Cyber resilience is the capacity of an organization to prepare for, respond to, and recover from cyber threats—not just technically, but operationally and behaviorally. It's much more than risk mitigation or breach prevention. True cyber resilience means bouncing back quickly and effectively after an incident, with minimal disruption to business continuity.
Resilience strategies often focus exclusively on infrastructure: firewalls, patch cycles, backups. But these systems are only as strong as the people operating them. The overlooked variable in most cyber resilience plans is human behavior, with roughly three out of four breaches involving a human element.
True cyber resilience isn’t just about surviving attacks either, but how fast and effectively your people recover from them. Adaptive Security helps organizations operationalize this human layer of resilience through behavior-based simulations and measurable security awareness metrics.
What is cyber resilience? A modern definition
Cyber resilience requires going beyond traditional cybersecurity frameworks. It needs to address not only protection and detection, but also response and recovery. It’s a holistic approach that accounts for people, processes, and technology working in unison to minimize the impact of attacks and maintain business function.
Unlike legacy definitions centered around system uptime or data restoration, modern cyber resilience integrates human readiness as a core component. People configure, use, and respond to every piece of infrastructure, so cybersecurity alone isn’t enough protection.
How cyber resilience differs from cybersecurity
Cyber resilience forces security leaders to treat human risk with the same importance as technical risk. It means shifting from awareness activities to readiness outcomes. This is something Adaptive Security helps operationalize through data-driven human risk management.
Why the human layer still undermines cyber resilience
Despite billions invested in cybersecurity tooling, many breaches begin with a person, not a system flaw. According to Verizon’s 2025 DBIR, human action is the most unpredictable aspect of cybersecurity—human error remains a top cause of costly data breaches.
Here are a few common examples:
- Phishing: Sophisticated emails or SMS messages trick employees into clicking malicious links or sharing credentials, bypassing even the most advanced secure email gateways.
- Credential reuse: Employees reuse passwords across systems, increasing blast radius when one account is compromised.
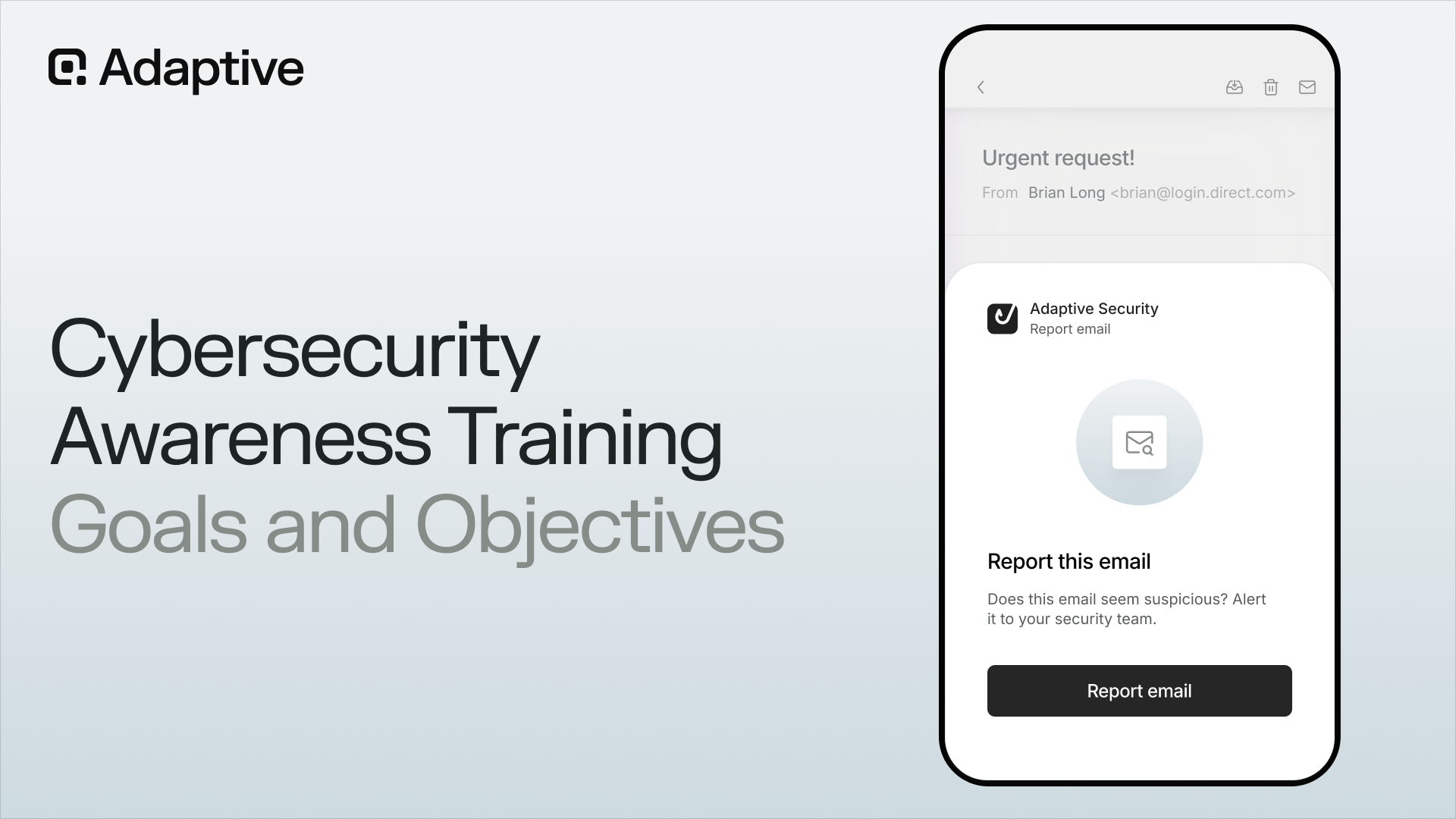
- Delayed incident reporting: Many users hesitate to report suspicious activity, either out of fear of repercussions or uncertainty around processes.
Security platforms are essential for detection and containment, but they can’t compensate for a workforce that isn’t ready to recognize or respond to cyberattacks. Traditional training programs struggle to keep up with evolving tactics, and fail to produce measurable improvements. A behavior-first approach closes the gap.
Adaptive Security treats human behavior as a risk signal that can be tracked, scored, and strengthened over time. Through real-world simulations and readiness analytics, organizations gain visibility into how their workforce performs under pressure, not just what they know in theory.
Operationalizing cyber resilience through behavior
To build truly resilient security programs, leaders must evolve from static policy documents and one-off training events to dynamic, behaviorally adaptive programs. Here are the foundational pillars of this shift that limit vulnerabilities and contain cyber risk.
Phishing simulations: Exposure to emerging threats
Static templates don’t cut it anymore. Adaptive’s AI-powered phishing simulations replicate real-world cybercrime, from deepfake audio to QR code phishing. The platform provides consistent, evolving exposure across channels, including email, SMS, voice. It also offers collaboration tools that allow you to:
- Target by department, role, or behavior history
- Run simulations to include generative artificial intelligence threats
- Help teams build "muscle memory" in real-world threat scenarios
Response readiness metrics: Speed and precision under pressure
It’s not just if users fall for phishing—it’s how fast they recover. Adaptive tracks key metrics like:
- Time to report suspicious messages
- False negative rates (threats missed)
- Escalation paths and bottlenecks
These insights allow teams to operationalize resilience, not just preach it. You can’t fix what you can’t measure, and most organizations can’t measure how their people respond when it counts. Protecting critical infrastructure and preventing financial losses requires prompt disaster recovery.
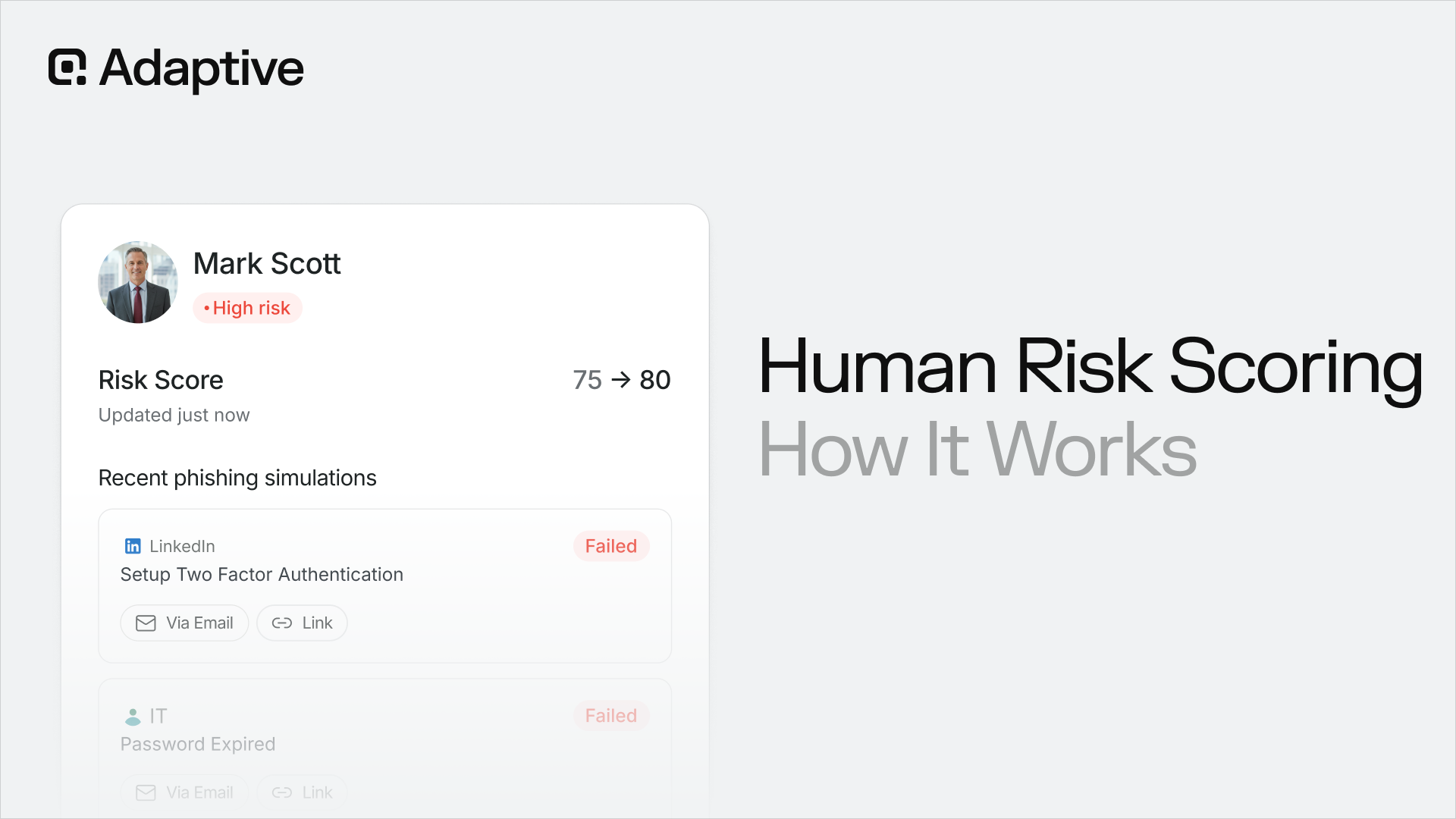
Behavioral risk scoring: Visibility into human risk
Imagine knowing your riskiest departments or users—not by gut feel, but with data. Having accurate threat intelligence and knowing where successful attacks may come from is huge.
Adaptive’s behavioral analytics layer offers:
- Trend visibility across time, teams, and roles
- Individual and group-level risk scores based on interaction history
- Integration with GRC dashboards to support board-level reporting
This is how human risk becomes reportable, improvable, and defendable—right alongside patch rates and endpoint status.
Integrating behavioral metrics into GRC reporting
For years, governance, risk, and compliance (GRC) leaders have confidently reported on technical controls—patch compliance, MFA enforcement, and vulnerability scan results. But when it comes to the human layer, the numbers are often anecdotal or missing entirely. But that’s changing.
Modern platforms like Adaptive Security now allow CISOs and compliance leads to report behavioral resilience with the same rigor as infrastructure metrics. This turns a historically soft area like “awareness” into a trackable, auditable concept.
Here are key behavioral KPIs Adaptive lets you include in your next board or audit report:
- Phishing simulation click rates: trended over time, segmented by department or role
- Time-to-report metrics: how fast employees escalate potential threats
- Retraining completion and improvement rates: tracking who improves post-intervention
- Risk scoring by team or region: identifying high-risk cohorts needing focused attention
These metrics support frameworks like:
- NIST CSF v2: Align with the “respond” and “recover” pillars via human-driven detection and response
- ISO 27001/27701: Show continuous improvement in awareness, competence, and incident handling
- SOC 2 (Security and Availability Trust Services Criteria): Evidence that people-based controls are monitored and effective
Integrating human-centric metrics into governance reporting allows security leaders to demonstrate not just technical preparedness, but an organization’s ability to respond to real-world behavior.
Building a human-centric cyber resilience framework: a 5-step framework
A behavior-first resilience program doesn’t just happen. It must be designed, deployed, and iterated like all other security measures. Preparing for ransomware and AI-powered deepfakes requires intentional and informed incident response planning.
Here’s a simple 5-step framework your team can use to build measurable human resilience from the ground up.
1. Assess behavioral risk
Start by establishing a baseline. Use internal metrics, like incident logs and training completion data, along with external tools like Adaptive’s readiness assessments to:
- Identify risky departments or roles.
- Understand past failure patterns (e.g., repeated phishing clicks).
- Establish KPIs that matter to your board or auditors.
2. Design role-based simulations
Not all users face the same threats. Tailor your simulations to match job functions:
- Finance teams: Focus on business email compromise and wire fraud scams.
- Developers: Include credential stuffing and package spoofing.
- Executives: Simulate deepfake vishing and impersonation threats.
Adaptive Security supports targeted simulation campaigns by role, region, and risk profile. It provides a much more accurate risk assessment, ensuring the right people see the right threats.
3. Run multichannel training
Modern cybersecurity incidents aren’t just in your inbox. Hackers show up in chat, voice, SMS, and video, and your training should reflect that.
- Email phishing: Still prevalent, but more personalized
- Voice phishing (vishing): Growing with deepfake audio
- SMS phishing (smishing): Especially common in finance and logistics
- Video lures: AI-generated “CEO messages” or vendor updates
Adaptive delivers cross-channel simulations powered by AI, giving users real-world practice across every major threat vector. Want to see how your team performs? Run a free phishing simulation.
4. Measure and report readiness gaps
Don’t stop at completion rates. Instead, focus on outcomes:
- Who fell for what?
- How long did it take to escalate?
- What patterns emerge across time, role, or region?
Adaptive’s dashboard gives security teams real-time behavioral intelligence, which comes in handy for weekly ops reviews and quarterly board updates.
5. Close gaps with just-in-time nudges
Awareness fades, so reinforcement matters. That’s why high-performing organizations now deliver real-time nudges when they detect risky behavior, creating a security lifecycle. Some examples include:
- A user enters credentials into a suspicious site, so they receive an immediate micro-training.
- Someone fails to report a simulated attack, so they trigger contextual retraining.
Adaptive offers automated nudges and micro-lessons that drive behavior change at the moment it matters most.
Why Adaptive Security is built for cyber resilience
Cyber resilience isn’t a box you can just check off. A proper cyber resilience strategy is a continuous process. It means knowing how your people will perform when technology fails, and having data on readiness, not just awareness. Ultimately, it means moving beyond static training to behavioral cybersecurity.
From deepfake-enabled phishing simulations to employee-level behavioral scoring and real-time feedback loops, Adaptive empowers security leaders to build, measure, and optimize human resilience at scale. It’s how CISOs can operationalize ecosystem readiness with the same confidence they bring to patching cycles or endpoint coverage.
Book a demo or take a self-guided tour to see Adaptive’s cyber resilience engine in action.
FAQs about cyber resilience
What’s the difference between cyber resilience and cybersecurity?
Cybersecurity focuses on preventing and detecting threats: think firewalls, endpoint protection, and access controls. Effective cyber resilience goes further. It’s about how fast your people and critical systems recover from cyber events, maintain business continuity, and reduce future risk.
How can you measure cyber resilience?
You can measure cyber resilience through both technical and behavioral indicators. On the human side, track metrics like simulation click rates, time-to-report phishing attempts, and behavioral risk scores. This provides a quantifiable view of readiness and a snapshot of your current data protection.
What’s an example of behavioral cyber resilience?
Imagine a finance employee receiving a convincing deepfake voicemail from a fake “CEO” requesting a wire transfer. If they recognize it as a threat and report it immediately, it's because they’ve been trained with realistic simulations. That’s behavioral cyber resilience in action: trained instincts, not just knowledge.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents




.avif)