Role-Based Security Awareness Training Program: The Complete Guide to Building, Deploying, and Measuring Human Risk Reduction
A role-based security awareness training program assigns security education according to each employee's job function, access level, and actual threat exposure. This guide examines:
- How to identify which roles have the greatest attack surface
- How to build a program that produces measurable behavioral change
- How to satisfy role-differentiated training requirements under HIPAA, PCI DSS, GDPR, and CMMC
- How AI-powered spear phishing, deepfake impersonation, and vishing attacks are reshaping the knowledge requirements for each role
Applying uniform training content to all employees ignores the reality that risk is not evenly distributed. A finance director with wire transfer authority, a developer with production access, and a front desk coordinator face fundamentally different threat landscapes that generic training cannot adequately prepare them for. Security leaders who apply role-based principles will have a program architecture they can build, deploy, and defend to the board.
Companies seeking a platform that can automatically generate role-based security awareness training are encouraged to explore an Adaptive Security demo.
What Is a Role-Based Security Awareness Training Program?
A role-based security awareness training program is a structured approach that assigns security education based on an employee's job function, system access level, and corresponding threat exposure, rather than delivering identical content to every individual in the organization.
Where generic annual training treats a CFO and a warehouse worker as equivalent security risks, a role-based program maps curriculum to each role's actual attack surface.

Role-Based Security Awareness Training vs. Generic Security Awareness Training
Generic security awareness training (SAT) is built around the lowest common denominator, delivering a single curriculum organization-wide, once a year, regardless of the specific threats each employee faces. Conversely, role-based programs address this gap by measuring threat exposure based on job responsibilities rather than headcount.
For instance, a finance director processing wire transfers is more exposed to business email compromise (BEC) and deepfake CFO impersonation as live attack vectors, while a developer faces credential phishing and supply chain compromise.
Role-based training does not preclude exposure to other threat types; a developer, for instance, may also encounter business email compromise. The objective is to prioritize content delivery according to the threats employees are most likely to face.
The Two Tracks Every Mature Program Runs
NIST SP 1288 confirms that most mature federal organizations are required to conduct role-based cybersecurity training for personnel assigned roles that carry security and privacy responsibilities. This standard is one that private-sector programs increasingly mirror.
Most mature programs now operate two tracks simultaneously: compliance-driven training mandated for specific roles by frameworks such as HIPAA, PCI-DSS, FISMA, or GDPR, and risk-driven training targeted at roles demonstrating the greatest behavioral vulnerability based on simulation data, open-source intelligence (OSINT) exposure, and incident history.
Compliance-driven role-based training fulfills regulatory mandates by tying specific training requirements to job functions:
- HIPAA requires privacy and security training for all personnel handling protected health information
- PCI-DSS mandates security awareness training for all personnel with access to cardholder data
- FISMA requires agencies to train personnel with significant information security responsibilities at a depth well beyond general awareness
Risk-driven role-based training goes further by using simulation results, OSINT profiling, and incident data to identify which roles exhibit the highest behavioral vulnerability at any given time.
A finance team member who clicked a spear phishing link in the previous quarter receives escalated training on invoice fraud rather than the same module completed by a marketing colleague.
Security awareness training built on this model treats the curriculum as dynamic rather than static, adjusting as threat patterns shift and employee risk scores change.
Why Generic Security Training Fails and Role-Based Training Works
A role-based security awareness training program exists because generic training fails to address the specific threats each employee faces, yet most organizations still deploy one-size-fits-all annual modules that bear no relationship to how attackers target a finance analyst versus a systems administrator.
That misalignment between training content and actual threat exposure is where breaches originate, as human risk within organizations is not evenly distributed. A small percentage of employees, typically in high-access roles such as finance, IT, and executive administration, generate a disproportionate share of security incidents.
Lance Spitzner, Director of Security Awareness at the SANS Institute, argues that the most effective security awareness programs treat training as a behavioral science problem, not a compliance checkbox. Content must be relevant to what each person actually does and the threats they personally face.
According to the Verizon 2025 Data Breach Investigations Report, 60% of breaches involve a human element, with the average cost of a breach at $4.4 million. This means creating meaningful content is essential to maintaining organizational security while ensuring the effective use of resources.
Who Needs Role-Based Security Awareness Training?
A role-based security awareness training program recognizes that a generic curriculum leaves the most targeted groups significantly underprepared, as adversaries study organizational charts before executing an attack. Therefore, security training programs must be structured accordingly.
High-Risk Role-Based Security Awareness Training
Executives and senior leaders are primary targets for:
- Business email compromise (BEC)
- Deepfake video impersonation
- AI voice cloning
- Spear-phishing campaigns that exploit their authority to circumvent standard verification procedures
Training for this group must extend beyond threat recognition to encompass cybersecurity governance responsibilities and decision-making frameworks that remain effective under social engineering pressure, including live simulations that replicate the urgency and realism of actual deepfake video calls.
Finance and accounting teams constitute the operational execution layer that adversaries require to execute wire and invoice fraud schemes, as they manage daily payment approval workflows. They are frequent targets of vendor impersonation and fraudulent invoice requests designed to bypass finance controls.
BEC scenario training with embedded payment verification protocols that require out-of-band confirmation for any new or modified payment instruction directly addresses this exposure.
IT administrators represent a structurally distinct risk category, with privileged access to systems, credentials, and network infrastructure, making them high-value targets for credential theft, supply chain compromise, and insider threats.
Training for this group emphasizes developing personnel as human sensors, specifically by recognizing indicators of compromise in their own access patterns, identifying social engineering attempts that exploit their technical authority, and determining when an unusual request warrants escalation rather than compliance.
Mid-Level-Risk Role-Based Security Awareness Training
HR and recruiting teams manage sensitive employee data and routinely open unsolicited files from unknown senders. Adversaries exploit this workflow through fake résumé malware delivery and HRIS credential phishing.
Legal and compliance teams access confidential contracts and merger-and-acquisition data, making them targets for attorney impersonation and document-request phishing aimed at extracting privileged information prior to deal closure.
Research and development teams possess source code and intellectual property of direct competitive value. This group is specifically targeted through industrial espionage, including spear phishing and credential stuffing, with adversaries seeking access to repositories or proprietary designs.
Customer service and support staff face vishing and smishing attacks that exploit their training to resolve issues promptly and their trust in the individuals they assist. Adversaries deliberately weaponize this behavioral tendency.
How Do Tenure and Cross-Functional Roles Affect Training Design?
New hires exhibit elevated click rates during onboarding windows because they are still developing familiarity with internal processes, communication norms, and the indicators of unusual requests. This makes the first 90 days a concentrated period of elevated human risk.
Long-tenured employees present a distinct challenge, as familiarity with routine workflows produces complacency, leading them to approve requests automatically that a less habituated employee might scrutinize.
Employees with cross-functional responsibilities should receive training mapped to the highest-risk function they perform. A finance manager who also administers HR systems represents a dual-vector target and should be trained accordingly.
Lastly, a foundational layer of competencies applies across all roles regardless of seniority, covering broader topics such as:
- Phishing recognition
- Password hygiene
- Multi-factor authentication (MFA)
- Device security
- Incident reporting
These are non-negotiable baseline competencies that every employee must demonstrate before role-specific content is introduced. A security awareness training platform that leverages role and behavioral data to automatically assign training closes this gap without requiring security teams to make manual enrollment decisions.
Identifying which roles carry the greatest exposure is the prerequisite. Understanding why generic training fails to address those exposures is where most programs lose ground.
How to Build a Role-Based Security Awareness Training Program
Building a role-based security awareness training program requires eight structured steps:
- Conduct a human risk assessment
- Map threats to roles
- Segment the workforce into training tracks
- Define content requirements per track
- Assign subject matter experts
- Select delivery formats by role
- Integrate with HR systems and LMS
- Secure leadership buy-in and define accountability
Omitting the risk assessment phase produces a curriculum that targets the wrong roles with the wrong threats. Organizations operating in hybrid or remote environments must ensure that every step accounts for the collaboration tools and personal device contexts employees use daily, as third-party platforms introduce attack vectors that office-centric programs consistently fail to address.
How to Build a Role-Based Security Awareness Training Program Step 1: Conduct a Human Risk Assessment
Risk assessment is the foundation of the entire program, as without it, training resources are directed toward employees who need them least and away from those who generate the most incidents.
Simulation failure rates, open-source intelligence (OSINT) profiling results, credential breach history, and access privilege maps should be consolidated to identify which departments carry disproportionate threat exposure.
How to Build a Role-Based Security Awareness Training Program Step 2: Map Threats to Roles
Generic threat inventories enumerate attack types in the abstract while role threat mapping connects each attack type to the specific workflows and access rights of a given department.
The goal is to make every training scenario feel operationally real; the threats should mirror what each role genuinely encounters in their day-to-day workflow. This alignment dramatically improves both engagement and retention, because people learn faster when the risk feels personal and immediate rather than theoretical.

How to Build a Role-Based Security Awareness Training Program Step 3: Segment the Workforce Into Training Tracks
Employees should be divided into training tracks based on role, department, access tier, and risk score. Contractors and third-party vendors require scoped training that addresses their specific access permissions without exposing internal program architecture, simulation calendars, or security control details.
Treating contractors identically to full-time employees presents both security and compliance risks. Regulatory frameworks, including HIPAA and PCI DSS, distinguish between obligations applicable to internal personnel and those applicable to third-party personnel.
How to Build a Role-Based Security Awareness Training Program Step 4: Define Content Requirements per Track
Every employee requires foundational content covering phishing recognition, password hygiene, and incident reporting.
Beyond that baseline, content requirements diverge significantly. Security teams should cross-reference information from the three previous steps, adapting training tracks to each role and its associated threats, as well as to individual human risk assessments that identify the highest-risk employees.
Compliance frameworks, including NIST CSF, SOC 2, and HIPAA, should be used to validate mandatory content for regulated roles and ensure no required topic is absent from an auditable training track.
How to Build a Role-Based Security Awareness Training Program Step 5: Assign Subject Matter Experts
Scenario realism deteriorates when security teams develop role-specific content in isolation. Subject matter experts (SMEs) from finance, legal, IT, and executive leadership should be engaged to review and validate scenarios prior to deployment.
A finance SME can immediately determine whether a simulated invoice-fraud scenario aligns with actual approval workflows. When scenarios fail to align with real workflows, employees dismiss them as unrealistic, and the training fails to produce behavioral change.
SME validation closes the gap between security teams' assumptions about role functions and the threats those roles encounter in practice.
Internal subject-matter expertise, while essential for validation, is inherently constrained by the boundaries of an organization's environment. Security teams can only draw on the threats and incidents they have directly encountered.
Platform and security awareness training providers address this limitation by contributing threat intelligence aggregated from thousands of organizations across multiple industries.
These vendors monitor the evolution of phishing campaigns, business email compromise, and social engineering tactics as they emerge, translating that intelligence into scenario libraries that reflect current attacker behavior.
Partnering with such providers enables security teams to evaluate their scenarios not only against internal workflows but against the techniques actively employed by cybercriminals, ensuring that training programs remain relevant as the threat landscape continues to shift.
How to Build a Role-Based Security Awareness Training Program Step 6: Select Delivery Formats by Role
Executives prefer concise briefings and simulation exercises to extended e-learning modules, while technical staff respond more effectively to hands-on simulations and capture-the-flag-style challenges. Frontline employees show the highest engagement with microlearning that is triggered immediately after a simulated phishing failure.
Aligning format to role is not a matter of preference, as misaligned delivery produces completion without retention, yielding no measurable reduction in risk.
How to Build a Role-Based Security Awareness Training Program Step 7: Integrate With HR Systems and LMS
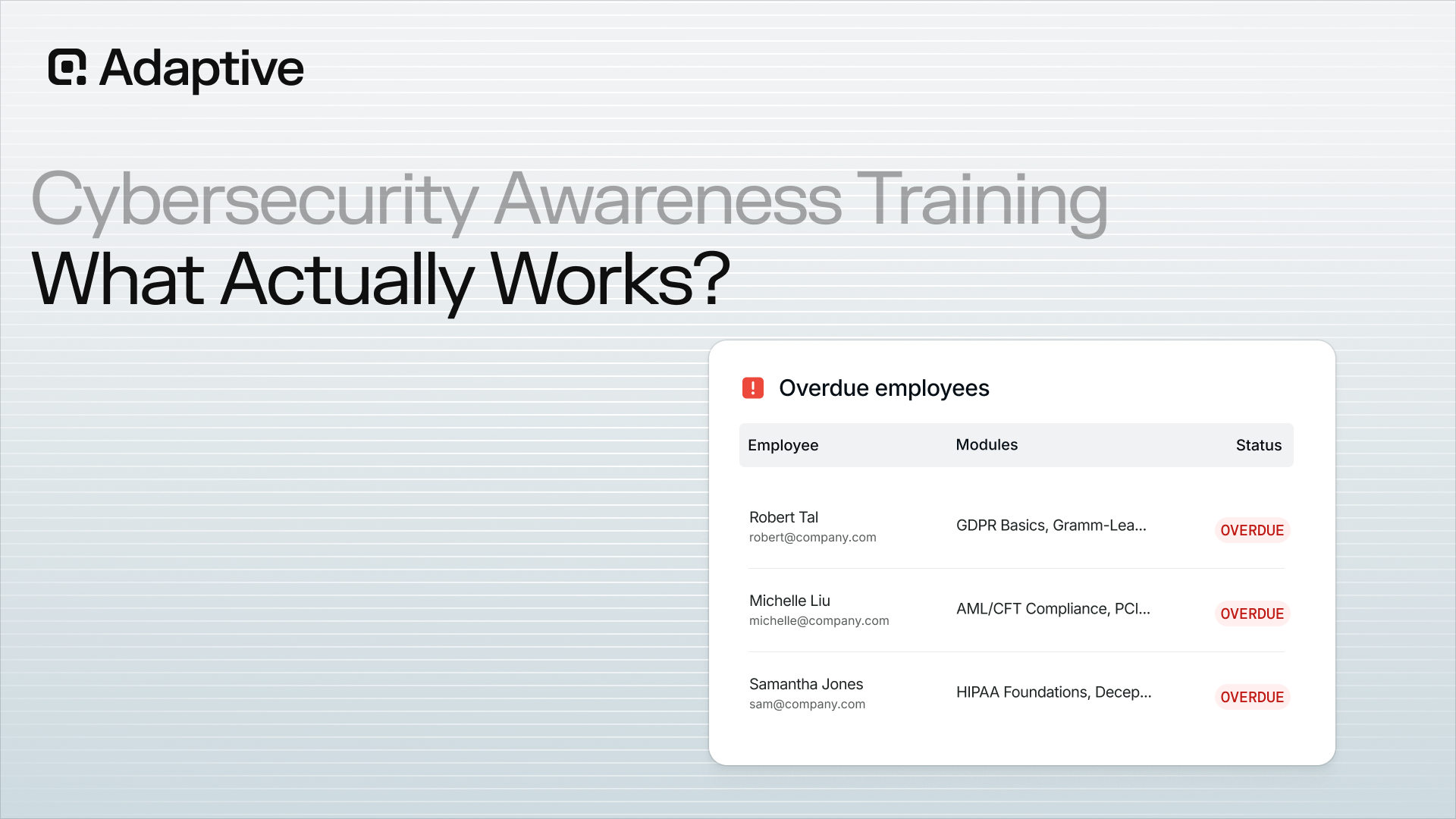
Connecting training track assignments to HRIS and identity management systems ensures that enrollment updates automatically when employees change roles, are onboarded, or are offboarded.
An employee transitioning from a low-privilege customer success role into a finance position should automatically inherit the higher-risk training track, without requiring a manual ticket. Static CSV uploads disrupt this continuity and introduce compliance gaps that surface during audits.

How to Build a Role-Based Security Awareness Training Program Step 8: Secure Leadership Buy-In and Define Accountability
CISOs require executive sponsorship to enforce completion across business units that treat security training as a productivity cost. The business case should be built using breach-cost data and risk quantification that is directly tied to the organization's own simulation failure rates and OSINT exposure.
Accountability ownership must be defined explicitly, identifying whether enforcement authority resides with the CISO, CIO, or individual business unit managers, and documenting that assignment accordingly.
Without named owners, completion rates stall, high-risk employees remain untrained, and the program produces reporting artifacts rather than behavioral change.
Organizations seeking a security awareness training platform that delivers simulations across multiple roles and offers full customization based on individual performance and learning pace are encouraged to explore the Adaptive Security demo.
Role-Based Security Awareness Training Program KPIs
Measuring a role-based security awareness training program means tracking metrics relevant to board-level reporting, which are behavioral in nature, encompassing:
- Susceptibility trends by role
- Speed of threat reporting
- Risk score trajectory
- Credential exposure reduction
Measure Behavioral Signals in the Role-Based Security Awareness Training Program
Training completion rates indicate how many employees viewed a module, providing no insight into whether those employees would successfully identify and resist a sophisticated targeted attack.
The behavioral metrics that carry meaningful signals include:
- Simulation failure and improvement rates by role over time
- Phishing report rates
- Mean time to report a suspicious message
- Repeat simulation failure rates by individual and department
- Credential-breach exposure reduction is tracked via open-source intelligence (OSINT) monitoring.
Phishing report rate warrants particular emphasis, as it measures active vigilance rather than susceptibility alone.
Hypothetically, a finance team that reports 70% of simulated spear phishing attempts within minutes is materially more resilient than one that merely avoids clicking, as the former accelerates incident response while the latter addresses only one attack vector.
Mean time to report complements this metric by revealing how quickly a threat escalates from exposure to triage, directly compressing the window available for lateral movement.
Create Board-Ready Role-Based Security Awareness Training Program Reports
The risk score trajectory, tracked at both the departmental and individual levels, is the most reliable proxy available to a CISO for quantifying reductions in business risk.
A department whose aggregate human risk score declined 40% over two quarters, driven by improved simulation performance, faster incident reporting, and reduced credential breach exposure, reflects a directly measurable reduction in the probability of a costly security incident.
Positive reinforcement accelerates risk score improvement, as punitive responses to simulation failures suppress reporting behavior and reduce long-term engagement. Recognition of correct actions, such as reporting a simulated phishing attempt or flagging a suspicious voice call, builds the habit loops that sustain vigilance over time.

Role-specific scenarios should be updated at a minimum annually, or following any significant change to the threat environment or organizational structure. Training that reflects outdated attack patterns while adversaries have advanced to deepfake vishing creates a dangerous illusion of preparedness.
Compliance Frameworks That Require Role-Based Security Training
A role-based security awareness training program is not simply a best practice. For most regulated industries, it represents a documented legal or contractual obligation. The distinction between a compliance-driven and a risk-driven approach is narrower than it appears: one satisfies auditors; the other reduces the probability of a breach.
A compliance-only program trains for the minimum roles specified by the regulation, while a risk-driven program uses that regulatory baseline as a floor and then layers behavioral simulation and real-world threat context on top of it.
Which Frameworks Explicitly Mandate Role-Differentiated Training?
The major regulatory frameworks each define specific roles and corresponding training obligations:
- HIPAA: The HIPAA Security Rule requires workforce training appropriate to each member's function and their level of access to protected health information (PHI). Privacy officers, clinical staff, billing teams, and IT administrators carry distinct obligations. A nurse accessing patient records and a billing coder reviewing claims face entirely different threat surfaces, and training must reflect that distinction.
- PCI-DSS: PCI-DSS v4.0.1 requires security awareness training for all personnel with access to cardholder data environments, with elevated requirements for system administrators and developers who can modify system configurations
- GDPR: Staff who process personal data must receive training commensurate with their data-handling responsibilities. A data protection officer carries obligations that a customer service representative does not
- FISMA / NIST SP 800-53: Control AT-3 explicitly requires organizations to provide role-based training before personnel are authorized to access systems, and at defined intervals thereafter. A 2023 NIST study on federal role-based training (SP 1288) found that inconsistency in how agencies define role categories was the primary gap undermining compliance. Agencies used divergent taxonomies, making cross-agency benchmarking and gap remediation nearly impossible
- ISO 27001: Annex A requires awareness appropriate to roles and responsibilities within the information security management system. A cloud infrastructure engineer and a marketing coordinator do not share the same control responsibilities.
- CMMC Level 1 and Level 2: Department of Defense supply chain contractors must demonstrate training appropriate to their access level. Level 2 adds requirements for personnel handling Controlled Unclassified Information (CUI)
- SOC 2: Auditors assess whether training programs address the specific risks relevant to personnel with access to in-scope systems, making generic, one-size-fits-all programs difficult to defend during an audit.
Why Compliance Alone Is Not Enough
Regulatory frameworks define the minimum viable training obligation, not the optimal program. An organization that trains its billing team to comply with HIPAA but stops there leaves finance staff, executives, and engineers exposed to cyberattacks that no compliance checklist currently covers.
The most defensible posture treats each framework's role definitions as the structural backbone of a broader security awareness training program, supplemented by behavioral simulation, real-time risk scoring, and threat-specific content layered atop the regulatory baseline.
Satisfying auditors and reducing exposure can be achieved simultaneously. What most often separates organizations that accomplish both from those that accomplish neither is whether training content accurately reflects the threats each role faces in practice.
How AI-Powered Threats Are Reshaping Role-Based Training Requirements
Generative AI has fundamentally changed what a role-based security awareness training program must cover. Attackers now use open-source intelligence (OSINT) to craft personalized spear phishing emails that reference an employee's actual job title, recent projects, and reporting structure.
Details scraped from LinkedIn, company websites, and public filings render generic simulations structurally incapable of preparing employees for the attacks they will actually encounter.

What makes this threat landscape particularly difficult to defend against is that AI eliminates the bottleneck that once constrained attackers: time. Historically, crafting a convincing, context-aware spear phishing campaign required hours of manual research per target, a constraint that naturally limited attack volume.
Generative AI removes that ceiling entirely. Adversaries can now feed OSINT data into a model and produce hundreds of highly individualized, grammatically polished, contextually accurate lures in minutes.
The asymmetry this creates for defenders is severe: finance teams, engineers, and executive assistants each face attack vectors tailored specifically to their workflows, tools, and communication patterns, at an industrial scale. Effective role-based training must match that sophistication.
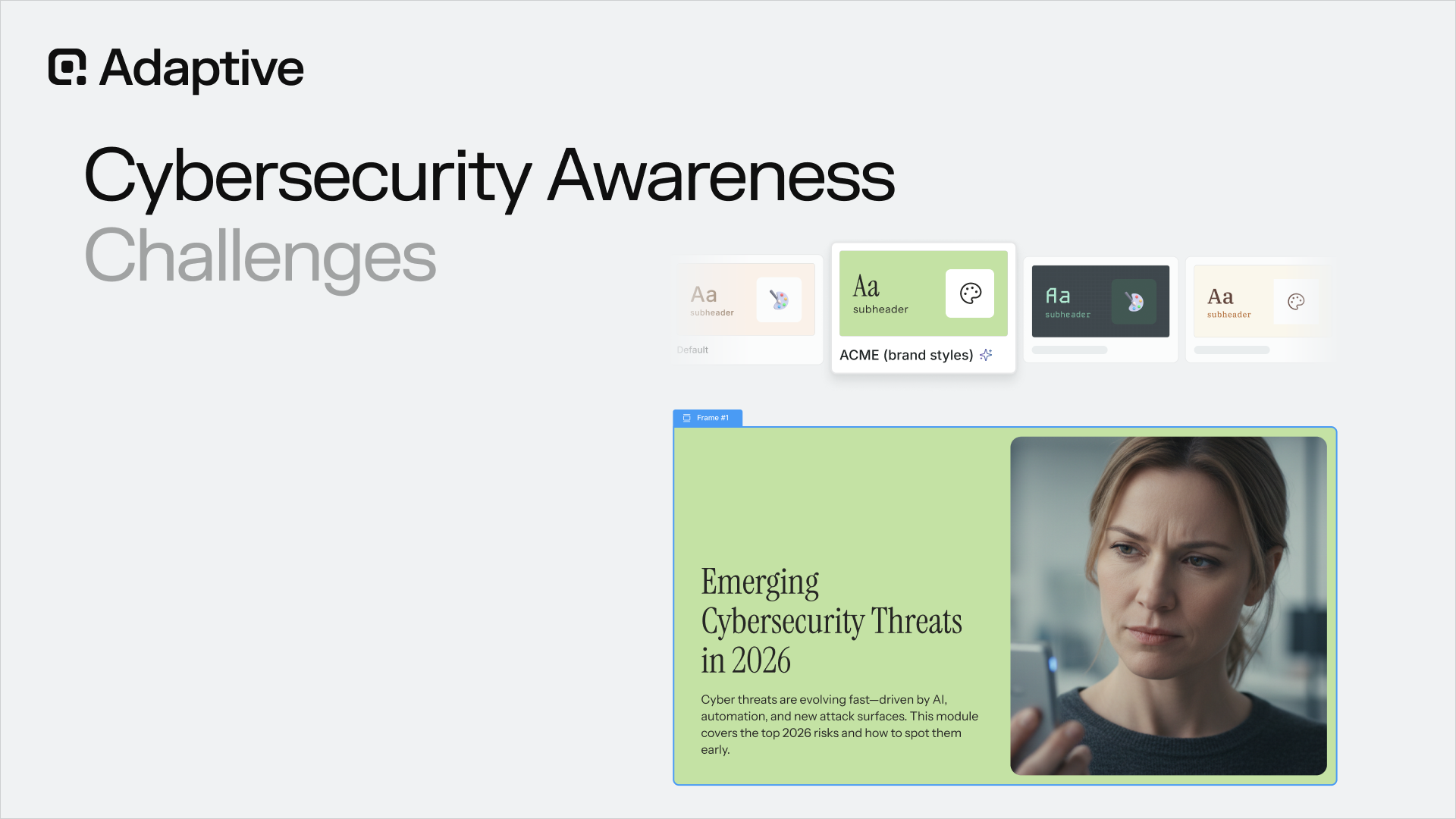
On the defensive side, AI-powered training platforms can apply the same logic in reverse, ingesting role-specific context to generate realistic, personalized simulations that reflect what a staff accountant or a cloud architect would actually receive in their inbox, without requiring security teams to manually author scenarios for every department.
The result is training coverage that scales across the entire organization while preserving the contextual fidelity that makes simulations genuinely predictive rather than performatively compliant.
Why Does OSINT Profiling at the Role Level Change Attack Surface Prioritization?
OSINT profiling assigns each employee a risk score based on 1,000+ data points, including their public social media footprint, dark web credential exposure, and visibility in the organizational chart.
Applied at the role level, this enables security teams to identify which departments represent the broadest attack surface before a threat materializes. That pre-materialization intelligence distinguishes reactive compliance training from a genuine risk-reduction program.
The operational result is enrollment automation. When an OSINT signal or a simulation failure is detected for a specific role segment, targeted training is triggered immediately, compressing the response window from months to hours.
Security programs operating this way stop measuring training as an activity and instead measure it as a risk-reduction mechanism. That shift in measurement changes what gets prioritized, what gets resourced, and ultimately what gets stopped.
Frequently Asked Questions About Role-Based Security Awareness Training
What Is a Role-Based Security Awareness Training Program?
A role-based security awareness training program delivers threat scenarios and learning content matched to each employee's specific job function, access level, and risk exposure. The following examples illustrate this approach:
- Finance teams practice detecting invoice fraud and business email compromise (BEC)
- IT staff work through scenarios involving credential theft and privilege escalation
- Executives run impersonation and deepfake drills
The result is training that reflects the actual attacks each employee is most likely to face.
How Is Role-Based Training Different From Generic Security Awareness Training?
Generic security awareness training treats a junior customer service representative and a CFO as identical risks, even though they are not. Role-based programs use job function, data access, and behavioral risk signals to route each employee into relevant scenarios.
Which Employee Roles Need the Most Targeted Training?
Finance and accounting teams face the highest exposure to BEC and invoice fraud. IT and system administrators are primary targets for credential theft and privilege escalation. Executives are targeted by deepfake impersonation and spear phishing attacks specifically because of their authority to approve transactions. Human resources staff are targeted for employee data and payroll fraud. Any role with elevated system access or financial authorization represents a priority risk segment.
Does Role-Based Training Satisfy Compliance Requirements Like HIPAA, PCI-DSS, and GDPR?
Role-based programs support compliance by mapping content to the specific control requirements of each framework. Healthcare organizations need training mapped to HIPAA workforce security standards. Payment processors need scenarios aligned with PCI DSS requirements. A well-designed security awareness training program produces auditable completion records and role-specific documentation that satisfies regulatory requirements. Generic completion logs typically do not meet the specificity required by those frameworks.
How to Measure Whether Role-Based Training Is Working?
The primary metrics are:
- Phishing simulation click rates by role
- Time-to-report for suspicious activity
- Individual risk score changes over time
A finance team that starts with a 30% simulation click rate and drops to under 8% after three months of targeted training has produced a measurable, defensible outcome. Completion percentages alone tell security leaders nothing about behavioral change.
What Is the Difference Between Role-Based Security Awareness Training and Standard Security Awareness Training?
Role-based security awareness training assigns a curriculum based on each employee's job function, access level, and specific threat exposure, while standard security awareness training delivers the same content to every employee regardless of role.
Standard training optimizes for completion rates; role-based training optimizes for behavioral change among the employees who carry the greatest risk. The structural difference is that role-based programs use simulation data, access privilege mapping, and OSINT profiling to assign targeted content, not just job titles.
Which Compliance Frameworks Require Role-Based Security Awareness Training?
Several major frameworks explicitly mandate or strongly imply role-differentiated training:
- HIPAA requires workforce training appropriate to each member's role and access to protected health information, with distinct obligations for clinical staff, billing teams, and privacy officers
- PCI-DSS requires security awareness training for all personnel with cardholder data environment access, with elevated requirements for system administrators
- FISMA and NIST SP 800-50 mandate role-based training mapped to job functions for federal agencies.
Additionally, ISO 27001, SOC 2, GDPR, and CMMC Level 2 each carry parallel obligations tied to the access and responsibilities of specific personnel.
How Often Should Role-Based Security Training Content Be Updated?
Role-specific training content should be reviewed and updated at least annually, with more frequent refreshes whenever the threat landscape shifts or the organization undergoes structural changes, such as new technology rollouts, acquisitions, or workforce restructuring.
High-risk roles, including executives, finance teams, and IT administrators, warrant quarterly scenario updates given the continuous refinement of attack tactics.
Stale simulations produce false confidence: an employee who passes a prior year's phishing test may be entirely unprepared for a current AI-personalized spear phishing variant. Content tied to regulatory compliance should also be reviewed whenever a framework issues updated guidance.
How to Identify Which Employee Roles Need the Most Targeted Security Training?
Identifying which roles require the most targeted training involves combining four data sources:
- Phishing simulation failure rates by department
- Privilege access mapping, identifying which roles hold administrative rights or financial approval authority
- OSINT exposure profiling, identifying which individuals and roles are visible on LinkedIn, corporate directories, or dark web credential dumps
- Historical incident data indicating where breaches or near-misses have originated
Roles with high authority, broad system access, or frequent external communication, including executives, finance teams, IT administrators, and HR teams, consistently emerge as priority segments. Simulation data alone is insufficient because it measures susceptibility to generic attacks rather than role-specific threat vectors.
What Training Formats Work Best for Executives Compared to Frontline Employees?
Executives respond best to short, scenario-based briefings, exercises simulating BEC and deepfake impersonation incidents, and board-ready risk summaries that connect security decisions to financial outcomes.
Time is the primary constraint for this segment, so content must be dense, directly relevant, and free of foundational concepts already understood at that level.
Frontline employees engage more effectively with microlearning modules triggered immediately after a simulated phishing, vishing, or smishing test failure, as learning at the moment of a mistake produces stronger behavioral retention than scheduled annual modules.
Technical staff benefit from hands-on simulation environments and challenge-based exercises that reflect their actual system access.
How Should Role-Based Training Be Structured for Contractors and Third-Party Vendors?
Contractors and third-party vendors require a scoped training track that aligns with their specific access levels without exposing internal threat intelligence or program architecture to external parties.
Training should address the systems and data they can reach, the attack vectors relevant to their engagement type, and clear protocols for reporting suspicious activity. Organizations should not assume vendor security training programs are equivalent to internal standards, as many third-party breaches originate from contractors who received no organization-specific training.
Onboarding should automatically trigger enrollment, and access should be tied to training completion status. Contracts should explicitly define training obligations rather than rely on informal expectations.
Can Role-Based Security Training Be Automated, or Does It Require Manual Program Management?
Role-based security training can and should be substantially automated. Modern platforms integrate with HRIS and identity systems so that role changes, new hires, and offboarding automatically update training track assignments without manual intervention.
Simulation failures can trigger immediate targeted microlearning rather than waiting for the next scheduled training cycle. Risk score thresholds can prompt escalated training for individuals displaying elevated behavioral signals.
Manual program management at scale is neither efficient nor consistent, as human-assigned training tracks introduce lag, coverage gaps, and update failures. Automation handles enrollment logic, enabling security awareness managers to focus on content quality, scenario realism, and program strategy.
What Metrics Should Security Leaders Use to Prove the ROI of Role-Based Training to the Board?
Board-ready metrics must translate behavioral data into business risk language. The most credible indicators include:
- Simulation failure rate reduction by role over time, demonstrating behavioral improvement rather than completion alone
- The phishing report rate is increasing, indicating that employees are actively contributing to the organization's defense
- Mean time to report a suspicious message
- Repeat simulation failure rates by department
- Risk score trajectory per business unit
These metrics should be framed against widely available benchmarks for breach costs.
How Does AI-Powered Spear Phishing Change What Role-Based Training Needs to Cover?
AI-powered spear phishing changes the threat model for every high-risk role by enabling adversaries to craft personalized attacks at scale using OSINT data scraped from LinkedIn, corporate websites, and public filings.
An executive who passes a generic phishing test may still be vulnerable to an AI-generated email referencing actual direct reports, recent travel, or live deal activity.
Role-based training must now include deepfake voice and video recognition, OSINT-informed social-engineering scenarios, and decision-verification protocols, particularly for finance and executive roles, where a single approval can authorize a significant financial transaction.
See How Adaptive Security Delivers Role-Based Training Personalized to Every Employee's Actual Threat Exposure
The gap between compliance-driven training and risk-driven training is where breaches happen. Adaptive Security closes that gap by mapping Security Awareness Training, Phishing Simulations, and Risk Monitoring and Mitigation directly to each employee's role, risk score, and real-world threat exposure, rather than to a generic curriculum.
Book a demo with Adaptive to see how the platform personalizes training at scale across job functions in an organization.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents