Phishing simulations built for AI-powered cyber attacks.
Simulate every attack channel your employees face across email, SMS, voice calls, and deepfakes.
Multi-channel simulations across email, voice, and SMS
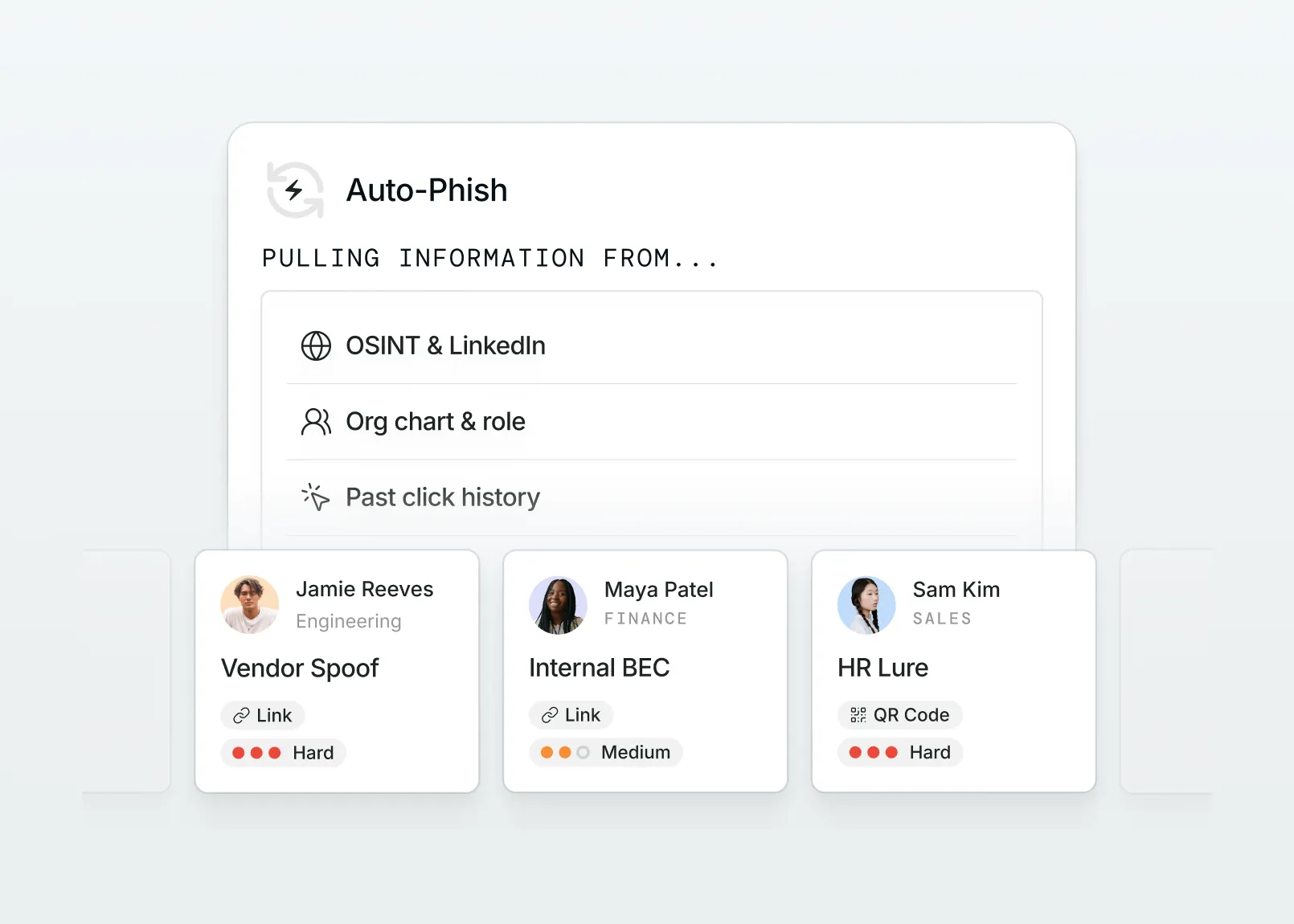
OSINT-powered attacks built from real company data
Always-on phishing simulations that adapt to employee's role, risk, and behavior.










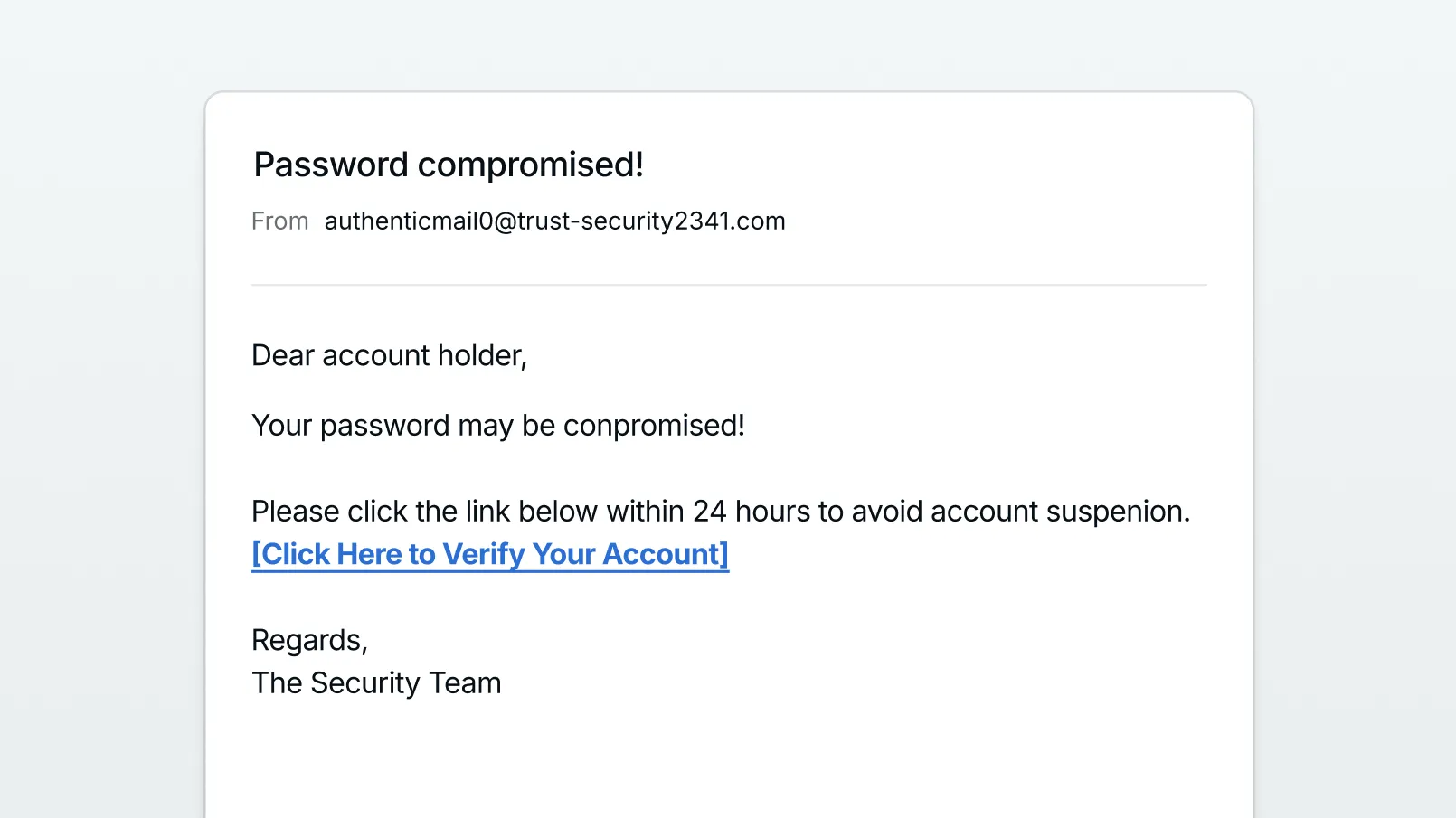
Attacks have evolved. Phishing simulations haven't.
Employees pass outdated tests and stay completely unprepared for how modern attackers actually strike.



AI powered simulations built to train against real attacks.
Multi-channel, hyper-personalized phishing simulations that adapt to every employee and run automatically from day one.




Realistic phishing simulations powered by AI.
Built to simulate the attacks your employees actually face.



Simulations across every channel, target, and tactic.
Comprehensive coverage across every attack scenario, from vendor impersonations to department-specific threats.
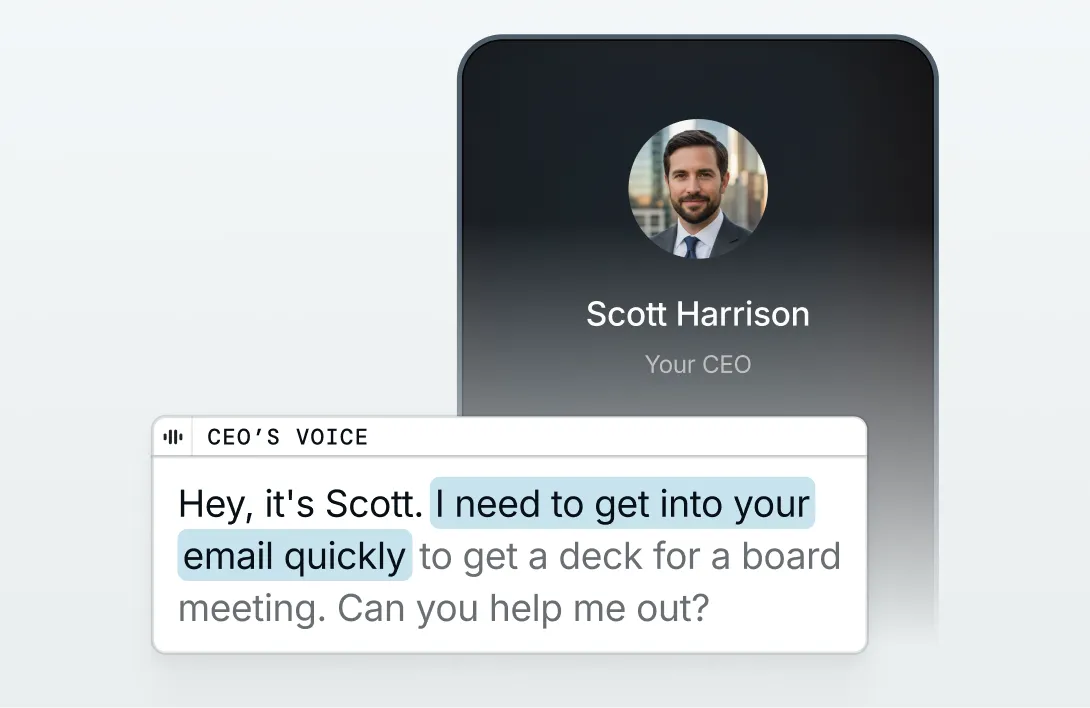
Simulations for AI-generated attacks, smishing, vishing, QR code phishing, and multi-channel scenarios.
Convincing impersonations of executives and internal staff to test responses to urgent, authority-based requests.
Scenarios built around the vendors, brands, and trusted tools employees interact with every day.
Role-specific scenarios targeting the attacks most likely to hit each department, from financial fraud to credential harvesting.
Adaptive vs. Legacy SAT.
What modern phishing simulation looks like against platforms that haven't kept up.
2800+ simulations
Old, stale scenarios
Outdated
Features AI personas of executives
Does not offer
Does not offer
Create your own scenarios
Does not offer
Limited customization
With custom email & spoof pages
Does not offer
Basic impersonation
Across voice, SMS, and email
Does not offer
Does not offer
With dynamic scenario generation
Does not offer
Does not offer
Hear why security leaders trust Adaptive.




Phishing simulations for your industry's specific risks.
Different industries face different threats. Adaptive trains employees for what is specific to theirs.







Frequently Asked Questions.
A phishing simulation is a controlled test that mimics real-world phishing attacks to evaluate how employees respond. It identifies risky behaviors like clicking malicious links or sharing credentials and turns those moments into training opportunities that improve cybersecurity awareness over time.
Phishing simulations are important because they measure real employee behavior, not just knowledge. They show who is likely to click, share credentials, or report suspicious activity, giving a clear picture of human risk. They also reinforce learning through experience. Simulated attacks create immediate, practical training moments that improve awareness and decision-making over time. Finally, they provide measurable data. Teams can track trends like click rates and reporting behavior to identify risk and strengthen overall security.
An artificial intelligence phishing simulation uses generative models to write phishing emails that mirror the attacks real threat actors send, personalized to each employee's role, department, recent activity, and public profile. Unlike legacy phishing testing software that ships with a library of fixed templates, Adaptive's artificial intelligence phishing simulation crafts unique lures on demand, including deepfake voice calls and AI-generated text messages.
Phishing simulations are most effective when run continuously. Many organizations test employees monthly or more frequently for high-risk roles, reinforcing awareness through repeated exposure.
Yes. Modern phishing simulations can include email, SMS (smishing), and voice-based attacks (vishing), as well as deepfake impersonation scenarios. This ensures employees are prepared for threats across multiple channels.
Human risk is an organization’s biggest cybersecurity gap.