Microsoft's new research on Medusa ransomware should be a wake-up call for every security team. The attackers are not waiting.
Last week, Microsoft published research on the Medusa ransomware group that deserves far more attention than it has received. The findings are stark. Medusa actors are breaking into organizations, stealing data, and deploying ransomware within 24 hours of gaining initial access. In some cases, they are exploiting software vulnerabilities before those vulnerabilities have been publicly disclosed, targeting the gap between the moment a bug exists and the moment a patch is available. That gap has shrunk from weeks to days. Sometimes less.
Microsoft specifically flagged two vulnerabilities, one in SmarterMail and one in GoAnywhere Managed File Transfer, that Medusa actors exploited a full week before public disclosure. The Cybersecurity and Infrastructure Security Agency (CISA) has since confirmed both were used in live ransomware attacks. This is what researchers call zero-day or near-zero-day exploitation, and it is no longer the exclusive territory of nation-state hackers with unlimited resources. A ransomware group is doing it now, at scale, targeting hospitals, schools, financial firms, and local governments.

Speed Is the New Weapon
What makes this research alarming is not just the technical sophistication but also the operational tempo. Medusa does not linger. The group moves with a speed and discipline that most organizations are simply not built to match. Security teams that are monitoring for threats and preparing responses over days are already losing the race when the attackers are working in hours.
The moment Medusa gains a foothold, they create new user accounts to lock in persistent access. They use legitimate remote management tools (ConnectWise ScreenConnect, AnyDesk, SimpleHelp), so the traffic looks normal to monitoring systems. From there, they move laterally, identify valuable data, exfiltrate it, and deploy ransomware. In the fastest cases, this entire sequence runs in under a day.
The group has been running since 2021 and has hit healthcare facilities, county governments, and universities across the United States, United Kingdom, and Australia. The most recent victims include the University of Mississippi Medical Center (the largest hospital in Mississippi) and Passaic County in New Jersey. Both are critical public infrastructure.
The Perimeter Is the Problem
Medusa's primary entry point is web-facing systems: the servers, portals, and file transfer services that organizations expose to the internet. These are the edges of the network, and they are consistently the weakest link. Microsoft's research makes clear that the group actively hunts for organizations that have not yet patched known vulnerabilities, moving quickly during that window when the exploit is known to attackers and before it is known to defenders.
Attackers are getting faster. They are getting more systematic. And they are targeting organizations that have not done the basic work of understanding what they are exposing to the outside world.
Every organization has a digital footprint (IP addresses, web applications, file transfer portals, email gateways), and many of them have no clear picture of what that footprint actually looks like from an attacker's perspective. While most security teams know their major systems, far fewer have a real-time view of every internet-facing asset and whether each one is patched, configured correctly, and monitored. That gap is where Medusa lives.
Healthcare Keeps Getting Hit
Microsoft's report highlights a particularly troubling pattern in healthcare. Medusa has repeatedly and deliberately targeted hospitals and medical systems. This is not coincidental. Healthcare organizations tend to run older infrastructure, operate under intense time pressure, and face enormous consequences when systems go offline. For a ransomware group trying to maximize leverage, a hospital is a high-value target.
The University of Mississippi Medical Center attack took the FBI and the Department of Homeland Security to help contain. The hospital fully reopened on March 2, weeks after the initial breach. That is weeks of disrupted patient care, diverted ambulances, and staff working around crippled systems. The human cost of these attacks is real, and it is growing.
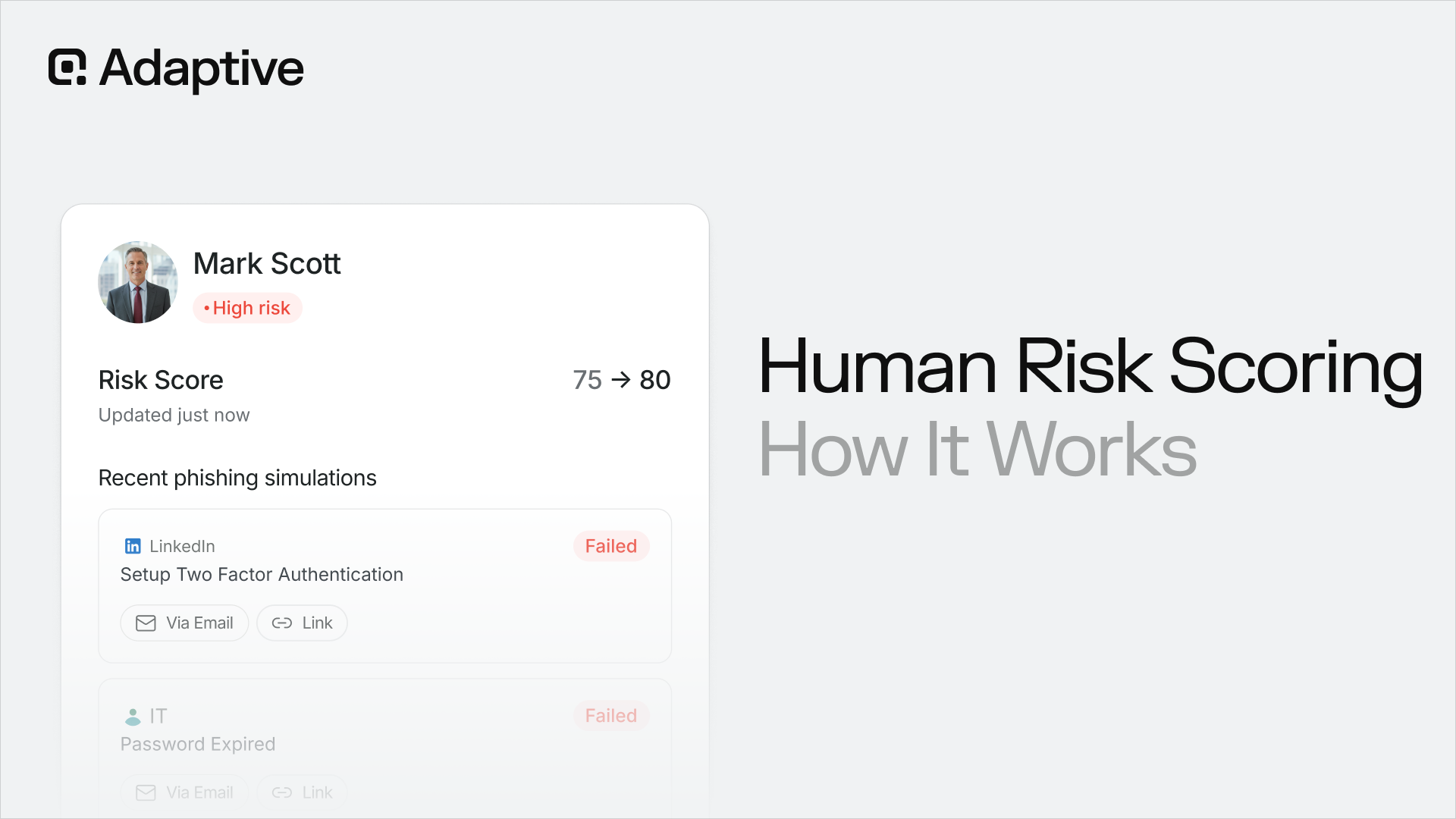
According to Brian Long, CEO and Co-Founder of Adaptive Security, conversations with CISOs across industries over the past 18 months point to a significant shift in how healthcare organizations think about security. Organizations that once treated security investment as a low priority are now confronting the reality that an attack is a matter of when, not if. A year ago, roughly one in ten security executives Long spoke with had directly experienced a sophisticated AI-powered or exploitation-based attack. Today that number is well over half.
What Organizations Need to Do Right Now
The speed of these attacks changes what effective security practice looks like.
- Patch management cycles that assume organizations have days or weeks to respond are already outdated. When a vulnerability is disclosed, and in some cases before it is disclosed, attackers are actively looking for unpatched systems. The window for a safe and measured response has shrunk dramatically.
- Security teams need continuous, real-time visibility into their internet-facing attack surface. That means knowing every web-facing asset, monitoring for new exposures as they appear, and having a patch prioritization process that can move in hours when a critical vulnerability hits a high-risk system. It also means understanding how attackers see an organization: what data is publicly available, what systems are visible, and what an attacker could learn before they ever touch the network.
- On the detection side, Medusa's use of legitimate remote management tools is a reminder that behavioral monitoring matters as much as signature-based detection. When an attacker is using ConnectWise or AnyDesk, a firewall rule is not going to stop them. What will catch them is anomalous behavior: new accounts being created, unusual data transfers, remote tools being used outside normal business hours on systems that do not typically use them.
- Incident response plans also need to account for the speed of modern attacks. A response playbook that assumes a team has 48 hours to assess a situation and contain it is not aligned with the reality that data exfiltration may already be complete by the time an alert fires. Faster detection, faster containment, and pre-positioned response capabilities are baseline requirements for any organization serious about defending against modern attacks.
Taken together, these measures shift security from a reactive posture to one that matches the speed and precision of the attacks now targeting organizations across every sector.
The Broader Trend
Medusa is one group. But the pattern it represents – fast exploitation of known and unknown vulnerabilities, precision targeting of high-leverage sectors, combination of data theft and ransomware for maximum pressure – is the direction the entire threat landscape is moving. The tools that enable this kind of operation are getting cheaper, faster, and more accessible every month.
Open-source AI models that can be run locally without moderation are now widely available. The compute required to run sophisticated attack tools has dropped to the point where a well-funded criminal operation, let alone a nation-state, faces almost no barrier to standing up AI-augmented attack infrastructure. The asymmetry between offense and defense is growing, and organizations that treat security as a periodic exercise rather than a continuous discipline will find themselves on the wrong side of that gap.
The Microsoft research on Medusa is a detailed, public, and specific account of what sophisticated ransomware operations look like today. Every security leader should read it and use it as a forcing function to ask whether their organization could detect and contain a 24-hour attack, because that is the standard attackers are now setting.




Contents