A cybersecurity awareness training platform delivers the structured security education, phishing simulations, and behavioral risk measurement employees need to detect and stop social engineering cyberattacks before they escalate into incidents.

According to Verizon's Data Breach Investigations Report (2025), 60% of breaches involve a human element. A cybersecurity awareness training platform deployment that generates completion records without changing behavior is, effectively, no deployment at all. This guide covers:
- How to evaluate and select a cybersecurity awareness training platform built for today's threat environment;
- How to resolve the technical prerequisites required before any cybersecurity awareness training platform deployment goes live;
- How to structure a phased cybersecurity awareness training platform deployment by role, department, and organization size;
- How to run phishing simulations and measure cybersecurity awareness training platform deployment outcomes in terms boards and compliance auditors can act on;
- How cybersecurity awareness training platform deployment supports regulatory compliance across HIPAA, GDPR, PCI-DSS, and related frameworks.
Threats now extend well beyond email phishing to vishing, smishing, deepfake video impersonation, and AI-generated spear phishing. Cybersecurity awareness training platform deployment practices must match that scope.
Adaptive Security puts human risk reduction on a measurable trajectory from day one.
What Is a Cybersecurity Awareness Training Platform and Why Deployment Matters
A cybersecurity awareness training platform is used by organizations to deliver role-based security education, phishing simulations, behavioral risk measurement, and compliance reporting across their workforce. These platforms exist to close the gap between technical security controls and human behavior: the layer where most breaches originate. The critical distinction that determines program outcomes is how rigorously cybersecurity awareness training platform deployment is executed across roles, channels, and threat scenarios.
Legacy Compliance Platforms vs. Modern Cybersecurity Awareness Training Platforms
Legacy cybersecurity awareness training platforms were engineered for a narrower threat landscape. Annual cybersecurity awareness training modules, generic phishing email tests, and completion-rate dashboards satisfied regulatory checkboxes. They were designed for an era when a phishing cyberattack meant a suspicious link in a poorly formatted email.
Modern cybersecurity awareness training platforms are built to simulate and train against the full range of AI-era cyberattack vectors:
- Generative AI spear phishing;
- Deepfake video impersonation;
- Vishing (AI-cloned executive voices);
- Smishing (SMS-based social engineering).
A cybersecurity awareness training platform that only tests email phishing leaves every employee untrained against the cyberattack types that now account for the fastest-growing share of social engineering incidents.
What Threats a Modern Cybersecurity Awareness Training Platform Must Address
The threat surface that a cybersecurity awareness training platform must cover extends well beyond email. Phishing remains the dominant initial access vector, but business email compromise (BEC), which exploits trusted relationships rather than malicious links, demands a separate simulation discipline.

Vishing cyberattacks use AI-cloned executive voices to manufacture urgency over phone calls. Smishing delivers social engineering via SMS, bypassing email filters entirely. Deepfake video calls now enable cyberattackers to impersonate CFOs, legal counsel, or IT administrators in real time. This was demonstrated when an Arup finance employee transferred $25 million after joining a video call in which every participant was AI-generated. Effective phishing simulations within a cybersecurity awareness training platform must replicate all of these vectors.
Why Deployment Quality Determines Cybersecurity Awareness Training Platform Outcomes
An organization that licenses a modern cybersecurity awareness training platform but rolls it out with generic training assignments, infrequent simulations, and no role-based targeting will see negligible behavior change.
According to Verizon's Data Breach Investigations Report (2025), third-party involvement in breaches reached 30%, and credential abuse remains one of the leading initial access vectors at 22%. Getting cybersecurity awareness training platform deployment right is the primary variable between a program that reduces breach risk and one that produces only audit documentation.
See what a properly executed cybersecurity awareness training platform deployment looks like with Adaptive Security.
How to Choose the Right Cybersecurity Awareness Training Platform for Deployment
Selecting a cybersecurity awareness training platform is a risk management decision. According to IBM's Cost of a Data Breach Report (2025), the average data breach costs $4.44 million. The evaluation criteria used during cybersecurity awareness training platform deployment directly determine whether an organization materially reduces exposure or just generates the illusion of doing so.
Evaluate cybersecurity awareness training platforms across eight dimensions before signing a contract:
- Threat coverage across all social engineering channels;
- Content quality, recency, and role specificity;
- Integration compatibility with existing identity and directory systems;
- Simulation realism, including OSINT-powered personalization;
- Compliance support mapped to relevant regulatory frameworks;
- Analytics depth for human risk scoring and behavioral tracking;
- Administrative overhead and ease of ongoing management;
- Vendor onboarding quality and time-to-value benchmarks.
The most consequential distinction to draw early is whether a cybersecurity awareness training platform is built for compliance theater or genuine behavior change. That architectural choice determines ROI.
1. Confirm Threat Coverage Spans Every Attack Channel
Email-only phishing simulations do not reflect how cyberattackers operate. Modern social engineering campaigns coordinate across email, voice calls (vishing), SMS (smishing), and deepfake video. This leaves the majority of workforces untrained on some of the fastest-growing cyberattack vectors. Require vendors to demonstrate live simulations across all four channels before any cybersecurity awareness training platform deployment conversation advances.
2. Evaluate Content Quality, Recency, and Role Specificity
Most legacy cybersecurity awareness training platforms rely on generic annual compliance modules that fail to change behavior. Finance teams face invoice fraud and wire transfer scams. IT staff face credential-reset impersonations. Executives face deepfake video calls and executive impersonation. Cybersecurity awareness training platforms built on role-specific, continuously updated content are the only ones capable of keeping pace with AI-generated cyber threats that evolve weekly.
3. Verify Integration Compatibility and SCORM Support
A cybersecurity awareness training platform that requires manual user provisioning adds friction that undermines adoption at scale. Confirm native compatibility with Microsoft 365, Google Workspace, HRIS systems, and SSO providers (including Okta) before deployment begins. Review Adaptive Security's integration options as a benchmark for what native, two-click connectivity looks like in practice. SCORM compliance matters for organizations running an existing LMS. Without it, training completion data stays siloed outside the cybersecurity awareness training platform.
4. Assess Simulation Realism and OSINT-Powered Personalization
Phishing simulations that use generic sender names and template email copy do not train employees to recognize actual cyberattacks. Effective cybersecurity awareness training platforms use open-source intelligence (OSINT) to build personalized spear phishing scenarios drawn from employees' public digital footprints, job titles, LinkedIn activity, and organizational structure. Vishing and deepfake simulations should clone real executive voices and faces, because that is the exact technique cyberattackers deploy.
5. Confirm Compliance Framework Coverage and Reporting Depth
Any cybersecurity awareness training platform selected must produce audit-ready documentation mapped to the frameworks the organization is accountable to. SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 are the most common. Board-ready dashboards that translate training completion and risk score trends into business-language metrics are non-negotiable for CISOs who must justify human risk investment at the executive level.
Explore Adaptive Security's compliance reporting capabilities before committing to a cybersecurity awareness training platform deployment.
Technical Prerequisites Every Organization Must Resolve Before Cybersecurity Awareness Training Platform Deployment
Cybersecurity awareness training platform deployment fails at the technical layer before it ever reaches an employee. Completing the right groundwork determines whether simulation data reflects real employee behavior or noise. The four areas that must be resolved are: allowlisting, directory synchronization, identity integration, and API-based connectivity. Assign ownership across IT, security, and communications before touching the platform console.
1. Configure Allowlisting Before Sending a Single Simulation
Allowlisting is the step most teams skip and most often regret. When simulated phishing emails pass through an organization's email security gateway without being explicitly permitted, automated security scanners pre-click embedded links before the message reaches an employee's inbox. Those automated clicks register as employee interactions in the cybersecurity awareness training platform reporting dashboard, inflating click rates and making the workforce appear far more susceptible than it actually is.
Work with IT to add the platform's sending IP addresses, domains, and mail headers to the allowlist in Microsoft Defender for Office 365, Google Workspace spam filters, or any third-party secure email gateway in the mail flow path. Validate allowlisting before launch by sending a test simulation to a small pilot group. Confirm zero bot-click signatures appear in the cybersecurity awareness training platform results before proceeding.
2. Sync Directory for Accurate User Provisioning
Accurate user data is the foundation of role-based training assignments on a cybersecurity awareness training platform. Connect the platform to Active Directory, a SCIM-compatible identity provider, or an HRIS system. Employee records, including department, role, and manager, must populate automatically and stay current as the org chart changes.
Manual user management creates two compounding problems:
- Departed employees remain enrolled in training;
- New hires miss their onboarding assignments.
Automated directory sync, like the HRIS and SCIM integrations supported by modern cybersecurity awareness training platforms,54w eliminates both failure modes without ongoing IT intervention.
3. Connect SSO and Identity Providers for Frictionless Employee Access
Single sign-on (SSO) integration with Okta, Azure Active Directory, or Google Workspace removes password friction that suppresses cybersecurity awareness training platform completion rates. Employees who must create a separate login routinely abandon the enrollment flow. That technical barrier creates a false picture of program adoption that obscures real participation gaps.
4. Use API-Based Connection for Microsoft 365 and Google Workspace
Modern cybersecurity awareness training platforms connect to Microsoft 365 and Google Workspace via API, not MX record changes. MX record modifications reroute all inbound mail through new infrastructure, introducing delivery risk and requiring extended change-management cycles. An API-based connection reads mailbox data and injects simulations directly, going live in minutes with no mail flow disruption.
5. Define Internal Roles Before Launch Day
Three internal roles must be confirmed before cybersecurity awareness training platform deployment begins:
- A program owner who holds accountability for training completion rates and simulation scheduling;
- An IT contact who owns allowlisting, directory sync, and SSO, and serves as the escalation point when configurations drift;
- A communications lead who manages the internal announcement strategy, framing the program as a skill-building initiative rather than a surveillance exercise.
Teams that leave these roles undefined arrive at launch day with no one authorized to approve the first simulation send and no one to fix a broken SCIM connection. The resulting delays introduce data gaps that undermine baseline measurements for the entire cybersecurity awareness training platform deployment.
How to Structure a Phased Cybersecurity Awareness Training Platform Deployment Rollout
A successful cybersecurity awareness training platform deployment follows four sequential phases:
- Establish a baseline before any training goes live;
- Prepare the workforce through targeted internal communication;
- Segment the rollout by role and department;
- Calibrate deployment for the organization's scale.
Each phase of a cybersecurity awareness training platform depends on the output of the one before it. Skipping the baseline means there is no benchmark against which to measure behavioral change. Point-of-failure education and post-click training reinforce the live cybersecurity awareness training program throughout, turning simulation failures into immediate learning moments rather than missed signals.
Phase 1: Run a Baseline Before Cybersecurity Awareness Training Platform Deployment Goes Live
A baseline phishing simulation is a controlled test sent to all employees before any cybersecurity awareness training program content is deployed. Its purpose is to measure the organization's true starting vulnerability so that every subsequent metric has a reference point.
Use the baseline result to categorize exposure by team, role, and seniority. Finance staff clicking at 40% warrant different prioritization than an IT team clicking at 12%.
The baseline also sets the program's credibility with leadership. A 28% click rate falling to 6% after 12 months of consistent simulation and training is a board-level outcome.
Run a baseline phishing simulation automatically with Adaptive Security before a single training module goes live.
Phase 2: Internal Communication and Cybersecurity Awareness Training Preparation

Employees perform better throughout a cybersecurity awareness training program when they understand its purpose before the first simulation lands. Announce the cybersecurity awareness training program before launch, but do not disclose simulation timing or templates. The goal is to build context, not coach employees to scrutinize their inboxes on one specific day.
The communication strategy should span multiple channels:
- An all-hands email from the CISO or CEO framing the program as a skills initiative;
- A brief Slack or Teams message from department leads reinforcing the same message;
- A short FAQ addressing the "why now" question directly.
Every message should position employees as the organization's strongest line of defense against AI-powered cyberattacks. Cybersecurity awareness training programs that frame employees as liabilities see lower voluntary reporting rates and higher disengagement. Launch internal communications two to three weeks before the first simulation wave.
Phase 3: Segmented Cybersecurity Awareness Training Platform Deployment by Role and Department
Role-based targeting is the mechanism that determines whether cybersecurity awareness training platform deployment actually changes behavior. Generic, all-employee modules create awareness. Scenarios matched to a person's actual threat exposure build the instincts needed to stop a cyberattack.

Phishing simulations built on Smart Groups allow administrators to assign distinct simulation tracks without manual list management. Smart Groups are automatically-managed user collections organized by predefined criteria (such as department, role, or job function), eliminating the need for manual list maintenance. For example:
- Finance teams should receive BEC and wire fraud scenarios. According to FBI's IC3 Annual Report (2024), BEC losses approached $2.8 billion in 2024 alone;
- Executives receive deepfake video and vishing simulations reflecting the impersonation risk specific to their profiles;
- IT staff work through advanced social engineering modules covering credential harvesting, help desk pretexting, and multi-step cyberattack chains.
For large or geographically distributed teams, staggering cybersecurity awareness training platform deployment by department over four to six weeks prevents administrative capacity from becoming a bottleneck. It also ensures simulation traffic does not trigger spam filters or alert employees before their cohort launches.
Phase 4: Enterprise vs. SMB Cybersecurity Awareness Training Platform Deployment Differences
Cybersecurity awareness training platform deployment complexity scales non-linearly with headcount. A 200-person organization can complete initial setup, baseline simulation, and a first training wave within two weeks. A 5,000-employee enterprise requires HRIS synchronization, role-taxonomy mapping, executive reporting configuration, and often multi-region compliance considerations. That full cybersecurity awareness training platform deployment realistically spans six to twelve weeks.
Integration depth differs significantly between the two:
- Enterprise deployments typically connect to Okta, Workday, or ServiceNow for automated user provisioning;
- SMB deployments more often rely on a direct Microsoft 365 or Google Workspace sync that takes minutes to configure.
Enterprises generally assign a dedicated cybersecurity awareness training program manager. SMBs typically run the program through a shared IT role alongside other responsibilities. In an enterprise, post-click remediation training routes automatically to the employee who clicked, regardless of which cohort they were in, keeping the learning cycle tight without requiring manual intervention from the security team.
How Phishing Simulations and Point-of-Failure Training Drive Behavioral Change After Cybersecurity Awareness Training Platform Deployment
Cybersecurity awareness training platform deployment produces measurable behavioral change only when simulations move beyond static email tests. Cybersecurity awareness training platforms that run multi-channel simulations, covering spear phishing emails, vishing calls, smishing texts, and deepfake video, expose employees to the actual threat vectors cyberattackers use today.
What Simulation Types Should a Cybersecurity Awareness Training Platform Cover?
Effective cybersecurity awareness training platforms build phishing simulations across four channels:
- Email spear phishing personalized using open-source intelligence (OSINT);
- Vishing calls that replicate AI-cloned executive voices;
- Smishing texts mimicking vendor alerts or IT notifications;
- Deepfake video that impersonates company leadership in real time.
OSINT personalization makes each scenario specific to the employee, using job title, manager's name, recent company announcements, or publicly visible data to construct scenarios cyberattackers would realistically build. Employees must now recognize AI-generated authority, not just suspicious formatting.
What Is Point-of-Failure Education and Why Does Timing Matter in Cybersecurity Awareness Training?
Point-of-failure education is microlearning triggered right at the moment an employee clicks a simulated phishing link, submits credentials, or fails a cybersecurity awareness training platform simulation. It fires immediately, not hours or days later.
In cybersecurity awareness training, that window is decisive. An employee who receives a two-minute explainer about spear phishing the moment they click a simulation link processes the lesson while the mistake is still emotionally salient. That is the highest-leverage moment for rewiring behavior.
Adaptive Security's point-of-failure education turns every simulation mistake into a real-time learning moment.
What Click-Rate Benchmarks Should Organizations Target After Cybersecurity Awareness Training Platform Deployment?
Well-run programs target a phishing simulation click rate below 5% within 12 months of cybersecurity awareness training platform deployment. Organizations that run simulations only once or twice per year show minimal behavior change. Those exposed monthly internalize detection instincts across cyberattack types. Consistent simulation rotating across email, voice, and deepfake vectors on a monthly or quarterly cadence is what drives sustained decline.
How Should Teams Handle Employees Who Repeatedly Fail Cybersecurity Awareness Training Platform Simulations?
Repeated simulation failures signal a skills gap that standard microlearning alone will not close. The response should escalate proportionally:
- A second failure within a defined window triggers enrollment in a targeted security awareness training module matched to the simulation type: credential phishing, vishing, or executive impersonation;
- A third failure brings the manager into a structured conversation, with HR involvement documented for compliance purposes.
This escalation path treats persistent risk as an organizational signal. It gives security teams the audit trail regulators expect from a well-governed cybersecurity awareness training platform deployment.
How to Keep Employees Engaged and Prevent Awareness Fatigue After Cybersecurity Awareness Training Platform Launch
Sustaining engagement is where cybersecurity awareness training platform deployment most often stalls. The initial launch generates participation. Without deliberate design choices around format, cadence, relevance, and variety, completion rates decline and employees treat training as background noise within months.
1. Replace Annual Modules With Monthly Microlearning on the Cybersecurity Awareness Training Platform
Session length is one of the most controllable variables in cybersecurity awareness training platform completion and retention rates. According to the SANS Security Awareness Report (2025), drawing insights from over 2,700 security awareness practitioners across 70+ countries, sustained program effort over time is what drives behavior change. The longer a program has been in place, the more likely it is to reduce human risk.
Modules capped under 10 minutes align with how adults process and retain new information. Monthly touchpoints sustain recall between simulations and give employees enough repetition to build genuine instinct.
2. Build Role-Specific Cybersecurity Awareness Training Content
An employee disengages the moment a cybersecurity awareness training platform module describes a scenario that has nothing to do with their role. A finance team member processing invoices faces a fundamentally different threat profile than an engineer with privileged system access.
Aligning security awareness training content to role-specific risks converts training from a passive viewing exercise into active skill-building:
- Invoice fraud and wire transfer scams for accounts payable;
- Credential-reset vishing scenarios for IT staff;
- Executive impersonation simulations for executive assistants.
3. Use Gamification to Reinforce Cybersecurity Awareness Training Without Trivializing It
Leaderboards, progress tracking, and recognition mechanics increase cybersecurity awareness training platform participation when applied to meaningful metrics: simulation reporting rates, completion streaks, and risk score improvements, rather than superficial points. The goal is to signal that security behavior is noticed and valued. Organizations that publicly recognize employees who correctly flag phishing simulations create positive reinforcement loops that keep the entire workforce alert.
4. Rotate Themes and Channels to Prevent Cybersecurity Awareness Training Habituation
Awareness fatigue sets in when employees see the same simulation format repeatedly. A workforce that has received 12 consecutive email phishing tests will pattern-match on format rather than content. They will miss a vishing call or deepfake video request entirely. Quarterly rotation across channels and themes resets attentiveness and builds multi-channel recognition skills:
- Channels: email, SMS smishing, voice vishing, deepfake video;
- Themes: credential harvesting, invoice fraud, vendor impersonation, executive urgency.
5. Use AI Content Generation to Keep Cybersecurity Awareness Training Current
The velocity problem is real: cyber threat actors iterate cyberattack methods in hours while most cybersecurity awareness training platform content libraries update quarterly or annually. Adaptive Security's AI Content Studio allows program managers to generate new training modules from a prompt, an internal policy document, or a recently observed cyber threat pattern in minutes. This eliminates the wait for a vendor's content release cycle. When a new BEC variant surfaces or a regulatory requirement changes, the program adapts immediately rather than leaving a gap between emerging threat and employee awareness.
Stop letting your cybersecurity awareness training library fall behind the threat landscape. Adaptive Security's AI Content Studio closes the gap.
How to Measure Cybersecurity Awareness Training Effectiveness and Calculate ROI
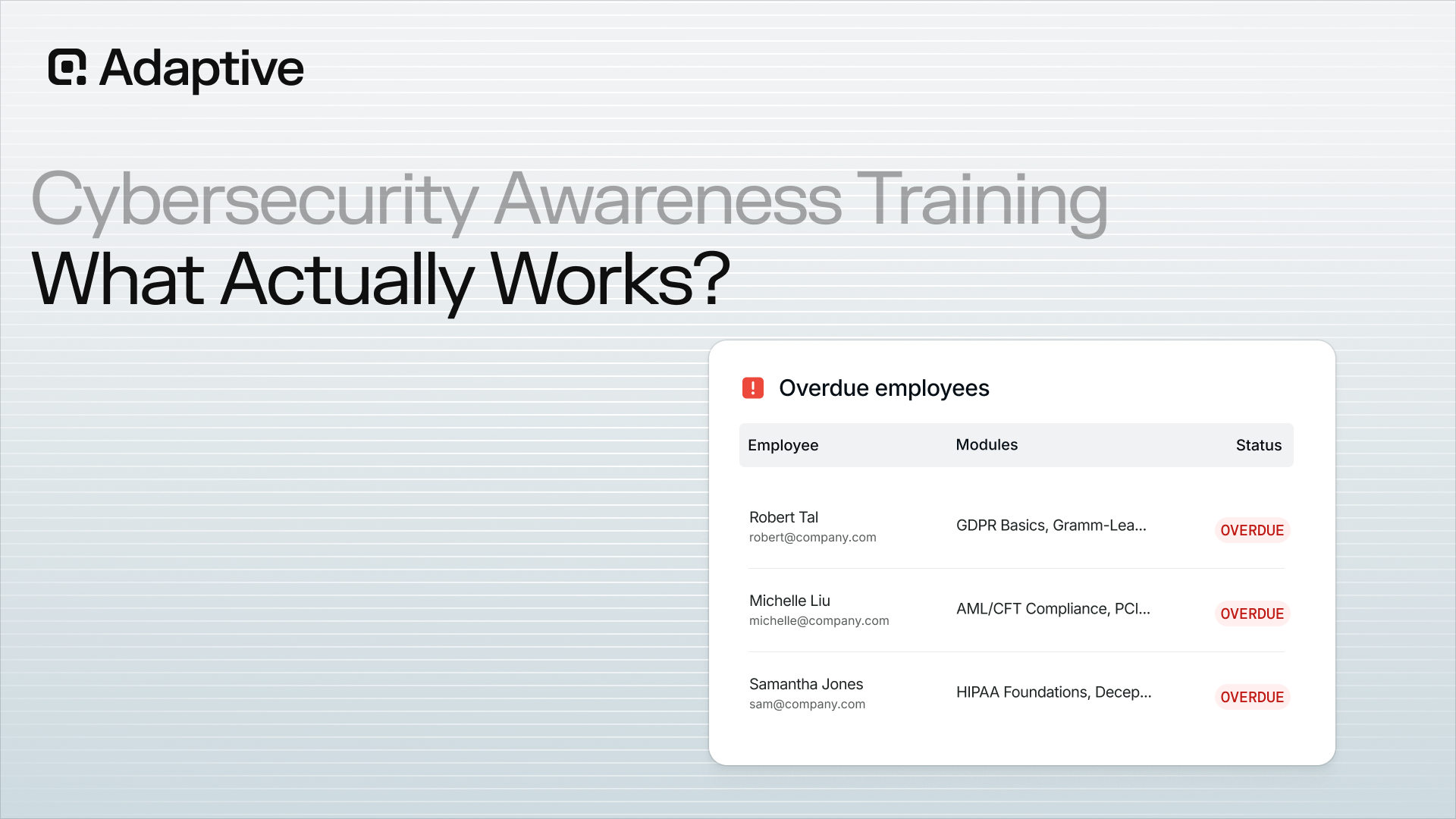
Measuring the impact of cybersecurity awareness training platform deployment requires tracking behavioral signals across phishing click rates, reporting rates, and dynamic human risk scores, not just completion logs. Organizations should establish a baseline before deployment, define target thresholds for each metric, and tie every data point to a board-ready risk narrative that connects training outcomes to financial exposure.
1. Establish Phishing Click Rate as the Primary Cybersecurity Awareness Training Platform Benchmark
Cybersecurity awareness training platform phishing click rates, the percentage of employees who click a simulated phishing link, are the clearest signal of real-world susceptibility before and after training. A high pre-training click rate confirms the program's urgency. A declining post-training rate proves it is working. Neither metric means anything without the other, which is why baselining before the first simulation is non-negotiable. A 10-percentage-point reduction in an organization's phish-prone population translates statistical exposure into measurable financial risk averted.
2. Track Cybersecurity Awareness Training Completion Rates as a Necessary but Insufficient Signal
Cybersecurity awareness training platform completion rates confirm that employees accessed content. They do not confirm behavioral change. An organization with 100% completion and a 25% phishing click rate has a compliance record, not a security program. Completion data matters for audit trails mapped to frameworks like SOC 2, HIPAA, and GDPR, but it must be presented alongside simulation performance data to carry any meaningful risk narrative.
3. Monitor Phish Reporting Rates to Measure Active Defense
Phish reporting rates measure how frequently employees flag suspicious emails, capturing active defense behavior rather than passive knowledge. A rising reporting rate signals that employees have shifted from awareness to action, treating suspicious messages as events to escalate rather than ignore. Cybersecurity awareness training platforms that provide automated phish triage close the loop by classifying every reported email, reducing analyst workload while reinforcing the reporting habit.
Adaptive Security's phish triage automation turns employee reporting into a measurable security operation.
4. Use Human Risk Scores to Identify and Prioritize Cybersecurity Awareness Training Intervention
Human risk scores aggregate cybersecurity awareness training platform simulation performance, training completion, OSINT exposure, credential breach history, and AI or shadow IT behavior into a single per-employee risk indicator. Unlike static completion logs, risk scores update continuously. They surface which individuals and departments need immediate intervention rather than waiting for the next annual review cycle.
Organizations that track risk score trajectories over time gain a defensible, data-driven record of cybersecurity awareness training platform effectiveness that completion logs alone cannot provide.
5. Translate Cybersecurity Awareness Training Metrics Into Board-Ready Business Risk Language
Security leaders who present click-rate percentages to a board get polite attention. Those who translate the same data into avoided breach costs get a budget. The formula is straightforward: multiply the organization's phish-prone population percentage by the probability that a successful phishing cyberattack escalates to a breach, then apply the $4.44 million average breach cost from the IBM Cost of a Data Breach Report (2025) as the financial denominator.
Long-term cybersecurity awareness training platform deployment governance requires:
- A named owner for simulation cadence;
- A defined escalation threshold that triggers targeted retraining;
- A quarterly reporting cycle to track risk score trajectories across departments.
Programs without this structure drift back toward annual compliance exercises within 18 months of launch. With it, the cybersecurity awareness training platform becomes a sustained, measurable defense layer and the foundation for building the kind of board-level risk narrative that earns sustained investment.
Give your board the risk language they need. Adaptive Security's reporting dashboard does the translation.
Supporting Compliance Requirements Through Cybersecurity Awareness Training Platform Deployment
Cybersecurity awareness training platform deployment generates the documented evidence that regulators and auditors demand. Seven major frameworks explicitly require or strongly recommend security awareness training:
- HIPAA mandates workforce training as a required implementation specification under the Security Rule (45 CFR §164.308(a)(5));
- PCI-DSS v4.0 requires security awareness training for all personnel with access to cardholder data;
- SOC 2, ISO 27001, NIST CSF, GDPR, and CMMC Levels 1 and 2 each treat employee awareness as a control objective.
Training content mapped to these frameworks turns cybersecurity awareness training platform completion from an internal metric into auditable compliance evidence.
Why Cyber Insurers Now Require Proof of Active Cybersecurity Awareness Training Programs
Insurers repriced cyber risk after breach losses mounted and human error appeared as the root cause in claim after claim. Carriers now treat documented cybersecurity awareness training platform results as underwriting conditions. Organizations that cannot produce this data face higher premiums or coverage exclusions at renewal. An active, continuous cybersecurity awareness training program signals lower probability of a successful social engineering cyberattack, which directly reduces the insurer's expected loss exposure.
How Audit-Ready Reporting Reduces Cybersecurity Awareness Training Compliance Documentation Burden
The compliance burden in a manual program is the documentation assembly that precedes every audit. A cybersecurity awareness training platform with structured audit reporting capabilities exports cybersecurity awareness training completion records, phishing simulation results, and individual risk score histories in audit-ready formats. These map directly to framework control requirements. A HIPAA auditor asking for evidence of workforce training under 45 CFR §164.308(a)(5) receives an exportable report, not a manually compiled spreadsheet.
Why Regulators Prefer Continuous Cybersecurity Awareness Training Programs Over Annual Completion Logs
Annual cybersecurity awareness training produces a single data point: a completion timestamp. Continuous cybersecurity awareness training programs produce an evidence trail: recurring simulation results, triggered microlearning completions, and declining risk scores over time. That evidence demonstrates sustained behavioral change rather than checkbox compliance. The NIST Cybersecurity Framework PR.AT control category frames awareness and training as an ongoing organizational function, a position regulators and insurers have increasingly adopted as the standard for evaluating program maturity.
Map your cybersecurity awareness training platform deployment outputs directly to compliance frameworks with Adaptive Security.
Where Cybersecurity Awareness Training Platform Deployment Fits Within a Human Risk Management Program
Cybersecurity awareness training platform deployment produces meaningful risk reduction only when it operates as one component of a broader human risk management (HRM) architecture. Training completion data confirms that employees accessed a module, not that behavior changed. The behavioral gap between training completion and actual decision-making under pressure remains the central problem security leaders must solve.
Why Cybersecurity Awareness Training Program Completion Alone Fails to Capture Actual Human Risk
Cybersecurity awareness training platform completion rates measure administrative activity. They do not measure behavioral readiness. An employee who finishes a 10-minute phishing awareness module still carries measurable risk if they recently clicked a simulated credential-harvesting email, have exposed personal email addresses indexed across data broker sites, or have credentials surfaced in a known breach dataset.
A genuine HRM program aggregates all three signal types:
- Simulation behavior,
- OSINT exposure,
- Credential breach history.
These combine into a dynamic risk score that reflects actual organizational vulnerability in real time. That score degrades when an employee fails a simulation and improves when they report a suspicious email correctly, creating a continuous measurement loop rather than an annual compliance event.
How OSINT Profiling Strengthens Cybersecurity Awareness Training Simulations and Risk Scoring
OSINT profiling uses publicly available data to map the personal and professional cyberattack surface each employee presents to cyber threat actors. The data sources include: LinkedIn job history, forum registrations, data broker aggregations, and conference speaker bios. Within a cybersecurity awareness training platform, this data serves two functions simultaneously.
First, a spear phishing scenario referencing an employee's actual vendor relationships or job title carries far higher psychological realism than a generic template. This produces more accurate susceptibility data.
Second, OSINT signals feed directly into risk scoring by quantifying how much actionable information a cyberattacker already has about each individual, enabling security teams to prioritize remediation toward the most exposed employees.
How Phish Triage Automation Connects Cybersecurity Awareness Training to Operational Security Outcomes
Phish triage closes the loop between the cybersecurity awareness training platform and the security operations center. When employees are trained to recognize and report suspicious emails, the volume of analyst-reviewed submissions increases significantly. Without automation, that volume creates alert fatigue that slows incident response.

AI-powered phish triage classifies every reported email as safe, spam, or malicious using confidence scoring. It auto-resolves low-risk submissions above a configurable threshold and escalates genuine threats for analyst review. The operational result is faster incident response on confirmed threats and analyst time redirected toward higher-value investigation. This turns the cybersecurity awareness training platform from a compliance output into a measurable contributor to security operations capacity.
Adaptive Security's phish triage connects your cybersecurity awareness training program directly to security operations outcomes.
How Adaptive Security Delivers Cybersecurity Awareness Training Platform Deployment Outcomes From Day One
Adaptive Security is purpose-built to close the gap between cybersecurity awareness training platform deployment and measurable risk reduction. The platform connects to Microsoft 365 or Google Workspace via API in minutes. It launches a baseline phishing simulation within the first week and begins generating per-employee human risk scores before most legacy platforms finish onboarding. Organizations do not wait weeks for their first data point. They arrive at the first security review with a full behavioral baseline already established.
Adaptive Security's cybersecurity awareness training platform simulation engine covers all four social engineering channels that cyberattackers actively exploit: email spear phishing personalized through OSINT profiling, vishing calls using AI-cloned executive voices, smishing via SMS, and deepfake video impersonation of company leadership. Each simulation reflects the actual threat profile of the employee receiving it, not a generic template reused across the workforce.
When an employee fails a simulation, point-of-failure education triggers immediately, delivering a targeted microlearning module at the exact moment the mistake is most memorable.
Beyond simulations, Adaptive Security's AI Content Studio enables program managers to generate new training modules from a prompt or internal policy document in minutes, keeping content current as the threat landscape evolves. Human risk scores update continuously across simulation behavior, OSINT exposure, and credential breach history, giving security leaders a real-time view of organizational vulnerability.
Adaptive Security is designed to function as a complete HRM layer: connecting employee behavior change to operational security outcomes, board-level risk reporting, and continuous compliance evidence in a single cybersecurity awareness training platform deployment.
See measurable human risk reduction from the first week of deployment.
Frequently Asked Questions About Cybersecurity Awareness Training Platform Deployment
How Long Does Cybersecurity Awareness Training Platform Deployment Take?
Most modern cybersecurity awareness training platforms complete technical deployment in one to three days, with a full program launch achievable within two to four weeks. The technical steps include allowlisting simulated phishing domains, connecting to Microsoft 365 or Google Workspace via API, syncing the employee directory through Active Directory or SCIM, and configuring SSO. These typically take a single IT administrator less than a day on a well-documented platform.
What extends the timeline is program readiness. Drafting internal communications, segmenting employees into role-based groups, and scheduling the baseline phishing simulation all add time before cybersecurity awareness training platform deployment goes live. For large enterprises with 5,000 or more employees, a phased 90-day rollout covering technical setup, baseline testing, segmented training assignments, and a first post-training simulation is a realistic and proven deployment model.
What Is a Baseline Phishing Test and Why Should Organizations Run One Before Cybersecurity Awareness Training Platform Deployment?
A baseline phishing test is a simulated phishing cyberattack sent to employees before any formal cybersecurity awareness training platform content is deployed. It measures an organization's starting susceptibility rate without the influence of prior training. Running one before launch gives an accurate measure of how many employees click malicious links, submit credentials, or fall for social engineering scenarios without preparation.
Roughly one in three employees will fail a simulated cyberattack before training begins. Without that baseline, program managers have no credible before-and-after data to demonstrate ROI, report progress to leadership, or identify which departments carry the highest risk. Skipping this step is one of the most common cybersecurity awareness training platform deployment mistakes.
How Do Cybersecurity Awareness Training Platforms Support HIPAA, GDPR, and PCI-DSS Compliance?
Cybersecurity awareness training platforms support HIPAA, GDPR, and PCI-DSS compliance by delivering training content mapped to each framework's specific requirements and generating the audit-ready documentation that regulators and auditors expect:
- For HIPAA, the HHS Security Rule explicitly requires covered entities to implement a security awareness and training program for all workforce members, including periodic reminders and protection from malicious software;
- For PCI-DSS, Requirement 12.6 mandates a formal security awareness program that educates all personnel about cardholder data security cyber threats;
- For GDPR, data protection authorities consistently treat documented employee training as evidence of the technical and organizational measures required under Article 32.
Cybersecurity awareness training platforms support compliance through role-based training modules pre-mapped to framework controls, completion logs and simulation results exportable for audit evidence, and continuous program records that demonstrate ongoing compliance activity.
What Phishing Click Rate Should Organizations Target After Cybersecurity Awareness Training Platform Deployment?
Organizations running a well-structured cybersecurity awareness training platform should target a phishing simulation click rate below 5% within 12 months of launch.
Reaching sub-5% requires more than cybersecurity awareness training platform deployment alone. Simulation frequency, immediate point-of-failure education, role-specific content, and monthly reinforcement all drive the reduction. Organizations that run only annual training and infrequent simulations see much slower improvement.
How Is a Human Risk Score Calculated in a Cybersecurity Awareness Training Platform?
A human risk score is a dynamic, per-employee metric calculated by combining behavioral signals from across a deployed cybersecurity awareness training platform. The core inputs typically include:
- Phishing simulation outcomes: whether an employee clicked, reported, or ignored a simulated cyberattack;
- Training completion rate and quiz performance;
- Historical repeat-fail patterns across simulations;
- OSINT exposure signals such as personal data visible in public breaches or on professional networks;
- Indicators of risky AI or shadow IT behavior, where supported.
Each input is weighted by severity and recency, producing a rolling score that rises when risk signals accumulate and falls as employees demonstrate improved behaviors. This composite approach is what separates human risk scoring from simple compliance tracking. Completion logs say whether training happened; risk scores explain whether behavior is actually changing.
Adaptive Security's human risk scores give security leaders the real-time visibility that completion logs cannot.
Key Takeaways: Cybersecurity Awareness Training Platform Deployment
- Cybersecurity awareness training platform deployment closes the gap between technical controls and human behavior: the layer where most breaches originate.
- Cybersecurity awareness training platform deployment quality, not platform selection alone, determines whether that exposure is reduced.
- Technical prerequisites including allowlisting, directory sync, SSO integration, and API connectivity must be resolved before any simulation is sent.
- Human risk scores aggregate simulation behavior, OSINT exposure, and credential breach history into a continuous, per-employee risk indicator that completion logs cannot replicate.
- Continuous programs produce the audit evidence trail regulators and cyber insurers require. Annual completion logs produce a timestamp.
- Compliance frameworks including HIPAA, PCI-DSS, SOC 2, GDPR, and ISO 27001 all treat documented, ongoing cybersecurity awareness training platform deployment as a control objective.
Adaptive Security delivers all of the above, from API-based deployment in minutes to board-ready risk reporting, as a complete human risk management layer.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents




.png)