Cybersecurity awareness training platform features determine whether a program produces measurable behavior change or a compliance checkbox. The gap between those two outcomes is exactly what cyberattackers exploit. The human element is the biggest cause of data breaches, while AI-powered phishing has accelerated the pace and precision of every channel cyberattackers use.
Choosing the right cybersecurity awareness training platform has transformed from a procurement detail to a financial decision. According to the World Economic Forum's Global Cybersecurity Outlook 2025, 72% of organizations reported a rise in cyber risks, and 47% identified adversarial advances powered by generative AI as their primary concern.
This guide outlines the essential cybersecurity awareness training platform features that distinguish modern, AI-native solutions from legacy tools, enabling organizations to identify critical capability gaps:
- Multi-channel phishing simulations spanning email, voice, SMS, and deepfake video as core cybersecurity awareness training platform features;
- Open-source intelligence (OSINT) personalization that mirrors how cyberattackers research targets;
- Continuous human risk scoring that replaces static completion-rate tracking with a live behavioral readiness metric;
- AI-powered phish triage that auto-resolves clear-cut cases without analyst review;
- Compliance-mapped cybersecurity awareness training platform features, including audit-ready reporting.
Stop measuring training in completion rates and start measuring it in behavior change with Adaptive Security.
What a Cybersecurity Awareness Training Platform Does and Why Legacy Tools Fall Short
A cybersecurity awareness training platform is a dedicated software system that equips employees with the knowledge, skills, and behavioral instincts to recognize and resist cyberattacks. Coverage spans phishing emails, AI-generated voice impersonations, deepfake video calls, and OSINT-personalized spear phishing. These platforms operate at the human layer of security — an attack surface no firewall, endpoint detection tool, or email gateway is designed to address.
Legacy cybersecurity awareness training platforms were architected for a single channel (email) and a single threat type (static phishing links). That architecture made sense in 2015. It fails today, when cyberattackers clone executive voices in under a minute, generate personalized spear phishing using OSINT, and coordinate simultaneous email, SMS, and video call cyberattacks against the same employee.
Cybersecurity awareness training platform features confined to email templates cannot prepare employees for a threat surface that has moved decisively beyond the inbox.
Awareness Versus Training: Two Outcomes Cybersecurity Awareness Training Platform Features Must Cover
Awareness is cognitive and shapes how an employee thinks about cyber threats, including whether an urgent wire-transfer request from the 'CEO' deserves scrutiny before acting. Cybersecurity awareness training is behavioral, building the reflexes to act correctly under pressure, such as picking up the phone to verify an instruction before approving a transaction.
A cybersecurity awareness training platform that delivers only awareness modules produces employees who understand risk in theory but freeze or comply when confronted with a convincing real-time deepfake call. The cybersecurity awareness training platform features determine whether the program drives measurable behavior change or simply generates completion certificates for auditors.
Equip employees with reflexes that hold under pressure through Adaptive Security cybersecurity awareness training.
Cybersecurity Awareness Training Platform Features: Phishing Simulation Features
Cybersecurity awareness training platform features that stop at email phishing simulations now miss the majority of how coordinated social engineering cyberattacks actually unfold. Single-channel testing measures only one dimension of employee susceptibility while leaving voice, SMS, and video channels entirely untested. According to ENISA Threat Landscape 2025, phishing accounts for approximately 60% of all observed initial intrusion cases, and the agency reports that AI-supported phishing campaigns represented more than 80% of observed social engineering activity worldwide by early 2025.
Multi-channel cybersecurity awareness training platform features extend the testing surface to include vishing, smishing, and deepfake video, the exact channels cyberattackers combine in sequenced campaigns designed to overwhelm an employee's ability to verify. The architectural gap between single-channel and multi-channel platforms has become one of the most consequential evaluation criteria in selecting a cybersecurity awareness training platform.
Cybersecurity Awareness Training Platform Features: Email Phishing Simulations and OSINT Personalization

Email phishing simulations are a foundational part of cybersecurity awareness training platform features. Controlled tests send realistic fake phishing emails to employees and measure who clicks, who submits credentials, and who reports the message. The primary metric is Phish-prone Percentage (PPP): the share of employees who fall for a simulated cyberattack at any given point. Over successive simulation rounds, a well-run cybersecurity awareness training program drives PPP down measurably. Over successive simulation rounds, the baseline vulnerability data turns into a trackable risk reduction curve security leaders can present to boards.
OSINT personalization separates hyperrealistic phishing simulations from generic templates. By analyzing the same public data a cyberattacker would use, job titles, reporting relationships, recent projects, vendor names, and LinkedIn activity, the simulation engine constructs cyberattack scenarios tailored to each employee's specific context. Adaptive Security evaluates 1,000+ public data points per employee to build simulations a recipient would have no reason to question on appearance alone.
See how Adaptive Security's OSINT-personalized phishing simulations expose the gap that generic templates leave open.
Cybersecurity Awareness Training Platform Features: Vishing, Smishing, and Deepfake Video Simulations
Vishing and smishing extend simulation coverage to the channels cyberattackers most frequently pair with email in coordinated campaigns. Vishing simulations deliver AI-cloned voice calls and pre-recorded voicemails that impersonate executives, IT helpdesk staff, or vendors. Smishing simulations send realistic SMS attack sequences to employee mobile numbers, mimicking HR alerts, authentication prompts, or urgent payment requests.
The combination matters because cyberattackers rarely rely on one channel alone. A coordinated campaign typically opens with a spoofed email establishing context, follows with a vishing call adding authority, and closes with an SMS prompt driving final action. An employee who has only practiced resisting email phishing has no rehearsed response when the "CFO" calls 20 minutes after sending the invoice request.
Deepfake video simulations represent the highest-fidelity test cybersecurity awareness training platform features can deliver. Real-time or pre-rendered AI impersonations of company executives, delivered via video message or simulated call, request actions like credential resets, fund transfers, or policy exceptions. The $25 million wire fraud executed against engineering firm Arup in 2024 succeeded because the cyberattacker used deepfake video to impersonate a CFO on a live call with multiple fabricated participants. Email filters and password policies are not designed to intercept that type of cyberattack.
Cybersecurity Awareness Training Platform Features: Point-of-Failure Education
Point-of-failure education is the highest-leverage learning event in any cybersecurity awareness training program. When an employee clicks a simulated phishing link or complies with a vishing call, the cybersecurity awareness training platform immediately surfaces a just-in-time microlearning module: a brief, focused lesson tied directly to the specific cyberattack type that just fooled them.
That moment of heightened attention, when the mistake is fresh and the stakes feel real, produces retention rates that scheduled quarterly cybersecurity awareness training cannot replicate. Employees learn more than what happened; they practice the correct decision path they should have taken, building the muscle memory that changes behavior under pressure.
Move beyond email-only testing and prepare employees for the multi-channel attacks Adaptive Security simulates end-to-end.
Cybersecurity Awareness Training Platform Features and Training Content That Drive Real Behavior Change
The content and delivery architecture of a cybersecurity awareness training platform determines whether employees actually change behavior or simply click through slides to satisfy a compliance checkbox. Most legacy cybersecurity awareness training platform features were built for the latter. AI-powered cyberattackers now use OSINT to craft attacks personalized to individual employees, which means generic annual cybersecurity awareness training content cannot produce the situational awareness needed to stop them.
Microlearning, Role-Based Personalization, and AI-Powered Content Generation
Microlearning is a cybersecurity awareness training platform feature that breaks content into focused sessions under 10 minutes, designed to align with how the brain encodes and retains information. Effective platforms pair bite-sized modules with scenario-based formats that put employees inside realistic decision points: recognizing a spoofed vendor email before wiring funds, or questioning an urgent voice request that sounds like the CFO.
A finance analyst and a software developer face fundamentally different attack surfaces. A cybersecurity awareness training platform built on generic content delivers the same business email compromise (BEC) module to both, which means neither receives cybersecurity awareness training that reflects the specific cyber threats aimed at their role. Personalized programs assign role-specific modules, adjust simulation difficulty based on individual performance history, and prioritize content for the threat vectors most likely to reach each employee.
Generative AI eliminates the stale-content problem that plagues legacy libraries. An AI Content Studio built into a modern cybersecurity awareness training platform can generate a fully structured training module from any text prompt or uploaded policy document in minutes. When a new social engineering tactic surfaces, a novel deepfake vishing approach or a fresh BEC variant, security teams can build and deploy a targeted module the same week.
Compliance-Mapped Cybersecurity Awareness Training Platform Features That Double as Behavioral Skill Building
Compliance-mapped cybersecurity awareness training platform features serve two functions: satisfying regulators and building security behavior. A strong cybersecurity awareness training platform maps modules to SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001, so that completion data is audit-ready and exportable for GRC teams on demand.
The content library must extend beyond policy attestation into the practical cyber threat categories employees actually encounter: AI-generated spear phishing, deepfake executive impersonation, vishing, smishing, and credential theft scenarios. Effective cybersecurity awareness training platforms treat training as the development of a capability rather than the assignment of a penalty.
Replace stale content libraries with the Adaptive Security AI Content Studio and match the cyber threats employees face this week.
Human Risk Scoring and Dynamic Learning Cybersecurity Awareness Training Platform Features
A human risk score is a dynamic, quantitative measure of an individual employee's susceptibility to social engineering cyberattacks. It is calculated continuously from simulation behavior, cybersecurity awareness training completion, OSINT exposure data, and credential breach history. Unlike a completion rate, which only confirms an employee watched a module, a human risk score reflects actual behavioral readiness: whether that employee clicks on simulated phishing, reports suspicious messages, and demonstrates recall under pressure.

According to the World Economic Forum Global Cybersecurity Outlook 2026, 73% of survey respondents reported that they or someone in their network had been personally affected by cyber-enabled fraud during 2025, underscoring why behavioral readiness has become the metric that matters.
How Human Risk Scoring Models Work
Modern cybersecurity awareness training platforms include risk scoring engines that aggregate signals from multiple behavioral and exposure inputs simultaneously. Simulation performance carries the heaviest weight: an employee who clicks phishing emails and ignores vishing calls contributes more risk than one with 100% cybersecurity awareness training completion but zero simulation failures.
OSINT profiling adds a second dimension by evaluating an employee's public digital footprint across social media, professional networks, conference appearances, and published credentials. Credential breach history layers in a third signal that purely behavioral data cannot capture. The insertion of "cybersecurity awareness training platform features, such as purely behavioral data, cannot capture. The result is a composite score that security teams can read at the individual, department, and organizational level without manual analysis.
Dynamic Learning and Executive Exposure Monitoring
Dynamic learning uses the human risk score as a feedback mechanism rather than a passive reporting metric. When an employee's score crosses a configurable risk threshold, triggered by a simulation failure, a new credential breach, or a spike in OSINT exposure, the cybersecurity awareness training platform automatically enrolls them in targeted training without manual intervention. Dynamic employee groups update in real time, meaning a finance team member who fails a BEC simulation today receives role-specific remediation cybersecurity awareness training that afternoon, instead of at the next quarterly refresh.
Executive exposure monitoring treats OSINT profiling as a distinct priority for C-suite employees. Their public presence is extensive by necessity: keynote speeches, earnings calls, media interviews, and LinkedIn activity generate thousands of data points that cyberattackers use to construct deepfake impersonations. The cybersecurity awareness training platform features map each executive's specific public attack surface across 1,000+ data points, identifying the exact channels and information types that make them vulnerable to impersonation.
Repeat offenders and high-risk users across all levels receive dedicated remedial training tracks, with automated re-enrollment triggered every time simulation behavior signals persistent vulnerability. The goal is a measurable, declining human risk score across successive simulation cycles.
Convert human risk into a continuously declining metric using Adaptive Security risk monitoring and mitigation.
Reporting, Analytics, and Compliance Cybersecurity Awareness Training Platform Features Security Teams Need
Cybersecurity awareness training platform features only justify their cost when they produce evidence: evidence of behavior change, evidence of risk reduction, and evidence of regulatory compliance. Without structured reporting and analytics, security leaders manage human risk blind, unable to prove program ROI to boards or satisfy auditors. The reporting infrastructure should be built before launching a single simulation campaign because the metrics tracked determine whether the cybersecurity awareness training platform's features drive outcomes.
Admin Dashboards Built for Security Teams and Boards
A modern Admin Portal surfaces the right data at the right altitude for every audience. At the individual level, security teams need each employee's simulation click history, training completion status, and a dynamic human risk score that updates based on behavior. At the department level, dashboards display aggregated phishing simulation click-through rate trends, completion rates by team, and comparative risk scores across business units so program managers identify which departments carry the highest exposure.
Board-ready reporting is where most legacy cybersecurity awareness training platform features fall short. Executives and audit committees do not need raw click-through rate tables; they need a single risk score, a trend line showing improvement over time, and a clear statement of what that improvement means in business terms. Per IBM Cost of a Data Breach Report 2025, the global average breach cost reached $4.44 million, while the U.S. average climbed to a record $10.22 million.
Compliance Reporting That Survives Audit Scrutiny
Compliance reporting requires documentation that satisfies auditors. The best cybersecurity awareness training platform features produce training completion records that are automatically timestamped, tied to individual employee accounts, and exportable on demand. Content mapped to SOC 2 demonstrates that personnel are educated on security policies. HIPAA mapping satisfies workforce training mandates for protected health information handlers, while GDPR, PCI-DSS, and ISO 27001 mapping addresses each framework's specific awareness requirements without requiring manual record assembly before every audit cycle.
Policy attestation workflows close a gap that pure training metrics leave open. A cybersecurity awareness training platform that tracks policy reads, logs acknowledgment timestamps, and generates audit-ready attestation records eliminates the manual spreadsheet process that consumes GRC team hours before every assessment.
KPIs That Measure Effectiveness Rather Than Activity
Five KPIs separate cybersecurity awareness training programs that demonstrate measurable risk reduction from those that demonstrate only activity:
- Phishing simulation click-through rate reduction tracking the percentage of employees who interact with simulated cyberattacks over time;
- Training completion rates confirming engagement beyond enrollment alone;
- Employee risk score improvement measuring whether high-risk individuals trend toward lower risk profiles after targeted remediation;
- Mean time to triage reported phish connecting cybersecurity awareness training directly to incident response efficiency;
- Incident volume trends tracking whether real-world phishing reports and confirmed security events are declining as the program matures.
Trade activity reporting for the defensible risk-reduction case Adaptive Security puts in front of every audit committee.
Cybersecurity Awareness Training Platform Features: Phish Triage and Automated Response Features
Phish triage is the process of classifying employee-reported emails as Safe, Spam, or Malicious and taking the appropriate response action. An effective cybersecurity awareness training platform triage workflow needs a one-click reporting tool employees will actually use, AI classification with confidence scoring that auto-resolves clear-cut cases, and org-wide inbox remediation that contains confirmed cyber threats before they spread.
AI Email Classification That Reduces Analyst Alert Fatigue
Manual SOC review of reported phishing emails is no longer viable at enterprise scale. The Vectra AI 2023 State of Threat Detection study of 2,000 SOC analysts found they receive an average of 4,484 alerts daily, with 67% going unreviewed due to alert fatigue. Applying that same manual model to a growing queue of employee-reported phish creates a predictable outcome: real cyber threats wait in line while analysts burn out.
AI-powered triage solves this by classifying every reported email automatically. Adaptive Security's Phish Triage assigns each submission a confidence score and category, then auto-resolves submissions that exceed configurable thresholds. Cases scoring Spam at 90% or above, or Malicious at 95% or above, resolve without analyst intervention. VirusTotal integration adds a verification layer to every classification decision, with URLs and attachments checked against aggregated threat intelligence before a verdict is issued.
The Phish Alert Button and Org-Wide Inbox Remediation
Triage automation is only as useful as the volume and quality of emails employees actually report. The Phish Alert Button is a one-click reporting tool embedded natively inside Gmail and Outlook, including Outlook mobile, that removes every friction point standing between an employee's suspicion and a submitted report. There is no forwarding address to remember, no separate portal to open, and no manual steps between the employee's suspicion and the security team's queue.
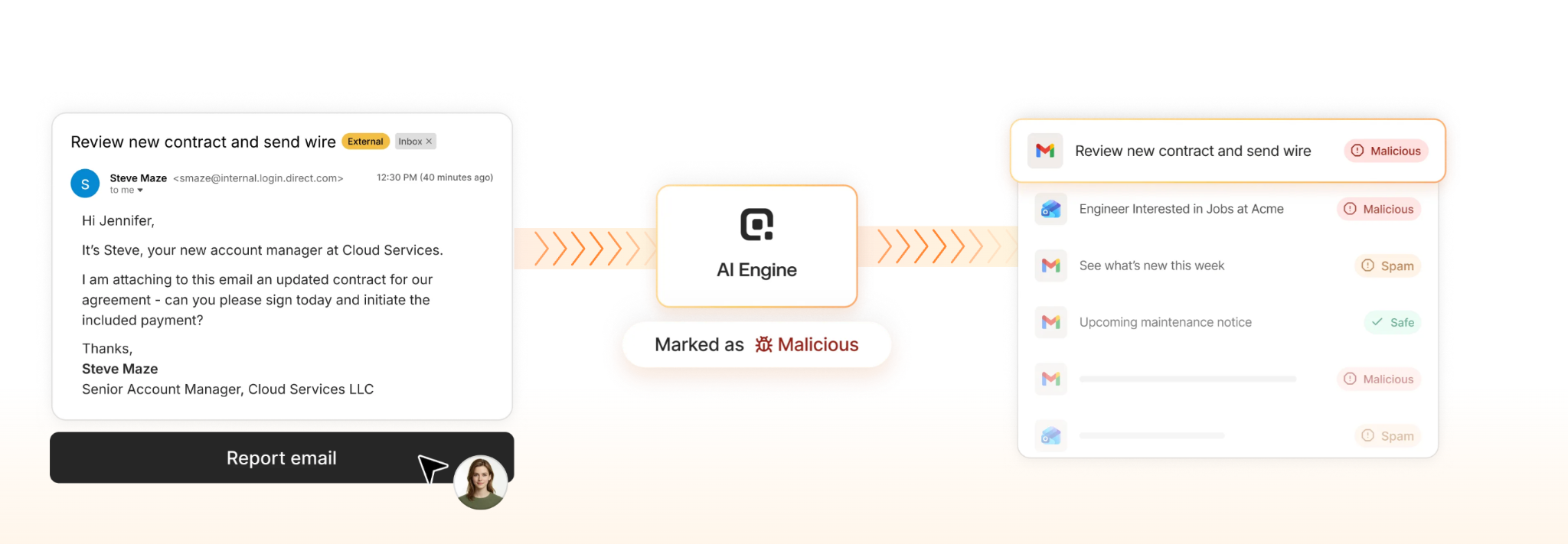
Once a reported email is confirmed Malicious, the cyber threat extends beyond the employee who reported it. The same message likely reached dozens or hundreds of inboxes across the organization. Adaptive Security's Phish Triage executes org-wide inbox remediation in a single click, pulling the confirmed malicious email from every affected inbox simultaneously. Every remediation action is fully reversible, which matters for security teams that need to move fast under pressure without risking permanent data loss.
Compress average time to respond from hours to minutes with Adaptive Security Phish Triage auto-resolving clear-cut cases.
Cybersecurity Awareness Training Platform Features: Integrations and Deployment for Enterprises
A cybersecurity awareness training platform that cannot connect to the systems employees already use every day will sit unused regardless of how strong its content library is. Enterprise-grade deployment requires native email environment integration, automated user provisioning, identity management, and global content delivery, all configured without demanding weeks of IT resources. The gap between platforms that get this right and those that do not becomes visible on day one.
Microsoft 365, Google Workspace, SSO, and HRIS Connectivity
Microsoft 365 and Google Workspace together represent the dominant productivity infrastructure in the enterprise market. Any cybersecurity awareness training platform that requires complex mail flow reconfiguration creates immediate friction with IT and delays time-to-value. The most effective platforms deploy via a two-click integration with both environments, with no MX record changes, DNS reconfiguration, or scheduled maintenance window required. For a mid-sized organization of 500 to 2,000 employees, this architecture compresses full deployment from weeks to minutes.
Single sign-on (SSO) via SAML 2.0, Okta, and Azure Active Directory is among the non-negotiable cybersecurity awareness training platform features for enterprise IT teams. SCIM provisioning automates the user lifecycle entirely; when a new employee joins, their training account provisions automatically from the HRIS, and when someone leaves, access terminates without manual intervention. Third-party vendors and contractors represent a distinct consideration, with access control supporting scoped provisioning that grants simulation and cybersecurity awareness training access without extending permissions into internal systems.
GRC integrations extend this infrastructure further, allowing cybersecurity awareness training completion data to flow directly into compliance reporting systems. SCORM export provides an additional compatibility layer for organizations with existing LMS investments, protecting prior infrastructure while adding simulation capability the LMS alone cannot deliver.
Multi-Language Localization for Global Deployment
Cybersecurity awareness training platform features delivered only in English fail multinational workforces and create compliance exposure in jurisdictions where employee communication requirements apply under frameworks such as GDPR. Access to 39+ languages is the baseline for ensuring every employee receives the same quality of behavioral training regardless of their primary language.
Localization at this scale requires more than machine translation. Effective cybersecurity awareness training platform features adapt simulation content, including phishing email copy, SMS text, and voice scripts, to reflect regional language patterns and local business conventions. A cyberattacker targeting a German-speaking employee will craft a cyberattack that sounds native; cybersecurity awareness training platform features must match that fidelity. White-labeling and custom-branding capabilities matter for managed service providers (MSPs) and enterprise resellers deploying the cybersecurity awareness training platform across client organizations.
Deploy cybersecurity awareness training to a global workforce in days rather than quarters with Adaptive Security's two-click integrations.
Structuring a Continuous Program Using Cybersecurity Awareness Training Platform Features
Annual compliance training was built to satisfy auditors rather than to defeat cyberattackers. Cybersecurity awareness training platform features work only when deployed as a continuous cadence: monthly phishing simulations, quarterly microlearning, and real-time remediation triggered the moment an employee fails a test.
The difference between cybersecurity awareness training platform features that shift behavior and ones that simply collect completion records almost always comes down to cadence structure and content freshness.
Setting the Right Training Frequency Across Three Layers
The starting point is separating three distinct cybersecurity awareness training activities by frequency and purpose:
- Phishing simulations run monthly, frequent enough to keep threat recognition sharp without creating simulation fatigue;
- Microlearning modules deploy quarterly, giving employees concentrated skill-building on emerging attack types without overwhelming workload;
- Real-time remediation training triggers immediately when an employee fails a simulation, delivering a targeted lesson at the exact moment it has the most impact on retention.
This layered structure matters because spaced repetition is how behavioral change actually forms. A single annual training session fades within weeks. Monthly exposure to realistic simulation scenarios combined with just-in-time remediation builds the pattern recognition that holds under pressure during a real cyberattack.
Gamification, Generative AI Content, and ROI Framing

Leaderboards, progress tracking, and reward mechanics change completion rates and cybersecurity awareness training persistence. The key is framing these features around skill development and team performance, never around who failed a simulation last month. When employees see their own human risk score improving over time, they engage with training as a personal capability benchmark rather than a compliance obligation.
Generative AI content engines keep the training library fresh against a moving threat landscape. Security teams can build entirely custom modules from scratch in minutes by prompting the cybersecurity awareness training platform features with a threat scenario or policy document, rather than waiting on a vendor content calendar. When cyberattackers shift tactics by combining SMS phishing with a deepfake voicemail, a generative AI engine lets organizations build a matching simulation scenario immediately.
The return on cybersecurity awareness training is straightforward to calculate when framed against breach costs. According to the FBI's IC3 2024 Internet Crime Report, total reported losses reached $16.6 billion across 859,532 complaints, a 33% year-over-year increase, with business email compromise (BEC) alone accounting for $2.77 billion across 21,442 incidents. Against the annual cost of a cybersecurity awareness training platform, the math supports this category as one of the highest-return investments in any security budget.
Build a continuous training cadence that compounds behavior change month over month inside Adaptive Security.
Why AI-Powered Threats Are Reshaping Cybersecurity Awareness Training Platform Features
The cybersecurity awareness training platform features that defined the category three years ago, static phishing email libraries, annual compliance modules, and generic click-rate reporting, were designed for a threat environment that no longer exists. Generative AI has fundamentally changed the scale, precision, and channel breadth of social engineering cyberattacks, and platforms built before this era cannot simulate what employees face today.
How Generative AI Turned Spear Phishing Into a Scalable Weapon
Spear phishing has always been effective because it is personal. What changed is the cost. Crafting a convincing, personalized cyberattack once required hours of manual research; generative AI compresses that process into minutes. Cyberattackers now use OSINT scraped from public sources to generate hyper-personalized emails at scale, referencing a target's actual colleagues, recent projects, and employer-specific terminology with near-perfect accuracy.
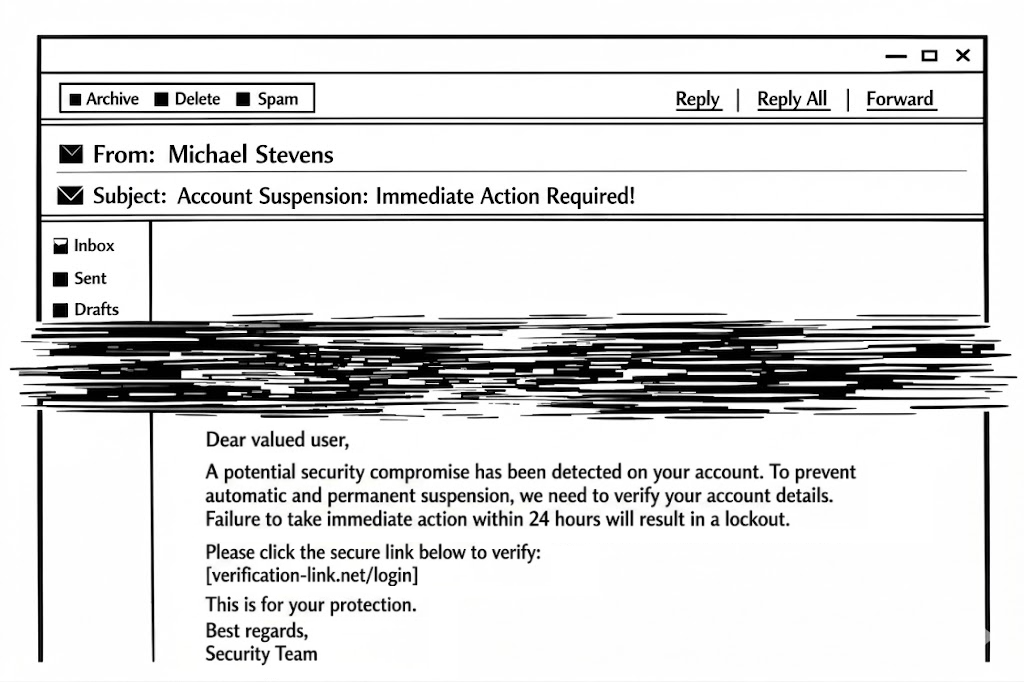
Per IBM Cost of a Data Breach Report 2025, phishing overtook stolen credentials as the most common initial cyberattack vector, responsible for 16% of breaches at an average cost of $4.8 million. The defensive capability that closes this gap is OSINT personalization, a cybersecurity awareness training platform feature that mirrors cyberattacker methodology by building phishing simulations from each employee's actual public footprint.
AI Voice Cloning Means Vishing Defense Cannot Wait
Vishing has historically been the most underrepresented attack vector in cybersecurity awareness training programs, partly because it was difficult to simulate at scale. AI voice cloning eliminated that barrier for cyberattackers. A voice clone now requires only a few seconds of publicly available audio from a conference call, earnings release, or podcast, after which threat actors can deliver a convincing replica of an executive's voice via live call or voicemail.
The cybersecurity awareness training platform feature requirement that follows is vishing simulation capability: the ability to deliver AI-cloned voice calls and voicemails to employees as part of a structured cybersecurity awareness training program, so that the first time they hear an AI voice impersonating leadership is in a safe, recoverable environment.
According to the Deloitte's Generative AI Is Expected to Magnify the Risk of Deepfakes and Other Fraud in Banking 2024, fraud losses in the United States facilitated by generative AI are projected to climb from $12.3 billion in 2023 to $40 billion by 2027, a compound annual growth rate of 32%. Employees who experience these scenarios with cybersecurity awareness training platform features build the pattern recognition that holds when the real call arrives.
Deepfake Video and Coordinated Multi-Channel Attacks
Live video was once treated as proof of identity. Deepfake generation tools now operate in real time on consumer hardware, making executive impersonation on video calls an accessible cyberattack vector for a widening range of threat actors. An employee who has only been trained to spot suspicious email headers has no framework for evaluating a call where the CFO and three familiar colleagues all appear on screen, every face synthetic.
According to DeepStrike's data, online deepfakes grew from roughly 500,000 in 2023 to about 8 million in 2025, an annual growth rate approaching 900%. Multi-channel simulation capability, combining email, voice, SMS, and deepfake video under one cybersecurity awareness training platform, mirrors how real attacks actually unfold across coordinated channels.
The cybersecurity awareness training platform features required to defend against AI-era social engineering are the criteria by which platforms must now be evaluated. The deciding criterion is no longer content volume or compliance checkbox coverage; it is the ability to simulate and defend against the cyberattacks actually reaching employees today.
Test employees against the AI-era attacks generic templates were never designed to replicate, simulated end to end by Adaptive Security.
See Adaptive Security's Cybersecurity Awareness Training Platform Features in Action
Choosing based on a cybersecurity awareness training platform features list alone leaves the most important question unanswered: does it actually change how employees behave under pressure? Adaptive Security was built to answer that question with evidence rather than a brochure. The platform combines OSINT-personalized phishing simulations across email, voice, SMS, and deepfake video, a continuously updated human risk score for every employee, AI-powered Phish Triage with org-wide inbox remediation, and compliance-mapped cybersecurity awareness training platform features covering SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001.
What separates Adaptive Security from legacy cybersecurity awareness training platforms is the unified architecture. Most vendors deliver simulation, training content, risk scoring, and phish triage as four disconnected products glued together by manual reporting. Adaptive Security delivers them as a single system where a finance manager who fails a deepfake vishing test this morning is enrolled in role-specific remediation cybersecurity awareness training that afternoon, with the action automatically logged in the GRC export that ships to the auditor next quarter.
Seeing those workflows operate in a real environment, on a real employee population, against the multi-channel cyberattacks organizations face today, is the only reliable way to evaluate fit. A self-guided product tour walks through the cybersecurity awareness training platform with no sales conversation required, and a personalized demo walks through it with the team that built it.
Let outcome data drive the cybersecurity awareness training platform decision; see Adaptive Security in a live environment.
Frequently Asked Questions About Cybersecurity Awareness Training Platform Features
The questions organizations ask about cybersecurity awareness training platform features reveal how much the category has evolved in the past two years. What was once a checklist of modules and completion rates is now a procurement decision with direct implications for organizational resilience against AI-powered social engineering. The answers below reflect current platform capabilities, compliance requirements, and measurable outcomes.
What is a cybersecurity awareness training platform?
A cybersecurity awareness training platform is a software system that teaches employees to recognize, resist, and report cyber threats, including phishing, social engineering, vishing, smishing, deepfake impersonation, and BEC. Modern platforms combine interactive cybersecurity awareness training modules, multi-channel phishing simulations, automated remediation, and continuous human risk scoring to change how employees behave when targeted, beyond simply what they know.
What are the most important cybersecurity awareness training platform features?
The features that separate high-performing cybersecurity awareness training platforms from legacy tools are the ones that mirror how attacks actually happen today. The most important include:
- Multi-channel phishing simulations covering email, voice, SMS, and deepfake video;
- OSINT-personalized scenarios replicating how cyberattackers target specific employees using public data;
- Role-based cybersecurity awareness training modules delivering content based on job function and individual risk profile;
- Automated remediation enrolling high-risk employees in targeted training without manual intervention;
- Risk scoring dashboards quantifying human risk at the individual, team, and organizational level;
- Compliance-mapped content covering SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001;
- Phish triage automation with one-click reporting, AI classification, and org-wide inbox remediation.
The defining test is whether a cybersecurity awareness training platform can simulate the cyber threats employees actually face in 2026, including AI-generated deepfakes and voice-cloned executives, and automatically course-correct based on how each individual responds.
What is the difference between cybersecurity awareness training and human risk management?
Cybersecurity awareness training delivers content and tests employees with phishing simulations, then measures completion and pass/fail outcomes. Human risk management (HRM) goes further: it continuously calculates a dynamic human risk score for every employee based on simulation behavior, training engagement, OSINT exposure data, and credential breach history, then automatically adjusts training and simulation difficulty without manual intervention. The most capable cybersecurity awareness training platforms deliver both under a single unified interface.
How do cybersecurity awareness training platforms support GDPR, HIPAA, PCI-DSS, and SOC 2 compliance?
Each framework requires documented evidence that employees with access to sensitive data have been trained on security policies and risks. SOC 2 requires demonstrable workforce training on security procedures. HIPAA mandates training on privacy and security safeguards for protected health information. GDPR requires data protection training for employees who handle personal data. PCI-DSS requires annual cybersecurity awareness training for all personnel with cardholder data access. Cybersecurity awareness training platform features that map content to these frameworks and generate audit-ready completion reports give compliance officers the documentation they need without building it manually.
What is a human risk score and how is it calculated?
A human risk score is a numerical representation of an individual employee's likelihood of falling for a social engineering cyberattack, typically on a 0 to 100 scale. Cybersecurity awareness training platforms calculate it by combining multiple behavioral and contextual signals:
- Phishing simulation click and report rates across email, voice, and SMS channels;
- Cybersecurity awareness training module completion and assessment results;
- OSINT exposure indicators including data breach history, public social media presence, and executive visibility;
- Historical reporting behavior on suspicious messages.
Scores update continuously as new data arrives, allowing automated remediation to trigger immediately when an employee's risk crosses a defined threshold.
How does just-in-time training work after a failed phishing simulation?
Just-in-time training, also called microlearning, delivers a short, targeted cybersecurity awareness training module to an employee immediately after they fall for a simulated cyberattack. Rather than waiting for the next scheduled training cycle, the employee receives relevant context within seconds of clicking a malicious link or complying with a simulated vishing call. Modules delivered this way are typically under five minutes, scenario-specific, and designed to reinforce the behavioral habit of pausing and verifying.
What integrations should a cybersecurity awareness training platform support?
The integrations that matter most for fast deployment include Microsoft 365 and Google Workspace for email simulation delivery, SSO providers such as Okta and Azure AD for single sign-on, SCIM provisioning for automated user management synced to the employee directory, and HRIS systems for role-based training assignment. GRC platform integrations enable compliance tracking without double entry. The deployment standard today is two-click integration with no MX record changes required.
How long does it take to deploy a cybersecurity awareness training platform?
Deployment time depends almost entirely on the integration model. Cybersecurity awareness training platforms that connect directly to Microsoft 365 or Google Workspace via API, without requiring MX record changes or IT infrastructure modifications, can be fully operational within minutes. Employee rosters sync automatically via SCIM or HRIS integration, and the first phishing simulation campaign can launch within days of setup. The practical time-to-value benchmark for a modern cybersecurity awareness training platform is days rather than weeks.
What KPIs should organizations use to measure cybersecurity awareness training effectiveness?
The metrics that reflect genuine behavior change rather than checkbox compliance include phishing simulation click-through rate over time, employee reporting rate for suspicious messages, mean time to report a suspected phish, completion rates by department and role, and individual and team human risk score trends. Click-through rate alone is insufficient: cybersecurity awareness training platform features that lower clicks without increasing reporting rates have not built a security-aware workforce.
What is the typical ROI of a cybersecurity awareness training platform?
The ROI case is built on breach cost avoidance. According to the AFP 2025 Payments Fraud and Control Survey Report, 63% of organizations experienced BEC attempts in the prior year, demonstrating how broadly the cyber threat lands on every finance team. When organizations reduce phishing click-through rates substantially through continuous phishing simulations, they directly lower the probability of credential theft and social engineering incidents that initiate the majority of breaches. Security leaders presenting ROI to boards should frame cybersecurity awareness training spend as a fractional cost of a single avoided incident.
How does a cybersecurity awareness training platform simulate vishing, smishing, and deepfake attacks?
Multi-channel simulation platforms generate realistic cyberattack scenarios across voice, SMS, and video by using AI synthesis tools to clone executive voices, compose targeted text messages, and render deepfake video impersonations of company leaders.
A vishing simulation places an AI-generated phone call to an employee using a voice modeled on a senior executive.
Smishing simulations send crafted SMS messages mirroring the format and urgency of real attack campaigns.
Deepfake video simulations present employees with realistic video calls featuring AI-generated impersonations, exposing them to the same coordinated multi-participant fraud format documented in recent enterprise wire fraud incidents. All three channels can be personalized using OSINT.
Can a cybersecurity awareness training platform train third-party vendors and contractors?
Yes. A cybersecurity awareness training platform that supports external user enrollment, role-based module assignment, and compliance-mapped completion reporting can extend the organization's human risk program beyond its direct workforce. Audit-ready documentation covering third-party cybersecurity awareness training participation is also a requirement under several compliance frameworks, including SOC 2 and ISO 27001, when vendors are classified as having access to in-scope systems or data.
Key Takeaways
- Cybersecurity awareness training platform features must mirror the cyberattacks employees actually face today, spanning email, vishing, smishing, and deepfake video rather than email-only testing.
- OSINT personalization separates hyperrealistic phishing simulations from generic templates, building scenarios from each employee's real public footprint.
- Human risk scoring replaces static completion rates with a continuously updated measure of behavioral readiness, triggering automated remediation the moment risk crosses threshold.
- Compliance-mapped cybersecurity awareness training content satisfies SOC 2, HIPAA, GDPR, PCI-DSS, and ISO 27001 while doubling as practical skill-building rather than policy attestation alone.
- AI-powered phish triage with one-click reporting and org-wide inbox remediation compresses mean time to respond from hours to minutes without expanding analyst headcount.
- Two-click integration with Microsoft 365, Google Workspace, SSO, SCIM, and HRIS systems compresses deployment from weeks to minutes for mid-sized and enterprise organizations.
- A continuous cybersecurity awareness training program built on monthly phishing simulations, quarterly microlearning, and real-time remediation produces measurable behavior change that annual compliance training cannot replicate.
- Generative AI content engines keep the cybersecurity awareness training platform library current against a threat landscape that shifts faster than any static library can track.
Auditors expect accountability from your contractors and vendors. Book a demo to extend Adaptive Security training across your supply chain.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents









