Cybersecurity awareness training gives every employee the skills to recognize and stop social engineering attacks before they escalate into security incidents that cost millions. This guide covers the full range of measurable benefits of cybersecurity awareness training that security leaders need to build the case for investment or program modernization, including:
- How the benefits of cybersecurity awareness training translate into measurable breach cost reduction;
- Which compliance frameworks mandate ongoing security awareness training programs;
- Why continuous cybersecurity awareness training outperforms annual-only programs in reducing phishing susceptibility;
- What behavioral metrics prove program ROI to boards and executive leadership;
- How AI-powered platforms scale the benefits of cybersecurity awareness training across distributed workforces.

According to the Verizon 2025 Data Breach Investigations Report, approximately 60% of confirmed breaches involved a human action, whether through a malicious click, a socially engineered phone call, or the misdelivery of sensitive data. A single prevented incident funds multiple years of training investment at most organizations.
Stop letting untrained employees remain the weakest link; Adaptive Security transforms human risk into measurable defense.
What Is Cybersecurity Awareness Training
Cybersecurity awareness training is a structured program that teaches employees to recognize, avoid, and respond to cyber threats, including phishing, social engineering, vishing, smishing, deepfakes, and business email compromise (BEC). Modern programs combine simulated attacks, microlearning modules, and behavioral reinforcement to build measurable threat resistance rather than theoretical knowledge alone.
Security awareness means knowing threats exist. Security training means building the skill to respond correctly under pressure. Confusing the two produces programs that check compliance boxes without reducing actual risk, which is why understanding the full benefits of cybersecurity awareness training requires distinguishing between passive knowledge and active behavioral change.
What Does Cybersecurity Awareness Training Actually Cover?
The scope of an effective cybersecurity awareness training program extends well beyond email phishing. Cyberattackers now impersonate executives over voice calls, send credential-harvesting SMS messages, and deploy AI-generated deepfake video to authorize fraudulent wire transfers. A program that trains only on email leaves every other attack surface undefended.
An effective cybersecurity awareness training program must cover:
- Phishing and spear phishing recognition;
- Vishing and smishing identification;
- Deepfake social engineering across video and audio channels;
- Business email compromise (BEC) patterns;
- Insider threat recognition and data handling protocols;
- Incident reporting procedures.
Incident reporting is often the most underweighted component. When employees flag suspicious activity immediately, security teams contain threats before damage escalates. Without that reflex, cyberattackers dwell inside networks for days or weeks undetected.
How Continuous Training Delivers Greater Benefits of Cybersecurity Awareness Training Than Annual-Only Programs
Annual compliance cybersecurity awareness training is a snapshot. Cyber threats evolve daily. As per the norm, baseline susceptibility does not improve with a single annual training event.
Organizations running continuous cybersecurity awareness training simulation and reinforcement cycles close behavioral gaps faster because employees build recognition reflexes through repeated, realistic practice. Continuous security awareness training programs also allow risk scoring to update dynamically, routing high-risk employees into targeted modules automatically rather than waiting for the next annual review cycle. The gap between when a threat emerges and when cybersecurity awareness training responds is where most breaches begin, and closing that gap is among the most significant benefits of cybersecurity awareness training.
14 Key Benefits of Cybersecurity Awareness Training
The benefits of cybersecurity awareness training extend far beyond ticking a compliance box. Human behavior remains the most consistently exploited cyber attack surface in enterprise security. Organizations that build structured, continuous programs compress the gap between a new threat emerging and employees being equipped to stop it.
1. Reduces the Risk of Data Breaches
Human behavior drives the majority of data breaches. Cybersecurity awareness training converts that vulnerability into a measurable defense layer by building recognition skills before employees encounter live attacks.
Organizations with structured cybersecurity awareness training programs report lower click rates on phishing simulations year-over-year, directly reducing the probability of a data breach event.
2. Defends Against Phishing and AI-Generated Attacks
Email filters block known malicious domains and recognized malware signatures, but they cannot catch a hyper-personalized spear phishing email crafted by a generative AI model using open-source intelligence (OSINT) scraped from LinkedIn and public filings. According to the IBM Cost of a Data Breach Report 2025, one in six data breaches involved cyberattackers using AI, with 37% of those leveraging AI for phishing specifically.
Trained employees recognize the behavioral cues of manipulation, including urgency, authority, and unsolicited wire requests, regardless of how convincing the sender appears. That recognition layer is the only defense that adapts in real time when the cyber attack vector is human judgment rather than a technical signature.
3. Protects Against Social Engineering Across All Channels
Social engineering does not stop at email. Vishing, smishing, and deepfake video impersonation are now active attack vectors targeting finance teams, executives, and IT staff through phone calls, text messages, and video conferencing platforms.
According to Keepnet's 2025 Phishing Statistics Report, SMS phishing click-through rates range from 19% to 36%, compared with just 2% to 4% for email phishing, making smishing up to nine times more effective. Cybersecurity awareness training programs that simulate attacks across all three channels build the muscle memory employees need to pause, verify, and report suspicious contact regardless of how it arrives.
4. Reduces Human Error
Employees who understand how attacks work make fundamentally different decisions under pressure. Cybersecurity awareness training reframes every credential request, invoice approval, and software download as a moment requiring verification rather than automatic compliance.
Organizations that treat employees as a trainable asset build a workforce that catches what technical controls miss. This reduction in human error is one of the foundational benefits of cybersecurity awareness training across every industry.
5. Builds a Security-Focused Culture and Human Firewall
Compliance-driven cybersecurity awareness training produces completion logs rather than behavioral change. The gap between the two is where breaches happen. When security awareness becomes an organizational reflex, embedded in onboarding, reinforced through role-specific scenarios, and normalized through regular simulation, employees stop treating security as IT's problem and start treating it as their own.
Carnegie Mellon's CyLab Security and Privacy Institute's Protecting People from Phishing: The Design and Evaluation of an Embedded Training Email System consistently shows that organizations embedding security behaviors into daily workflows reduce susceptibility faster than those relying on annual training events alone. The cultural shift is among the most durable benefits of cybersecurity awareness training because it persists beyond any single training window.
6. Supports Regulatory Compliance
SOC 2, HIPAA, GDPR, PCI-DSS, ISO 27001, NIST CSF, and CMMC all require documented evidence of employee security training, and regulators increasingly audit for ongoing program continuity rather than annual completion records alone.
Cybersecurity awareness training content mapped to these frameworks provides the audit trail compliance officers need to demonstrate due diligence. An undocumented or lapsed program exposes organizations to regulatory penalties that routinely exceed the cost of training itself, making compliance alignment one of the most practical benefits of cybersecurity awareness training.
Compliance gaps widen every quarter an organization waits; Adaptive Security maps training directly to SOC 2, HIPAA, PCI-DSS, and ISO 27001 requirements.
7. Reduces Breach Costs and Potential Cyber Insurance Premiums
According to the IBM Cost of a Data Breach Report 2025, the global average breach cost is $4.44 million, with U.S. organizations facing a record $10.22 million average. Cyber insurers have taken note, and carriers increasingly require evidence of active, ongoing security awareness training as a condition of coverage or as the basis for premium discounts.
Organizations that provide documented cybersecurity awareness training data, phishing simulation results, and measurable improvement in human risk scores present a lower claims profile. While premium reductions vary by insurer and policy structure, documented cybersecurity awareness training programs strengthen the overall security posture that underwriters evaluate when setting rates and coverage terms.
8. Delivers Measurable ROI
At the average global breach cost documented by the IBM report, a single prevented incident funds years of cybersecurity awareness training investment across most organizational budgets. The ROI calculation converts directly into avoided incident response costs, legal fees, regulatory fines, and customer notification expenses.
Cybersecurity awareness training programs that track simulation click rates, risk score changes, and reporting rates over time give security leaders the data to quantify that return to finance teams and boards. Measurable ROI remains one of the most compelling benefits of cybersecurity awareness training when building the investment case.
9. Strengthens Incident Response
Trained employees report suspicious emails, calls, and messages faster, and faster reporting compresses dwell time, the window between initial compromise and detection during which cyberattackers escalate access and stage data exfiltration. According to the IBM Cost of a Data Breach Report 2025, organizations identified and contained breaches within a mean time of 241 days, the lowest figure in nine years.
Every hour shaved from dwell time limits the blast radius of a data breach across network segments, cloud environments, and third-party integrations. Phishing simulations that reward reporting behavior accelerate this response reflex across the entire organization.
10. Reduces Insider Threat Risk
Insider threats fall into two categories: malicious actors deliberately exfiltrating data, and well-meaning employees who expose sensitive information through shadow IT, misconfigured file sharing, or password reuse. According to the IBM Cost of a Data Breach Report 2025, shadow AI was a factor in 20% of breaches, adding $670,000 to average costs.
Cybersecurity awareness training that covers acceptable use policies, data handling procedures, and the specific risks of AI tools and unauthorized SaaS applications closes the unintentional exposure category. Employees who understand why these behaviors create risk change them permanently rather than only while the policy poster is visible.
11. Protects Company Reputation and Builds Customer Trust
A publicized breach does not just trigger regulatory scrutiny; it fractures customer confidence in ways that persist long after technical remediation is complete. Organizations that demonstrate a mature, proactive security posture signal to clients, partners, and regulators that they take data protection seriously before an incident rather than in response to one.
Training is the most visible, documentable expression of that posture. Reputation protection is one of the benefits of cybersecurity awareness training that compounds over time as organizations build demonstrable track records of security investment.
12. Supports Remote and Hybrid Workforce Security
Distributed employees introduce attack surfaces that technical controls cannot fully close: unsecured home Wi-Fi networks, personal devices used for work email, and mobile device misuse under reduced IT visibility.
Cybersecurity awareness training bridges that gap by building the individual decision-making skills employees carry regardless of where they work. A remote employee who recognizes a vishing call or a suspicious SMS lure does not need a firewall to stop the attack; the pattern recognition that training builds is the defense.
13. Provides Competitive Advantage and Builds Customer Confidence
Enterprise procurement cycles increasingly include vendor security questionnaires that ask specifically about employee cybersecurity awareness training programs, simulation frequency, and compliance documentation. Organizations with documented, ongoing cybersecurity awareness training programs answer those questions with evidence, reducing friction in sales cycles and satisfying due diligence requirements.
A structured cybersecurity awareness training program is no longer a security investment only. It is a trust signal in competitive deal flow, making competitive differentiation one of the strategic benefits of cybersecurity awareness training.
14. Scales Behavioral Change With Continuous, Adaptive Learning
Annual training updates cannot keep pace with cyberattackers who refresh attack techniques in days rather than months. AI-powered training platforms personalize content to each employee's role, prior simulation results, and behavioral risk signals, automatically enrolling high-risk individuals in targeted modules when their behavior warrants it.
According to Gartner's Top Trends in Cybersecurity 2025, enterprises combining GenAI with integrated security behavior and culture programs will experience 40% fewer employee-driven cybersecurity incidents by 2026. This architecture compresses the gap between a new attack variant emerging and the workforce being trained to recognize it, replacing the static annual cybersecurity awareness training cycle with a continuously updating defense layer.
Every day without adaptive training is a day cyberattackers have the upper hand; Adaptive Security closes the gap between emerging threats and employee readiness.
How to Measure the Effectiveness of Cybersecurity Awareness Training Programs
Measuring the effectiveness of cybersecurity awareness training requires tracking behavioral signals rather than administrative outputs alone. Security leaders should establish baseline phishing simulation click rates, track report rates and mean time to report over successive simulation cycles, monitor human risk scores by department and role, and connect training outcomes to confirmed reductions in security incidents caused by human error.
Completion logs show participation. Only behavioral metrics prove that employees have changed how they respond to real threats. Annual cybersecurity awareness training cycles are structurally insufficient to keep pace with AI-driven threat evolution, which is why continuous or quarterly programs are now the operational standard for realizing the full benefits of cybersecurity awareness training.
1. Separate Behavioral Metrics From Vanity Metrics
Completion rates are the most commonly reported cybersecurity awareness training metric and the least meaningful one. A 95% completion rate tells a CISO that employees clicked through modules; it says nothing about whether those employees can identify a spear phishing email or report a vishing attempt.
Behavioral indicators in cybersecurity awareness training tell a materially different story:
- Phishing simulation click rates trending down over successive quarters;
- Report rates trending up;
- Mean time to report shrinking from days to hours.
The metrics that reflect program health are repeat clickers and human risk score movement by department and role. Repeat clickers are employees who fail multiple cybersecurity awareness training simulation rounds across different channels, and they identify the highest-concentration risk pockets before cyberattackers find them. Risk score trends tracked at the team level surface structural gaps that completion logs will never expose.
2. Track Cybersecurity Awareness Training Simulation and Reporting Rates Over Time
Phishing click rates measured at a single point in time produce a snapshot; tracked across quarterly simulation cycles, they produce a trend. A finance team with a 28% click rate in Q1 that drops to 11% by Q3 represents a measurable, defensible outcome. Pair that with an increase in the phish report rate and the data supports both budget justification and board-level reporting.
According to the Verizon 2025 Data Breach Investigations Report, 20% of users reported phishing in simulation engagements, and 11% of those who clicked the email also reported it. Mean time to report is an underused metric with direct operational value: when employees report suspicious emails faster, security teams contain threats earlier.
Human risk scoring dashboards that aggregate simulation behavior, cybersecurity awareness training completion, and OSINT exposure signals into a unified score by role and department give security leaders the real-time visibility that static reporting cannot provide.
Vanity metrics disguise risk; Adaptive Security's human risk scoring dashboards expose the behavioral signals that actually predict breaches.
3. Replace Annual Cybersecurity Awareness Training Cycles With Continuous or Quarterly Cadences
Annual cybersecurity awareness training was designed for a threat environment that no longer exists. AI has compressed attacker development cycles from weeks to hours, and the tactics in last year's phishing module are already outdated by the time employees complete it.
Quarterly cybersecurity awareness training simulation rotations, cycling through email spear phishing, vishing, smishing, and deepfake video scenarios, ensure that employees encounter novel attack formats regularly. A continuous cadence also enables microlearning at the moment of failure: when an employee clicks a simulation, they receive a short, targeted cybersecurity awareness training module immediately, reinforcing the lesson while the experience is fresh.
According to a Gartner survey cited in its Top Cybersecurity Trends for 2026 report, over 57% of employees use personal GenAI accounts for work purposes and 33% admit inputting sensitive information into unapproved tools. These rapidly shifting behaviors require training programs that adapt in near-real time rather than annually.
How the Benefits of Cybersecurity Awareness Training Differ for Technical vs. Non-Technical Employees
One-size-fits-all cybersecurity awareness training underserves both audiences it claims to address. Non-technical employees in finance, HR, operations, and the executive suite face the highest concentration of social engineering risk, yet most generic modules bury them in protocol memorization they will never use. Technical employees disengage from basic phishing awareness they already understand, missing the adversary-behavior context that makes them genuinely harder to compromise.
Role-based cybersecurity awareness training closes that gap by matching content to the actual threat profile of each job function. The result is measurably lower susceptibility across the organization.
Why Do Non-Technical Employees Need Different Training to Realize the Benefits of Cybersecurity Awareness Training?
Finance approvers, HR administrators, and executives are the primary targets of business email compromise (BEC), voice impersonation, and invoice fraud. According to the FBI 2024 Internet Crime Report, BEC losses totaled $2.77 billion across 21,442 reported incidents, with nearly $8.5 billion in cumulative BEC losses reported between 2022 and 2024. These cyberattacks exploit authority and urgency rather than technical knowledge gaps.
Training this audience in network protocols or malware architecture misses the point entirely. What they need are scenario-based cybersecurity awareness training exercises that replicate the exact manipulation tactics cyberattackers use against their role: a spoofed CFO voice request, a fabricated vendor invoice, a deepfake video approval.
The HIPAA Security Rule maintained by HHS requires covered entities to train all workforce members on security policies and procedures, with cybersecurity awareness training tailored to each employee's role. That compliance mandate exists precisely because role-specific cyber threat risk varies dramatically across a healthcare organization.
What Should Technical Employees Learn Beyond Standard Cybersecurity Awareness Training?
Developers, IT administrators, and security analysts already recognize phishing emails. They need training that reflects how cyberattackers use social engineering to bypass the technical controls those employees build and manage.
The cybersecurity awareness training skills that reduce risk at the technical layer include:
- Secure coding awareness and vulnerability identification;
- Credential hygiene under targeted vishing pressure;
- Understanding how OSINT enables adversary reconnaissance;
- Recognizing how cyberattackers pivot from a stolen credential to cloud environment compromise.
A developer who understands how an attacker pivots from a stolen GitHub credential to a cloud environment is a fundamentally stronger line of defense than one who can only identify a typosquatted email domain.
How Does Role-Based Training Improve the Benefits of Cybersecurity Awareness Training Over Generic Programs?
Role-based cybersecurity awareness training produces better retention because the content is directly relevant to the decisions each employee makes every day. When a security awareness training module mirrors the exact scenario a finance analyst or a system administrator actually encounters, the behavioral transfer from training to real-world decision-making is faster and more durable.
Vertical-specific compliance content reinforces this further. Finance teams completing PCI-DSS-mapped modules connect training directly to the consequences they are regulated on, while healthcare employees completing HIPAA-mapped scenarios understand that the compliance requirement is tied to genuine patient harm risk. That context is what converts a cybersecurity awareness training completion into a behavioral change, and behavioral change is what actually reduces breach exposure.
Generic training modules leave role-specific risk blind spots wide open; Adaptive Security tailors simulations to each employee's actual threat profile.
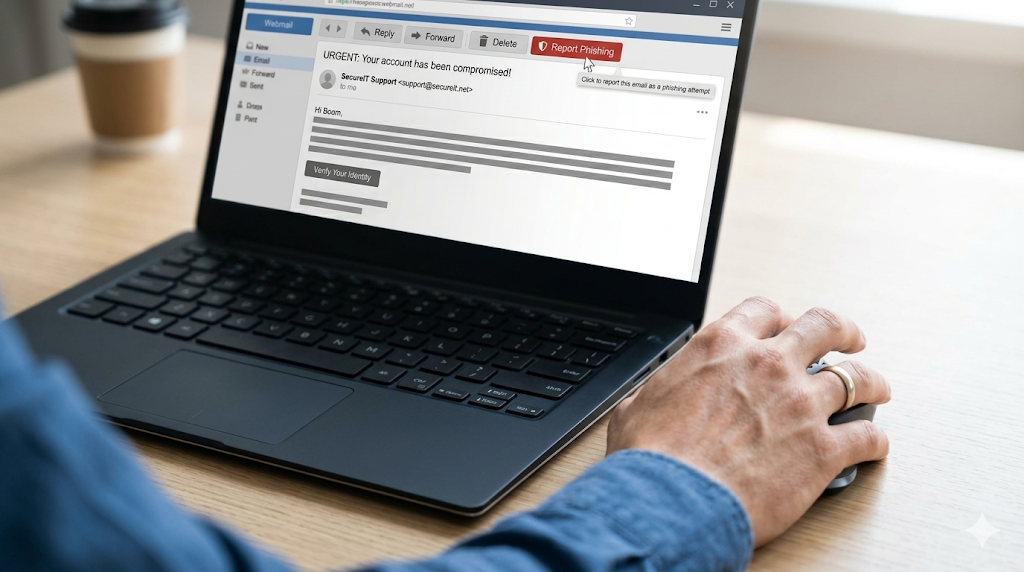
How Simulated Phishing Tests Strengthen the Benefits of Security Awareness Training

The benefits of security awareness training multiply when simulation and training operate as a feedback loop. Simulations surface real behavioral vulnerabilities that self-reported awareness surveys never reveal. An employee can correctly answer a quiz about phishing while still clicking a convincing spear phishing link minutes later. Training without simulation identifies knowledge gaps; simulation without cybersecurity awareness training leaves those gaps open.
Why Self-Reported Awareness Falls Short of Measuring the Benefits of Cybersecurity Awareness Training
Surveys and completion logs measure what employees say they know. Simulations measure what employees actually do under realistic pressure. These two data points routinely diverge, and the gap between them is where breaches happen.
OSINT, the practice of gathering publicly available data from LinkedIn profiles, press releases, and conference bios, allows both real cyberattackers and simulation platforms to craft personalized attacks that generic awareness surveys cannot anticipate. When a simulation uses an employee's actual job title, manager name, and a vendor they work with, the psychological pressure is orders of magnitude higher than a template email, and the behavioral data captured is far more accurate.
What Modern Simulation Programs Cover to Maximize the Benefits of Cybersecurity Awareness Training
Legacy cybersecurity awareness training simulation platforms test email. Modern cyberattackers do not limit themselves to email. A current simulation program must replicate:
- Vishing through AI-cloned executive voice calls;
- Smishing via SMS-based lures;
- Deepfake video impersonation.

That exact combination led Arup's Hong Kong finance employee to approve a $25 million wire transfer in 2024 after joining a video call where every participant, including the CFO, was a deepfake. That attack succeeded precisely because the employee had never experienced a multi-channel deepfake scenario in a controlled environment. Organizations that limit phishing simulations to email are training for a threat model that cyberattackers abandoned years ago.
Email-only simulations ignore the channels where cyberattackers are already winning; Adaptive Security replicates vishing, smishing, and deepfake attacks in controlled environments.
How Microlearning After a Failed Simulation Locks in the Benefits of Cybersecurity Awareness Training
Timing determines whether a failed simulation becomes a lasting cybersecurity awareness training lesson or a forgotten event. Microlearning delivered immediately after a failed cybersecurity awareness training simulation catches employees at peak receptivity, the moment when a realistic cyberattack has just demonstrated exactly where their judgment broke down.
According to a 2025 cluster randomized field study published in Data: Journal of Information Systems and Management, structured cybersecurity awareness training with embedded microlearning and periodic phishing simulations doubled employee reporting rates and reduced failure rates from 11.2% to 7.5%. That just-in-time intervention replaces abstract policy recitation with a concrete, personal example, which is why it consistently outperforms scheduled cybersecurity awareness training alone in driving long-term behavior change.
Why Leadership Buy-In Determines the Success of Cybersecurity Awareness Training Programs
Security awareness programs without visible executive sponsorship consistently produce lower completion rates, weaker behavioral outcomes, and a culture where employees treat training as optional overhead. According to the World Economic Forum's Global Cybersecurity Outlook 2025, 72% of respondents reported a rise in cyber risks, and organizations with board-level engagement in cybersecurity demonstrated meaningfully higher resilience across every comparable measure.
When executives do not visibly participate, cybersecurity awareness training reads as compliance theater. When they do, it reads as a business imperative.
What Happens When Executives Fail to Champion the Benefits of Cybersecurity Awareness Training?
Employees take cues from leadership. A CISO who mandates cybersecurity awareness training while the executive team skips simulations sends a clear message: this applies to the workforce rather than leadership. The result is predictable, with lower voluntary completion, higher simulation failure rates, and a reporting culture where employees stay silent about near-misses.
According to the World Economic Forum's Global Cybersecurity Outlook 2025, 42% of organizations experienced a successful social engineering attack in the past year, a number expected to increase with advances in the malicious adoption of AI. Without executive ownership, cybersecurity awareness training programs lose the organizational authority that drives behavioral change.
Why C-Suite Leaders Are Themselves High-Value Targets for Social Engineering
Executives are not just program sponsors. They are prime attack targets. Business email compromise schemes, deepfake video calls impersonating the CFO, and vishing attacks using AI-cloned executive voices all exploit the authority that comes with seniority.
According to the World Economic Forum's Global Cybersecurity Outlook 2025, 55% of CISOs polled stated that deepfakes pose a moderate-to-significant cyber threat to their organization. Executives participating in phishing simulations and deepfake scenario training accomplishes two objectives simultaneously: it models the behavior expected of every employee, and it reduces the actual attack surface created by leadership's own public exposure.
How Board-Ready Reporting Sustains the Investment Case for the Benefits of Cybersecurity Awareness Training
The most common reason cybersecurity awareness training programs lose funding is the same reason they struggle to earn it: security leaders present completion percentages to executives who measure outcomes in dollars and risk exposure. Human risk scores, department-level simulation trends, and phishing susceptibility rates translate training activity into the business language boards understand.
When the data shows that a finance team's simulated click rate dropped from 28% to 6% over two quarters, that is a concrete breach probability figure rather than a training metric. That framing is what moves cybersecurity awareness training from a line item to a protected investment, directly connecting the benefits of cybersecurity awareness training to the executive decision-making cycle.
Board presentations built on completion rates fail to protect budgets; Adaptive Security turns behavioral data into the risk language executives act on.
How Cybersecurity Awareness Training Fits Into a Human Risk Management Strategy
Cybersecurity awareness training extends well beyond completed modules and passing quiz scores. It feeds directly into a broader human risk management (HRM) framework that treats employee behavior as a continuous, measurable security signal. Calendar-based programs generate a static snapshot of awareness, while HRM programs require a dynamic, signal-driven picture of where human risk is concentrated at any given moment.
What Does Human Risk Management Actually Measure in Cybersecurity Awareness Training?

Human risk management aggregates data from multiple behavioral sources to produce a dynamic risk score for each employee. The inputs include:
- Simulation behavior: Whether an employee clicked a phishing link, submitted credentials, or reported a suspicious message;
- Cybersecurity awareness training completion: Module engagement and assessment results;
- Reported incidents: Active threat-detection instincts demonstrated through reporting;
- OSINT monitoring: Continuous scanning of publicly available employee data that cyberattackers use to personalize attacks.
These inputs combine to answer a question that completion logs alone cannot: which employees, in which roles, are most likely to be successfully targeted next? A finance employee who completed annual training but has a public LinkedIn profile listing internal systems and recently changed job titles is measurably more exposed than their completion record suggests.
How Cybersecurity Awareness Training Shifts From a Calendar Event to a Risk Intervention
In an HRM framework, training is triggered by risk signals rather than scheduled by the calendar. When an employee clicks a simulated phishing email, that behavior elevates their risk score and automatically enrolls them in a targeted microlearning module calibrated to the specific attack type they failed.
According to the IBM Cost of a Data Breach Report 2025, organizations using security AI and automation extensively cut their breach lifecycle by 80 days and saved nearly $1.9 million on average. The same principle applies to closing human-layer gaps through automated, signal-triggered training.
Human risk management reframes cybersecurity awareness training from a compliance checklist line item into a continuous feedback loop where training outcomes become the evidence that risk is declining. When that evidence is missing, it signals that an intervention is needed before a cyberattacker gets there first.
Risk signals that trigger instant remediation outperform quarterly reviews every time; Adaptive Security automates the intervention loop.
Frequently Asked Questions About the Benefits of Cybersecurity Awareness Training
How often should cybersecurity awareness training be conducted?
Cybersecurity awareness training should be conducted on a continuous or monthly basis. Annual-only programs fail because the threat landscape evolves faster than a 12-month training cycle can track. CISA guidance on employee cybersecurity education reinforces that ongoing awareness is a foundational security practice. Organizations running continuous training programs see sustained reductions in phishing click rates, while annual-only cohorts typically revert to baseline susceptibility within 60 to 90 days.
Does cybersecurity awareness training reduce cyber insurance premiums?
Yes. Most cyber insurers now require documented evidence of an active security awareness training program as a condition of coverage or as a factor in premium pricing. Organizations that demonstrate continuous training, phishing simulation results, and measurable improvement in human risk scores present a lower claims profile, strengthening the overall security posture that underwriters evaluate.
What compliance frameworks require cybersecurity awareness training?
Multiple major compliance frameworks explicitly require or strongly mandate cybersecurity awareness training:
- SOC 2 (CC9.2) requires security awareness education as part of its Common Criteria;
- HIPAA's Security Rule mandates workforce training on security policies and procedures;
- PCI-DSS Requirement 12.6 requires a formal security awareness program for all personnel;
- ISO 27001 (Annex A.7.2.2) requires awareness, education, and training;
- NIST CSF and CMMC 2.0 both embed awareness training as a core control;
- GDPR expects organizations to train staff handling personal data.
How do organizations prove the ROI of cybersecurity awareness training to a board?
The strongest ROI argument centers on breach cost avoidance. With global average breach costs in the millions and U.S. averages exceeding $10 million, a single prevented incident justifies years of program investment. Present the board with behavioral metrics: phishing simulation click rate trends, mean time to report suspicious emails, and repeat offender rates by department. These figures translate human risk into financial exposure, and a declining click rate is a quantifiable reduction in the organization's attack surface.
What is the difference between security awareness and security training?
Security awareness is the knowledge that cyber threats exist. Security training builds the behavioral skills to recognize and respond to those threats correctly. Awareness alone does not change behavior. Effective programs combine both: awareness content establishes context and motivation, while skills-based training, including simulated phishing, vishing, and smishing exercises, builds the conditioned reflexes that hold under pressure.
How does simulated phishing testing differ from cybersecurity awareness training?
Simulated phishing testing is a diagnostic tool. Cybersecurity awareness training is the intervention. Simulations expose real behavioral vulnerabilities by mimicking the tactics cyberattackers actually use, including spear phishing, BEC lures, vishing calls, smishing texts, and deepfake video impersonation. Training closes those gaps with targeted content, and the most effective programs couple the two through just-in-time microlearning.
What topics should a cybersecurity awareness training program cover in 2026?
A 2026 program must cover:
- Phishing and spear phishing recognition;
- Vishing and smishing identification;
- Deepfake video and audio impersonation;
- Business email compromise (BEC) patterns;
- Password hygiene and multi-factor authentication;
- Safe remote work practices;
- Data handling and classification;
- OSINT exposure risks;
- Ransomware triggers;
- Incident reporting procedures;
- Shadow IT risks and the proper handling of sensitive data on personal devices.
How does cybersecurity awareness training help with remote and hybrid workforces?
Remote and hybrid employees introduce attack surfaces that technical controls cannot fully reach. Unsecured home networks, personal devices, and informal communication channels expand the organization's exposure. Cybersecurity awareness training closes the behavioral gap that endpoint protection and email filters leave open, equipping distributed employees to recognize social engineering attempts across SMS, personal email, collaboration tools, and phone calls.
Distributed teams multiply attack surfaces that firewalls cannot reach; Adaptive Security equips every remote employee with the recognition skills that travel with them.
What happens to organizations that do not invest in cybersecurity awareness training?
Organizations without active cybersecurity awareness training face higher breach probability, higher breach costs, and growing compliance exposure. According to the FBI 2024 Internet Crime Report, total reported cybercrime losses reached $16.6 billion, a 33% increase from 2023. Without training, employees remain the path of least resistance for cyberattackers, and untrained workforces are more likely to click phishing links, comply with fraudulent wire transfer requests, and mishandle sensitive data.
How does AI-powered security awareness training improve outcomes compared to legacy platforms?
AI-powered security awareness training produces measurably better outcomes by personalizing content, timing, and simulation difficulty to each employee's role, behavior, and prior performance. Legacy platforms deliver the same module to every employee on a fixed schedule regardless of individual risk profile.
AI-native platforms continuously update simulation content to reflect current attack patterns, including AI-generated phishing emails, deepfake voice calls, and OSINT-personalized lures. The result is a training program that tightens the gap between when a new threat emerges and when employees are equipped to recognize it.
See How Adaptive Security Measurably Reduces Human Risk Across an Entire Organization
Human-layer threats account for the majority of breaches, and the gap between emerging attack tactics and employee readiness is where organizations are most exposed. Adaptive Security's AI-native platform continuously adapts simulations, training content, and risk scoring to each employee's actual behavior, closing that gap in real time rather than waiting for the next scheduled training cycle.
The platform delivers the full spectrum of benefits of cybersecurity awareness training through:
- Multi-channel simulations that replicate phishing, vishing, smishing, and deepfake attacks using AI-generated content tailored to each employee's role and organizational context;
- Human risk scoring dashboards that aggregate simulation behavior, training completion, and OSINT exposure signals into a unified, department-level view security leaders can present to boards;
- Automated microlearning triggered at the moment of failure, delivering targeted remediation content while the experience is fresh rather than scheduling intervention weeks later.
Organizations using Adaptive Security replace the static annual training cycle with a continuously updating defense layer that compresses the gap between a new attack variant emerging and the workforce being trained to recognize it.
The difference between a prevented breach and a multimillion-dollar loss starts with a single platform decision; Adaptive Security makes that decision measurable.
Key Takeaways
- The benefits of cybersecurity awareness training extend across breach prevention, regulatory compliance, incident response acceleration, and measurable ROI that security leaders can present to boards.
- Continuous cybersecurity awareness training programs that operate on monthly or quarterly cadences consistently outperform annual-only programs in reducing employee susceptibility to phishing, vishing, and social engineering attacks.
- Role-based cybersecurity awareness training matched to each employee's actual threat profile produces faster behavioral transfer and more durable risk reduction than generic, one-size-fits-all modules.
- The benefits of cybersecurity awareness training multiply when simulation and training operate as a feedback loop, with microlearning delivered at the moment of failure to lock in behavioral change.
- Leadership buy-in directly determines whether cybersecurity awareness training programs produce cultural change or compliance theater; executive participation models the behavior expected of every employee.
- Human risk management frameworks transform cybersecurity awareness training from a calendar event into a continuous, signal-driven intervention that identifies and remediates the highest-risk employees before cyberattackers reach them.
- AI-powered platforms represent the next evolution of the benefits of cybersecurity awareness training, personalizing content and simulation difficulty to each employee's role, behavior, and prior performance in real time.
The benefits of cybersecurity awareness training are only realized through platforms that adapt as fast as the threats do; Adaptive Security is built for exactly that challenge.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents








.png)
.png)