Cybersecurity awareness training program trends have moved sharply away from annual compliance modules toward continuous, behaviorally grounded systems that measure whether employees make safer decisions under real cyberattack conditions. According to Verizon's 2025 Data Breach Investigations Report, 60% of confirmed breaches involve the human element, and phishing remains the number one initial access vector. This is a fundamentally architectural shift in cybersecurity awareness training programs, and organizations that have not made the transition face measurably higher breach probability than those that have.

Most organizations are still trying to fix a human problem with tools designed for a different era. According to IBM's Cost of a Data Breach Report 2025, the average breach cost reached $4.44 million, a figure that partly reflects how long behavioral risk goes undetected inside organizations still running awareness-only programs. The most expensive failure point in enterprise security is not a technical one.
By the end of this guide, readers will have a clear framework for:
- Evaluating an existing cybersecurity awareness training program and identifying its structural gaps;
- Building a cybersecurity awareness training program that produces measurable reductions in human-layer risk;
- Mapping a cybersecurity awareness training program to compliance frameworks across healthcare, financial services, and government;
- Aligning a cybersecurity awareness training program with the cybersecurity awareness training program trends shaping AI-era threat defense;
- Translating cybersecurity awareness training program outcomes into board-ready ROI metrics.
Stop measuring training completion and start measuring whether employees actually resist cyberattacks with Adaptive Security.
What a Cybersecurity Awareness Training Program Is, and What It Has Become
A cybersecurity awareness training program is a structured organizational initiative designed to reduce human-layer risk by teaching employees to recognize, avoid, and report social engineering cyberattacks, phishing attempts, and cyber threats before they cause damage. These programs combine phishing simulations, role-based training modules, microlearning, human risk scoring, and compliance mapping into a continuous defense layer that technology controls cannot replicate.
The category has split into two architecturally distinct models that share a name but produce different outcomes. Legacy cybersecurity awareness training programs are built around an annual training event, a static content library, and pass/fail quizzes. Modern cybersecurity awareness training programs are built around continuous simulation, behavioral telemetry, and dynamic content delivery.
The fork happened because static cybersecurity awareness training programs cannot teach an employee to recognize a cyberattack vector that did not exist when the content was written, and the velocity of AI-generated threats now exceeds annual content cycles by several orders of magnitude.
What a Complete Cybersecurity Awareness Training Program Includes Today
Modern cybersecurity awareness training programs operate across five interconnected components:
- Realistic phishing simulations across email, voice, SMS, and deepfake video channels;
- Role-specific training modules that match threat scenarios to job function;
- Microlearning that triggers automatically when an employee fails a simulation;
- Human risk scoring that measures individual susceptibility over time;
- Compliance mapping to frameworks including SOC 2, HIPAA, GDPR, and PCI-DSS.
Each component feeds the others. A failed simulation surfaces a training gap, completed training shifts the risk score, and updated scores inform the next simulation cycle.
Why Cybersecurity Awareness Training Program Design Matters as Much as Content
The threat data does not represent a content problem. It represents a program design problem. Annual training with generic scenarios builds awareness of threats employees rarely encounter in their specific roles, while leaving the actual cyberattack paths that target finance teams, IT administrators, and executives virtually unpracticed.
According to CrowdStrike 2025 Global Threat Report, AI-generated phishing emails land a 54% success rate against human targets, roughly 4.5 times the rate of human-written phishing.
That gap is where breaches happen, and closing it depends on how the security awareness training program is architected rather than how many hours of generic content it pushes per year.
Replace checkbox compliance with measurable behavior change through Adaptive Security.
The Industry Shift: From Compliance Theater to Measurable Behavior Change
Cybersecurity awareness training program trends have converged on a single uncomfortable truth: near-perfect completion rates do not protect organizations. A program where 98% of employees finish a 30-minute module and then forget most of it within a week produces an audit-ready report that overstates actual security posture.
Compliance metrics and human risk metrics are not the same number. Treating them as equivalent is how organizations get breached.
Why Annual Cybersecurity Awareness Training Programs Fail to Change Behavior
The mechanism of failure is well-established in cognitive science. Hermann Ebbinghaus demonstrated in 1885 that memory decays exponentially without reinforcement, a pattern now known as the Ebbinghaus Forgetting Curve.
People forget information fastest in the hours immediately after learning, with the rate slowing over time only if the knowledge is reactivated. Annual training cycles are structurally incompatible with this reality; employees complete a module in January and receive no reinforcement until the following January, by which point the information has long since degraded.
The problem compounds when training relies on fear. According to Tafet and Ortiz Alonso's research on learned helplessness and learned controllability, threat-heavy messaging triggers denial, learned helplessness, and avoidance rather than vigilance. Training that shames employees after a failed phishing simulation accelerates this disengagement.
What Behavioral Science Says Actually Works in Cybersecurity Awareness Training Programs
Effective cybersecurity awareness training program design applies four components simultaneously:
- Motivation: framing employees as skilled defenders rather than potential liabilities;
- Ability: providing specific, actionable skills rather than abstract warnings;
- Triggers: delivering training at the exact moment of relevance, such as immediately after a failed simulation;
- Reinforcement: repeating and varying exposures so knowledge survives the forgetting curve.
Nudge theory and positive reinforcement consistently outperform punitive approaches in sustained behavior change. When an employee fails a phishing simulation, the constructive response is an immediate, brief teachable moment. Not a public flag or a mandatory hour-long remediation course.
These behavioral principles are now operationalized through specific delivery mechanisms: microlearning modules under 10 minutes, just-in-time training triggered by real-world behavior, and gamification that builds consistent engagement without coercion. That shift is where the measurable gap between legacy and modern cybersecurity awareness training programs becomes visible in the risk data.
Train employees the way behavioral science actually works using Adaptive Security.
How AI-Powered and Multi-Channel Threats Are Reshaping Cybersecurity Awareness Training Program Trends
Cybersecurity awareness training program trends now require a fundamental rethinking of what threat simulation means. The cyberattack surface has moved far beyond email inboxes.
Generative AI has compressed the time required to build a convincing spear phishing campaign from weeks to hours. Adversaries craft hyper-personalized messages using open-source intelligence (OSINT), publicly available data scraped from LinkedIn profiles, company websites, and conference recordings. Annual training content cycles cannot close a gap that grows daily.
Why the Deepfake Threat Is So Hard to Train Against
According to Sumsub's 2024 Identity Fraud Report, deepfake fraud incidents grew 10 times year-over-year between 2022 and 2023, a rate of expansion that rendered static awareness content obsolete almost the moment it was published. According to CrowdStrike 2025 Global Threat Report, vishing cyberattacks then surged 442% between the first and second halves of 2024, confirming the channel had moved from edge case to mainstream.
The $25 million wire fraud targeting engineering firm Arup in Hong Kong, where a finance employee was deceived by a video call in which every visible participant was AI-generated, illustrated the specific cognitive gap cybersecurity awareness training programs must close. Employees have no visceral reference point for how convincing these cyberattacks feel until they experience one.
That gap is precisely what legacy platforms, built for 2010s email threats, were never designed to address.
How AI Has Changed the Spear Phishing Cyberattack Surface
Generative AI enables cyberattackers to build personalized spear phishing messages at industrial scale using an employee's role, reporting relationships, travel history, and social connections scraped from public sources.
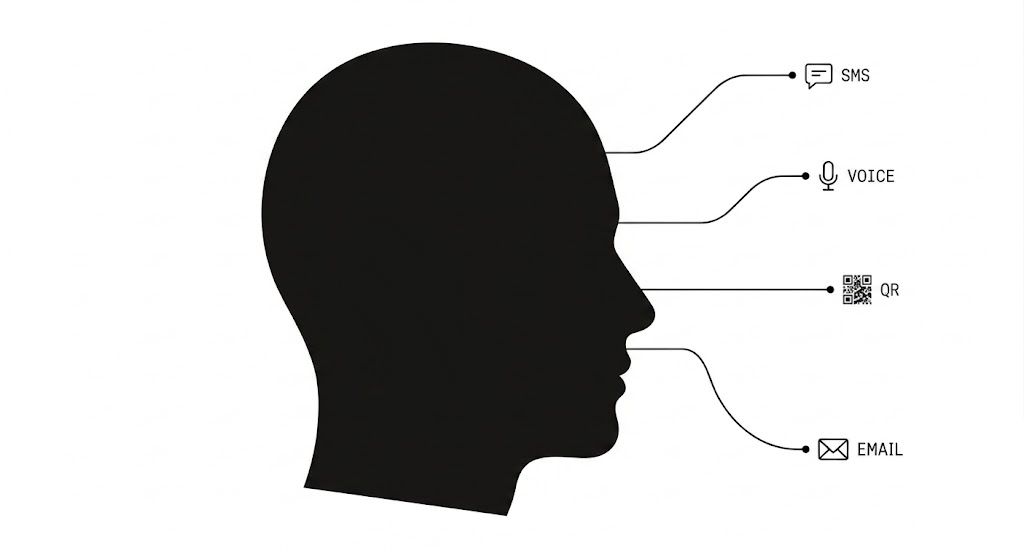
That same OSINT data enables cyberattackers to reach employees across multiple channels:
- Vishing cyberattacks delivered through AI-cloned executive voices;
- Smishing campaigns via SMS;
- Quishing cyberattacks embedded in QR codes;
- Social engineering attempts pushed through Microsoft Teams or Slack.
Most phishing simulations never test these channels. Each channel exploits different behavioral instincts, which means training that covers only email leaves employees unequipped for the cyberattacks most likely to succeed against them today.
Why Legacy SAT Platforms Fail Against These Vectors
Legacy platforms were built to simulate one channel, email, and measure one metric: click rate. They produce completion logs without driving behavioral change, and their content libraries update on quarterly or annual cycles while adversary tooling evolves in hours.
A training program that measures whether employees watched a video about phishing cannot tell whether those same employees would detect a deepfake video call or recognize a vishing attempt from a cloned CFO voice. That gap between what training covers and what cyberattackers actually deploy is where breaches happen, and it demands a fundamentally different program architecture to close.
Test employees against the AI-era cyberattacks they will actually face with Adaptive Security.
What a Modern Cybersecurity Awareness Training Program Must Include
A current-generation cybersecurity awareness training program addresses seven distinct capabilities rather than a single annual module. Build the program by layering multi-channel simulation, personalized training, behavioral analytics, compliance mapping, and a closed-loop reporting mechanism.
Each component connects to a measurable output: a reduced phishing click rate, a lower human risk score, or an auditable compliance record. Weak programs treat any one component as the whole program; effective programs treat all seven as non-negotiable.
1. Deploy Multi-Channel Phishing Simulations
Email-only phishing tests covered the threat landscape of 2015. According to Entrust 2025 Identity Fraud Report, a deepfake attempt occurred every five minutes in 2024, confirming that cyberattackers now reach employees through voice, SMS, and deepfake video as frequently as email.
A complete phishing simulation program tests all four channels and rotates scenarios quarterly. This approach builds recognition reflexes across every surface a cyberattacker uses.
2. Personalize Training by Role and Demonstrated Risk
Role-based curricula map content to an employee's job function, OSINT exposure, and specific behaviors flagged in simulation results. The mechanism matters: a finance analyst who clicked a vendor impersonation email gets targeted business email compromise (BEC) training within the same risk window, with content shaped by which OSINT data point made the lure convincing.
This personalization closes the gap between what an employee was trained on and the cyberattacks most likely to reach them.
3. Apply Microlearning with Spaced Repetition
Modules under 10 minutes, delivered at high frequency, align with established learning science. Hermann Ebbinghaus's Forgetting Curve research demonstrates that people forget roughly 70% of new information within 24 hours without structured reinforcement.
Spaced repetition rebuilds the memory trace before it degrades completely, and short, frequent modules eliminate the completion fatigue that kills engagement in traditional annual cybersecurity awareness training program cycles.
4. Trigger Just-in-Time Training at Contextual Moments
The highest-impact moment to deliver a security lesson is immediately after a risky behavior rather than three months before it. Automated just-in-time training fires when an employee fails a simulation, resets a password, or opens an unexpected external email.
Contextual timing connects the lesson directly to the risk behavior, producing faster and more durable behavioral correction than scheduled training alone.
5. Score Behavioral Risk Continuously
Static completion logs tell leaders who finished a module rather than who will click the next cyberattack. Dynamic risk scoring ingests simulation behavior, training completion rates, OSINT exposure data, and credential breach history to produce a continuously updated employee risk score.
This signal enables security teams to automatically enroll high-risk employees in targeted remediation before an incident occurs. It also gives CISOs the board-ready metrics needed to justify training investment.
6. Map Cybersecurity Awareness Training Program Content to Compliance Frameworks
SOC 2, HIPAA, PCI-DSS, GDPR, ISO 27001, and NIST CSF each require documented evidence that employees received relevant security training. Training content mapped to these frameworks converts a cybersecurity awareness training program from a security investment into a compliance asset, reducing audit preparation time and eliminating the gap between control requirements and demonstrated employee knowledge.
7. Close the Loop with Phish Triage and Reporting
A phishing response capability anchored by a Phish Alert Button transforms employees from passive targets into active threat contributors. When employees report suspicious emails and receive immediate feedback on whether the message was safe, spam, or malicious, the feedback loop reinforces recognition skills in real time.
It also surfaces live cyberattack campaigns reaching the organization before they generate incidents.
How Generative AI Is Changing Cybersecurity Awareness Training Program Content Production
AI-generated content engines are collapsing the time between identifying a new threat pattern and deploying training about it from weeks to minutes. Traditional content libraries require subject matter experts, scriptwriters, video production, and localization cycles that can take months.
A generative AI content engine, such as Adaptive Security's AI Content Studio, builds a training module from any prompt or policy document in the same session. It adapts content to an employee's specific role, risk profile, and language without creating a separate content track for every segment, making role-based training operationally viable at scale.
Together, these seven components form a feedback loop where each output (a failed simulation, a triggered microlearning, a reported phish, an updated risk score) becomes the input for the next cycle, replacing the linear, one-time-per-year structure of legacy programs.
Equip a cybersecurity awareness training program with every capability the AI era demands through Adaptive Security.
Personalization, Behavioral Analytics, and Predictive Risk Scoring in Cybersecurity Awareness Training Programs

Generic cybersecurity awareness training program trends all point in the same direction: one-size-fits-all approaches fail at the cognitive level as well as the engagement level. Cognitive Load Theory establishes that extraneous cognitive burden, the kind introduced when content is irrelevant to a learner's actual role and threat exposure, directly impairs knowledge retention.
According to Brain Sciences Systematic Review of AI Adaptive Learning 2025, AI-driven adaptive learning systems reduce extraneous cognitive load and produce measurable gains in retention because they eliminate irrelevant content and adapt to individual cognitive profiles in real time. The review synthesized 103 studies on adaptive learning effectiveness.
Why Generic Cybersecurity Awareness Training Programs Fail to Change Security Behavior
Generic training fails because it treats a software engineer, a finance manager, and an executive as interchangeable risks. A developer pushed through invoice fraud modules retains nothing useful. A CFO who skips vishing drills because they seem abstract remains exactly the target cyberattackers prioritize.
The downstream consequence extends beyond low quiz scores. It is unchanged behavior under real cyberattack conditions.
How Behavioral Analytics Enable Predictive Risk Scoring
Modern human risk management platforms now aggregate behavioral signals continuously:
- Simulation failure patterns across email, voice, SMS, and deepfake video;
- Training engagement rates;
- Credential breach exposure via dark web monitoring;
- OSINT signals drawn from over 1,000 public data points per employee.
These inputs feed dynamic risk scores that identify at-risk employees before an incident occurs rather than after. Instead of waiting for the next annual enrollment window, the platform automatically triggers targeted microlearning the moment an employee's signal profile crosses a risk threshold.
OSINT monitoring serves a dual function. The same employee data that sharpens risk scoring also makes phishing simulations more credible and role-specific, because cyberattackers use the same public information to craft convincing lures.
How Role-Based Personalization Differs Across High-Risk Populations
The threat surface is not uniform, and neither is the training. High-risk populations require distinct curricula:
- Finance teams rehearse wire-transfer fraud and vendor impersonation;
- Executives train on deepfake video calls and AI-cloned voice requests, scenarios that mirror real cyberattack patterns and carry disproportionate blast radius if successful;
- IT administrators face credential-harvesting simulations targeting privileged access.
According to Pindrop 2025 Voice Intelligence and Security Report, synthetic voice cyberattacks at insurance companies rose 475% in 2024, a concentration that justifies industry-specific simulation curricula rather than uniform content.
What Cultural Indicators Signal Real Cybersecurity Awareness Training Program Impact
Completion rates measure compliance rather than competence. Cybersecurity awareness training programs with genuine behavioral impact produce different signals:
- Employees initiating peer-to-peer security conversations without prompting;
- Voluntarily self-reporting near-miss incidents rather than staying quiet out of embarrassment;
- Proactively asking security teams questions about suspicious requests.
These behaviors indicate that security has shifted from an annual obligation into an operational reflex. Programs that fail to produce these cultural signals, even with high completion metrics, have not changed the underlying human risk posture.
Surface high-risk employees before an incident does, only with Adaptive Security.
How Often a Cybersecurity Awareness Training Program Should Be Conducted
Cybersecurity awareness training program trends have moved decisively away from the annual training model. Cyberattackers refine social engineering lures daily, while a once-per-year session leaves behavioral memory gaps that threat actors exploit.
Build a sustainable cadence by combining continuous microlearning, monthly phishing simulations, and event-triggered modules. Measure behavioral outcomes rather than completion rates.
1. Replace the Annual Model With Continuous Delivery
Annual training has one structural flaw that no amount of content quality can fix: the threat landscape it covers is outdated before the session ends. AI-generated spear phishing, deepfake video fraud, and vishing cyberattacks evolve on a weekly cycle.
As the SANS Institute states in its security awareness guidance, cyber threats evolve constantly and a one-time training session cannot prepare employees for the latest voice cloning tactics or emerging cyberattack methods.
The practical replacement is a cadence of short, role-specific microlearning modules delivered monthly. Phishing simulations every four to six weeks rotate across cyberattack types: email, SMS, voice, and deepfake video.
2. Apply Risk-Tiered Frequency, Not a Uniform Schedule
Not every employee carries equal exposure. Several roles face materially higher threat probability than a standard end user:
- Finance teams processing wire transfers;
- Executives whose digital footprint enables OSINT profiling;
- IT administrators with privileged access.
High-risk tiers warrant simulation cadences two to three times more frequent than baseline, with scenarios matched to their specific cyberattack surface. Executives should rehearse deepfake video impersonation and vishing scenarios at least quarterly. Sending them the same phishing email the entire company gets is insufficient. Phishing Simulations built on OSINT profiling deliver exactly that kind of targeted rehearsal at scale.
3. Design Cybersecurity Awareness Training Programs for Remote and Hybrid Workforces
Distributed teams introduce delivery constraints that fixed-cadence programs built for office environments cannot accommodate. Asynchronous access, mobile-compatible formats, and timezone-distributed scheduling are prerequisites for completion rates that reflect actual workforce reachability. They are not optional features.
Rotating simulation scenarios and alternating training formats also prevents habituation. Short video modules one month, scenario-based decision exercises the next. Employees who receive the same credential-phishing test repeatedly learn to recognize the template rather than the threat type.
Frequency is a necessary condition for cybersecurity awareness training program effectiveness rather than a sufficient one. Tracking click rates, reporting rates, and risk score trends after each simulation cycle is what converts cadence into verifiable behavioral change.
Run continuous simulations across every channel cyberattackers use through Adaptive Security.
How to Measure the Effectiveness of a Cybersecurity Awareness Training Program
Measuring cybersecurity awareness training program effectiveness starts with replacing lagging indicators like completion rates and pass/fail quiz scores with behavioral signals that predict real risk reduction.
Track phishing simulation click rates and report rates over time, monitor employee risk score trajectories by department and role, and calculate program ROI against a credible breach-cost benchmark. Completion percentages satisfy auditors. They do not move the needle on breach probability.
The clearest signal a cybersecurity awareness training program is working is a workforce that clicks less, reports faster, and extends secure behaviors across channels beyond email.
1. Track Phishing Simulation Click Rates and Report Rates in Tandem
Phishing click rate alone is a one-dimensional metric. The ratio that separates high-performing programs from compliance theater is the gap between click rate and report rate moving simultaneously in opposite directions.
Both shifting together signals genuine behavioral change rather than test fatigue. A finance employee who no longer clicks a business email compromise (BEC) simulation but also hits the Phish Alert Button within two minutes of receiving it demonstrates the dual outcome every program should target.
2. Measure Mean Time to Report and Repeat Offender Rate
Mean time to report suspicious emails directly affects how quickly security teams can contain a real threat. Faster reporting collapses the window cyberattackers use to pivot laterally after initial access.
Repeat offender rate, the percentage of employees who fail simulations across multiple consecutive cycles, identifies individuals who require targeted intervention rather than another generic module. It is the most actionable segmentation variable a security awareness manager has.
3. Monitor Employee Risk Score Trajectory by Department and Role
Aggregate risk scores mask where exposure actually concentrates. Segmenting risk score movement by department, role, and tenure surfaces patterns that cohort-level data buries.
A finance team whose score plateaus after quarter one is a different problem than a new-hire cohort whose score spikes during onboarding. According to Lance Spitzner, Director of Security Awareness at the SANS Institute, security awareness programs that measure behavioral change at the individual level, rather than relying solely on cohort completion data, are significantly better positioned to intervene before incidents occur. Platforms with human risk monitoring dashboards translate these trajectories into the department-level evidence boards need to approve the budget.
4. Track OSINT Exposure Reduction and Compliance Completion by Framework
OSINT exposure reduction measures whether employees are actively narrowing the digital cyberattack surface that cyberattackers use to craft spear phishing lures. Declining public profile data, removed personal details, and reduced social media footprints are concrete indicators of awareness translating into defensive action.
Compliance training completion rates by framework, SOC 2, HIPAA, PCI-DSS, serve a separate but equally important function. They create the auditable evidence trail that satisfies regulators and survives an incident investigation.
5. Build Board-Ready ROI Framing for the Cybersecurity Awareness Training Program
Operational metrics only justify budget when translated into financial language. Anchored against the IBM's breach-cost benchmark cited earlier, a cybersecurity awareness training program that demonstrably reduces breach probability by 10% represents over $400,000 in annual expected loss reduction.
Frame the ROI argument around three board-facing numbers:
- Dollar-value risk reduction derived from risk score improvement;
- Breach likelihood reduction tied to simulation performance trends;
- Total program cost relative to the cost of a single incident.
That framing converts security awareness from a line-item expense into a quantifiable risk mitigation investment, the shift that separates programs with sustained funding from those cut in the next budget cycle.
Turn behavioral metrics into a budget conversation the board approves with Adaptive Security.
Compliance Requirements Driving Cybersecurity Awareness Training Program Trends and Adoption

Regulatory mandates have converted cybersecurity awareness training program adoption from an organizational preference into a legal obligation across healthcare, financial services, government contracting, and beyond. According to FBI Internet Crime Report 2024, business email compromise (BEC) generated $2.77 billion in losses across 21,442 reported incidents, the kind of human-layer exposure regulators now codify training requirements to address.
Organizations that build programs only to satisfy auditors consistently underperform on actual risk reduction.
How Cybersecurity Awareness Training Program Requirements Differ by Industry
The regulatory floor varies sharply by sector, and conflating frameworks creates compliance gaps. Healthcare organizations must satisfy HIPAA Security Rule requirements, which mandate documented workforce training on security policies and procedures for all personnel handling protected health information.
Financial services firms face a layered stack:
- PCI-DSS 12.6 requires ongoing security awareness training for all personnel;
- SEC cybersecurity disclosure rules introduced in 2023 require public companies to describe their processes for managing cybersecurity risk, including human-layer controls;
- FFIEC guidance directs financial institutions to conduct role-based training commensurate with employees' access levels.
Government contractors face the sharpest mandate. CMMC Phase 1 implementation began November 10, 2025, requiring Level 1 and Level 2 compliance as a condition of DoD contract eligibility. Level 2 maps directly to the 110 security practices in NIST SP 800-171, including awareness and training controls.
Globally, regulatory pressure is accelerating. The EU's NIS2 Directive, which took effect in October 2024, explicitly requires member-state organizations in critical sectors to implement cybersecurity hygiene training for their workforce. GDPR Article 39 obligates data protection officers to promote awareness of data protection obligations across their organizations. Organizations with EU operations now face dual obligations under both frameworks.
What Documentation a Compliant Cybersecurity Awareness Training Program Requires
Audit readiness depends on records rather than intentions. Compliance documentation for security awareness training programs typically requires:
- Training completion records tied to individual employees;
- Phishing simulation results showing which employees were tested and when;
- Risk score reports demonstrating improvement over time;
- Audit trails linking specific training modules to the compliance frameworks they address, with content mapped to HIPAA, PCI-DSS, CMMC, GDPR, ISO 27001, or NIST CSF.
Regulators increasingly expect organizations to demonstrate that training content was role-appropriate across departments and that remediation occurred when employees failed simulations.
A cybersecurity awareness training platform that generates audit-ready reporting automatically, and maps training content to specific framework controls, frees compliance teams from manual documentation. It also removes the operational tax that turns compliance into a quarterly fire drill rather than a continuous output of the program.
Generate audit evidence automatically and shift focus back to behavior change with Adaptive Security.
What to Look for When Evaluating a Cybersecurity Awareness Training Program Platform
Selecting the right cybersecurity awareness training program platform is one of the most consequential decisions a security leader makes. The criteria have fundamentally changed as AI-powered cyberattacks outpace the capabilities of email-only training tools.
The primary distinction between legacy security awareness training (SAT) platforms and modern AI-native platforms is simulation fidelity. Legacy tools were architected before deepfakes, vishing, and smishing existed as mainstream cyberattack vectors, while AI-native platforms simulate all four channels simultaneously.
Legacy platforms deliver static email templates and completion-rate dashboards; modern platforms generate OSINT-personalized simulations, score individual behavioral risk in real time, and automate phish triage without analyst intervention. According to FBI Internet Crime Report 2024, total reported cybercrime losses exceeded $16 billion, a 33% increase over 2023. The cybersecurity awareness training platform an organization selects directly influences how much of that exposure reaches employees. Building a program in-house gives control but demands dedicated staff, continuous content production, and simulation infrastructure most security teams cannot sustain.
Which Evaluation Criteria Separate Modern Cybersecurity Awareness Training Program Platforms from Legacy Tools
Beyond multi-channel simulation, OSINT personalization depth is the criterion most often overlooked in platform evaluations. A simulation built from an employee's public LinkedIn profile and company org chart is exponentially more convincing, and more instructive, than a generic phishing template that any employee in the organization could receive verbatim.
Other table-stakes evaluation criteria include:
- Behavioral risk scoring;
- Phish triage automation;
- Compliance framework coverage mapped to SOC 2, HIPAA, GDPR, and PCI-DSS;
- Microsoft 365 and Google Workspace integration that deploys in minutes rather than weeks.
What SMBs Should Prioritize With Limited Budgets
Smaller organizations cannot afford the overhead of complex platform configurations or dedicated security awareness administrators. For SMBs, the most important platform criteria are:
- Fast deployment;
- Automated enrollment triggered by risk signals rather than manual assignment;
- Low administrative overhead that allows a lean IT team to run a consistent cybersecurity awareness training program.
AI-powered cybersecurity awareness training platforms that generate training modules from policy documents or prompts—without requiring custom production—eliminate the content gap that forces small teams to depend on outdated libraries. A platform that consolidates simulation, triage, and risk reporting into a single interface reduces vendor contracts and the operational friction of reconciling data across tools.
Why Cybersecurity Awareness Training Program Platform Consolidation Creates a Cleaner Risk Picture
Platform consolidation, combining Security Awareness Training, Phishing Simulations, Phish Triage, and risk monitoring in a single platform with one admin interface and one unified risk score, reduces vendor complexity and produces cross-signal visibility that point solutions cannot match.
When a simulated vishing call, a failed deepfake test, and a reported phishing email all feed the same employee risk score, security leaders can identify which teams carry the highest exposure and direct training resources accordingly.
That unified risk picture translates directly into board-ready reporting. Instead of presenting disconnected completion percentages from three separate tools, a CISO can show risk trajectory by department, frame the cost of inaction in financial terms, and demonstrate measurable behavioral improvement over time.
Consolidate four security awareness tools into one risk-scored platform through Adaptive Security.
Building a Security-Conscious Culture Beyond the Cybersecurity Awareness Training Program Module
The newest cybersecurity awareness training program trends treat culture as a measurable layer of the program, distinct from training delivery and platform telemetry. The reason is operational: an employee who passes every quiz can still freeze under social pressure during a live vishing call, and the gap between tested knowledge and applied judgment is where cyberattackers operate.
That gap is a leadership and organizational psychology problem rather than a content problem.
Why Leadership Endorsement Determines Whether Cybersecurity Awareness Training Program Culture Takes Root
When executives treat security as someone else's department, employees follow that signal. Leaders who publicly complete training alongside their teams and discuss security decisions in staff meetings signal that the behavior is genuinely valued.
The inverse is equally true. A CISO who sends mandatory training notices while the CEO routes approvals around verification protocols destroys the program's credibility in one action.
How Psychological Safety Around Reporting Drives Down Human-Layer Risk

A blame-free reporting culture is one of the highest-value outcomes any cybersecurity awareness training program can produce. When employees fear consequences for reporting near-misses, a clicked link or credentials shared before realizing the error, those incidents disappear from visibility entirely, and the security team loses the early warning data it needs to respond.
Organizations that normalize self-reporting gain a continuous, real-time signal of where human-layer exposure actually lives. This makes human risk management a living system rather than a quarterly exercise.
Why Extending Cybersecurity Awareness Training Programs Into Personal Lives Strengthens Resilience
Personal security education strengthens organizational resilience for a direct structural reason. Cyberattackers using OSINT do not limit their reconnaissance to corporate systems.
Several personal channels become entry points for spear phishing and executive impersonation:
- Personal social media accounts;
- Home email addresses;
- Compromised home devices and routers.
When employees apply strong authentication, email verification, and skepticism toward unsolicited contact in their personal lives, they reduce the OSINT-exploitable surface cyberattackers map before targeting an organization. Personal security education extends beyond an employee benefit. It functions as a perimeter extension.
The organizing framework beneath all of this remains human risk management. The goal is a measurable, continuous reduction in human-layer exposure across every role, channel, and relationship that cyberattackers exploit.
Build a culture employees defend instinctively, powered by Adaptive Security.
How Human Risk Management Connects Cybersecurity Awareness Training Programs to Business Outcomes
Cybersecurity awareness training program trends are converging on a single structural shift: the movement from measuring what employees learned to measuring what employees do. Human risk management (HRM) is the framework driving that shift, extending security programs far beyond completion logs into continuous, signal-based behavioral monitoring.
The result is a security posture that acts on risk before incidents occur rather than after.
HRM operates on a per-employee risk vector model, where each individual carries a continuously updated score derived from observable behavioral signals. That score is the unit of measurement security teams use to prioritize remediation, allocate simulation cadence, and report exposure trends to leadership.
What Signals an HRM Platform Actually Monitors
An HRM platform aggregates risk signals from across the employee's digital footprint rather than just training records. Dynamic risk scores reflect:
- Simulation behavior across email, voice, and SMS channels;
- Credential breach exposure from dark web monitoring;
- OSINT profiling of publicly accessible employee data;
- Shadow IT and AI tool usage patterns;
- Training engagement history.
Each signal contributes to a continuously updated, per-employee risk score rather than a static compliance status. An employee who completed annual training six months ago but clicked a vishing simulation last week carries elevated real-time risk. HRM captures that distinction; static training records cannot.
How Risk Dashboards Translate Into Board-Level Decisions
Department-level and executive dashboards aggregate individual risk scores into a coherent organizational picture that CISOs can present without requiring board members to interpret raw security data.
A security leader can show, for example, that the finance team's average risk score dropped 22 points after role-specific invoice fraud simulations, or that credential exposure among executives increased following a conference where open LinkedIn profiles were harvested. That kind of quantified, trend-based narrative gives security investment a defensible business case. Budget conversations move from gut instinct to evidence.
This translation layer, from granular behavioral signals to board-ready metrics, is what separates human risk management platforms from legacy SAT tools structurally as well as philosophically.
Operationally, the difference shows up in what security teams do with their week. Awareness-only teams spend it building completion reports. HRM-equipped teams spend it intervening on the highest-risk individuals identified by the platform that morning.
Move from periodic awareness to continuous human risk management with Adaptive Security.
The Future of Cybersecurity Awareness Training Program Trends
Cybersecurity awareness training program trends are at an inflection point driven primarily by the velocity at which AI-era threats mutate and scale. According to the Gartner Top Trends in Cybersecurity for 2025, enterprises combining generative AI with integrated, platform-based security behavior and culture programs will experience 40% fewer employee-driven cybersecurity incidents by 2026.
That projection is a direct rebuke of annual, static training models. Cyberattackers now iterate in hours rather than quarters, and the update cycle of traditional cybersecurity awareness training programs cannot keep pace.
How Generative AI Is Changing How Cybersecurity Awareness Training Program Content Gets Built
The next layer of generative AI in cybersecurity awareness training programs is multilingual, multimodal training that adapts to where the employee is working and on what device. A field engineer in Manila and a finance lead in Frankfurt can receive the same scenario in their working language, in the format that fits their workflow, without the security team commissioning two separate content tracks.
That capability transforms content freshness from a nicety into an operational security control, and it removes localization as a structural barrier to global program coverage.
Whether Deepfake and AI Voice Simulations Will Become Standard

Deepfake and vishing simulations are no longer advanced features reserved for enterprise edge cases. They are becoming baseline components of any credible phishing simulations program.
According to the Gartner Deepfake Exposure Survey 2025, 62% of organizations reported facing a deepfake cyberattack in the previous 12 months. A finance employee who has never experienced a synthetic executive video call on a training platform is unprepared for one in the real world. Organizations that treat these formats as optional will face cyberattack surfaces their employees have never rehearsed against.
What Predictive Behavioral Analytics Mean for Cybersecurity Awareness Training Program Delivery
The next evolution in training delivery moves from scheduled enrollment to real-time risk intervention. Behavioral signals trigger training before a threat materializes rather than after one is clicked.
An employee who flags unusual access patterns, pastes sensitive data into an unauthorized AI tool, or fails a smishing simulation receives targeted content within that same risk window. This transforms training from a periodic event into a continuous risk-reduction mechanism tied directly to observable behavior.
The expanding cyberattack surface compounds every trend above. Collaboration platforms (Microsoft Teams, Slack, WhatsApp), QR code phishing, and AI-enabled business email compromise (BEC) at scale have moved well beyond email as the primary delivery channel for social engineering.
Regulatory pressure is formalizing the response. AI governance training requirements are emerging as enterprises face new mandates around AI tool usage and data handling, making structured cybersecurity awareness training programs a compliance obligation rather than just a security best practice.
Train Teams Against AI-Era Threats Across Every Channel With Adaptive Security
AI has expanded the cyberattack surface well beyond email, and most legacy cybersecurity awareness training programs were never built to address it. Adaptive Security's platform covers the full range of modern threat vectors (deepfake video, vishing, smishing, and spear phishing) with role-based simulations and behavioral analytics that measure actual risk reduction rather than module completion.
What this looks like in practice is a security team that starts Monday with a prioritized list of which employees the platform flagged as high-risk over the weekend, why, and what microlearning has already been triggered for each of them. The work shifts from chasing completion rates to acting on signals.
Organizations evaluating modern programs benefit most when they see the platform applied to their own workforce risk profile. A self-guided product tour walks through real simulation scenarios, role-based content delivery, and the dashboards security leaders use to translate behavioral data into board-level reporting.
Discover what an AI-era cybersecurity awareness training program looks like in practice with Adaptive Security.
Frequently Asked Questions About Cybersecurity Awareness Training Programs
What Are the Key Cybersecurity Awareness Training Program Trends for 2026?
The defining cybersecurity awareness training program trends for 2026 are AI-powered threat simulation, deepfake audio and video simulation, behavioral analytics, and the shift from annual compliance training to continuous human risk management.
According to World Economic Forum Global Cybersecurity Outlook 2025, human-layer risk and AI-enabled social engineering rank among the most pressing organizational exposures, reinforcing why cybersecurity awareness training program architecture, alongside content, is the decisive factor.
How Often Should a Cybersecurity Awareness Training Program Be Conducted to Be Effective?
The current benchmark for effective cybersecurity awareness training programs is monthly or quarterly phishing simulations combined with short microlearning modules delivered at high frequency, supplemented by just-in-time training triggered by specific behavioral events such as a failed simulation. High-risk employees (executives, finance teams, and IT administrators) benefit from more frequent, targeted simulations.
What Is the Difference Between a Compliance-Based and a Behavior-Change Cybersecurity Awareness Training Program?
A compliance-based cybersecurity awareness training program measures whether employees completed training. A behavioral-change based program measures whether employees make safer decisions.
Behavior-change programs apply principles from behavioral science (spaced repetition, just-in-time interventions, positive reinforcement, and role-based personalization) to shift how employees actually respond to threats. The metric that separates them goes beyond completion rate. It is whether phishing simulation click rates decline and suspicious-email report rates rise over time.
For a closer look at how program architecture affects outcomes, see how modern security awareness programs are built to reduce risk.
How Is the ROI of a Cybersecurity Awareness Training Program Measured?
The ROI of a cybersecurity awareness training program is calculated by comparing program costs against quantified risk reduction, using breach cost avoidance as the primary denominator (anchored on the IBM's benchmark referenced earlier in this guide).
When a program demonstrably reduces phishing susceptibility and improves suspicious-email reporting, the avoided probability of a human-initiated breach translates directly into dollar-value risk reduction. The operational metrics that feed this calculation are:
- Phishing simulation click rate trend;
- Mean time to report;
- Repeat-offender rate;
- Employee risk score trajectory.
What Cybersecurity Awareness Training Program Requirements Apply to Healthcare and Financial Services Organizations?
For healthcare, the HIPAA Security Rule, administered by HHS, requires covered entities and business associates to train all workforce members on security policies and procedures, with periodic cybersecurity awareness training program retraining when material changes occur.
Financial services organizations face overlapping requirements:
- PCI-DSS requires ongoing security awareness training for all personnel who handle cardholder data;
- The SEC's 2023 cybersecurity disclosure rules require public companies to maintain documented cybersecurity risk management programs;
- FFIEC guidance sets expectations for financial institution employee training.
Both sectors must maintain auditable training completion records, simulation results, and risk score documentation from their cybersecurity awareness training programs.
Key Takeaways: Cybersecurity Awareness Training Program Trends
- Cybersecurity awareness training program trends in 2026 center on continuous, AI-aware delivery; programs built on annual compliance modules cannot keep pace and continuous, behaviorally grounded delivery is the new baseline.
- The human element drives the majority of confirmed breaches, making cybersecurity awareness training program design the decisive factor in breach probability.
- Modern cybersecurity awareness training programs combine phishing simulations, role-based microlearning, just-in-time training, human risk scoring, compliance mapping, and phish triage into one feedback loop.
- Behavioral metrics (click rate trend, mean time to report, repeat-offender rate, and risk score trajectory) replace completion rates as the indicators that predict real risk reduction.
- ROI framing for a cybersecurity awareness training program should anchor on dollar-value risk reduction (drawn from the IBM's breach-cost benchmark cited earlier) rather than module completion.
- Compliance frameworks (HIPAA, PCI-DSS, SOC 2, GDPR, CMMC, NIS2) define the floor; effective cybersecurity awareness training programs are built well above it.
- AI-generated content, deepfake and vishing simulations, and OSINT-personalized scenarios are the cybersecurity awareness training program trends that are now table-stakes for any platform under evaluation.
Future-proof your organization's cybersecurity awareness training program against AI-era threats using Adaptive Security.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents










