When a Singaporean woman lost $250,000 to phishing scammers in early 2025, despite having her bank accounts frozen and direct police warnings, this case illustrates how even the most cautious individuals can fall victim to phishing attacks
According to Anti-Phishing Working Group's Phishing Activity Trends Report (2025), 3.8 million phishing attacks were recorded in 2025 alone. Despite the cybersecurity advancements, phishing is not slowing down. It is scaling faster than most organizations can train against it.
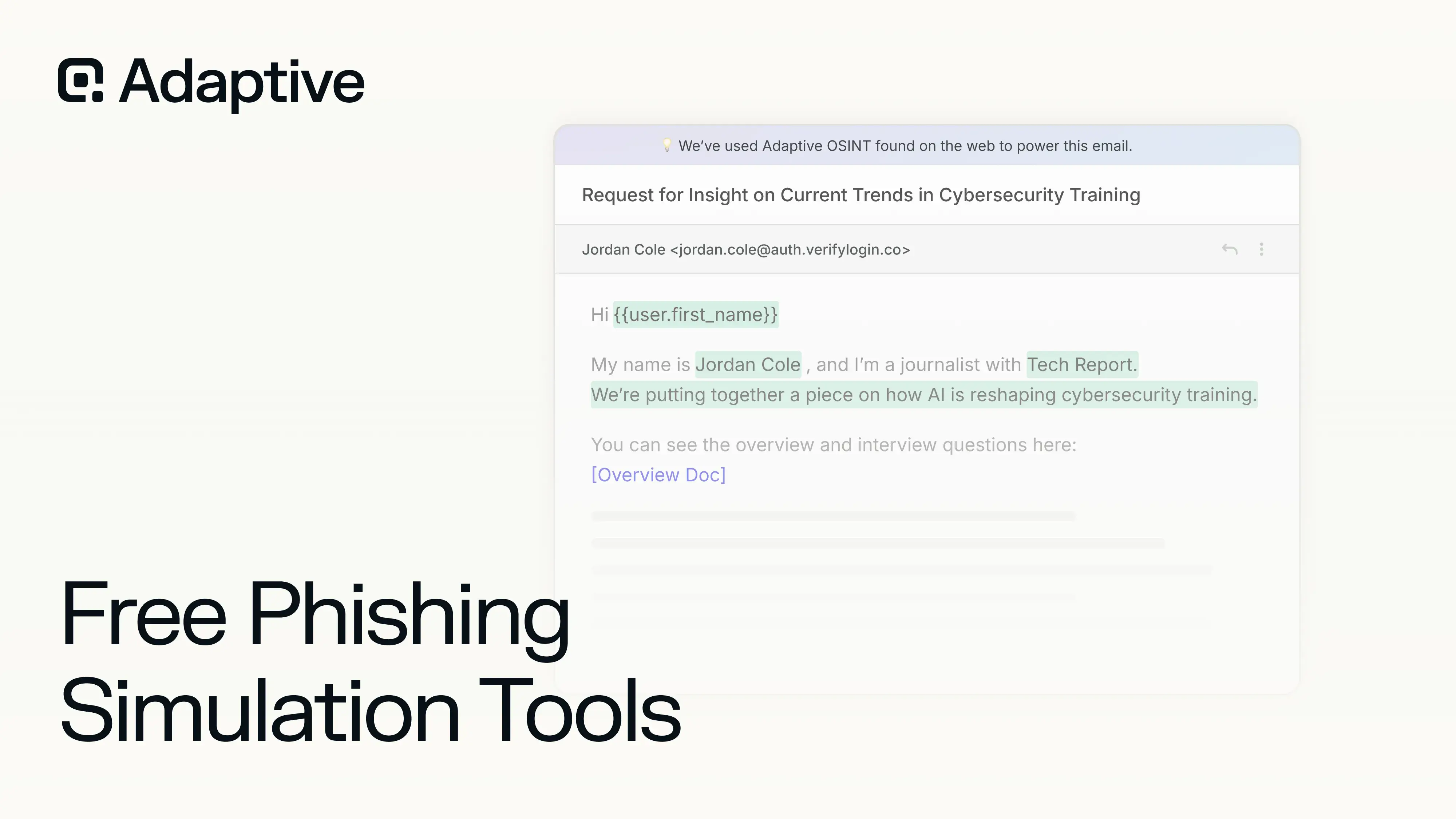
The problem is simple: attackers test your people every day, but most teams never test themselves. Enterprise-grade phishing simulations exist, but cost, setup complexity, and resource constraints keep them out of reach for many organizations.

This is where free phishing simulation tools come in. Organizations do not need a large budget to begin deploying realistic attack simulations. This free phishing simulation guide outlines how to:
- Run free phishing simulation tools across major attack vectors, including email phishing, smishing, vishing, deepfake scams, and ransomware simulations.
- Choose the right tools based on your organization's needs and constraints.
- Deploy phishing simulations without disrupting day-to-day operations.
- Build a program that drives real, measurable changes in employee behavior.
Phishing attacks are inevitable for organizations. But with the right approach, organizations can minimize the damage significantly. Adaptive Security helps companies achieve that.
Most teams get tested by real attackers every day. The ones that survive test themselves first.
Start Your Free Phishing Simulation
What Are Free Phishing Simulation Tools and What Do They Do?
Free phishing simulation tools are platforms that safely replicate phishing attacks to measure how employees respond under pressure. They simulate the exact tactics cyberattackers use, without exposing the organization to actual risk.
A free phishing simulation works by sending realistic phishing messages across multiple channels, like email, SMS, or voice, and tracking how users react. These phishing simulations measure critical behaviors that determine the risk level of each individual and educates employees accordingly. The goal is not to trick employees, but rather to identify gaps and improve response before phishing attackers can exploit them.
Free phishing simulation tools range from open-source frameworks to freemium SaaS platforms with enterprise-grade capabilities. Some free phishing simulation tools offer full campaign automation, analytics dashboards, and behavioral tracking at no cost.
A free phishing simulation directly supports risk reduction by turning employee behavior into measurable security data. According to Keepnet Labs Security Awareness Training Statistics (Updated 2026), effective security awareness training reduces breach likelihood by 65%. Free phishing simulation tools operationalize that training by testing it continuously, not annually.
To understand how phishing simulation fits into a broader program, check out this free phishing simulation guide.
What Is an Example of a Free Phishing Simulation?
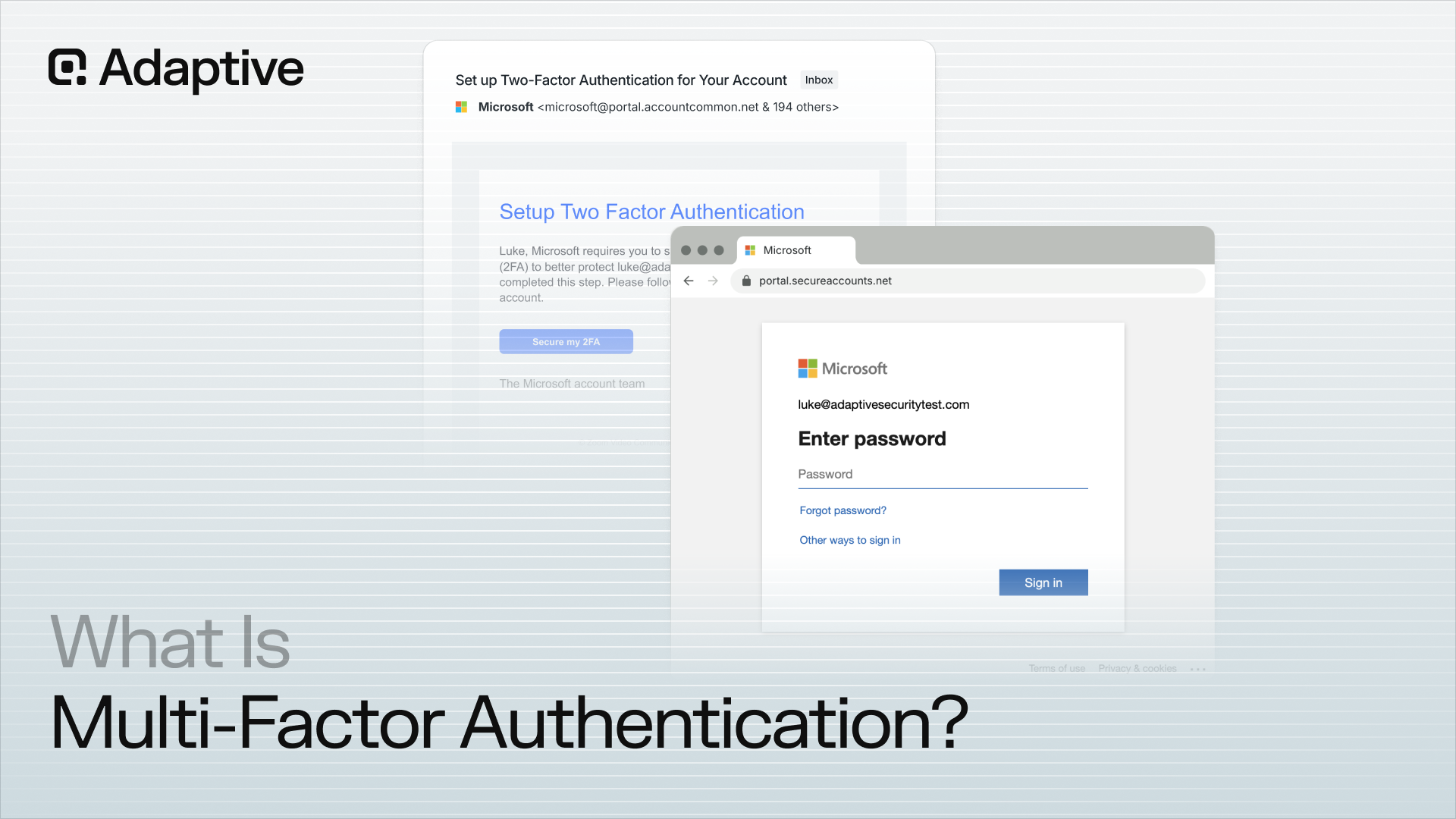
A common free phishing simulation starts with a simulated phishing email that looks like an urgent IT request. For example, in 2023 attackers sent emails impersonating Microsoft 365 security alerts, warning recipients of a "suspicious sign-in" and urging them to reset their password via a provided link; the fake notice led to a credential-harvesting page that harvested Office 365 logins and enabled wide account takeover.
When a user interacts with the simulated phishing email, the free phishing simulation tool tracks specific actions:
- Click rate: who clicked the link, counting it in their phishing click rate percentage.
- Credential submission: who entered login details.
- Report rate: who flagged the email as suspicious.
A free phishing simulation captures these behaviors in real time and often triggers immediate feedback. If a user clicks, they may see a training prompt explaining what they missed. If they report it, the system reinforces that behavior. This turns every interaction with the simulated phishing email educational.
How Do Free Phishing Simulations Work?
A phishing attack simulation follows a simple three-step process designed to mirror attack conditions while enabling safe testing. Most free phishing simulation tools follow this structure.
The following describes how a free phishing simulation works in practice:
- Attack is sent: The tool delivers a phishing message using techniques like domain spoofing or sender impersonation to mimic real threats.
- User interacts (or ignores): Employees click, submit credentials, delete, or report the message.
- Learning is triggered: The system logs behavior and delivers instant feedback or training based on the user's action.
Adaptive Security delivers instant microtraining the moment an employee clicks, turning every failure into a teachable moment before it becomes a real incident.
See On-the-Spot Learning in Action
"A successful awareness campaign would do more than tell people to pause. It would guide them through a two-step process. First trigger suspicion, motivating them to look more closely. Then, direct their attention by telling them what to look at and how to evaluate it. When both happen, the person is far more likely to make a better decision." - Bruce Schneier
A free phishing simulation focuses on behavior, not just exposure. According to Zensec Phishing Statistics 2025, 33.1% of employees are susceptible to phishing at baseline, but organizations reduce that by over 40% within 90 days of training. Free phishing simulation tools drive that reduction by repeatedly testing and reinforcing correct responses.
Types of Free Phishing Simulations You Can Run for Your Organization
A free phishing simulation tool once supported only fake emails. But phishing attackers now use SMS, phone calls, AI-generated voices, and even ransomware delivery through social engineering.
In fact, smishing click-through rates reach up to 36%, according to Keepnet Labs Smishing Statistics Report 2026, far higher than traditional email phishing. That is why organizations need to expand beyond a single-channel approach when using free phishing simulation tools.
Free Phishing Simulation Tool #1: Email Phishing Simulator
An email phishing simulator is the foundation of most free phishing simulation tools. It sends controlled phishing emails to employees using spoofed sender addresses, realistic subject lines, and prebuilt bait templates designed to trigger clicks or credential submissions.
A typical free phishing simulation email includes:
- Spoofed sender domains that mimic trusted brands or internal executives;
- Template libraries with scenarios like password resets, invoice requests, or HR alerts;
- Tracking mechanisms such as link clicks, attachment opens, and credential submissions;
- Fake landing pages that safely capture entered credentials for reporting.
Most free phishing simulation tools start here because emails are still the most scalable attack vector. Many phishing simulation platforms also provide template libraries similar to those referenced in industry-standard tools, making it easy to launch campaigns quickly. For a comprehensive tool comparison, see our post on the best phishing simulation tools.
Free Phishing Simulation Tool #2: Smishing Simulation (SMS-Based)
A smishing simulation is a free phishing simulation that targets employees through SMS instead of email. Smishing stands for SMS phishing, where attackers use text messages to create urgency and prompt immediate action.
A typical free smishing simulation includes:
- Fake delivery notifications asking users to click product tracking links;
- Bank alerts warning about suspicious activity or transactions;
- MFA or OTP prompts designed to steal authentication codes.
SMS messaging tends to feel more personal than email, as recipients often perceive a sense of familiarity from senders who possess their contact information — which is why Keepnet Labs 2026 findings suggest that smishing campaigns achieve significantly higher engagement rates than email. This is why modern free phishing simulation tools increasingly support SMS testing.
However, running a smishing simulation introduces carrier restrictions and legal considerations, especially around consent and message spoofing, which many free tools only partially support.
Free Phishing Simulation Tool #3: Vishing Simulation (Voice Phishing Tests)
A vishing simulation is a free phishing simulation that uses voice calls to test how employees respond to real-time social engineering. Vishing, or voice phishing, involves attackers impersonating trusted individuals over the phone to extract sensitive information.
A typical free vishing simulation includes:
- Scripted phone calls posing as IT support, executives, or vendors;
- Requests for credentials or access codes under time pressure;
- Call scenarios designed to test verification behavior.
How does voice phishing work? Vishing attackers create urgency and authority during a live conversation, making it harder for targets to pause and verify. In 2025, vishing attackers targeted companies like Marks & Spencer and Harrods, impersonating IT staff to manipulate employees into resetting passwords, resulting in data exposure.
According to Keepnet Labs Vishing Statistics Report 2026, vishing attacks surged by 442% in 2025, largely due to the increased ease of AI-generated voices.
While some free phishing simulation tools offer basic vishing scenarios, advanced voice simulations often require paid platforms due to infrastructure and compliance complexities.
Attackers don't stop at email. Test how your team holds up against live voice impersonation, AI-generated calls, and SMS attacks––all in one place.
Explore Multichannel Phishing Simulations
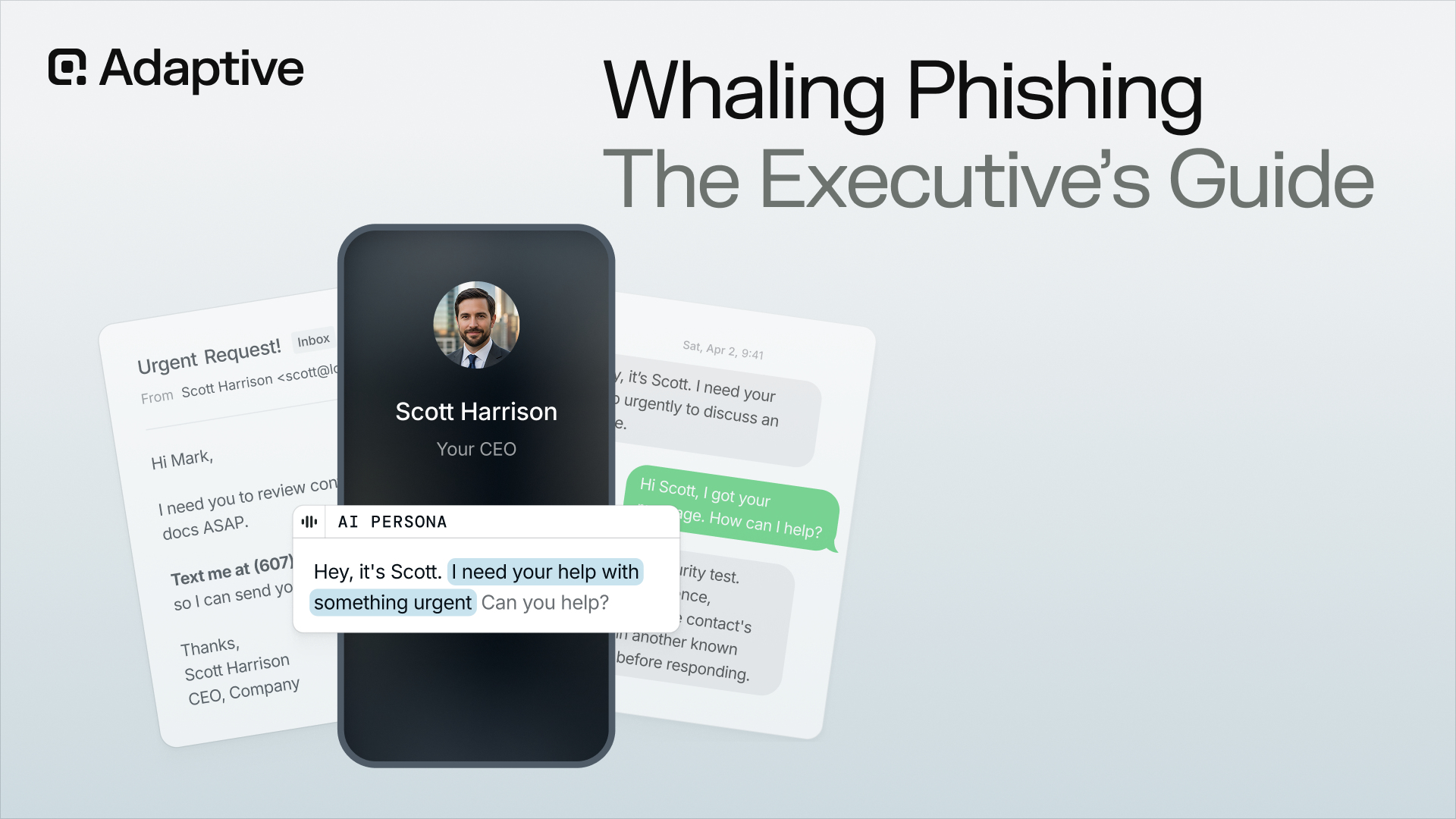
Free Phishing Simulation Tool #4: Deepfake Phishing Simulation
A deepfake phishing simulation is an advanced phishing simulation that uses AI-generated audio or video to impersonate real individuals. This includes cloned voices of CEOs, managers, or trusted partners who deliver convincing instructions.
A deepfake phishing simulation includes:
- AI-generated voice messages requesting urgent actions;
- Video impersonations of executives in internal communications;
- Highly personalized scripts based on OSINT data.
What is an example of a deepfake phishing attack? In early 2024, the Hong Kong office of the international engineering firm Arup was the victim of a sophisticated deepfake phishing scam that resulted in a loss of HK$200 million (approximately $25.6 million USD). Programs.com 2025 finds that deepfake fraud attacks have increased by over 2,000% since 2022.
Most free phishing simulation tools do not fully support deepfake simulations yet due to technical complexity. This gap is important because AI-driven impersonation is one of the fastest-growing cyber threat vectors.
Most platforms cannot simulate a deepfake CEO calling your finance team. Adaptive Security can, and it creates the kind of wake-up call employees actually remember.
See Adaptive Security's Deepfake Simulation
Free Phishing Simulation Tool #5: Ransomware Simulation
A ransomware simulation is a free phishing simulation that safely mimics how ransomware behaves after a successful phishing attack. Instead of causing real damage, it runs controlled tests that demonstrate impact without encrypting actual files.
A typical free ransomware phishing simulation includes:
- Simulated file encryption attempts to show potential impact;
- Lateral movement scenarios across systems;
- User-triggered execution paths starting from phishing emails.
According to Verizon DBIR 2025, ransomware is involved in 44% of breaches, making it one of the most critical outcomes of phishing attacks. That is why organizations combine ransomware testing with free phishing simulation tools to measure real-world risk.
Good ransomware simulations are rare in free phishing simulation tools because they require controlled environments and deeper system access. However, even basic phishing simulations help demonstrate the real consequences of a single successful phishing attempt.
AI-Driven Phishing Simulations: What's New in Free Phishing Simulation Tools for 2026
AI-driven phishing simulations are replacing old templates with dynamic, context-aware phishing attacks that mirror cyber threats in real time. AI can generate:
- personalized phishing emails at scale;
- clone voices for vishing calls;
- create deepfake videos;
- and continuously refine attack strategies based on user behavior.
This allows phishing attackers to run thousands of unique, high-conversion phishing attacks simultaneously with little manual effort.
"By fully automating all parts of the phishing process, the cost of personalized and highly successful phishing attacks is reduced to the cost of mass-scale and non-personalized emails. This means that we will face a vast increase in credible and hyper-personalized spear-phishing emails that are cheap for attackers to scale up en masse." - Bruce Schneier
That is why modern free phishing simulation tools now generate personalized baits based on employee roles, recent activity, and publicly available data (Open-Source Intelligence), then adjust difficulty individually and dynamically as users interact with the phishing simulation. This turns a free phishing simulation from a one-time test into a continuous, always-improving training loop.
According to Programs.com AI Cyberattack Statistics 2025, 82.6% of phishing emails are now created using AI, a 53.5% increase year over year. That means free phishing simulation tools that rely on fixed templates are no longer reflecting real attack conditions.
A modern free phishing simulation tool also adapts in real time. If an employee hesitates, ignores, or reports an email, the system adjusts future simulations automatically so it is harder to detect, ensuring employees do not plateau in their awareness development.
According to Zensec 2025, traditional grouping of phishing emails will become obsolete by 2027 due to AI-driven multi-form phishing attacks, reinforcing the need for dynamic free phishing simulation tools. Learn more about how AI is transforming phishing simulations into AI Phishing Simulations for organizations.
AI-Generated Phishing Simulations in Free Phishing Simulation Tools - Is It Possible?
AI-generated phishing simulations are possible because free phishing simulation tools can now generate messages on demand using real-time context instead of fixed templates. What used to be deeply technical now takes moments to set up.
AI-powered simulations are now the bare minimum standard for modern free phishing simulation tools. Static simulations train pattern recognition, not decision-making. Real phishing attacks never repeat templates anymore. A free phishing simulation that cannot generate unique, context-aware scenarios fails to simulate actual risk, defeating its purpose as a training tool.
AI-Powered Phishing Simulations vs. Traditional Free Phishing Simulation Tools
Traditional free phishing simulation tools rely on static templates that repeat across campaigns, making them easy to recognize over time. AI-powered phishing simulations replace those templates with dynamic, behavior-driven scenarios that change based on user responses within each phishing simulation.
"Spear phishing attacks are expensive, time-consuming, and don't scale well, as they are individualized for each recipient, but they are highly effective. Thus, attackers can choose between cheap and ineffective or expensive and effective. AI changes this playing field by drastically reducing the cost of spear phishing attacks, while maintaining or even increasing their success rate." - Bruce Schneier
The following compares AI-powered phishing simulation tools with traditional free phishing simulation tools:
- Accuracy: AI-powered simulations mirror attacks using current data, while static tools rely on outdated templates.
- Personalization: AI generates role-specific and context-aware lures, while traditional tools send generic messages.
- Scalability: AI creates thousands of unique simulations instantly, while template-based tools require manual setup.
- Adaptability: AI adjusts difficulty in real time, while static tools remain fixed across campaigns
"AI-powered" in free phishing simulation tools should mean more than automation. It should include live content generation, behavioral adaptation, and data-driven personalization.
If your phishing simulations look predictable after a few runs, attackers are already ahead of you. See how AI-powered phishing simulations change what "realistic" actually means.
Best Free Phishing Simulation Tools for Internal Phishing Simulations in 2026
Choosing the best free phishing simulation tools is mostly about control vs. convenience. Open-source tools give you full control and customization but require setup. Freemium platforms make free phishing simulation easy to launch but limit scale, channels, or reporting depth.
Here are the 3 most popular free phishing simulation tools for internal testing in 2026, ranked by their usability and capabilities:

Every free phishing simulation tool above serves a different level of maturity. Open-source tools like Gophish dominate because they remove limitations entirely, while SET leans on the technical side to simulate phishing and other attacks.
But if you're looking for the best performing phishing simulations tools, check out Adaptive's ultimate comparison of phishing simulation tools.
The Standard For Open Source & Free Phishing Simulation Tools
Gophish specifically sets the standard for open-source, free phishing simulation tools. With its flexibility and control, Gophish stands out with its fully transparent, widely audited, community-maintained code. It is one of the most trusted open source phishing simulation tools available.
With Gophish, you can run highly customized free phishing simulation campaigns, build realistic landing pages, and track user behavior at a precise level. This level of control is why many security teams treat it as the gold standard among free phishing simulation tools.
The trade-off is that free phishing simulation tools require manual setup and maintenance, which can present a significant challenge for resource-constrained organizations. They work best for organizations with internal IT or security teams that can manage the complexity, and want complete ownership of their phishing simulation environment.
Want to skip the server setup and launch a simulation in minutes instead of days?
Try Adaptive Security's Cross-platform Phishing Simulations
How to Choose the Best Free Phishing Simulation Tool
Choosing between free phishing simulation tools should not feel complicated. At this point, the objective is clear: select the tool that most effectively reveals employee behavior under simulated attack conditions.

Focus on these core factors when evaluating, as any good free phishing simulation tool:
- Simulates real-world attack vectors. A free phishing simulation tool must go beyond email. According to Keepnet Labs Smishing Statistics Report 2026, SMS phishing reaches up to 36% click rates. If the tool does not cover smishing, vishing, or AI-driven attacks, the simulation program remains incomplete.
- Uses realistic, convincing templates. A free phishing simulation tool should mimic SaaS alerts, invoices, and internal messages. According to Keepnet Labs 2026, 96% of phishing emails exploit trusted domains, so you should use that in your phishing simulations as well.
- Delivers actionable reporting. The best free phishing simulation tools track who clicked, who submitted credentials, and who reported the attack. According to DeepStrike.io 2026, breaches take 261 days to detect. Phishing simulations should help reduce that delay.
- Enables fast deployment. A free phishing simulation tool should not slow you down. Tools like Gophish stand out because teams can launch campaigns fast without heavy setup.
- Supports compliance and audit requirements. Your free phishing simulation tools should produce reports you can use for audits, not just internal reviews.
Too much to manage on your own? Adaptive Security handles campaign setup, dynamic testing, multichannel delivery, and behavioral reporting; so your team can focus on outcomes, not operations.
Instead of evaluating arbitrary numbers, pick the free phishing simulation tool that tests behavior under pressure, runs easily, and evolves with modern threats. Everything else is noise.
Free Simulated Phishing Email Templates: What Real Phishing Simulations Look Like
A free phishing simulation tool is only as strong as its templates (or its ability to generate one). If the phishing email simulator does not appear authentic, employees will identify the simulation, and the resulting data will lack validity.
What is an Example of a Phishing Email Simulation?

The following examples illustrate what effective templates inside free phishing simulation tools look like:
Security Alert (Unusual Login / MFA Prompt)
From: Security Team
Subject: Unusual sign-in detected
Opening: "We detected a login attempt from a new device. Verify now."
This phishing email template, like the March 2026 LastPass phishing campaign spoofing "unauthorized access" notices to push users to a fake SSO login, triggers fear-based compliance and tests credential reuse, which is an extremely common tactic in 2026.
IT Password Reset (Office 365 / Windows Alert)
From: IT Support
Subject: Password expires today — action required
Opening: "Confirm your password using the link below to avoid account lockdown.."
This free phishing simulation tool template works because urgency overrides verification. It tests whether users click without checking the domain.
M365 Migration / File Access
From: Microsoft 365
Subject: New secure file shared with you
Opening: "Access the encrypted file using the link below."
This simulated phishing email example scenario exploits trust in cloud platforms, which phishing attackers abuse in the right environment.
Pending Invoice (Finance / Vendor Attack)
From: Accounts
Subject: Invoice #48321 overdue
Opening: "Please review the attached invoice to avoid late penalties."
This simulated email phishing scenario mirrors real BEC attacks. According to DeepStrike.io 2026, BEC losses reached $2.77 billion in 2024.
CEO Wire Transfer Request
From: CEO
Subject: Urgent: Need quick transfer
Opening: "Are you available to process a confidential payment today?"
This free phishing simulation tool template tests authority pressure and decision-making under stress.
How to Run Simulated Phishing Emails
Running a simulated phishing email inside your free phishing simulation tools follows a structured process. Execution matters more than the template itself when it comes to phishing simulations.
- Start by selecting a realistic template inside your free phishing simulation tool. Choose a scenario relevant to your organization. Finance teams respond differently than HR or marketing.
- Then configure the sender. A simulated phishing email should use a spoofed or lookalike domain to mirror real attacks. According to Keepnet Labs 2026, trusted domains are exploited in 96% of phishing attempts.
- Set your landing page next. Your free phishing simulation tool should allow either:
- A credential capture (login) page to simulate a real phishing attack environment.
- An awareness page to educate immediately after wrong interaction.
- Define your target group inside the free phishing simulation tools. Separate by department, seniority, or risk profile to get meaningful insights.
- Send your simulated phishing email mid-week during (peak) business hours. That is when employees are busiest and most likely to react without verifying.
Note: Do not warn employees beforehand. A phishing simulation only works when behavior is natural, not staged.
Adaptive Security launches targeted microtraining the moment someone interacts with a simulation. No manual follow-up needed.
How to Test Your Employees With Free Phishing Simulation Tools
Modern phishing threats require a multichannel approach. According to Programs.com 2025 reports, deepfake fraud has grown over 2,000% since 2022. A free phishing simulation tool that only tests email misses the majority of real attack paths. That is why organizations should test employees across multiple attack vectors:
- Email phishing targeting credentials and links;
- Smishing exploiting urgency through mobile devices;
- Vishing using authority and real-time pressure;
- Deepfake phishing replicating executives or colleagues;
- Ransomware scenarios triggered through attachments or downloads.
This is where phishing simulations become behavioral testing, not awareness checking.
"So if we want meaningful behavioral change, it needs a lot more than just a pause. It needs cognitive scaffolding and system designs that account for all the dynamic interactions that go into a decision to click, download, or share. And that takes real work — more work than just an ad campaign and a slick video." - Bruce Schneier
Here is how to apply it in practice using your free phishing simulation tools:
- Identify your baseline across multiple channels. Run email, SMS, and at least one voice-based simulation to identify where risk is highest before starting regular phishing simulations.
- Separate employees by role and exposure. Finance, HR, and executives have different attack vectors than general employees. Your free phishing simulation tool should be able to adjust to that.
- Trigger immediate micro-learning feedback after interaction. This reinforces behavior at the moment of failure.
Running phishing simulations is step one. Building a program that actually changes behavior over time is step two. Adaptive Security handles both.
- Measure reporting behavior, not just failure rates. According to Keepnet Labs 2026, user reporting can increase by 178% with training—this is your early detection system.
- Introduce advanced simulations over time. Start simple, then move into deepfake and ransomware scenarios as employees improve.
That concludes the operational layer of phishing simulations. Once implemented, reinforce the strategy with continuous testing. While phishing simulations can reduce susceptibility significantly, it is nothing without consistency.
Free Phishing Simulation Examples by Industry
Effective free phishing simulation tools adapt scenarios to industry-specific risks. For example, a healthcare brand wouldn't get the same simulated phishing email as a finance company, just like the real phishing attacks.
The following outlines how free phishing simulation examples differ by sector:
- Healthcare: Fake EHR (Electronic Health Record) login request targeting patient data access.
- Finance: Urgent wire transfer approval from a spoofed executive.
- Retail: Vendor invoice with malicious attachment during peak season.
- Tech: GitHub or credential phishing targeting developers, and more.
According to Keepnet Labs 2026, 68% of phishing breaches in small businesses start with a single untrained employee. Industry-specific phishing simulation examples make that risk visible and fixable.
The more relevant your free phishing simulations are to daily workflows, the more accurate your risk assessment becomes.
Best Practices for Running Free Phishing Simulations Effectively
"The whole concept of security awareness training demonstrates how the computer industry has failed. We should be designing systems that won't let users choose lousy passwords and don't care what links a user clicks on." - Bruce Schneier
A free phishing simulation only drives real security outcomes when it changes behavior over time. Most free phishing simulation tools fail because they focus on testing employees instead of training them.
If you want to make the most of your free phishing simulation tools, follow these best practices to ensure the program reduces risk instead of just generating metrics:
- Get leadership buy-in before launching your free phishing simulation. Executive support increases participation, prevents internal pushback, and reinforces that security is a business priority, not just an IT initiative.
- Communicate the existence of your free phishing simulation tools without revealing timing. Employees should know simulations will happen, but unpredictability keeps behavior authentic and prevents "test-only" awareness.
- Use graduated difficulty in your free phishing simulation campaigns. Start with obvious phishing attempts, then progress to advanced attacks like BEC, smishing, vishing, and deepfake impersonation to build real-world detection skills.
- Never shame employees who fail a free phishing simulation. Public criticism reduces reporting rates and creates fear-based behavior. According to Keepnet Labs Security Awareness Training Statistics 2026, positive reinforcement leads to higher engagement and stronger long-term risk reduction.
- Always pair every free phishing simulation with immediate training. The moment someone clicks is the highest-impact learning opportunity. Without follow-up, even the best free phishing simulation tools fail to improve behavior.
- Track trends, not just click rates, in your free phishing simulation tools. Click rates alone do not reflect phishing simulation success. Focus on reporting rates, repeat failures, and time-to-detect improvements to measure real progress.
- Run free phishing simulation campaigns consistently, not occasionally. One-off simulations create temporary awareness, but continuous testing builds lasting instinct and resilience.
- Align your free phishing simulation scenarios with common attack patterns. According to Programs.com AI Cyberattack Statistics 2025, 82.6% of phishing emails are now AI-generated, meaning outdated templates no longer reflect real threats.
- Encourage a report-first culture through your free phishing simulation program. Faster reporting reduces breach impact, especially when phishing-related incidents take an average of 261 days to detect and contain (DeepStrike.io Phishing Statistics 2026).
Future Trends Among Free Phishing Simulation Tools
The next generation of free phishing simulation tools are already being shaped by AI, multichannel attacks, and rising regulatory pressure. Static simulations are already falling behind real-world cyber threats.
AI-generated phishing at scale
AI-driven phishing simulations are evolving to match attack patterns. According to Programs.com AI Cyberattack Statistics 2025, 82.6% of phishing emails are now created using AI, a 53.5% increase year-over-year. Every free phishing simulation must now reflect dynamic, personalized hooks instead of static templates.
Deepfake voice and video simulations
Voice and video-based attacks are becoming standard in free phishing simulation tools, and simulations that skip them leave teams exposed; Adaptive Security builds deepfake-aware scenarios that plug that gap. According to Programs.com AI Cyberattack Statistics 2025, deepfake fraud attacks have risen by over 2,000% since 2022. Simulations that ignore deepfake scenarios leave a major gap in preparation.
Multichannel attack chains
"The more effective phishing emails — the ones that result in people and companies losing lots of money — are personalized. Voice can be even more effective. It is not that being persuaded by an AI is fundamentally more damaging than being persuaded by another human, it is that AIs will be able to do it at computer speed and scale." - Bruce Schneier
A modern free phishing simulation does not focus on a single channel. Cyber attackers combine email, SMS, and voice in coordinated campaigns. Free phishing simulation tools are now evolving to replicate these chained attack paths in a single scenario.
Regulatory pressure and compliance requirements
Organizations are facing increasing pressure to prove human risk reduction. Free phishing simulation tools are becoming part of compliance frameworks, especially in industries handling sensitive data, where testing frequency and documentation are now expected.
Continuous simulation over periodic testing
Free phishing simulation tools are moving from annual or quarterly testing to continuous, dynamic programs. Instead of isolated campaigns, free phishing simulation tools are becoming always-on systems that adjust based on employee behavior and emerging cyber threats.
How Adaptive Security Approaches Phishing Simulations With an AI-powered Phishing Simulation Tool
A modern phishing simulation should prepare an organization's workforce for how phishing attacks occur in 2026. Most free phishing simulation tools stop at email, while real cyberattackers move across email, SMS, voice, and deepfake impersonation in a single campaign.

Adaptive Security takes a unique approach to phishing simulation by replicating the full attack sequence across channels. Instead of testing only whether someone clicks an email, the platform demonstrates how employees respond to a phishing email, followed by an SMS prompt, and then a voice call from a cloned executive voice, simulating the exact pattern used in social engineering attacks.
Adaptive Security also connects simulations directly to action. When someone fails a phishing simulation, they immediately receive targeted microtraining. When they report a threat, AI phish triage analyzes and resolves it in real time. Over time, risk scoring tracks precisely where the organization is improving and what needs to change.
Cyberattackers do not send one message and wait—most teams have only been tested that way. See how Adaptive Security simulates the full attack sequence.
Frequently Asked Questions About Free Phishing Simulation Tools
Do Free Phishing Simulations Work?
Yes, free phishing simulations effectively identify vulnerabilities and enhance employee training on phishing recognition when integrated into a broader security framework. Regular engagement significantly lowers risk and strengthens organizational preparation against actual phishing attempts.
Is It Legal to Use Brand Logos in Phishing Email Simulations?
Using brand logos in internal phishing simulations can be considered fair use for educational purposes, given that there is a clear disclosure and no intent to mislead. However, using trademarks without permission carries risks, as it may lead to legal action if misused or disruptive.
How Effective Are Simulated Phishing Emails?
Simulated phishing emails enhance security awareness and lower susceptibility, especially with regular campaigns. While results may vary, effective programs can reduce click rates to below 5%, improving vigilance, detection, and incident reporting among employees.
What Is a Phishing Attack Simulation?
A phishing attack simulation involves sending safe, simulated phishing emails / messages to employees to assess their ability to recognize cyberthreats. This training exercise mimics real tactics, boosts awareness, and helps identify vulnerable areas in security protocols without risking actual breaches.
What Is an Example of an AI Phishing Attack?
An AI phishing attack can replicate a company executive's writing style and send a context-aware email referencing a real project, recent meeting, or vendor invoice. The message may include a malicious link disguised as a legitimate workflow request, making it indistinguishable from normal business communication.
Are Phishing Simulations Legal?
Phishing simulations are legal when executed responsibly for internal training without gathering sensitive PII (Personally Identifiable Information). Organizations should ensure proper authorization, respect privacy laws, and avoid trademark violations to maintain both legal and ethical standards.
Can an Email Address Be Faked for Phishing?
Yes, email addresses can be faked through email spoofing, where attackers manipulate the sender's address to appear legitimate. This technique exploits insecure email protocols, making it crucial to enhance email security and employee awareness against such tactics.
What Is a Vishing Technique?
Vishing, or voice phishing, involves scammers using phone calls to deceive individuals into disclosing sensitive information. Attackers often pose as trusted entities, using urgency and pressure tactics to manipulate victims into revealing valuable data.
What Are the Best Free Phishing Simulation Tools for Small Businesses?
Gophish (open‑source), GoPhish's community templates, and PhishDef's free simulator provide full campaign capabilities. For serious AI‑powered scenarios, try Adaptive Security's AI‑powered phishing simulation tool.
Can I Run Phishing Simulations Without Paying for Software?
Yes. Open-source platforms such as Gophish, community-driven scripts, and free phishing simulation tools allow organizations to build, send, and track campaigns at no cost, requiring only basic server or cloud infrastructure.
Key Takeaways & Next Steps for Your Free Phishing Simulation
- Free phishing simulation tools are capable enough to run targeted realistic simulations. Organizations do not need a large budget to get started with modern phishing attack simulations across multiple channels.
- A free phishing simulation must go beyond email. Smishing, vishing, and deepfake scenarios, used in combination, reflect how attackers operate today.
- AI-generated simulations are now the baseline. Free phishing simulation tools that rely on static templates fail to represent modern, dynamic cyber threats.
- Behavior change matters more than click rates. A free phishing simulation should measure reporting rates, repeat failures, and response time. Monitoring only click events provides limited insight into overall employee risk exposure.
- Consistency outperforms one-time testing. Continuous free phishing simulation programs reduce risk faster, compared to the weak results from annual or occasional campaigns.
- Immediate microtraining after failure improves performance drastically. The moment someone fails a free phishing simulation is when they are most likely to learn and change behavior.
A free phishing simulation is ultimately a decision-making tool. It reveals where an organization is exposed, how employees respond under pressure, and which attack paths are most likely to succeed.Now you know what strong looks like. See whether your team's phishing exposure matches expectations, or uncover gaps hiding in plain sight.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents