Cybersecurity awareness training platforms are the primary tool organizations rely on to close the human layer of their security posture, yet most were built for a cyber threat environment that no longer exists. Completion certificates pile up while measurable behavior change does not, and the gap between the two is exactly where breach risk lives.
The challenges covered here span the full cybersecurity awareness training platform lifecycle:
- Why employees disengage and forget what their cybersecurity awareness training platform delivers;
- How generic content fails specific roles inside a cybersecurity awareness training platform;
- Why deepfake and vishing threats outpace annual content updates on most cybersecurity awareness training programs;
- Why completion rates tell security teams almost nothing about measurable behavioral change.
According to the Verizon Data Breach Investigations Report 2025, social engineering accounts for 60% of breaches involving the human element, and according to the IBM Cost of a Data Breach Report 2025, the average breach cost reached $4.44 million. Those figures reflect what happens when cybersecurity awareness training platforms generate certificates but not skills.
Stop training your employees for compliance and start training for measurable cyber threat risk reduction.
Why Cybersecurity Awareness Training Platforms Fall Short of Modern Threats
Cybersecurity awareness training platform challenges run deeper than most organizations realize. Most organizations still run programs designed for a threat landscape that existed a decade ago, while cyberattackers now operate at the speed of generative AI's development.
The distance between cybersecurity awareness training platform investment and measurable behavioral change is not a minor gap; it is a direct line to financial and reputational damage.
What Human Error Actually Causes in Breaches Affecting Cybersecurity Awareness Training Platforms
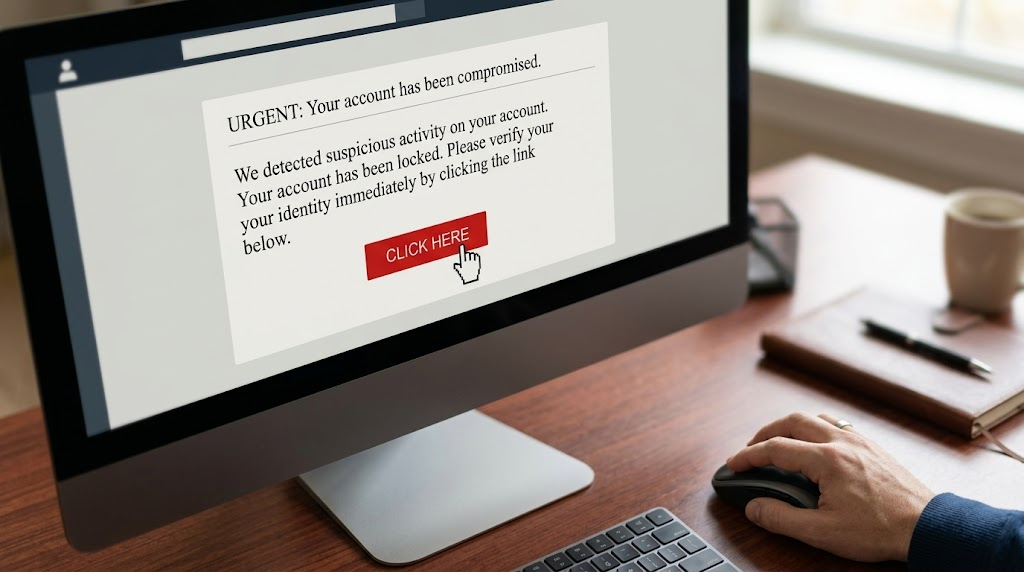
Cyberattackers exploit human trust, habit, and urgency because those vectors are often faster and cheaper than breaking technical controls. Legacy cybersecurity awareness training platforms were designed to raise awareness through annual modules and email phishing simulations.

These platforms were never built to train employees against deepfake video calls, AI-generated spear phishing, or vishing at scale. Awareness and behavior are not the same outcome, and most platforms measure the former while organizations pay the price for the latter.
Train employees against the full attack surface, including voice, SMS, and deepfake video with Adaptive Security.
Why Traditional Cybersecurity Awareness Training Platforms Have Not Closed the Gap
The gap between cybersecurity awareness training platform investment and actual risk reduction is well documented.
"These results mean that it will be hard for these common forms of training to meaningfully teach users protective behaviors, without a major rethinking and redesign of the training," said Grant Ho, Assistant Professor of Computer Science at the University of Chicago.
Ho's 2025 study conducted at UC San Diego Health found no significant correlation between completing annual cybersecurity training and employees' ability to resist phishing attacks. Employees who had completed training within days performed no better than those who had not trained in over a year.
Compliance-driven frequency does not substitute for cybersecurity awareness training platform content designed around behavioral science and realistic threat exposure. Employees are not the problem; they are the most scalable defense an organization has against social engineering, provided the training reflects actual attack conditions.
Low Engagement and the Forgetting Curve in Cybersecurity Awareness Training Platforms
Cybersecurity awareness training platform challenges compound quickly when employees disengage, and the forgetting curve ensures that disengagement carries a direct cost. A 2015 PLOS One study by researchers Jaap M.J. Murre and Joeri Dros at the University of Amsterdam replicated Hermann Ebbinghaus' original forgetting curve.
What Is the Forgetting Curve?
The forgetting curve is a psychological phenomenon demonstrating that individuals retain less and less information over time without reinforcement. According to a 2015 PLOS One replication study, individuals forget more than 50% of new information within a single day and, without reinforcement, up to 79% within a month.
Annual training cycles schedule themselves directly into the steepest part of that curve. Compliance certificates end up issued to employees who can no longer recall the behaviors those certificates are supposed to represent.
Why Generic Cybersecurity Awareness Training Programs Destroy Engagement
Generic training assumes that a hospital nurse, a financial analyst, and a software engineer share the same threat exposure and the same learning context. They do not, and a cybersecurity awareness training platform that ignores those differences produces no behavioral signal.

When cybersecurity awareness training platforms present identical scenarios to all three roles, none of them recognize the content as relevant to their actual working day, and attention drops accordingly. That credibility gap reinforces the broader belief that cybersecurity is an IT department responsibility rather than a shared organizational one.
Adaptive Security delivers role-specific training that reflects each employee's existing threat profile.
What Microlearning Looks Like Inside a Modern Cybersecurity Awareness Training Platform
Microlearning addresses both the engagement gap and the forgetting curve simultaneously. Modules under 10 minutes, delivered at the moment a relevant behavioral signal occurs, create a direct link between the learning moment and the work context that triggered it.
Adaptive Security has microlearning built into the platform whenever an employee clicks a simulated phishing email. Calendar-driven training asks employees to learn about threats they have not recently encountered, while event-triggered microlearning delivers a short, targeted module within minutes of a near-miss decision.
Adaptive Security triggers microlearning automatically the moment an employee fails a phishing test.
Generic Content and the Personalization Gap in Cybersecurity Awareness Training Platforms
A cybersecurity awareness training platform that delivers the same generic phishing scenario to a software developer, a finance analyst, and a hospital receptionist treats all three as equally prepared because they clicked "complete." That uniformity does not build behavioral resistance; it builds the illusion of it.
Why Role-Specific Cybersecurity Awareness Training Platforms Produce Better Outcomes
Each role faces a structurally different cyberattack surface, and a cybersecurity awareness training platform must demonstrate the threat the employee will actually face.
Common role-based threat profiles in cybersecurity awareness training platforms include the following:
- Finance employees are the natural target for business email compromise (BEC), where cyberattackers impersonate vendors or executives to authorize fraudulent transfers;
- Software developers face supply chain social engineering, including fake pull request approvals and credential harvesting through fake CI/CD tool notifications;
- Non-technical staff are most vulnerable to authority-based phishing, including impersonations of IT helpdesk, HR, or payroll systems requesting credential resets. Presenting a developer with a wire-fraud scenario fails to rehearse the threat they will actually face.
Personalize every simulation to the employee's role, department, and access level with Adaptive Security.
How OSINT-Driven Personalization Strengthens Cybersecurity Awareness Training Platforms
Open-source intelligence (OSINT) is precisely how attackers identify and personalize attacks before launching them. Threat actors gather publicly available information from LinkedIn profiles, conference talks, GitHub repositories, and social media to build convincing lures.
Role-based phishing simulations built on OSINT ground a cybersecurity awareness training platform in truly malicious attacker behavior. A simulation referencing an employee's actual job title, recent conference appearance, or GitHub handle lands with the cognitive weight of a genuine attack.
What Compliance Frameworks Require From a Cybersecurity Awareness Training Platform
NIST SP 800-50r1, published in September 2024, explicitly requires role-based training plans tailored to functional organizational responsibilities. NIST CSF 2.0 codifies this further under control PR.AT-02, specifying that individuals in specialized roles must receive training matched to those responsibilities.
HIPAA, PCI-DSS, and ISO 27001 carry equivalent requirements for differentiated content by access level and job function.
A cybersecurity awareness training platform that cannot segment training delivery by role, access privilege, or department does not meet these frameworks at audit. It creates documented exposure that auditors can price.
Adaptive Security maps every training module to the specific compliance frameworks your business reports against.
Evolving Threats and Content Obsolescence in Cybersecurity Awareness Training Platforms

When a cybersecurity awareness training platform's content falls behind the actual threat landscape, employees are trained to recognize yesterday's attacks rather than the ones arriving in their inboxes today. Generative AI has compressed the attack development cycle from weeks to hours, making annual content refresh schedules structurally obsolete.
According to the Sumsub Identity Fraud Report 2024, deepfake fraud incidents surged 17 times year over year, with over 100,000 reported in the U.S. alone. Most cybersecurity awareness training platforms offer no deepfake simulation capability at all, leaving employees entirely untrained for attacks that are already common.
Why Cybersecurity Awareness Training Platform Content Goes Stale So Quickly
Legacy cybersecurity awareness training platform architectures were built around curated content libraries updated on quarterly or annual cycles. That cadence was calibrated for a threat landscape that evolved across months, while modern adversaries iterate within hours.

According to the CrowdStrike Global Threat Report 2025, vishing attacks rose 442% between the first and second halves of 2024. A module recorded six months ago may reference social engineering tactics that cyberattackers have already abandoned in favor of AI-cloned executive voice calls or real-time deepfake video fraud. That is precisely the method used to steal $25 million from Arup, a multinational firm, in Hong Kong in 2024.
Replace stale content with Adaptive Security's AI-powered simulations that update as the threat landscape shifts.
Why Email-Only Cybersecurity Awareness Training Platforms Leave Major Gaps
Most platforms confine phishing simulations to email, leaving vishing, smishing, and deepfake video entirely untested. An employee who passes 12 email phishing simulations has no rehearsed response when an AI-cloned voice of their CFO calls requesting an urgent wire transfer.
According to the CrowdStrike Global Threat Report 2025, 79% of cyberattack detections in 2024 were malware-free, signaling a decisive shift toward credential abuse and human-targeted intrusion methods that email-only platforms cannot rehearse.
How Generative AI Both Helps and Hurts Cybersecurity Awareness Training Platforms
Generative AI accelerates content production significantly. Training modules that previously took weeks to script, record, and localize can be generated in hours. The trade-off is real, however, because volume without expert review introduces risk.
AI-generated training content carries risks of factual inaccuracy, missing threat context, and scenarios disconnected from the specific attack vectors targeting a given industry or role. Without expert review and continuous threat intelligence integration, AI-generated content produces high volume at the cost of low fidelity.
Platforms that pair generative AI content engines with multi-channel phishing simulations, spanning email, voice, SMS, and deepfake video, close this gap far more effectively than content updates alone.
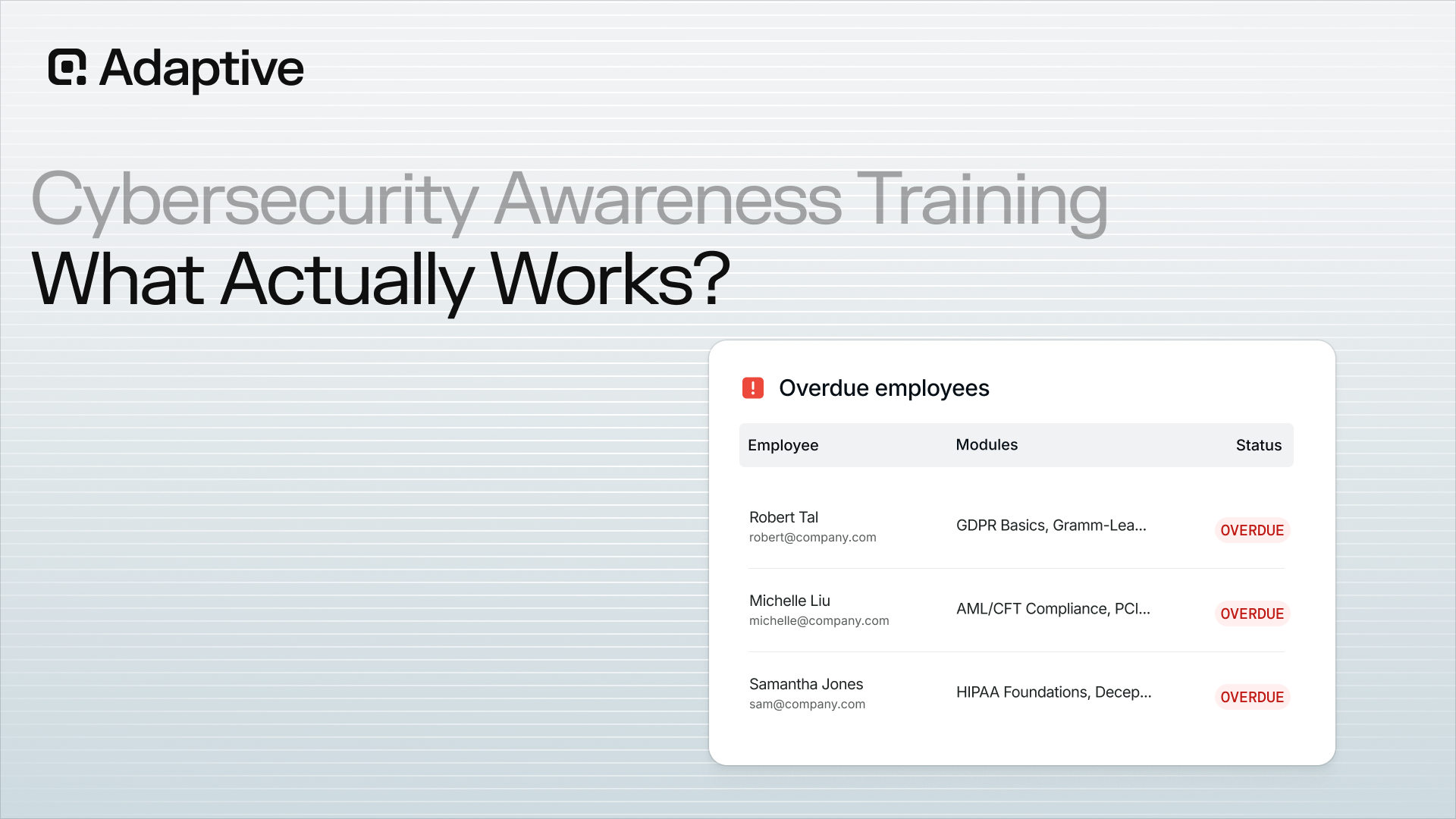
Measuring Effectiveness and Proving ROI on Cybersecurity Awareness Training Platforms
Cybersecurity awareness training platform challenges come into sharp focus when security leaders try to answer one deceptively simple question: is the training actually working? Completion rates and click-through rates have become the default metrics, yet both measure participation rather than behavior change.
Why Completion Rates Fail as Proxies for Cybersecurity Awareness Training Platform Effectiveness
A 95% completion rate tells security teams that employees opened a module. It says nothing about whether they recognized a spear phishing attempt three weeks later under deadline pressure. Click-through rates on simulations share the same blind spot.
A falling click rate over time could signal genuine vigilance, or it could mean employees have memorized the visual cues of test emails while remaining vulnerable to anything slightly different. Neither metric captures the decision-making instinct that determines whether an actual attack succeeds. Security culture, the default behavioral disposition employees bring to every interaction without prompting, is what actually reduces breach probability.
The metrics that track culture inside a cybersecurity awareness training platform include the following:
- Simulation click rate trends across rotating scenario types;
- Time-to-report for suspicious emails as a proxy for alertness;
- Training completion segmented by risk tier;
- Longitudinal risk score movement at the individual and department level.
Replace vanity metrics with risk score reporting your board can act on – Adaptive Security handles it for you.
What Hidden Costs Look Like Across Cybersecurity Awareness Training Platforms
A poorly implemented cybersecurity awareness training platform does not simply deliver weak ROI. It produces active costs that rarely appear in budget reviews.
Common hidden costs include the following:
- Wasted licenses accumulate when role-based targeting is absent and high-volume generic modules generate fatigue-driven disengagement;
- Compliance gaps emerge when training content is not mapped to the specific frameworks an audit requires;
- Undetected susceptibility grows silently when simulation cadence is too low or too narrow in channel coverage;
- Breach liability compounds each of these, as regulators and insurers increasingly treat documented training negligence as an aggravating factor in post-incident reviews.
With the above points in mind, poorly measured cybersecurity awareness training platform can shift from a budget concern into a liability the board can price.
Why Persistent Click Rates Signal a Diagnostic Failure
When phishing simulation click rates remain elevated despite repeated training cycles, the instinct to increase simulation frequency often worsens the outcome. Over-simulation without scenario variation or personalized follow-up produces resentment rather than vigilance.
Employees begin to perceive every internal communication as a test, eroding the trust that makes incident reporting functional. The correct response is diagnosis. Identify which role segments, departments, or simulation types are driving the persistent risk, then deploy targeted human risk monitoring and mitigation.
Building a defensible ROI case means translating risk score reduction into avoided breach cost. That framing shifts cybersecurity awareness training platform spend from a compliance line item into a risk-adjusted investment, which is the conversation that protects budget in a downturn.
See how Adaptive Security cybersecurity awareness training turns behavioral signals into measurable ROI.
Administrative Burden and Deployment Friction in Cybersecurity Awareness Training Platforms
Cybersecurity awareness training platform challenges extend well beyond content quality. The operational weight of running a program often overwhelms the teams responsible for it. Manual enrollment, content curation, compliance documentation, and simulation scheduling consume hours that security teams do not have.
According to the SANS Security Awareness Report 2024, the most mature awareness programs average 4.18 dedicated full-time employees to sustain operations. That is a resource level most organizations cannot meet, especially at small and mid-sized businesses.
How Access Friction Reduces Participation in a Cybersecurity Awareness Training Platform
Participation drops when training requires effort to reach. Separate login portals, platforms without single sign-on (SSO), and poor mobile experiences all create friction that employees, especially remote and hybrid workers, simply route around.
Friction points that systematically reduce participation include the following:
- Separate credential sets that force employees out of their daily workflow;
- Mobile experiences that fail to render core training modules;
- Manual enrollment that delays training delivery for new hires;
- Notification systems that bury training reminders inside generic email blasts.
Platforms that integrate natively with Microsoft 365 or Google Workspace, authenticate through existing SSO, and render fully on mobile remove every procedural excuse not to complete a module. Adaptive Security's integrations deploy via two-click Microsoft 365 or Google Workspace connection.
Why Remote and Hybrid Environments Strain Traditional Cybersecurity Awareness Training Platforms
Distributed teams remove the passive reinforcement channels (posters, in-person briefings, desk drops) that traditionally supported security culture. Device diversity compounds the problem.
Employees on personal laptops, shared workstations, and mobile devices encounter inconsistent training delivery when cybersecurity awareness training platforms are not built for multi-device, cloud-native access. Without consistent access and automated enrollment triggers, coverage gaps grow silently.
Roll out training across every device and location with Adaptive Security's instantaneous two-click deployment.
How Resource-Constrained Teams Run Effective Cybersecurity Awareness Training Programs
Small and mid-sized businesses face this challenge acutely. They have no dedicated security awareness manager, limited IT staff, and a per-seat budget that cannot absorb expensive customization projects.
Automation solves this problem. Cybersecurity awareness training platforms that handle enrollment based on HRIS data, trigger microlearning after a failed simulation, and generate audit-ready compliance reports without manual input remove the staffing dependency entirely.
Multilingual coverage is a related gap. Legacy cybersecurity awareness training platforms frequently list languages they nominally support but deliver only machine-translated content with no cultural localization, which is a failure point for globally distributed workforces. Genuine multilingual programs require localized scenarios, regional threat examples, and culturally adapted messaging.
How To Build Executive Buy-In for a Cybersecurity Awareness Training Platform Budget

Boards do not fund training programs; they fund risk reduction. Framing a cybersecurity awareness training platform investment against quantified breach exposure converts an IT line item into a financial hedge.
Concrete metrics matter when presenting to the board. Present current phishing simulation click rates, projected reduction curves with consistent training, and estimated cost per avoided incident. Board-level dashboards that translate employee risk scores into business exposure figures close the credibility gap between security operations and executive decision-making.
What To Look for in a Modern Cybersecurity Awareness Training Platform
Selecting the right cybersecurity awareness training platform requires evaluating capabilities across simulation coverage, personalization, risk intelligence, and reporting. The gap between a static SAT tool and a full human risk management platform determines whether the program produces behavioral change or only completion certificates.
1. Confirm Multi-Channel Simulation Coverage Across the Cybersecurity Awareness Training Platform
The cyberattack surface has expanded well beyond email. According to the CrowdStrike Global Threat Report 2025, large language models now produce phishing emails that achieve a 54% click-through rate compared to 12% for human-written attempts.
Modern variants include vishing, smishing, and deepfake video calls, none of which legacy email-only platforms can simulate. A cybersecurity awareness training platform that tests employees across email spear phishing, AI voice calls, SMS lures, and deepfake executive video covers the channels attackers actually use.
Run simulations across every channel attackers use, including AI-cloned voice and deepfake video with Adaptive Security.
2. Prioritize Cybersecurity Awareness Training Platform Delivery by Risk Tier
Enrollment logic built on job titles alone misses the threat exposure picture. Different functions carry different exposure profiles, and a cybersecurity awareness training platform should reflect that.
Examples of role-specific risk concentration include the following:
- Finance teams face business email compromise (BEC) and invoice fraud;
- IT administrators are targeted through fake credential resets;
- Executives carry OSINT exposure visible to any attacker with a LinkedIn account.
Platforms that combine simulation results, OSINT profiling, and behavioral signals to produce individual and department-level risk scores allow security leaders to direct the most intensive training to the employees who need it most. Human risk scoring that updates dynamically after each simulation or training event gives security teams a live picture of where exposure is concentrated.
3. Understand the Cybersecurity Awareness Training Platform vs. Human Risk Management Distinction
A security awareness training platform delivers content. A human risk management platform also measures whether that content changes behavior, and that distinction matters most at program maturity stages where security leaders need to justify budget.
Completion rate data satisfies a compliance checkbox, while a risk score that drops, say 40% over two quarters, justifies the investment and drives board-level conversation. Organizations buying for compliance baseline can start with SAT, while organizations accountable for measurable risk reduction need the full human risk management architecture.
Phishing simulations deliver the most value when paired with real-time behavioral data. Simulation clicks feed directly into risk scores, which trigger targeted microlearning automatically rather than waiting for the next scheduled training cycle.
4. Verify Compliance Mapping and Reporting Inside the Cybersecurity Awareness Training Platform
Training content must map to the specific frameworks the organization is accountable for. SOC 2, HIPAA, PCI-DSS, GDPR, ISO 27001, and NIST CSF each carry distinct documentation requirements.
Platforms with automated phish triage that includes AI confidence scoring reduce analyst workload while generating audit-ready evidence. Board-ready dashboards that translate human risk scores into business metrics, rather than raw click rates, give CISOs the language they need to make the security case at the executive level.
Replace manual phish triage with AI confidence scoring and automated evidence capture from Adaptive Security.
From Awareness to Behavioral Change: The Human Risk Management Shift
Human risk management marks the point where cybersecurity awareness training platform challenges stop being a tooling problem and become an organizational measurement problem. It is a framework for continuously monitoring behavioral signals to produce a dynamic picture of how likely each employee is to become an attack vector.
Inputs that feed a human risk management model include simulation response rates, training completion, OSINT exposure, and credential breach history. Unlike awareness training, which measures whether someone watched a module, human risk management measures whether that person's behavior actually changed.
Why Awareness Metrics Alone Cannot Quantify Cybersecurity Awareness Training Platform Risk
Completion percentages are activity logs rather than risk data. An employee who finished a 10-minute phishing module in January and clicked a credential-harvesting link in March has a 100% completion rate and a documented breach contribution.
According to the ENISA Threat Landscape 2024, phishing remains a primary initial access vector across European incidents, with social engineering campaigns increasingly augmented by generative AI and deepfake audio. That reality signals a measurement gap inside most cybersecurity awareness training platforms: organizations are counting activity when they should be tracking behavior change.
Why Boards Demand Risk Reporting From Cybersecurity Awareness Training Platforms
Boards ask about exposure and liability rather than module completion. A CISO presenting training completion rates to an audit committee is answering a question nobody asked.
Human risk management frameworks translate behavioral signal data into the quantified risk language that governance conversations require. Inputs include click rates on simulations, time-to-report on suspected phishing, and OSINT-derived executive exposure scores.
Organizations that make this shift treat security awareness as a program outcome with measurable risk reduction, rather than a compliance checkbox with a timestamp.
Move beyond completion rates and quantify human risk at the individual and department level using Adaptive Security.
Future Trends Shaping Cybersecurity Awareness Training Platforms
The next wave of cybersecurity awareness training platform development will be driven by threats and regulatory pressures that most organizations are only beginning to account for. The trends below represent where the category is heading, and where legacy platforms will fall furthest behind.
Agentic AI Attacks Will Require a New Class of Cybersecurity Awareness Training Platform Simulations
Agentic AI refers to autonomous systems capable of executing multi-step attack sequences without direct human involvement. Where today's social engineering attacks require a threat actor to craft a lure with AI and wait for a response, agentic systems can conduct reconnaissance, initiate contact, adapt messaging based on replies, and escalate to credential harvesting across an entire conversation chain, all without a human attacker in the loop.
Cybersecurity awareness training platforms built around static scenario libraries have no mechanism to simulate this. Training employees to recognize a single suspicious email does not prepare them for an autonomous agent that sustains a believable professional exchange over days before requesting access credentials.
Cybersecurity awareness training platforms will need dynamic, adaptive simulation engines that can replicate multi-turn agentic interactions to close this gap.
Regulatory Frameworks Will Make Cybersecurity Awareness Training Platform Accountability Non-Negotiable
The compliance dimension of cybersecurity awareness training is tightening significantly. The EU's NIS2 Directive, which came into force in October 2024, explicitly requires organizations to implement employee cybersecurity awareness training measures as part of their broader cyber risk management obligations, with board-level accountability attached.
The SEC's cybersecurity disclosure rules similarly require publicly listed organizations to disclose material cyber incidents and describe their risk management practices, which increasingly includes training program governance. Emerging AI liability frameworks in both the EU and the U.S. are beginning to treat inadequate human oversight training as an organizational liability in AI-assisted breach scenarios.
Organizations that treat cybersecurity awareness training platform selection as a purely operational decision are underestimating how quickly it is becoming a governance and legal one.
Cross-Channel Attack Chains Will Demand Coordinated Cybersecurity Awareness Training Platform Coverage
Most organizations today simulate single-channel attacks in isolation. A phishing simulation tests email. A vishing drill tests voice. These isolated tests do not reflect how sophisticated cyberattackers now operate.
Coordinated multi-vector attack chains, in which an employee receives a convincing email, a follow-up SMS, and an AI-cloned voice call within the same attack sequence, are increasingly documented in enterprise breach reports.
Cybersecurity awareness training platforms will need to simulate these coordinated sequences to build the pattern recognition employees need to identify an attack that spans multiple channels simultaneously. A workforce trained to spot each channel in isolation remains vulnerable to the coordinated sequence.
See how Adaptive Security is built for what's coming, not just what's here.
How Adaptive Security Solves Every Cybersecurity Awareness Training Platform Challenge
The challenges covered throughout this article (static content, single-channel simulations, and metrics that measure activity instead of risk) persist because most platforms were not architected to solve them. Adaptive Security was built specifically to close those gaps with an AI-native approach that addresses each structural weakness in legacy cybersecurity awareness training platforms.
Adaptive Security delivers AI-powered phishing simulations across emails, calls, SMS, and deepfake videos, rehearsing the full attack surface that cyberattackers now use. Microlearning modules trigger automatically the moment an employee clicks a simulated lure, anchoring the lesson to the exact behavioral context that prompted it, which answers the forgetting curve problem that calendar-driven training cannot solve.
Beyond simulation and training, Adaptive Security provides: dynamic human risk scoring that updates after each behavioral event, phish triage that uses AI confidence scoring to reduce analyst workload, and compliance reporting mapped to SOC 2, HIPAA, PCI-DSS, GDPR, ISO 27001, and NIST CSF. Two-click Microsoft 365 or Google Workspace deployment removes the administrative burden that consumes the 4.18 average FTEs cited in the SANS Security Awareness Report 2024.
Security leaders evaluating modern cybersecurity awareness training platforms should expect a single admin interface that consolidates security awareness training, phishing simulations, phish triage, and risk monitoring. That consolidation eliminates duplicate vendor management, removes data gaps between tools, and gives CISOs the board-ready reporting they need to translate behavior change into quantified risk reduction.
See how Adaptive Security's AI-native cybersecurity awareness training platform can replace every legacy tool in one workflow.
Frequently Asked Questions About Cybersecurity Awareness Training Platforms
What Are the Biggest Challenges of Cybersecurity Awareness Training Platforms?
The biggest cybersecurity awareness training platform challenges are low employee engagement, the Ebbinghaus forgetting curve, generic one-size-fits-all content, rapidly evolving threats that outpace annual content cycles, difficulty measuring behavioral outcomes, and excessive administrative burden on IT teams.
These are not isolated product failures. They reflect structural limitations in how legacy platforms were designed, built around compliance checkboxes rather than behavioral change. Organizations that recognize this gap are shifting toward continuous, behavior-triggered programs that measure risk reduction.
Why Are Annual Cybersecurity Awareness Training Programs No Longer Sufficient?
Annual cybersecurity awareness training is no longer sufficient because the human forgetting curve erases most knowledge retention within days of a single training session. Threat actors now operate on timescales of hours rather than months, while annual content cycles run on calendar years.
According to the CrowdStrike Global Threat Report 2025, the average breakout time for adversaries dropped to 48 minutes in 2024, with the fastest observed breakout taking only 51 seconds. AI-generated phishing emails, deepfake impersonation, and smishing attacks have compressed attack development cycles to the point where content updated once a year is structurally obsolete before the year ends.
Effective programs treat training as a continuous process, delivering short, behavior-triggered modules tied to threat signals rather than calendar dates.
How to Measure the Effectiveness of a Cybersecurity Awareness Training Platform?
Measuring the effectiveness of a cybersecurity awareness training platform requires moving beyond completion rates and phishing simulation click rates to track behavioral outcomes over time. Meaningful metrics include the following:
- Simulation click rate trend, measured as directional improvement over 90-day rolling periods;
- Time-to-report suspicious emails, where faster reporting indicates internalized behavior;
- Training completion by risk tier, where high-risk employees complete relevant training at higher rates than baseline;
- Risk score change at the individual and department level following targeted interventions;
- Phish triage resolution time, measuring SOC response speed enabled by employee reporting quality.
Completion rates confirm that employees sat through training. They say nothing about whether behavior changed.
What Is the Difference Between a Security Awareness Training Platform and a Human Risk Management Platform?
A security awareness training platform delivers educational content and phishing simulations to employees, then reports on completion and click rates. A human risk management platform measures behavioral signals continuously, including simulation response, training engagement, OSINT exposure, and credential breach history.
The practical difference is visibility. Awareness training tells security leaders what employees watched, while human risk management tells them who is most likely to be successfully attacked and why. For organizations that need to report to boards on human-layer risk posture rather than training activity logs, the distinction matters significantly.
How Can Organizations Overcome Low Engagement in a Cybersecurity Awareness Training Program?
Organizations overcome low engagement in a cybersecurity awareness training program by replacing long, infrequent, generic sessions with short, role-relevant, behavior-triggered interventions delivered at the moment of relevance.
According to the SANS Security Awareness Report 2024, 89% of security awareness practitioners identify social engineering as the most salient human risk in the threat landscape. Microlearning modules under 10 minutes, tied to a recent simulation interaction or threat event, consistently outperform annual training in both completion rates and knowledge retention. Content personalization is equally important, since a finance team member facing business email compromise (BEC) scenarios and a software developer facing credential phishing attacks have different threat models.
Employees engage when training feels credible, specific to their actual role, and connected to the actual consequences of the threats they face.
Replace annual training with behavior-triggered microlearning that lands as soon as your employees fail a phishing simulation.
Key Takeaways of Cybersecurity Awareness Training Platform Challenges
- Legacy cybersecurity awareness training platforms measure participation rather than behavior change.
- The forgetting curve makes annual cybersecurity training structurally obsolete, with the PLOS One replication study 2015 showing up to 79% of new information lost within a month without reinforcement.
- Generic content fails role-specific threat profiles, and frameworks including NIST SP 800-50r1, HIPAA, PCI-DSS, and ISO 27001 now require role-based training to satisfy audit.
- Email-only phishing simulations leave employees untrained for vishing and deepfake attacks, which the CrowdStrike Global Threat Report 2025 documented rising 442% in the second half of 2024.
- Generative AI accelerates both attacker capability and content production, with LLM-generated phishing achieving a 54% click-through rate compared to 12% for human-written attempts.
- Administrative burden cripples program impact, with the SANS Security Awareness Report 2024 finding that mature programs require 4.18 average dedicated FTEs to operate effectively.
- Human risk management replaces vanity metrics with quantified behavioral signals that translate directly into board-ready risk reduction reporting.
Adaptive Security solves every cybersecurity awareness training challenge covered here; only a click away.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents