Cybersecurity awareness training effectiveness is measured by one outcome: whether employees make more secure decisions under live threat conditions, not whether they completed a course. According to the Verizon Data Breach Investigations Report 2025, approximately 60% of breaches involve the human element. The percentage of breaches involving the human element does not come down because employees clicked through a module, it comes down when training produces different behavior the moment an attack lands.

This guide covers what genuinely drives cybersecurity awareness training effectiveness in the current threat environment.
- The structural gap between awareness and behavior change that limits cybersecurity awareness training effectiveness;
- Why most compliance-driven cybersecurity awareness training programs are designed to fail and what behavioral science shows about retention;
- How AI-generated spear phishing, deepfake vishing, and smishing campaigns have made legacy detection cues obsolete;
- A concrete measurement framework that ties cybersecurity awareness training effectiveness to board-level risk;
- A nine-step implementation guide grounded in continuous, dynamic, personalized delivery.
Stop measuring security awareness training by completion logs and start measuring it by behavior change with Adaptive Security.
What Cybersecurity Awareness Training Effectiveness Actually Means
Cybersecurity awareness training effectiveness is the measurable degree to which a program reduces risky employee behavior and improves security decision-making under real threat conditions. Completion is an activity metric; effectiveness is an outcome metric. Most organizations track the former, which is why their cybersecurity awareness training programs produce certificates but not protection.
Why the Stakes Demand More Than Awareness
The financial exposure behind this gap is concrete. When the dominant entry vector for breaches is the workforce itself, every dollar spent on perimeter tooling sits downstream of an employee decision; the only question is whether that decision was rehearsed.
According to IBM's Cost of a Data Breach Report 2025, the global average breach cost is $4.44 million, with the mean time to identify and contain a breach reaching 241 days, the lowest figure in nearly a decade. Cybersecurity awareness training that produces awareness without changing behavior leaves that exposure fully intact.
The Three-Tier Outcome Hierarchy That Defines Cybersecurity Awareness Training Effectiveness
Effective cybersecurity awareness training programs operate across three distinct levels where each builds on the last:
- Awareness: employees recognize that a threat class exists;
- Behavior change: employees respond differently, pausing before clicking, flagging a suspicious caller, verifying an urgent wire request through a second channel;
- Culture change: secure behaviors become organizational norms, reinforced by management and sustained without constant reminders.
The gap between tiers one and three explains why a cybersecurity awareness training program can report 95% completion while phishing click rates remain unchanged. Most security awareness training programs reach tier one and stop there.
Understanding why those cybersecurity awareness training programs stall at awareness requires a closer look at how modern threats are designed to exploit exactly that gap.
Move your cybersecurity awareness training program past completion stage and into measurable behavior change with Adaptive Security.
Why Most Programs Undermine Cybersecurity Awareness Training Effectiveness
Cybersecurity awareness training effectiveness breaks down at the program design level long before a single employee clicks a phishing link. Most organizations build their programs around compliance calendars and static content libraries.
That structural choice produces completion certificates but not behavioral change. The result is measurable: breaches continue to originate from the human layer despite cybersecurity awareness training budgets that grow every year.
Why the Ebbinghaus Forgetting Curve Destroys Annual Training ROI

Memory decay begins immediately after instruction ends. According to PLOS One research published by Murre and Dros (2015), employees forget up to 67% of new information within 24 hours and up to 79% within a month without reinforcement.
A single annual cybersecurity awareness training session delivers exactly that scenario: one exposure, no reinforcement, and 52 weeks of daily threat exposure in between. The math does not support the cadence.
Why Annual Cadence Is a Structural Design Failure
Scheduling cybersecurity awareness training once per year treats a dynamic, daily threat environment as if it were a static compliance event. Cyberattackers rotate from credential phishing to vishing to AI-generated spear phishing on a weekly basis.
Employees who completed cybersecurity awareness training in January are expected to apply that knowledge in November. Continuous, triggered learning models close this gap by delivering short-form reinforcement immediately after a risk behavior occurs.
Why One-Size-Fits-All Content Misses the Highest-Risk Employees
Generic cybersecurity awareness training content built for the average employee systematically ignores the population that matters most.
Blanket security awareness training wastes the majority of its reach on employees who present minimal risk while leaving high-risk individuals untouched by relevant scenarios. Cybersecurity awareness training effectiveness depends on directing intensity toward concentrated risk.
What Separates Compliance Theater From Actual Behavioral Change
Cybersecurity awareness training built to satisfy a regulatory checkbox produces two outputs: completion logs and a false sense of security. Neither reduces breach probability.
Cybersecurity awareness training programs designed around audit requirements optimize for documentation rather than decision-making. Auditors reviewing completion rates cannot measure whether employees actually paused before clicking a suspicious link.
How Fear-Based Programs Create Security Fatigue
Cybersecurity awareness training programs that lead with threat severity rather than pairing urgency with practiced response actions trigger avoidance rather than confidence. Psychological research on fear appeals consistently shows that high-threat messaging without efficacy cues produces learned helplessness.
Employees disengage because they believe the threat is too large for their actions to matter. Cybersecurity awareness training programs that build resilience develop practiced skill through repeated realistic scenarios, instead of generating anxiety through warnings without recourse.
Each of these failures shares a common root: they treat cybersecurity awareness training as an event rather than a continuous behavioral intervention. That distinction is where evidence-based cybersecurity awareness training program design has to start.
Replace static, calendar-driven modules with continuous, behavior-triggered reinforcement through Adaptive Security.
What the Evidence Says About Cybersecurity Awareness Training Effectiveness
Cybersecurity awareness training effectiveness is determined primarily by instructional design, not content volume. Research across learning science and cybersecurity-specific studies consistently shows that cybersecurity awareness training programs built on distributed practice, active participation, and personalized delivery outperform annual, lecture-based campaigns on every measurable outcome.
The format of cybersecurity awareness training matters as much as the content it delivers.
Why Spaced Repetition Outperforms Annual Cybersecurity Awareness Training
Annual cybersecurity awareness training sessions front-load information that memory discards within days. Spaced repetition addresses this by distributing practice across weeks and months, aligning with the brain's memory consolidation cycles instead of working against them.
Short microlearning modules under ten minutes, delivered at regular intervals, consistently produce stronger retention than hour-long annual sessions. They trigger recall at the moment knowledge begins to fade, before it has already been lost.
How Active Learning Produces Better Security Outcomes Than Passive Instruction
According to a 2014 meta-analysis published in the Proceedings of the National Academy of Sciences, a review of 225 studies found that students in traditional lecture formats were 1.5 times more likely to fail assessments than those in active learning, with average failure rates of 33.8% versus 21.8%.
In cybersecurity contexts, this translates directly: employees who practice detecting phishing in simulations build pattern recognition that passive watching cannot produce. Phishing simulations function as active learning interventions; employees encounter realistic attacks, make decisions under pressure, and receive immediate corrective feedback.
According to the Verizon Data Breach Investigations Report 2025, user reporting of suspicious emails increased fourfold at organizations that provided recent phishing simulation training, compared to organizations without recent training. The mechanism is rehearsal under realistic pressure, not knowledge transfer; employees who have actually paused, examined, and reported a simulated lure carry that decision pattern into live inboxes.
How Role-Based Personalization Raises Cybersecurity Awareness Training Effectiveness
Generic cybersecurity awareness training assigns the same threat scenarios to a software engineer and a finance director, even though their attack surfaces share almost nothing.
Personalization is what separates the two models; behavior-based programs match content to the specific risks an employee actually faces.
In cybersecurity awareness training, role-specific exposure matters operationally:
- Finance employees face invoice fraud, business email compromise (BEC), and wire transfer manipulation;
- Developers face credential theft and social engineering through code collaboration tools;
- Executives face deepfake impersonation and high-value targeting.
Role-based cybersecurity awareness training curriculum that reflect actual job function and open-source intelligence (OSINT) exposure produce measurably higher completion rates and knowledge retention because the content registers as immediately relevant.
Match training intensity to actual employee risk with role-based simulations from Adaptive Security.
What Psychological Principles Drive Lasting Behavior Change
Three behavioral mechanisms address distinct barriers to secure action and together raise overall cybersecurity awareness training effectiveness:
- Nudge theory: restructures default choices, such as setting MFA enrollment as opt-out rather than opt-in, so safer behavior requires no additional cognitive load;
- Implementation intentions: give employees a pre-formed decision rule ("If I receive an urgent payment request by email, I will verify by calling the sender directly") that activates under stress;
- Positive reinforcement: recognizing employees who correctly report phishing attempts, instead of penalizing those who click, builds a reporting culture.
Why Timing of Cybersecurity Awareness Training Delivery Determines Its Impact
Delivering a targeted microlearning module immediately after an employee fails a phishing simulation produces retention outcomes that scheduled training cannot replicate.
The behavioral mechanism is operant conditioning: the failed simulation creates an emotional signal that primes the brain for learning. Cybersecurity awareness training delivered within minutes of that signal is encoded with far greater fidelity than training delivered three weeks later. This just-in-time model transforms every simulation failure from a negative data point into a high-retention teaching moment.
How Programs Should Address Non-Technical and Remote Employees
Non-technical employees require different framing, vocabulary, and scenario depth than IT staff. A threat description pitched at a security operations analyst confuses an accounts payable clerk who simply needs to recognize what an invoice fraud attempt looks like and how to verify it by phone.
Effective cybersecurity awareness training programs adapt both depth and vocabulary without diluting accuracy. Remote workers compound this challenge: home networks lack enterprise security controls, shadow IT adoption rises when IT oversight is reduced, and the peer accountability that reinforces security norms in shared offices disappears entirely.
Cybersecurity awareness training programs that ignore these environmental differences deliver uniform content into non-uniform risk contexts. Closing the gap between completion rates and behavioral resilience requires continuous, dynamic, personalized delivery, and the architecture to prove it.
How AI-Powered Attacks Are Raising the Bar on Cybersecurity Awareness Training Effectiveness
Cybersecurity awareness training effectiveness is now directly measured by whether programs prepare employees for threats that did not exist two years ago.
According to Sumsub Identity Fraud Report 2024-2025, deepfake fraud incidents increased fourfold globally between 2023 and 2024 and now account for 7% of all fraud attempts. This includes the case in which engineering firm Arup lost $25 million when a finance employee approved a wire transfer after every participant on a video call turned out to be AI-generated. The threat model underlying most cybersecurity awareness training programs is already obsolete.
How AI Changes What Employees Need to Recognize
Generative AI has eliminated the traditional red flags employees are trained to spot. AI-generated spear phishing emails now arrive grammatically flawless, contextually accurate, and personalized using open-source intelligence (OSINT).
Cyberattackers use publicly available data such as LinkedIn profiles, job postings, and press releases to construct targeted social engineering attacks against specific individuals. An attacker who knows an employee's manager, a recent company announcement, and the employee's job function can craft a message that passes every visual and instinctive check a trained reader would apply.
Cybersecurity awareness training programs still focused on spelling errors and generic greetings are preparing employees to defeat threats from a decade ago.
Test your team against AI-generated spear phishing that mirrors today's adversaries through Adaptive Security.
What Makes Deepfake Vishing and Smishing Uniquely Dangerous

Voice and video attacks exploit the channels where employees have the lowest defensive awareness. According to CrowdStrike 2025 Global Threat Report, voice phishing (vishing) attacks increased 442% between the first and second halves of 2024, a step-change that legacy email-only cybersecurity awareness training cannot account for.
In a deepfake vishing attack, an AI-cloned voice synthesized from publicly available recordings of an executive calls an employee directly, establishes urgency, and requests a wire transfer or credential reset. The call sounds indistinguishable from the real person.
Coordinated multi-channel attacks layer this further: a smishing message arrives via SMS, followed by a voice call, followed by a spoofed email confirmation. Three channels reinforce the same fraudulent instruction and overwhelm the instinct to pause and verify. Employees trained exclusively on email phishing recognition have no rehearsed response for this sequence.
Why Annual Training Cycles Cannot Match AI-Speed Attacks
AI compresses attack development from weeks to hours, and training programs that update content annually are structurally incapable of keeping pace.
By the time a new attack variant appears in a quarterly module, that variant has already evolved. Effective programs require continuous content refresh cycles, near-real-time simulation updates, and multi-channel phishing simulations that expose employees to email, SMS, voice, and deepfake video.
According to World Economic Forum Global Cybersecurity Outlook 2025, 72% of organizations reported a rise in cyber risks driven in significant part by AI-enhanced phishing, vishing, and deepfakes. Measuring readiness only by email click rates is where most cybersecurity awareness training programs currently stop, and that gap defines the difference between compliance practice and genuine risk reduction.
How to Measure Cybersecurity Awareness Training Effectiveness
Measuring cybersecurity awareness training effectiveness requires tracking a layered set of behavioral, operational, and strategic metrics. Start with phishing simulation click rates and directional trend analysis, then build upward through reporting rates, knowledge assessments, time-to-report, and individual human risk scores.
The right metrics depend on a cybersecurity awareness training program's maturity stage: a compliance-focused cybersecurity awareness training program and a behavioral-change focused program measure fundamentally different things.
1. Track Phishing Simulation Click Rate Trends
Click rate is the most commonly reported metric, but its value lies in trend analysis rather than the raw number. A 12% click rate at month one is meaningless without cohort comparison.
That same 12% in month six, after repeated simulations, signals a stalled program. According to the Verizon Data Breach Investigations Report 2025, organizations that provided recent phishing simulation training saw a fourfold increase in employee reporting of suspicious emails — the primary measurable behavioral gain attributable to training.
2. Treat Reporting Rate as the Primary Culture Indicator
The rate at which employees report suspicious emails to the security team is a stronger signal of security culture than click rate alone.
Simulation reporting behavior predicts real-world reporting behavior: organizations that build high simulated threat reporting rates see a corresponding increase in actual threat reporting. Tracking this figure over time, broken down by cohort, reveals whether employees are shifting from passive recipients to active defenders.
3. Pair Knowledge Assessments With Behavioral Data
Pre and post-training knowledge assessments measure awareness gains directly, but scores in isolation do not confirm behavioral change.
A finance employee who scores 95% on a phishing assessment but still clicks a deepfake wire transfer request has not changed behavior. Assessment scores are most useful when cross-referenced against cyberattack simulation click rates and reporting rates from the same cohort.
4. Measure Time-to-Report Across Training Cohorts
How quickly an employee escalates a suspicious email is a discrete behavioral outcome that reflects both awareness and confidence.
Track median time-to-report from initial employee contact with a simulated threat to the moment the security team receives the report. As cybersecurity awareness training matures, this metric should compress; employees who recognize threats faster reduce attacker dwell time, which directly correlates with lower breach costs.
Surface the employees driving real risk and act on it with Adaptive Security.
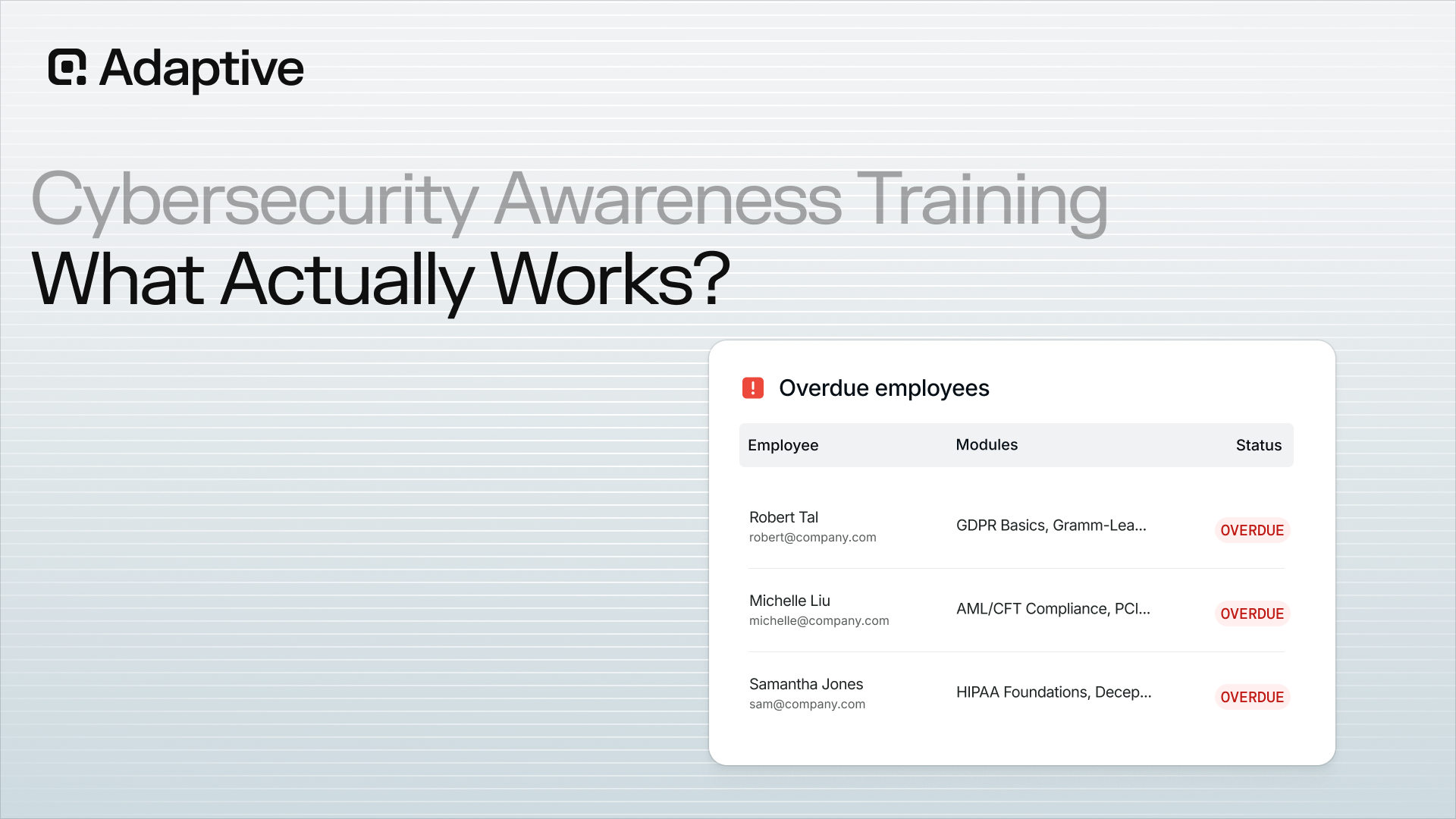
5. Use Human Risk Scores as the Operational Unit of Measurement

Individual human risk scores aggregate simulation behavior, training completion, OSINT exposure, credential breach history, and real-incident reporting rates into a single indicator per employee.
This is the most operationally actionable metric in any awareness program: it concentrates training intensity on the small population of employees driving the majority of incidents and allows security teams to direct targeted training where it produces the greatest risk reduction. Adaptive Security's human risk management platform monitors over 1,000 OSINT data points per employee to fuel those scores continuously.
6. Benchmark Against the SANS Security Awareness Maturity Model
The SANS Security Awareness Maturity Model, updated in 2025 with input from over 200 security awareness professionals, defines five stages: Non-Existent, Compliance-Focused, Promoting Awareness and Behavioral Change, Long-Term Culture Change, and Optimization and Resilience.
Each stage carries distinct measurable characteristics. A Stage 2 cybersecurity awareness training program measures audit completion; a Stage 4 cybersecurity awareness training program measures cultural indicators like employee security attitudes and cross-departmental security integration. Knowing which stage your cybersecurity awareness training program occupies determines which metrics are appropriate.
7. Translate Metrics Into Board-Level Business Risk Language
Boards do not evaluate cybersecurity awareness training effectiveness by click rate percentages.
Translate metrics into business risk indicators: average human risk score trend quarter-over-quarter, reduction in high-risk employee count, incident rate by training cohort, and estimated breach cost avoidance based on risk-reduced headcount. A measurable reduction in high-risk employee concentration carries direct financial value that security leaders can present alongside any other capital investment.
As cybersecurity awareness training programs mature from compliance theater to genuine culture change, the measurement framework must evolve alongside them. Static metrics applied to a dynamic program produce misleading signals.
Translate behavioral data into board-ready risk language with reporting from Adaptive Security.
How to Build a Program That Delivers Measurable Cybersecurity Awareness Training Effectiveness
Cybersecurity awareness training effectiveness is determined long before the first module launches. It lives in the decisions made during program design.
Building a cybersecurity awareness training program that measurably reduces human risk requires nine sequential actions. The underlying architecture is identical for small businesses and large enterprises; only the resource levels and automation dependencies differ.
1. Establish Executive Sponsorship
Leadership buy-in is a structural requirement. Cybersecurity awareness training programs where executives visibly model secure behavior and publicly support training see higher participation rates and faster cultural adoption.
Boards must treat cybersecurity as a business risk category instead of an IT expense, and that posture starts at the top.
2. Conduct a Baseline Risk Assessment
Before designing content or scheduling simulations, identify where exposure actually lives. Map phishing susceptibility by department, surface OSINT exposure by role, flag high-risk employee segments such as finance and executives, and document existing compliance gaps.
This assessment becomes the baseline against which all future cybersecurity awareness training progress is measured.
3. Define Objectives Tied to Business Outcomes
"Achieve 100% training completion" is not a cybersecurity awareness training program's goal. Frame objectives as risk reduction targets.
Reducing the phishing simulation click rate from 28% to under 10% within 90 days is a goal leadership can track alongside revenue and operational metrics. Set 90-day, 6-month, and 12-month benchmarks from the start.
4. Map Training Content to Roles and Threat Profiles
Generic content creates false confidence. Each role faces a distinct attack surface:
- Finance employees need business email compromise (BEC) and wire fraud scenarios;
- Executives require deepfake and vishing preparation;
- IT staff need credential theft and shadow IT coverage;
- All employees need AI-era phishing fundamentals, because generative AI spear phishing now reaches inboxes that email filters miss.
Multi-channel phishing simulations reflecting role-specific attack surfaces are the delivery mechanism that connects content to context.
Tailor every simulation to the role being attacked with Adaptive Security.
5. Launch Multi-Channel Phishing Simulations
Start with a baseline simulation to establish starting click and reporting rates. That number anchors every future comparison.
Then simulate email, voice, and SMS threat vectors in rotation. Employees who only train against email phishing remain exposed to vishing and smishing, attack channels most cybersecurity awareness training programs ignore entirely.
6. Deploy Microlearning Triggered by Simulation Outcomes
An employee who fails a cybersecurity awareness training simulation needs a targeted two-minute module within hours, instead of at the next quarterly training cycle.
Immediate, behavior-triggered microlearning closes the gap between failure and correction before the memory of the incident fades and old habits reassert themselves. Speed of intervention is what separates behavioral change from compliance theater.
7. Establish a Continuous Cadence
Annual cybersecurity awareness training is a compliance checkbox; it cannot function as a defense strategy.
Replace it with monthly microlearning, quarterly simulation campaigns, and real-time threat content updates that reflect current attack methods. AI-powered attack development moves fast enough that any static cybersecurity awareness training library is permanently behind within months of its creation.
8. Address Compliance Without Letting It Drive Design
Cybersecurity awareness training content should map to SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 requirements relevant to the organization.
Compliance coverage is a byproduct of a well-designed cybersecurity awareness training program rather than its primary purpose. Cybersecurity awareness training programs built solely around compliance checklists optimize for documentation over behavioral change, which is precisely why so many organizations pass audits and still suffer breaches.
9. Review and Iterate Quarterly
Use risk score trends, simulation click and reporting rates, and cohort-level data to adjust cybersecurity awareness training content targeting and report progress to leadership.
High-risk cohorts identified in quarter one should show measurable improvement by quarter two. If they do not, the cybersecurity awareness training content or cadence needs adjustment, instead of the employees. The cybersecurity awareness training platform a team chooses to run this process determines how much of that data is visible, actionable, and board-ready.
Run all nine steps from one platform with Adaptive Security.
The Business Case for Cybersecurity Awareness Training Effectiveness
Cybersecurity awareness training effectiveness translates directly into avoided breach costs, and that math is straightforward to present to any board. According to FBI Internet Crime Complaint Center IC3 Annual Report 2024, U.S. cybercrime complaints reached 859,532 with reported losses of $16.6 billion, a 33% increase over the previous year, with phishing and spoofing the most reported categories by volume.
A cybersecurity awareness training program that measurably reduces human-layer susceptibility produces a calculable risk reduction value that outpaces its cost. The savings compound as employees develop the judgment to short-circuit attacks before they escalate into incidents.
According to Comcast Business Cybersecurity Threat Report 2024, between 80% and 95% of breaches are initiated by a phishing attack; the human layer is the dominant entry vector, and it is also the most addressable.
Does Effective Training Reduce Cyber Insurance Premiums
Insurers increasingly evaluate cybersecurity awareness training program maturity during underwriting, and organizations with documented, regularly updated security awareness training programs often qualify for lower premiums or broader coverage terms.
Underwriters treat cybersecurity awareness training completion records and simulation results as evidence of managed human risk, which shifts their exposure calculation in the organization's favor. Verify specifics with your broker before building budget assumptions around insurance savings, as outcomes vary by carrier, policy structure, and industry vertical.
How Cybersecurity Awareness Training Maps to Regulatory Compliance
Effective cybersecurity awareness training programs map to multiple compliance frameworks simultaneously:
- HIPAA workforce training mandates;
- GDPR Article 39 data protection awareness obligations;
- PCI-DSS Requirement 12.6;
- SOC 2 CC1.1 and CC1.4 security awareness controls.
Different verticals carry different exposure profiles. Organizations in healthcare face HIPAA breach penalties and elevated insider threat profiles; financial services organizations face business email compromise (BEC) and wire fraud at scale; technology companies face credential theft and shadow IT exposure. Each vertical requires cybersecurity awareness training calibrated to its specific risk landscape.
Map your program to every framework you operate under with Adaptive Security.
Why Security Culture Is the Hardest Benefit to Quantify
An organization where employees actively report suspicious activity creates a distributed early-warning system that no firewall, endpoint tool, or email filter can replicate.
When a finance analyst flags an unusual wire request before approving it, or an executive's assistant questions a voice call from an unverified number, the threat is neutralized at the source. Enterprise organizations benefit most from automation, risk scoring, and role-based segmentation to scale that culture; smaller organizations benefit most from ease of deployment and ready-to-use content libraries that reduce time-to-protection.
A cybersecurity awareness training program that changes behavior is an asset that compounds as employees reinforce each other's vigilance over time.
Cybersecurity Awareness Training Effectiveness as a Human Risk Management Discipline
Cybersecurity awareness training effectiveness, measured at its highest tier, is not defined by training completion rates. It is defined by how well an organization continuously detects, scores, and reduces the behavioral risks its employees carry at any given moment.
Human risk management (HRM) is the discipline that operationalizes this standard. Security awareness training delivers content; HRM treats employee behavior as an organizational risk variable that must be monitored, measured, and managed the same way financial or operational risk is.
According to Forrester The Future Is Now: Introducing Human Risk Management 2024, the firm formally retired the "security awareness and training" market category and redefined HRM solutions as systems that detect and measure human security behaviors, quantify the resulting risk, and initiate policy and cybersecurity awareness training interventions based on those measurements.
What Separates Awareness Programs From HRM Disciplines
A traditional cybersecurity awareness training program answers one question: did employees complete training? An HRM discipline answers a harder one: are employees actually behaving more securely, and where is risk still concentrated?
HRM extends cybersecurity awareness training effectiveness across four interconnected functions:
- Continuous behavioral signal collection across simulations, real incidents, and OSINT exposure;
- Dynamic individual risk scoring updated by real behavior, instead of stale completion records;
- Automated intervention workflows that deploy targeted content the moment risk signals spike;
- Executive risk reporting that translates behavioral data into business risk language.
How HRM Extends Cybersecurity Awareness Training Effectiveness Beyond Training Delivery
Behavioral signal collection is the foundation. Where a traditional program captures simulation click rates, an HRM discipline aggregates signals from simulation performance, real-incident reporting history, OSINT exposure, and credential breach records to build a complete behavioral profile for every employee.
Those signals feed dynamic risk scores that reflect what an employee actually did last week, instead of whether they passed a module six months ago.
Automated intervention closes the gap between risk identification and remediation. When risk signals spike, HRM systems deploy targeted training immediately rather than waiting for the next scheduled campaign.
Board-level reporting then translates this behavioral data into business risk language: exposure trends by department, risk score movement over time, and measurable reductions in human-layer vulnerability that a CISO can justify to an executive audience. The maturity shift from awareness measurement to human risk management represents the highest tier of cybersecurity awareness training effectiveness.
What to Look for in a Platform That Drives Cybersecurity Awareness Training Effectiveness

Selecting the right cybersecurity awareness training platform is a capability decision as much as a vendor decision. The architecture determines whether a program continuously adapts or plateaus at scheduled delivery.
Legacy platforms built to address 2015 email threats cannot be patched into relevance against deepfake video, AI-generated vishing, and OSINT-personalized spear phishing. According to Microsoft Digital Defense Report 2025, Microsoft scans 5 billion emails and processes 100 trillion security signals daily; the threat surface that platforms must cover is no longer email-only.
1. Confirm Multi-Channel Simulation Coverage
Email-only simulation is structurally insufficient. A platform must cover email phishing, vishing, smishing, and deepfake video attacks because cyberattackers already deploy all four vectors in coordinated sequences.
According to APWG Phishing Activity Trends Report Q4 2024, 989,123 phishing scams were recorded in that quarter alone, averaging roughly 330,000 attacks per month across multiple delivery channels. Social engineering rarely arrives on a single channel anymore.
2. Require OSINT-Informed Personalization
Simulations built on generic templates train employees to spot generic attacks. Effective platforms use OSINT, publicly available employee data from LinkedIn, company directories, and social media, to build role-specific scenarios that mirror the targeting logic actual adversaries use.
A finance director should face vendor impersonation attempts; a developer should encounter credential-harvesting via fake code repositories.
3. Verify Automated Microlearning Triggers
A platform that waits for the next scheduled training cycle after an employee fails a simulation wastes the most teachable moment available.
Automated microlearning triggers deploy a targeted module immediately after a simulation failure, reinforcing correct behavior while the experience is still fresh. This is a structural advantage over batch-delivery programs.
4. Demand Dynamic Risk Scoring
Training completion percentages measure inputs, instead of outcomes.
Dynamic human risk scoring updates continuously based on behavioral signals: simulation results, reporting behavior, OSINT exposure, and credential breach history. The result is a real-time view of which individuals and departments carry the most exposure at any given moment.
See where human risk is concentrated across your workforce in real time with Adaptive Security.
5. Audit Content Freshness and AI Threat Coverage
The content library must include deepfake recognition, AI-generated phishing, vishing, and smishing modules as core curriculum, beyond optional add-ons.
Ask vendors directly: how frequently is content updated, and can the platform generate custom training from internal policies or real threat intelligence without requiring a content services engagement?
6. Validate Compliance Framework Mapping
Audit-ready reporting mapped to SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 should be generated automatically.
If a compliance officer has to export raw data and rebuild a report to satisfy an auditor, the platform is creating work instead of eliminating it.
7. Test Integration Depth Before Committing
Native integrations with Microsoft 365, Google Workspace, HRIS systems, and SIEM or SOAR platforms determine real deployment time and ongoing IT lift.
A cybersecurity awareness training platform that deploys in minutes through a two-click integration carries a structurally different adoption curve than one requiring MX record changes and professional services engagement.
8. Require Board-Ready Reporting
Security leaders cannot justify budget to a board using simulation click rates. The platform must translate risk scores and behavioral trend data into executive-level business risk language; showing exposure reduction over time, department-by-department risk delta, and ROI framing tied to breach cost avoidance.
9. Evaluate Vendor AI Investment and Platform Trajectory
A vendor's investment in AI simulation and content development signals whether their platform will keep pace with the threat landscape or fall further behind it.
Evaluate active product development in generative AI simulation, deepfake video capabilities, and automated threat content generation. What a platform builds toward in the next 18 months matters as much as what it does today.
See How Adaptive Security Drives Cybersecurity Awareness Training Effectiveness Across An Entire Organization
Adaptive Security is built specifically for the threat environment legacy platforms were never designed to address. Its AI-native engine combines phishing simulations across email, voice, and SMS with personalized training that responds to each employee's actual behavior, so security teams can see exactly where risk is concentrated and reduce it.
The platform monitors over 1,000 OSINT data points per employee to build dynamic human risk scores that update continuously, surfacing the small population of employees who drive the majority of incidents. Behavior-triggered microlearning, automated phishing simulations, and integrated phish triage workflows replace the manual lift that keeps most programs stuck in annual-cycle delivery.
For security leaders, the platform translates behavioral data into board-ready business risk language: exposure reduction over time, department-by-department risk delta, and ROI framing tied to breach cost avoidance. Compliance mapping to SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 generates automatically.
Bring measurable cybersecurity awareness training effectiveness to your workforce with Adaptive Security.
Frequently Asked Questions About Cybersecurity Awareness Training Effectiveness
Does cybersecurity awareness training actually reduce the risk of data breaches?
Yes. Cybersecurity awareness training effectiveness translates into measurable risk reduction when programs are designed around behavioral change instead of compliance completion.
The critical distinction is design: programs built to generate completion logs deliver documentation, while programs built around active learning, spaced repetition, and simulation-based practice produce statistically significant reductions in employee susceptibility.
How often should employees receive cybersecurity awareness training?
Employees should receive training continuously throughout the year, instead of once annually. Memory decay during the gap between annual sessions consistently erases the majority of retained knowledge before it can be applied.
Practical cadence:
- Monthly 5 to 10 minute microlearning modules;
- Quarterly phishing simulation campaigns;
- Just-in-time training triggered by specific risk signals.
What metrics should organizations use to measure cybersecurity awareness training effectiveness?
Organizations should track five primary indicators:
- Phishing simulation click rate trend: directional improvement over time;
- Suspicious email reporting rate: the strongest signal of security culture;
- Knowledge assessment scores: awareness gains paired with behavioral data;
- Time-to-report: how quickly employees escalate suspicious activity;
- Individual human risk scores: dynamic scores aggregating behavior, OSINT exposure, and credential breach history.
How are AI-generated phishing attacks and deepfakes changing what cybersecurity awareness training must cover?
AI-generated attacks have invalidated the most widely taught detection signals: spelling errors, generic greetings, and awkward phrasing are no longer reliable cues.
Training must now cover AI-generated spear phishing, deepfake vishing, smishing, and coordinated multi-channel sequences. The velocity problem compounds this; AI compresses attack development from weeks to hours, making annual content update cycles structurally obsolete.
What is the ROI of cybersecurity awareness training for businesses?
ROI is calculated against breach cost avoidance. A measurable reduction in human-layer susceptibility translates into a calculable risk reduction value that outpaces program cost.
The business case extends to lower cyber insurance premiums, compliance coverage across HIPAA, PCI-DSS, SOC 2, and GDPR, and a distributed reporting culture that no technical control replicates.
Cybersecurity Awareness Training Effectiveness: Key Takeaways
- Effectiveness is an outcome metric tied to behavior change under live threat conditions, beyond completion rates;
- Annual, generic training fails because memory decay outpaces reinforcement and concentrated risk goes untouched;
- AI-generated spear phishing, deepfake vishing, and coordinated smishing sequences have rendered legacy detection cues obsolete;
- Spaced repetition, role-based personalization, and behavior-triggered microlearning consistently outperform lecture-based campaigns;
- Layered measurement, including click rate trends, reporting rates, time-to-report, and human risk scores, replaces vanity metrics with actionable signal;
- Human risk management extends awareness training into a continuous discipline of detection, scoring, and intervention;
- Platform architecture determines whether a program adapts continuously or plateaus at scheduled delivery.
Put every takeaway above into practice with a platform built for measurable cybersecurity awareness training effectiveness, Adaptive Security.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents