Stop AI-Powered
Email Phishing
Built from the ground up to catch AI-generated attacks. Not a legacy rules engine with AI bolted on.
AI that catches what rules miss.
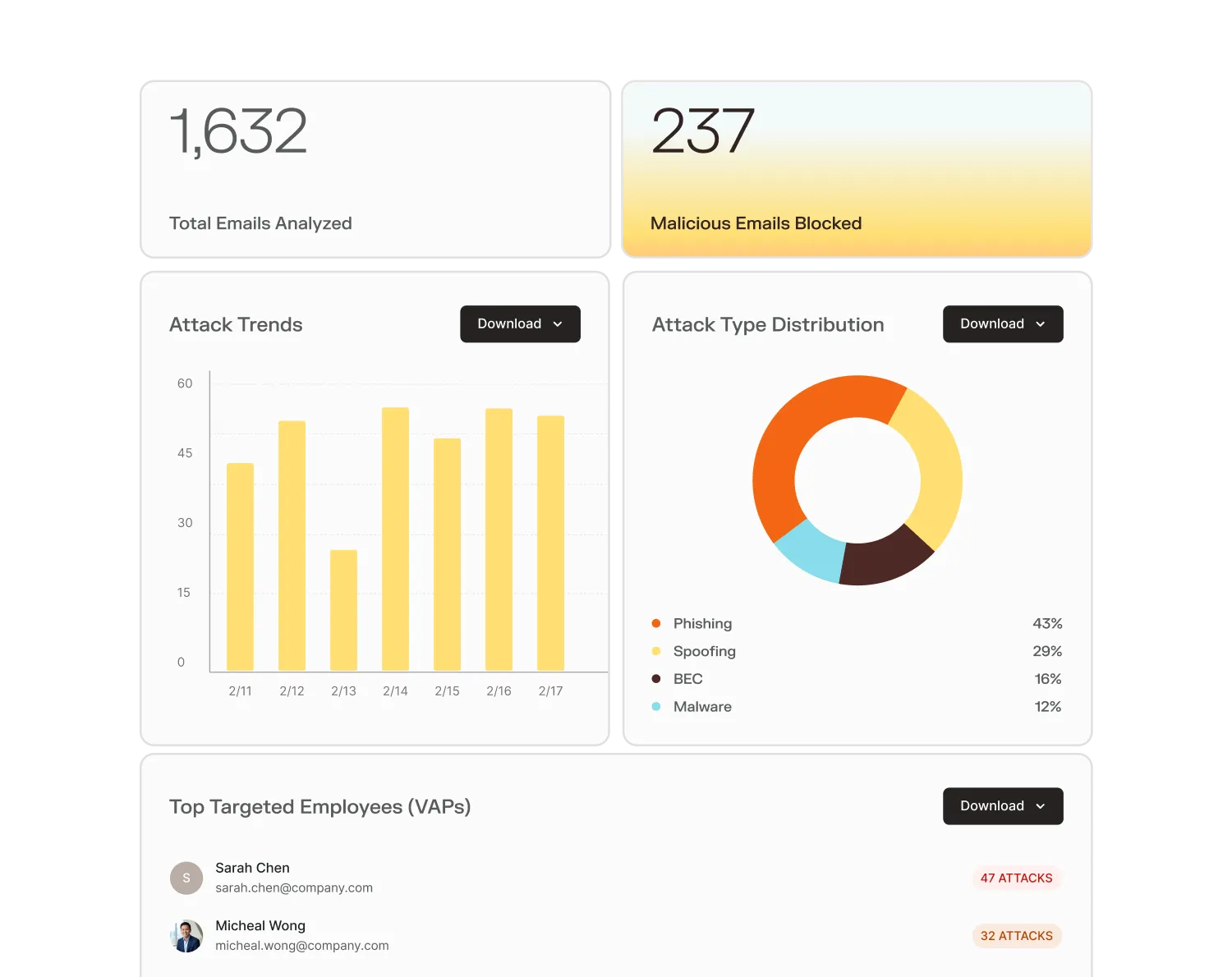
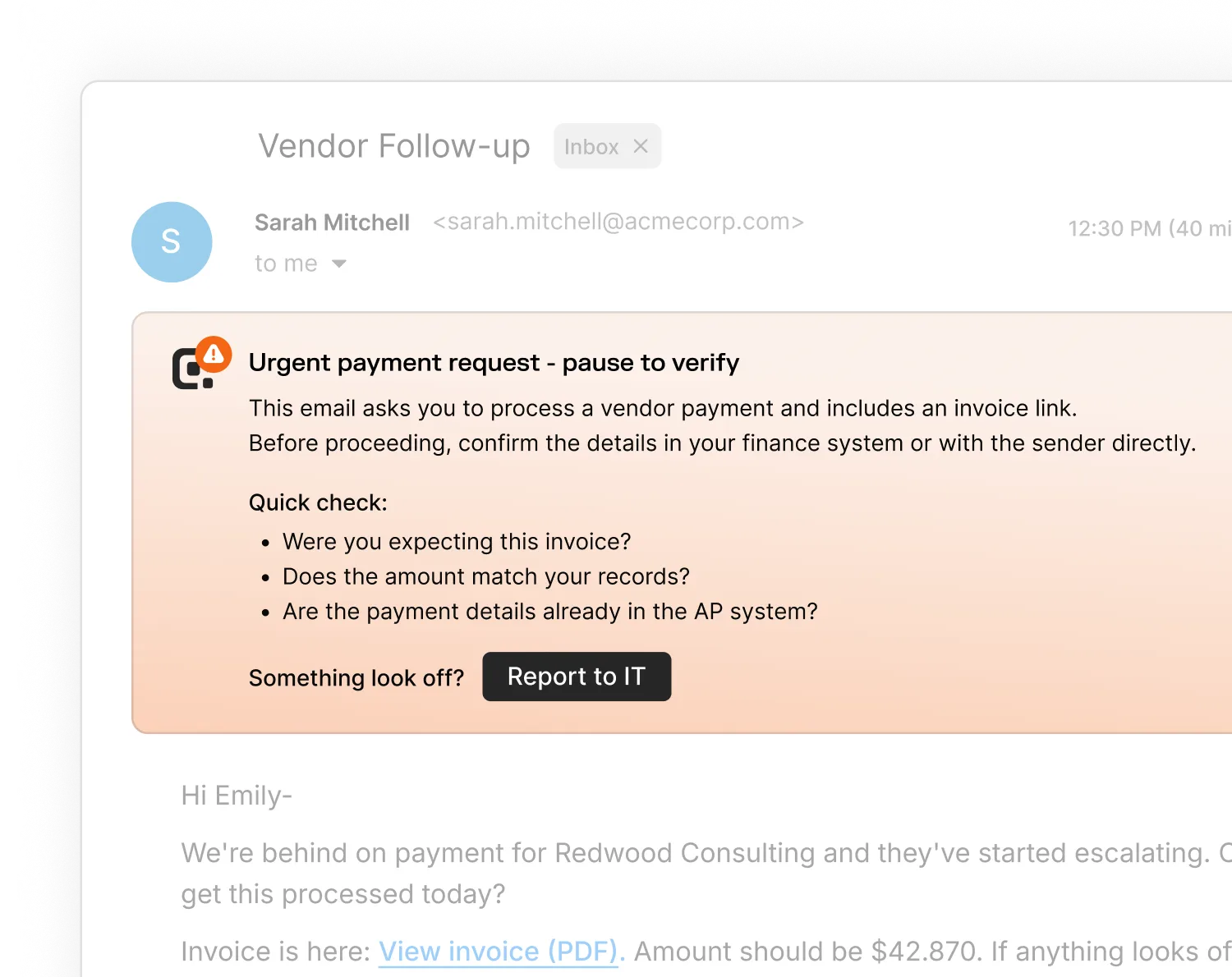
Every verdict is human-readable.
Email protection on autopilot.












.png)












.png)
AI-powered phishing is here. Legacy email security can’t stop it.
Increase in AI-powered email phishing attacks last year
Higher phishing success rate for AI-generated phishing emails
Of AI phishing emails bypass secure email gateways
Ready for production in just minutes.
Your questions answered
AI-generated phishing emails are personalized, grammatically perfect, and context-aware — they don't have the telltale signs (awkward phrasing, generic greetings, suspicious formatting) that older attacks relied on. That's why they bypass traditional rule-based filters at a much higher rate and are significantly more likely to fool employees.
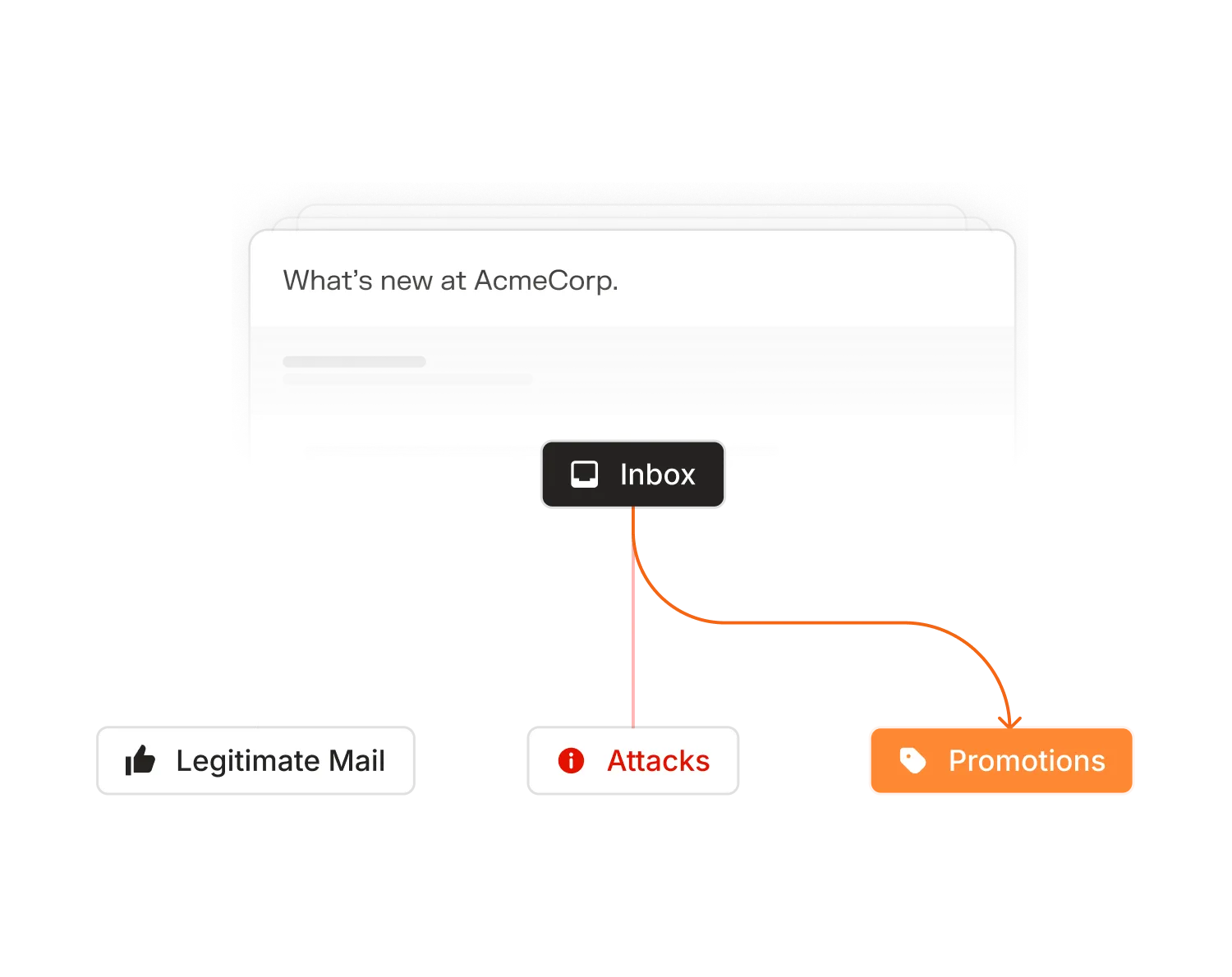
Legacy SEGs were built for a different threat landscape. They match known patterns, signatures, and reputation lists. AI-generated phishing doesn't trigger those rules — it's novel by design. Adaptive uses behavioral and contextual analysis to catch what rule-based systems miss, including attacks that have never been seen before.
No. Adaptive connects via native API to Microsoft 365 or Google Workspace — no MX record changes, no mail routing disruption, no delivery risk. You're up and running in under five minutes.
Yes. Because Adaptive integrates at the API level rather than sitting at the perimeter, it has visibility into internal (east-west) email traffic. That means it can detect business email compromise, account takeover activity, and lateral phishing that never touches an external gateway.
You can start in read-only mode to see exactly what Adaptive would catch without activating any blocking or remediation. It's a low-risk way to baseline your current exposure before going live.
Every detection comes with a human-readable verdict — not just a threat score. Security teams and employees can see a plain-language explanation of what was suspicious and why, which also reinforces security awareness over time.
Security teams at organizations of all sizes that are running Microsoft 365 or Google Workspace and want protection that doesn't require a lengthy deployment or dedicated email security headcount to manage.