In early 2024, a $22 million breach at a subsidiary of UnitedHealth was traced back to poor cyber hygiene, specifically a lack of proper multifactor authentication (MFA). Although MFA was available, it wasn’t enforced, and employees weren't prompted to update their passwords. This wasn’t just a tech failure; it was a behavioral one.
Modern day hackers using innovative attacks like AI-generated phishing emails now mimic internal company personnel. SaaS sprawl has created a mass of login portals across operating systems that introduce unmonitored risk. In this new environment, traditional security training like standard policy checklists and annual training sessions aren’t enough.
The solution? Moving beyond one-off education sessions and toward embedded security habits. Cyber hygiene isn’t just about knowing what to do—it’s about building secure reflexes into how people work every day. That means leveraging behavioral cybersecurity strategies and feedback loops that make secure employee behavior automatic and adaptive over time.
What is cyber hygiene?
Cyber hygiene refers to a fixed set of practices that keep software safe, including regularly patching software, rotating strong passwords, using MFA, and avoiding suspicious links or apps. It’s the digital equivalent of brushing your teeth; it's routine, essential, and rarely changes. These traditional employee security habits are helpful, but they aren't enough, as cyber hygiene must now address new cybersecurity risks:
- Hybrid workforces accessing sensitive systems from personal networks
- Shadow IT tools (tech used by employees without IT approval/oversight) being adopted without security vetting
- Human risk becoming the leading indicator of breach likelihood
These conditions expose the reality that many information security failures are due not to a lack of tools but from bad employee behavior. Systems don’t click links, reuse passwords, or fall for deepfakes—people do.
Cyber hygiene standards need to be raised to prevent aggressive future ransomware attacks. It’s about empowering people to consistently make secure choices and designing workflows that make those choices easier and faster.
Common cyber hygiene failures that lead to risk
Here are just a few examples of how everyday habits can bypass even the strongest security posture. Each reflects a gap, not in knowledge, but in habit. Security isn’t breaking down at the tool level, but during an employee’s decision.
- Reused credentials from breached SaaS logins: A project manager uses the same password across Trello, Notion, and Slack. When one is breached, attackers pivot quickly across platforms, typically undetected, mining sensitive information as they go.
- Employees bypassing VPNs or sharing files via personal tools: To speed up collaboration, a remote worker uploads sensitive documents to a personal Google Drive outside the monitored security software.
- Missed phishing cues in collaboration tools: An employee receives a direct message in Teams from an impersonated colleague asking to “review this file before the meeting.” The link routes to a credential harvesting page that looks nearly identical to OneDrive.
How to embed cyber hygiene through behavioral design
Knowing the basics of cyber hygiene best practices isn’t enough. Employees need systems that make the secure path the absolute easiest path. Embedding cyber hygiene into daily workflows means moving from one-off instruction to continuous behavioral reinforcement. This requires a mindset shift from compliance-focused training to habit-building.
Here are three practical ways to embed secure behaviors in your cybersecurity framework.
1. Make behavior stick
Security behaviors don’t become reflexive through a quarterly training video on the newest security software updates. They take root the same way any habit does: through triggers, timing, and repetition.
- Triggers: These are cues that nudge action, like a pop-up reminding a user not to reuse a password during SaaS onboarding.
- Timing: Interventions are more effective when they align with real decisions. Pre-login warnings and click-level reminders outperform generic emails.
- Repetition: Behaviors become habits through consistency. One-and-done training fails because habits need to be rehearsed.
Treating security habits like any other behavior change increases cybersecurity awareness and limits the success rate of cyber threats.
2. Set up environmental cues that reinforce security
Behavior is shaped more by environment than intention. In cybersecurity, that means layering in contextual nudges and feedback loops that guide decisions in real time. These cues make security second nature, especially in hybrid and high-pressure environments where shortcuts are tempting.
- Just-in-time prompts: Flag risky behavior (like file-sharing outside approved tools) at the moment it happens.
- Contextual warnings: Show alerts during off-network access or before suspicious downloads.
- Real-time feedback: Reinforce correct behavior with immediate positive feedback or rewards. This reduces frustration while reinforcing the desired action.
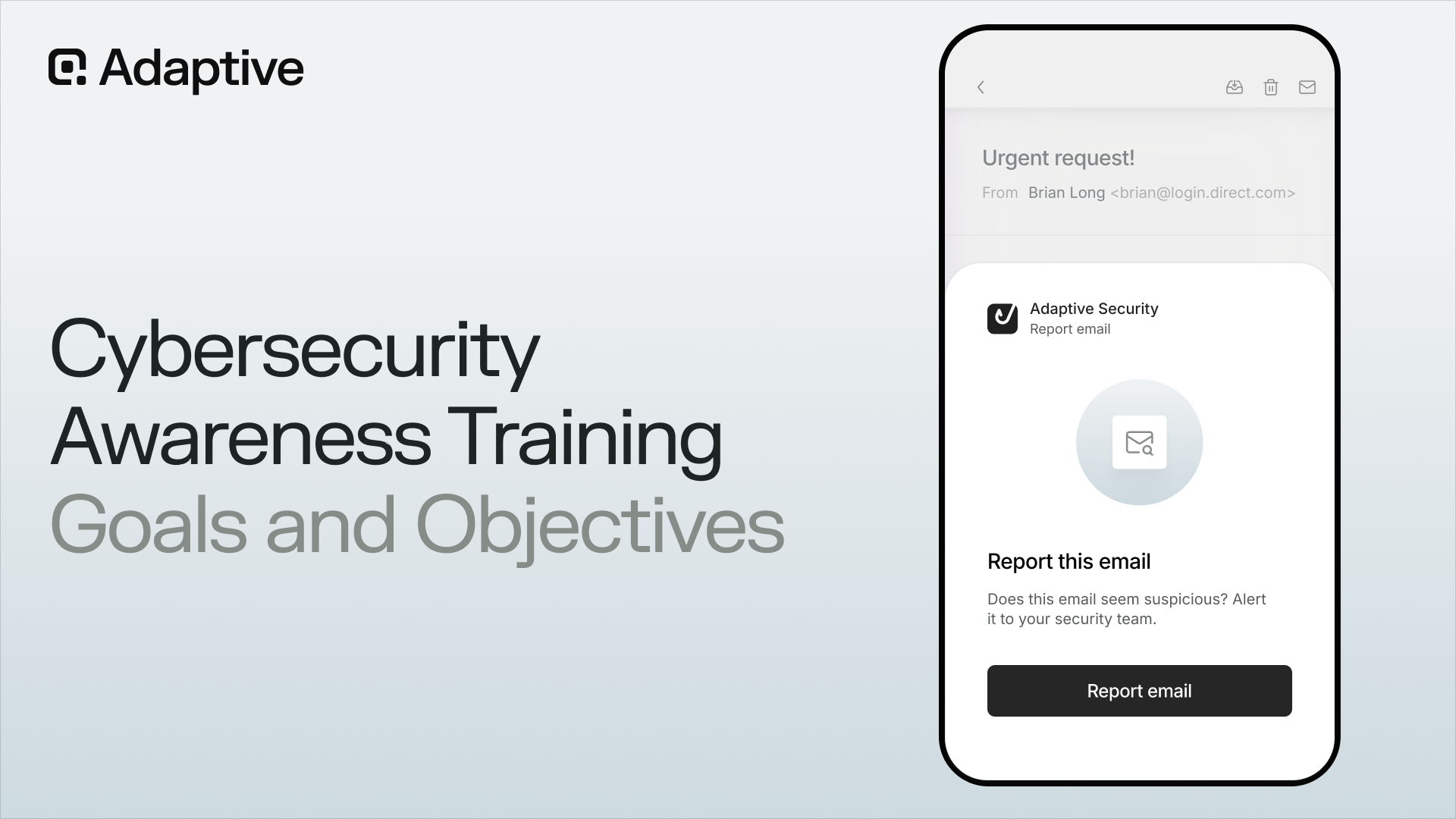
3. Use SAT platforms like Adaptive to build reflexes, not just awareness
Most security awareness training (SAT) platforms stop at basic knowledge. Adaptive goes further by simulating real-world threats and measuring responses against these known vulnerabilities. This guides behavioral improvements over time.
Adaptive embeds simulation-driven feedback loops. Employees don't just learn; they build reflexes that prevent everyday security lapses. This habit loop forms the foundation of good cyber hygiene.
Metrics that matter: measuring cyber hygiene beyond checklists
Too often, cyber hygiene is measured by surface-level metrics: training completion rates, policy acknowledgments, and audit readiness. While these satisfy compliance teams, they don’t reflect what truly matters—whether employees are actually behaving more securely and protecting sensitive data.
To understand and improve your actual security posture, your organization needs to shift toward behavior-based, risk-informed metrics that spot real-world impact. These three categories of metrics offer deeper insight into employee behavior and organizational resilience.
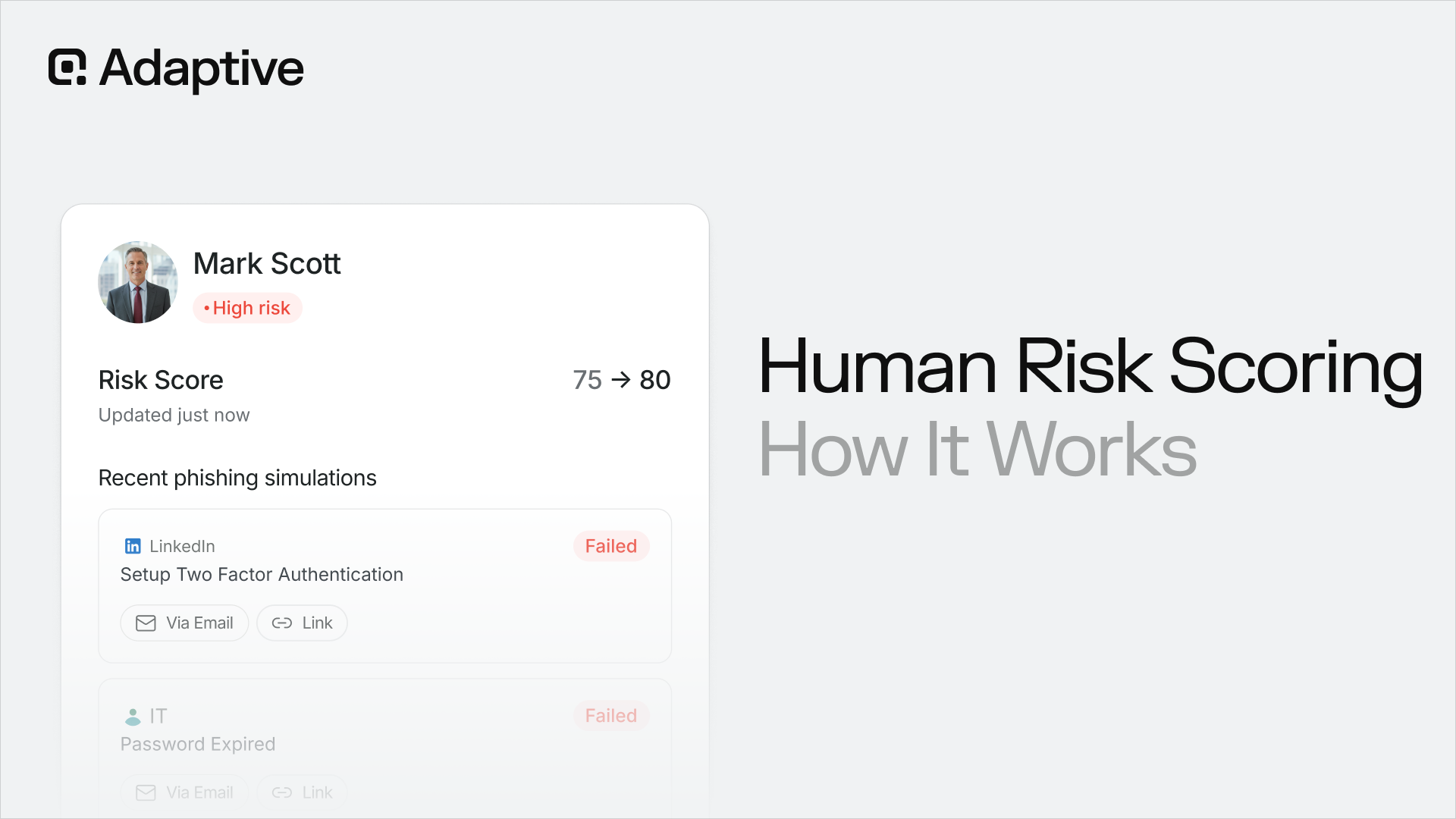
1. Risk-based segmentation
Rather than treating your workforce as a single unit, segment users based on risk behavior, and identify the following:
- Who clicks on simulated phishing emails and how often
- Who improves after retraining versus repeat offenders
- Which departments exhibit the highest human risk
This allows targeted cybersecurity hygiene interventions instead of blanket training.
2. Behavioral KPIs
Track behavior that correlates directly with breach likelihood. These KPIs provide a performance view that evolves with behavior, not just policy alignment. You should track:
- Click-rate reduction across phishing simulations
- Time-to-completion for patch prompts or password updates
- Adherence to just-in-time prompts (e.g., bypassing VPN alerts)
3. Culture metrics
Look for an increase in voluntary reporting (e.g., phishing alerts via Slack or email), peer engagement with awareness content, and positive reinforcement trends (e.g., manager recognition for secure behaviors). These metrics signal psychological safety and engagement, both critical elements of lasting change.
This is where Adaptive Security stands out. Unlike legacy training platforms, it captures data telemetry and converts it into actionable insights over time.
For example, the KPI, “Users with a 3+ point decrease in phishing susceptibility over 90 days” is a clear, board-ready signal that your program is driving down human risk.
With Adaptive’s intuitive dashboard, these signals become trend lines your leadership can track, not just data buried in PDFs. From repeat clickers to high-performing teams, you’ll see where to double down, where to intervene, and where your security controls are improving.
Change management for cyber hygiene: What works
Behavior change happens when leadership, systems, and social signals align. The most successful cyber hygiene programs don’t just train employees; they create momentum, accountability, and reinforcement at every level of the organization.
Here’s what real-world security behavior change looks like.
1. Executive modeling and visible support
Employees take cues from leadership. When CISOs and CIOs visibly practice strong cyber hygiene, using password managers, reporting phishing attempts, and completing simulations promptly, it sets a tone that security isn’t optional.
Make good cybersecurity practices visible:
- Have execs complete the same incident response simulations as employees.
- Share stories in all-hands meetings about security wins and near-misses.
- Reinforce that secure behavior is part of performance, not just policy.
2. Designating cross-functional security champions
Security doesn’t live solely in IT. To embed secure behaviors org-wide, designate security champions across departments—especially in HR, finance, and operations.
These champions reinforce best practices within their teams and provide feedback loops from the ground. They also help normalize security as a team value, not just a top-down directive. When security is peer-reinforced, it sticks.
3. Using simulations to spark urgency
Change accelerates when people see how easily cyber criminals can fool them and what the consequences can be. Adaptive’s CEO fraud deepfake demo is one such eye-opener.
In just minutes, Adaptive can generate a synthetic voice or video of your CEO requesting a “confidential wire transfer”—a data loss simulation that feels chillingly real. This turns abstract risk into tangible urgency, revealing blind spots in decision-making under social engineering.
These simulations are reminders that antivirus software won’t protect employees from the most ingenious attacks. Importantly, they create teachable moments without real-world consequences. It’s a shift in mindset from “it won’t happen here” to “I need to be ready for security breaches.”
Make cyber hygiene a daily habit, not an annual audit
Cyber hygiene isn’t about adding another checklist—it’s rethinking how we measure, reinforce, and model security behavior. From behavioral prompts and environmental cues to simulation-driven habit loops and meaningful metrics, cyber hygiene starts with Adaptive Security.
With Adaptive, you can leverage change management tactics and platforms to transform security from a compliance obligation into a cultural reflex.
See how Adaptive helps security behaviors stick; take a self-guided tour today.
FAQs about cyber hygiene
Why is cyber hygiene important?
Cyber hygiene is your organization’s frontline defense against everyday threats. Most breaches exploit lapses in basic behaviors, like reusing passwords or falling for impersonation scams. Good cyber hygiene reduces vulnerabilities and ensures employees are active participants in the fight against cyberattacks, not passive liabilities.
What’s the difference between cyber hygiene and cyber security?
Cyber security is the broader discipline of protecting systems, networks, and data from digital threats like malware. Cyber hygiene is a subset focused on the routine, preventative behaviors that individuals and teams follow—like updating software, avoiding suspicious links, and using secure credentials. Think of cyber hygiene as the “health habits” of your cyber security program.
Why do most cyber hygiene programs fail over time?
Most programs fail because they treat hygiene as a one-time training requirement, not an ongoing behavior shift. Without reinforcement, contextual prompts, or leadership modeling, employees forget or ignore security protocols, especially under pressure. Programs also often lack the right metrics to spot where behavior isn’t sticking, paving the way for data breaches.
How do you measure effective cyber hygiene in an organization?
Move beyond tracking whether basic training was completed. Instead, you should measure:
- Click rate reduction in phishing simulations
- Improvement over time in human risk scores
- Adherence to real-time prompts
- Reporting behavior
Platforms like Adaptive display these metrics in dashboards that reveal trends, team-level performance, and where intervention is needed.
What role does behavior play in cyber hygiene?
Behavior is the core of cyber hygiene. Tools, policies, and antivirus tech matter, but they only work when people consistently use them correctly. That means building habits, designing workflows with security cues, and creating a culture where secure action is the default, not the exception. Adaptive’s behavioral simulations help transform awareness into action, and action into reflex.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents




.avif)