Establish Remote Work
Remote work has its advantages and disadvantages. Regardless of personal opinions on the matter, fostering a cybersecurity-awareness culture is essential to mitigate the risks associated with this work arrangement. Companies inherently have less oversight over employees working remotely, including their network security.
Regular training equips employees to enhance the company's overall cybersecurity posture while also strengthening the digital security of their personal and home environments.
Strengthen Customer Trust
A company that focuses on improving digital safety naturally gains more trust among its customer base.
It is encouraging to hear that the company focuses on training across social media and encourages employees to do the same.
The key is to strike the right balance between sharing successes and appearing overly self-congratulatory.
Improve Employee Digital Literacy
Learning about cybersecurity not only enhances immediate technical skills but also expands employees' overall digital literacy. This broader understanding can lead to more effective use of company tools, including cloud platforms, and may inspire them to explore additional tools and methods for acquiring knowledge.
Incentivize Cross-Team Collaboration
Teams often operate within their own silos. However, since everyone must undergo basic security awareness training, this presents an excellent opportunity to align the entire organization around a clear, common work objective.
Companies can set up classes and study groups, as well as create teams that compete with one another, to encourage cross-team interaction and gamify the process.
See The Benefits Of Cybersecurity Awareness Training With One Of Our Customer Success Stories
Adaptive Security has an extensive history of customer success stories demonstrating the importance of cybersecurity awareness training.
NerdWallet exemplifies how this training not only enhances security but also fosters a robust cybersecurity culture throughout the organization.
Read the NerdWallet success story to learn more.
The Cybersecurity Awareness Solution Landscape
There are several tools to help a company develop the best possible security awareness training program. Below are some of the best tools on the market.
Here are some of the best cybersecurity awareness training platforms available on the market.
Adaptive Security
Adaptive Security emphasizes AI-driven attack simulations, utilizing data and user behavior to tailor training in real time for optimal effectiveness.
The platform offers various simulations, including advanced deepfake attack scenarios. Additional options include KnowBe4, Proofpoint, Hoxhunt, Ninjio, and other leading solutions.
What Should I Evaluate When Looking For An Effective Cybersecurity Awareness Training Tool?
First of all, it is important to have a clear idea of what a company wants when looking for a vendor. Most companies look for training for the following reasons:
- Provide training for newer and emerging threats.
- Establish a security culture.
- Meet compliance requirements;
- Reduce risk amongst the most common threats.
In most buying journeys, companies aim to find a solution that checks all of the boxes above. However, it is important to identify the top priority: not only to guide the search, but also to support decision-making in the case of a tie.
Phishing Simulation Quality And Depth
According to the Verizon Data Breach Investigation Report, phishing was present in 15% of all breaches analyzed, with nearly 30% using it as an initial access vector.
Phishing simulations are a must.
When assessing simulation capabilities, prioritize realism, accurate attack simulation, personalization, customization, multi-channel testing, and feedback quality.
Most vendors provide demos, tours, or videos; make sure to utilize these resources to identify the most comprehensive phishing simulation option.
For more information, refer to our phishing training guide for a deeper understanding of how criminals use these tactics and how to stop them.
Format And Content Distribution
Next, focus on content deliverability. How is the training delivered to users? As outlined above, there are many ways to deliver information, including short videos, microlearning, simulations, and more. Organizations should review these formats to determine which is the best fit.
For instance, if the goal is to keep the content fresh and top of mind, a microlearning-focused solution may be the best option. If the goal is to provide more extensive training, a more comprehensive tool may be more appropriate.
Engagement And Feedback
A company may find an excellent training solution, but it will have limited value if employees do not engage with it. It is therefore important to evaluate the platform's usability: Does it incorporate gamification? Is the feedback clear? How effectively does it track progress?
Another important consideration is customization and personalization, including not only the ability to tailor content but also to adapt learning paths. Because people learn in different ways, providing the most effective path for each individual can help ensure that everyone learns in the way that works best for them.
Library Coverage
When training a team, it is important to cover as much ground as possible. Phishing is one key area, but the threat landscape extends well beyond it. Business email compromise, deepfakes, SMS-based attacks, AI-driven phishing attacks, and voice phishing are also commonly used by cybercriminals.
Seeking the most comprehensive tool not only guarantees employees are thoroughly trained but also maximizes the return on investment.
Implementation And Technical Support
It is also important to evaluate the other side of the user experience: implementation and technical support. For organizations using this guide, this will likely be a key area of focus. How easy is it to create, distribute, and update training? Are integrations available? How is the technical support?
The best way to assess this is to speak with vendors or review the content they have published. The goal is to ensure that they are knowledgeable, credible cybersecurity experts and trusted partners. Also, fully test any security awareness training demo to understand its features.
Customer Reviews And User Cases
Do not take a vendor's word for it; read as many comments, reviews, and case studies as possible. Companies are often eager to share their success stories, and those stories can provide real value.
However, it is also worth going a step further. Forums such as Reddit can help reveal what other users are saying about the brand. AI-powered search tools can also help sort through large amounts of information more efficiently.
Pricing
Pricing is always a delicate matter, but there is a correct way to think about it. Pricing is not about the cheapest or the most expensive, but about the one that best fits a company's budget.
If the price range is far beyond the budget, there may be little that can be done unless additional funds become available. However, if a solution falls within the budget, that does not automatically make it the right choice. The goal is to find the best solution.
Proof Of Concept
After reviewing these factors, organizations should be able to narrow the selection down to two or three vendors. The most effective way to determine which solution best suits the company is to run a proof of concept for each.
Use the tools for two to three months, with a select group of employees from the organization involved in each implementation. Depending on the company's size, the number of users per option can range from several dozen to several hundred.
After that, the final decision should be guided by data and user sentiment. Organizations should review the key metrics outlined above and gather feedback from the people using the platform. After a few months, the combined information around each platform should make the decision much clearer.
Most Common Challenges In Cybersecurity Awareness Training (And How To Deal With Them)
Lack of leadership buy-in in security awareness training
Leadership buy-in is essential to this process, not only for budgetary reasons, but also because leadership sentiment is likely to influence the rest of the organization. If leadership does not view the initiative as important, employees are unlikely to, either. The question, then, is how to secure that buy-in.
Begin by examining some of the primary reasons why they may lack engagement:
- Leadership might perceive time spent on training as counterproductive, believing it could hinder the company's overall productivity. For each minute an employee dedicates to training, they are not performing their immediate work responsibilities.
- Additionally, some may not view cybercrime as a threat, either due to a lack of knowledge or optimistic assumptions.
- Regarding costs, it is often less of a barrier than initially perceived. When the training is deemed relevant, organizations generally do not object to paying for it.
Now, how to address these objections?
- Point out the worst outcomes of a cyberattack: the financial and reputational damage. Usually, these concerns are sufficient to capture their attention. Using an attack as an example enhances the impact, especially if it's relevant to their industry. If the example comes from a competitor, it heightens their concern: suddenly, they realize, "We could be next."
- The team responsible for the initiative will often have the best understanding of how to communicate effectively with leadership, but it is crucial to use language that will resonate. In general, the message should be simple, direct, and relatable.
- Present the risk of human error without placing blame on employees. Emphasize how easily individuals can be compromised if they are not careful, and how employees within the organization may become targets. Where appropriate, incorporating a relatable example or case study can help illustrate how such incidents can occur in the workplace.
Employee Engagement In Cybersecurity Awareness Training
One of the most significant errors in cybersecurity awareness training is making it mandatory, such as restricting access until completion. While this might ensure participation, it does not necessarily enforce learning. To genuinely engage employees, the approach should be thoughtful and strategic.
The key principles are to make the training enjoyable, straightforward, and engaging.
First, simplicity is crucial. Ensure the interface is user-friendly and provides a positive experience. Employees should not struggle with the training platform.
Personalization can be highly effective. Customizable security awareness programs enhance the learning process by making it more relevant and relatable. Employees relate to threats they might encounter and challenges that impact their daily responsibilities.
Role-based training is also exceptionally valuable. It demonstrates how individuals in specific roles may face particular risks, emphasizing relevance.
Finally, maintain a positive tone. Avoid making training feel burdensome; allocate sufficient time to complete it. Use lighthearted elements, such as gamification or team competitions, to increase motivation. There are several options, but the primary goal is to motivate the team to participate and learn willingly.
Security Awareness Training Fatigue
In the long term, this could present a challenge. While the primary objective is to deliver ongoing cybersecurity awareness training, it may become monotonous if employees are repeatedly exposed to the same content. How to address this issue?
Maintaining content freshness is essential, and AI-powered cybersecurity awareness training tools play a significant role in this. AI can assist in generating new material and ensuring it remains engaging and current.
Additionally, monitoring recent news for data breaches or cyberattacks helps keep the training relevant and topical.
How Adaptive Security Approaches Awareness Training
Our approach to awareness training emphasizes interactivity, customization, and role-based simulation. We believe that developing content around these three pillars enhances the experience, making it more engaging and facilitating deeper learning.
Security Awareness Training with Adaptive Security
For security awareness training, we develop interactive modules with scenario-based exercises to enhance practical skills and help employees manage AI-driven threats.
Since an AI threat requires an AI-based response, our approach includes training with realistic multi-channel simulations powered by AI and OSINT. This not only raises awareness of such threats but also equips employees with the knowledge to recognize and, if necessary, address them effectively.
Feel free to compare Adaptive to other tools to see for yourself.
Cybersecurity Awareness Training After Adaptive Security
There are two primary pieces of feedback we consistently receive from clients regarding cyber awareness training.
First, they highlight how deepfakes and AI have transformed employee perceptions of social engineering. Nothing makes this clearer than witnessing a video of their own CEO being used in a deepfake training.
Second, they note the high level of employee engagement in security training, largely driven by its customization and personalization. This is the expected outcome when using Adaptive: employees will not only learn but also want to learn, fostering a positive shift in security culture.
We invite you to visit the Adaptive Security case studies page to see for yourself.
Get Started On A Security Awareness Training Program Today (Checklist)
By following this comprehensive cybersecurity awareness training guide, a company can develop a team of highly trained, security-conscious employees who act as a "human firewall".
Keep in mind that cybercriminals often target both individuals and systems. Implementing cybersecurity awareness training is the most effective approach to transforming potential vulnerabilities into a strong line of defense.
Below is a comprehensive checklist of the topics covered in this guide to assist in a new program launch. Additionally, explore the Adaptive Security demo to begin developing a personalized training program.
Cybersecurity Awareness Training Checklist
- Decide who is the person responsible for creating and conducting training
- Assess the company's threat level and attack surface area
- Figure out the awareness training maturity level
- Get leadership buy-in, not only for the budget, but for participation
- Learn who the most at-risk people are in the company, according to role
- Pick the format(s) to use in training
- List the main topics to cover
- Check for regulations and frameworks, especially if there are some specific to the industry (like healthcare)
- Establish a clear channel of communication that goes both ways
- Look into the best cybersecurity awareness training tools available
- Measure the effectiveness of the training
- Plan to keep content fresh and consistent to foster a culture of cybersecurity awareness.
Frequently Asked Questions
What Is Security Awareness Training?
Security awareness training means educating employees on cybercrime threats that they might be exposed to or targeted by. The goal is to develop a structured program that teaches them to be aware of, recognize, report, and remediate the most common vectors cybercriminals use.
Why Is Cybersecurity Awareness Training Important For My Company?
Cybersecurity awareness training is important because it directly addresses one of the most common entry points for cyberattacks: the people. Cybercriminals target employees with phishing, social engineering, credential theft, and many more, focusing as much on human vulnerabilities as on technical ones.
How Does Cybersecurity Awareness Training Work?
Cybersecurity awareness training works through a combination of methods and resources to make employees as capable as possible of recognizing, identifying, avoiding, and reporting cybersecurity threats. Those resources might include lessons, simulations, exercises, quizzes, tests, and more.
How Long Should A Cybersecurity Awareness Training Be?
Cybersecurity awareness training is a continuous process. Individual training sessions can range from longer exercises and simulations that take up to an hour to shorter exercises lasting up to 10 minutes, interspersed to help retain information. The ideal training program combines resources of different lengths to deliver information reliably and effectively.
What Are The Main Types Of Cybersecurity Awareness Training?
The most commonly used cybersecurity awareness training methods are:
- Online cybersecurity awareness training classes or courses
- Microlearning lessons
- Newsletters and awareness campaigns
- Instructor-led training
- Phishing & threats simulations
- Role-based training
- AI-based training
Combining these resources helps companies create a more complete and effective training program.
What Is Cyber Hygiene?
Cyber hygiene is the practice of maintaining a clean, healthy, and safe digital environment for people, companies, and organizations. These include several best practices and sound security habits.
The goal is to prevent damage, including data leaks, fraud, identity and credential theft, and other cyberattacks.
The term "hygiene" refers to general personal hygiene, conveying the idea of simple habits anyone can adopt that can make a big difference.
How Does Cybersecurity Awareness Training Compare To Other Cybersecurity Practices?
Cybersecurity awareness training does not replace other cybersecurity practices. Cybercriminals exploit human weaknesses as much as they do technical ones, and both require adequate protection. By combining the strengths of each, a company can achieve a truly safe digital environment.
What Are The Tools Used For Cybersecurity Awareness Training?
Here are some examples of cybersecurity awareness training tools that are widely used:
- Adaptive Security
- KnowBe4
- Proofpoint
- Hoxhunt
- Ninjio
A successful program combines these dedicated tools with other options, such as video, campaigns, newsletters, and simulation tools.
The goal is to deliver a comprehensive approach using easy-to-deliver, easy-to-consume content.
How Much Does A Cybersecurity Awareness Training Solution Typically Cost?
A cybersecurity awareness training platform might cost within the following range:
Basic features: $1-$10 per user per year.
Medium features: $10-$20 per user per year.
Premium features: +$20 per user per year.
Costs and pricing models can vary by provider, though most companies offer base pricing with the possibility of custom quotes.
Payment options are usually available on a monthly, semester, or yearly basis, with the yearly option discounted. Companies also offer tiers, from basic to premium, with different features available at each tier.
How Do I Get Started With Cybersecurity Awareness Training?
Here are some quick tips on how to get started on cybersecurity awareness training:
- Assess the company's threat level and attack surface area
- Learn the most at-risk people in the company, according to role
- Pick the format(s) to use in training
- List the main topics to cover
- Check for regulations and frameworks, especially if there are some specific to the industry (like healthcare)
- Look into the best cybersecurity awareness training tools available
- Measure the effectiveness of the training
- Keep content fresh and consistent to create a culture of cybersecurity awareness
What Are The Biggest Mistakes To Avoid In Cybersecurity Awareness Training?
Here are some common mistakes:
- Not taking training seriously
- Relying on a single annual, generic training exercise
- Not taking advantage of the best technology, like AI, deepfakes, and real-world simulations
- Measuring and caring only about participation, not behavior change
- Not developing a nurturing culture around the topic
- Failing to gather leadership and employee engagement
- Letting content grow stale and outdated
Is Cybersecurity Awareness Training Mandatory?
Yes, in some cases. While there are no universal mandatory obligations for security awareness training, some companies may be required to provide it for compliance and regulation purposes, depending on the industry in which they operate.
How Often Should I Offer Cybersecurity Training To My Employees?
There is no ideal frequency for offering cybersecurity awareness training to employees. However, many companies use the format of one large formal training session per year, with exercises and microlearning lessons interspersed to keep content fresh and top of mind.
What Should I Consider While Looking For A Cybersecurity Training Provider?
Here is a quick list of what to look for in a potential cybersecurity training provider:
- Phishing simulation quality and depth
- Format and content distribution
- Tools to incentivize engagement and feedback
- Library coverage
- Implementation and technical support
- Customer reviews and user cases
- Pricing
Before checking for those characteristics, list exactly what the company is looking for, and filter for companies that can deliver it.
Who Should Receive Cybersecurity Awareness Training?
Every person in a company should receive at least basic cybersecurity awareness training.
However, some people might need enhanced training based on their role, as they may naturally be at higher risk. This is known as role-based training. A simple example is the executives.
Is It Worth Doing Personalized Cybersecurity Awareness Training?
Personalized or customizable awareness training offers many benefits. It can make training more fun, relatable, and engaging for users, leading to better performance across the board. However, it can also be more expensive and more complex to develop and maintain. Tools like AI help with those downsides.
What Skills Are Needed For Cybersecurity Awareness Training?
Undertaking cybersecurity awareness training requires no prior skills. For those developing training programs, it's important to have some technical and communication knowledge, as well as some behavioral expertise.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents